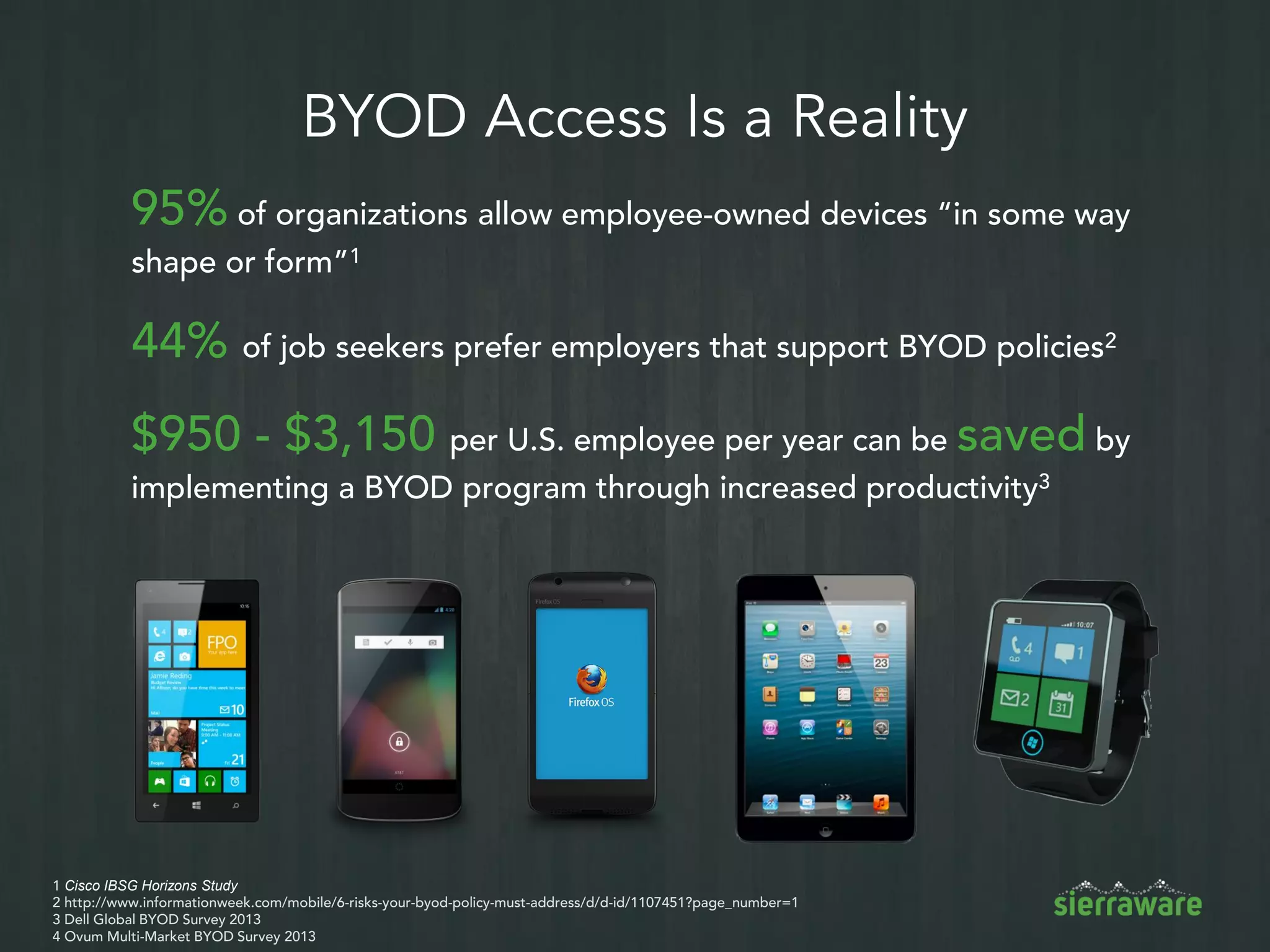
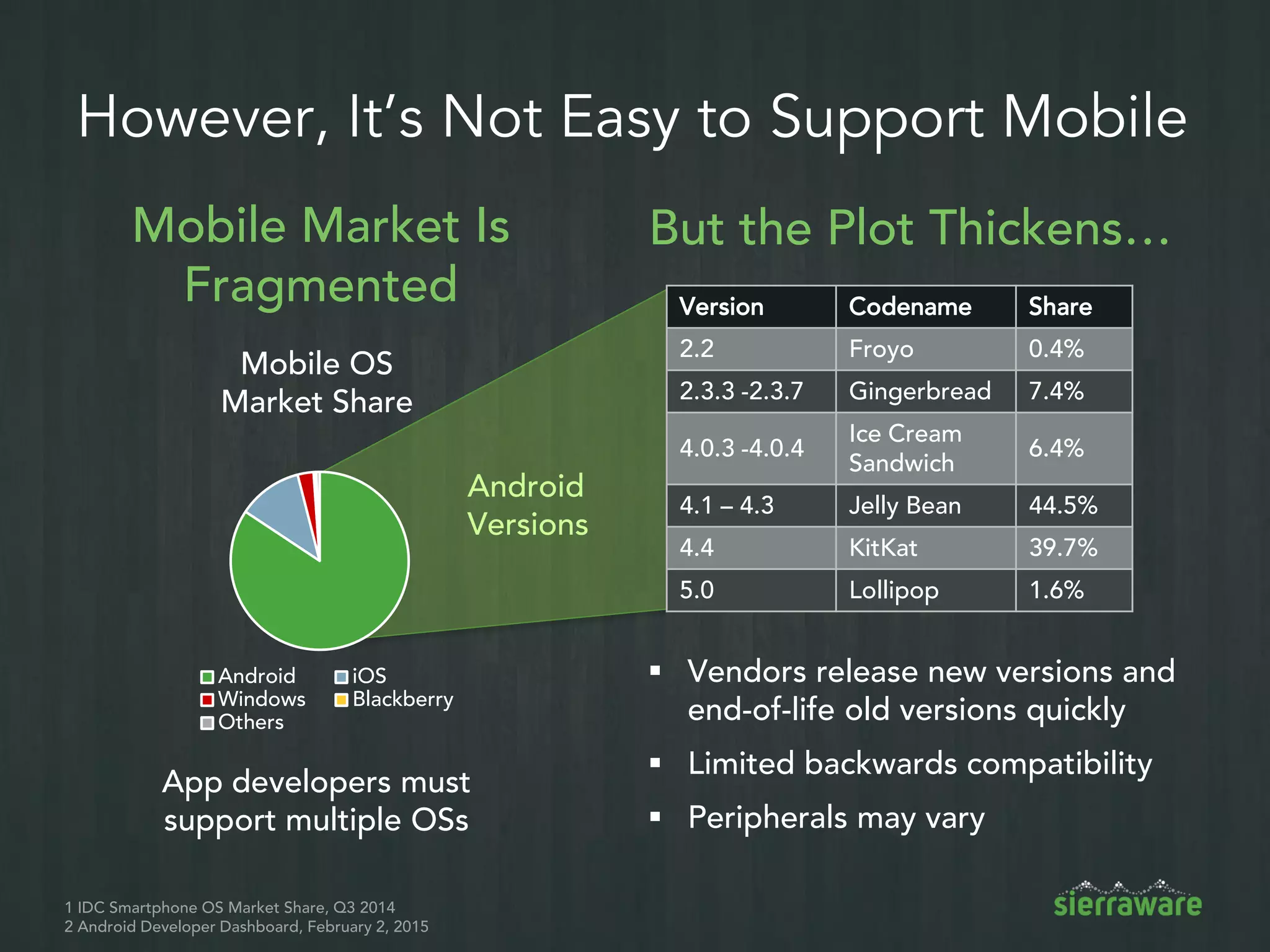
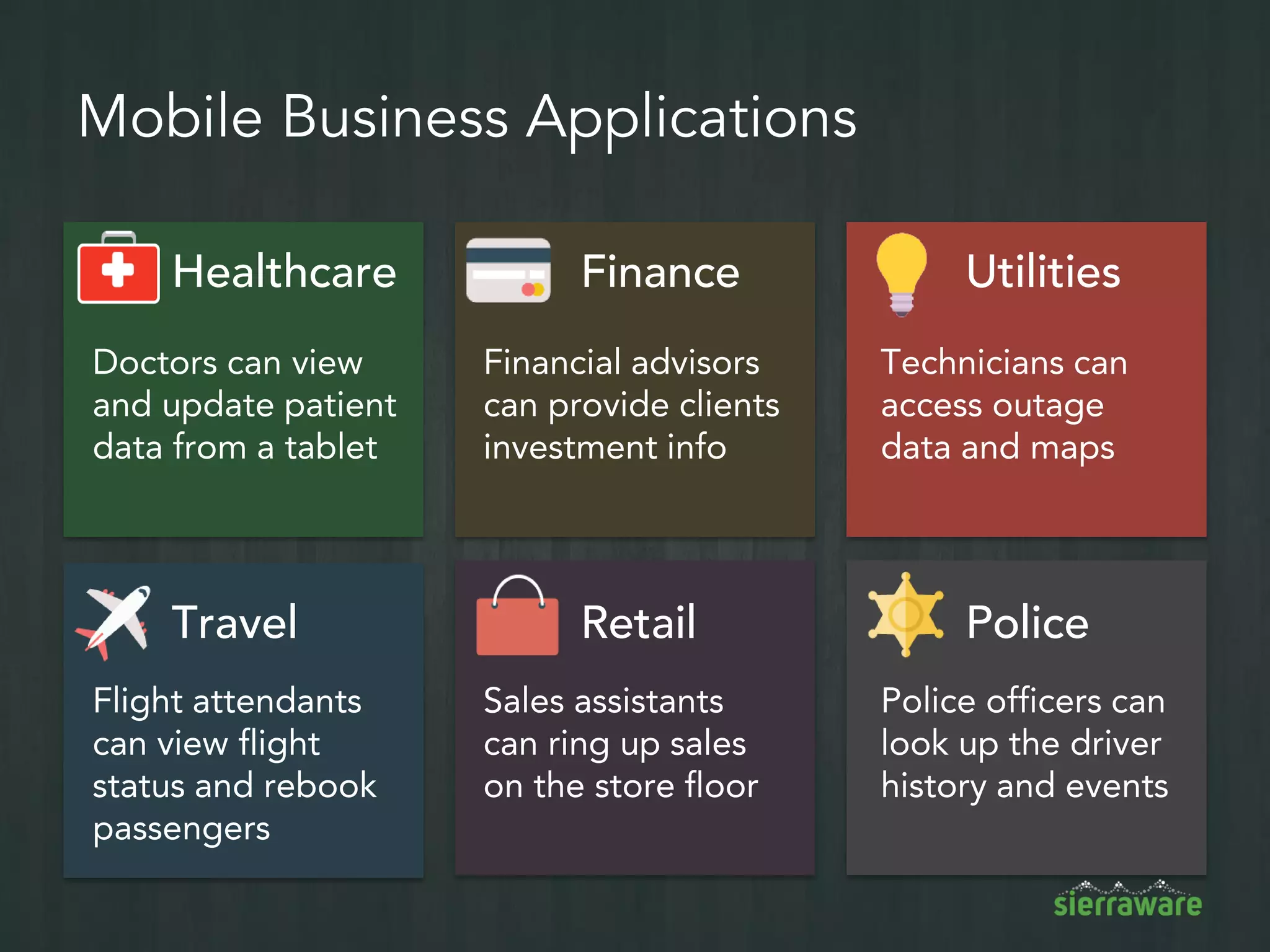
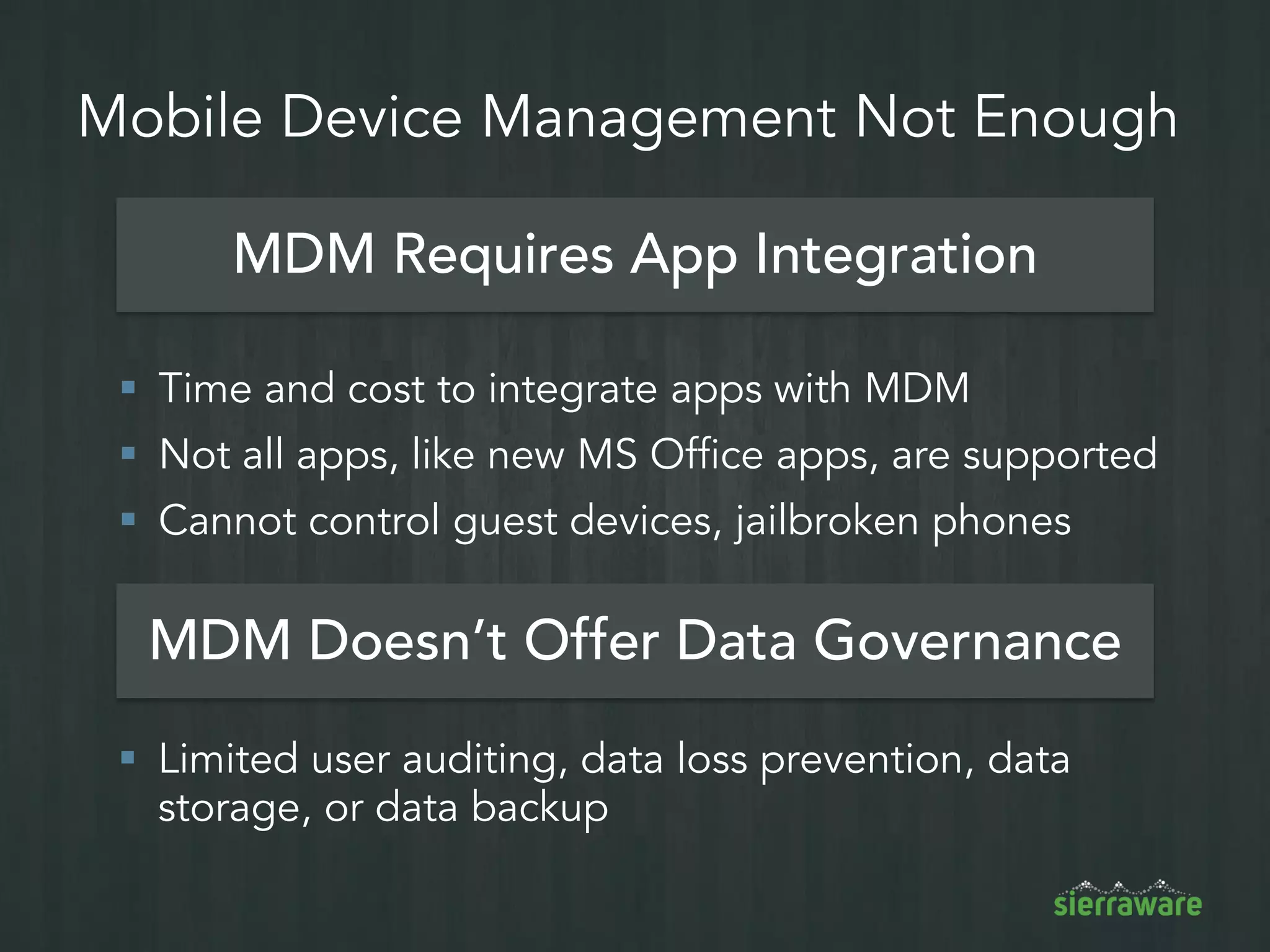
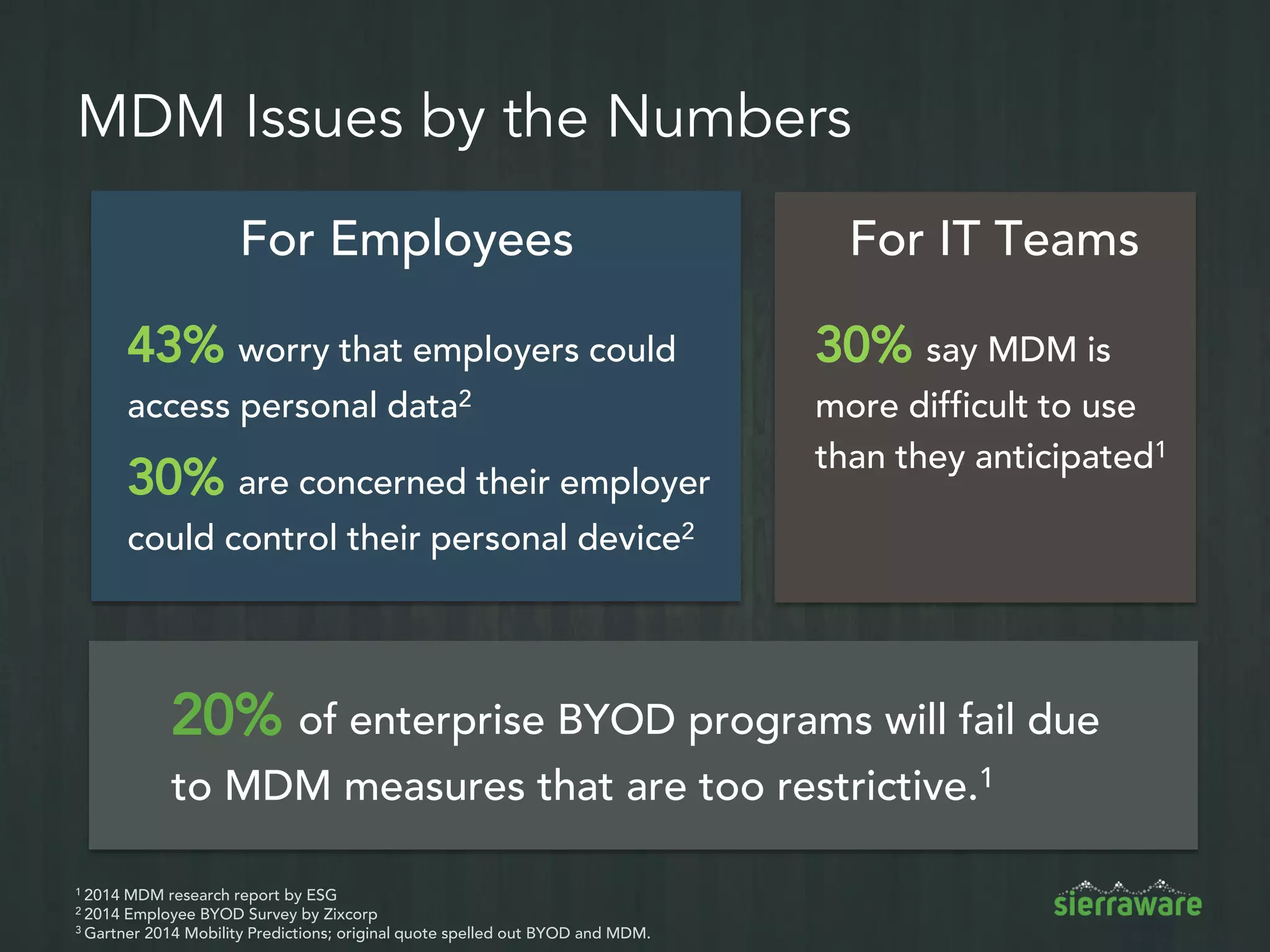
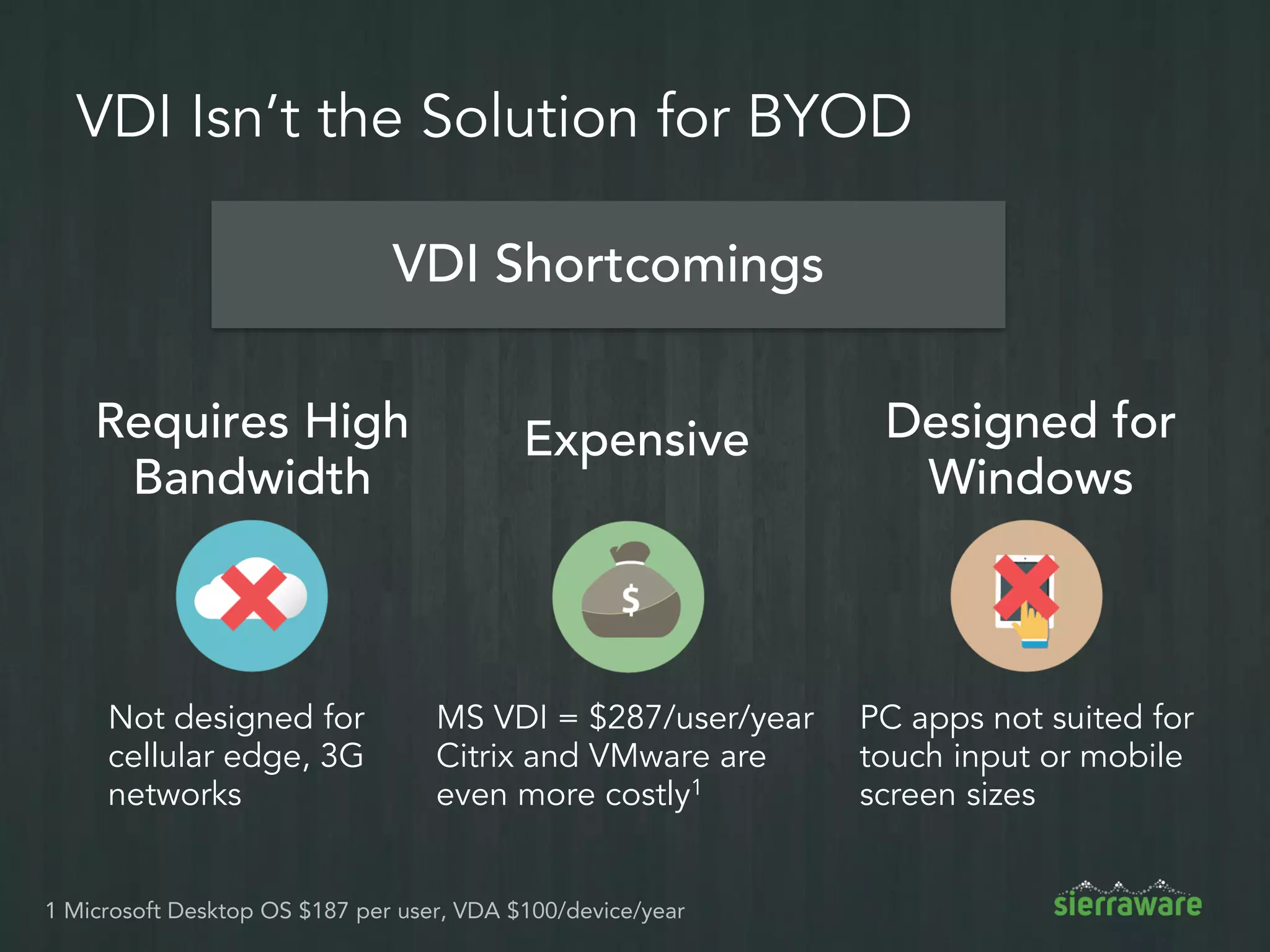
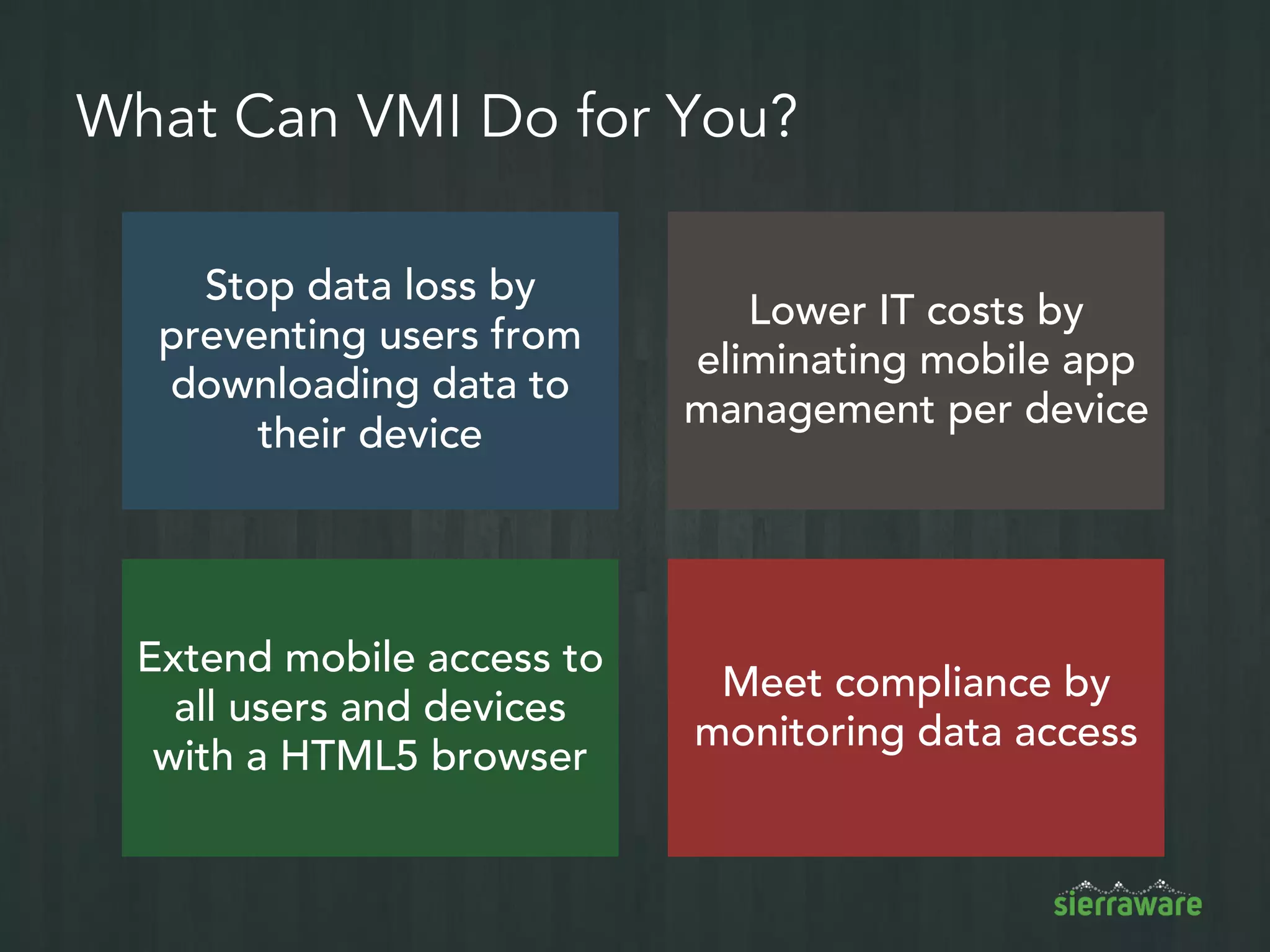
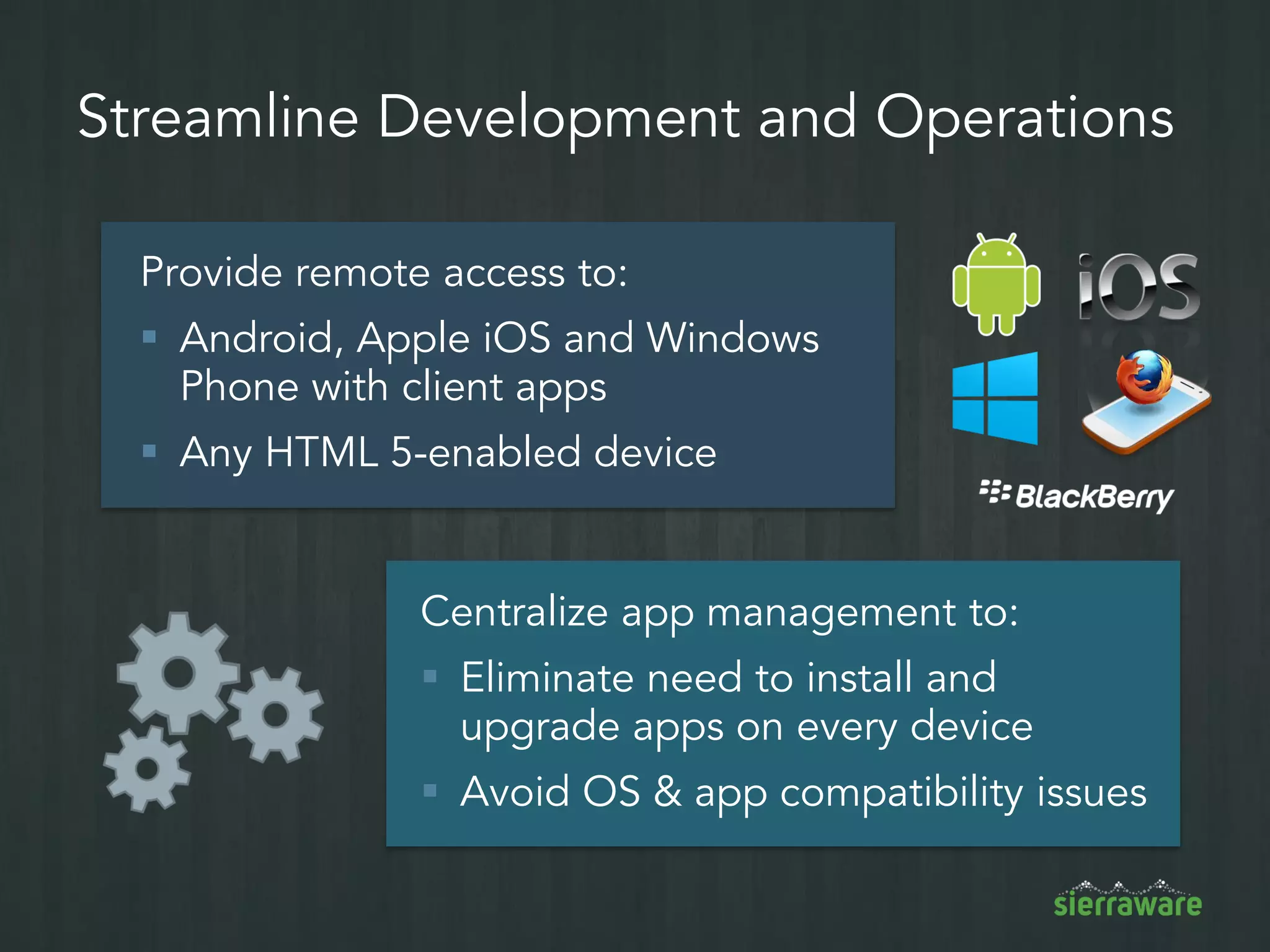
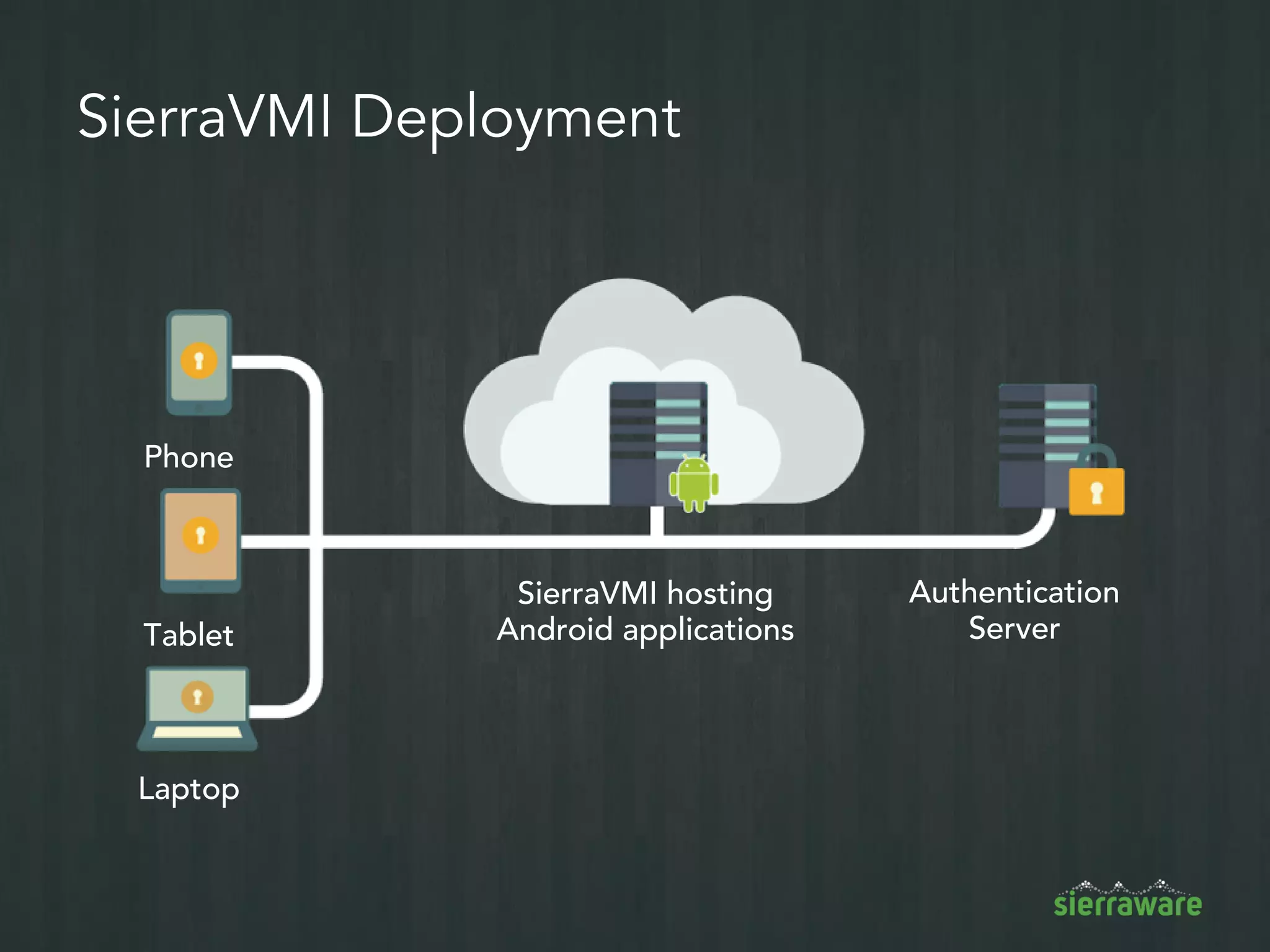
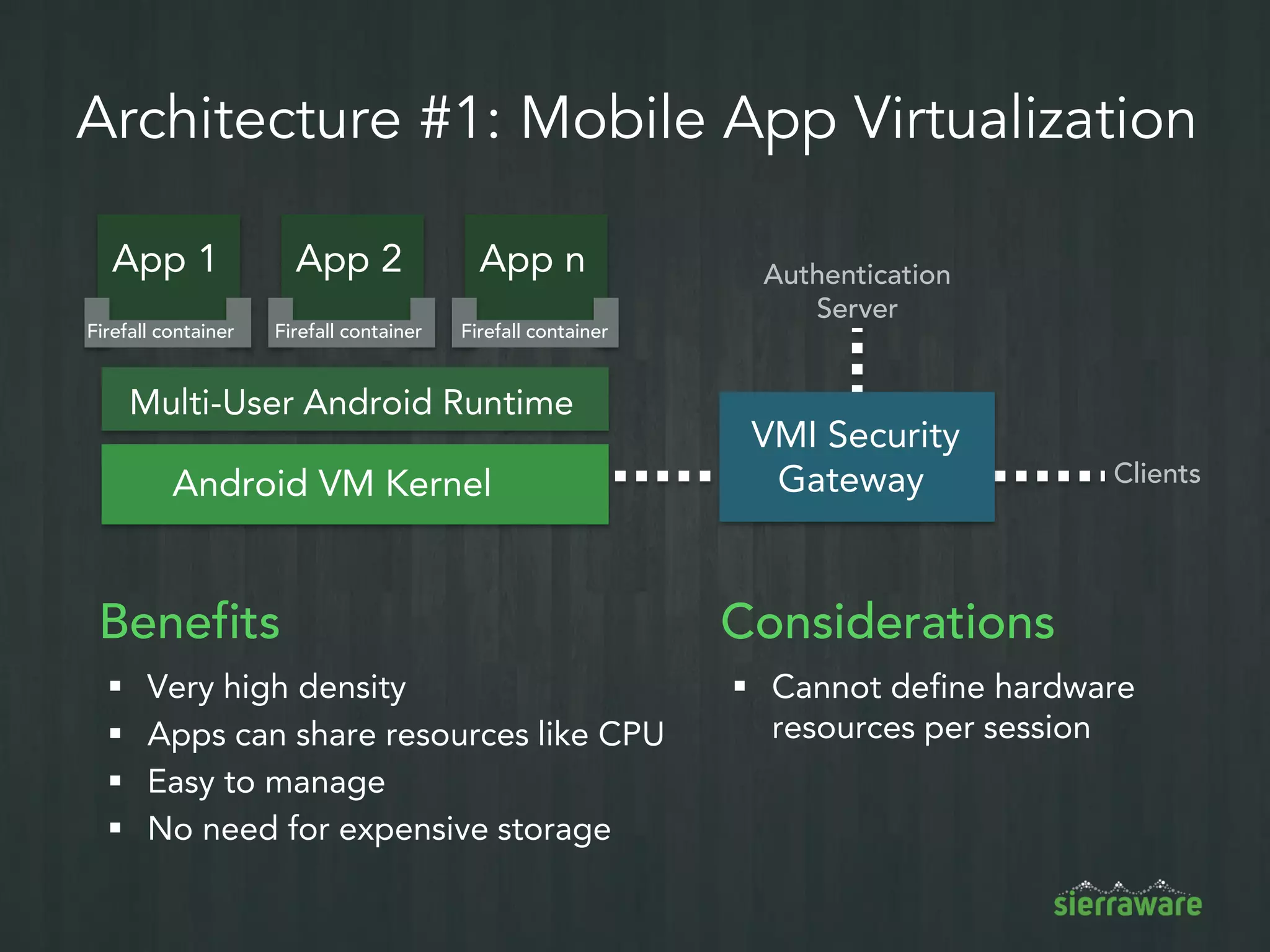
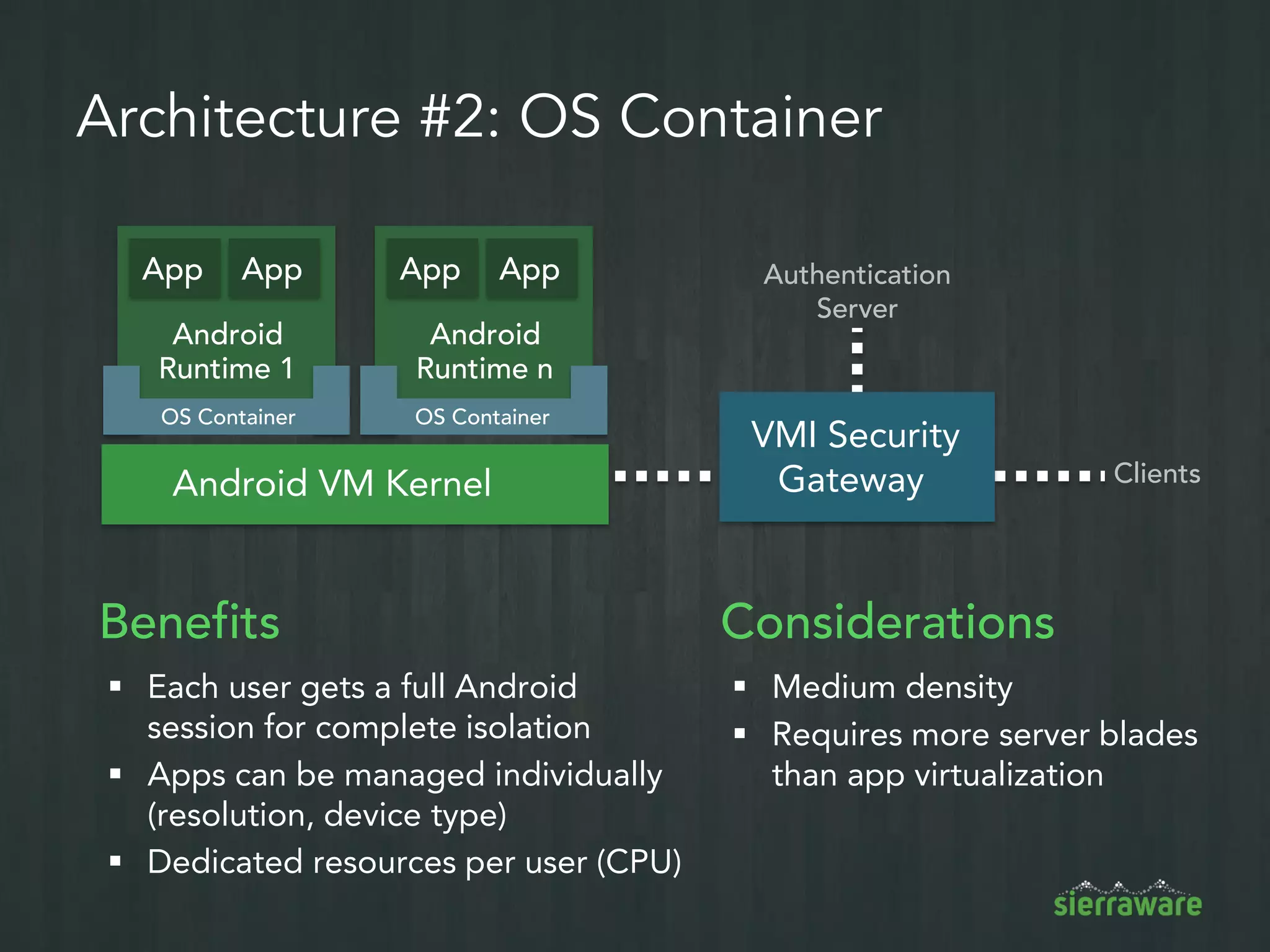
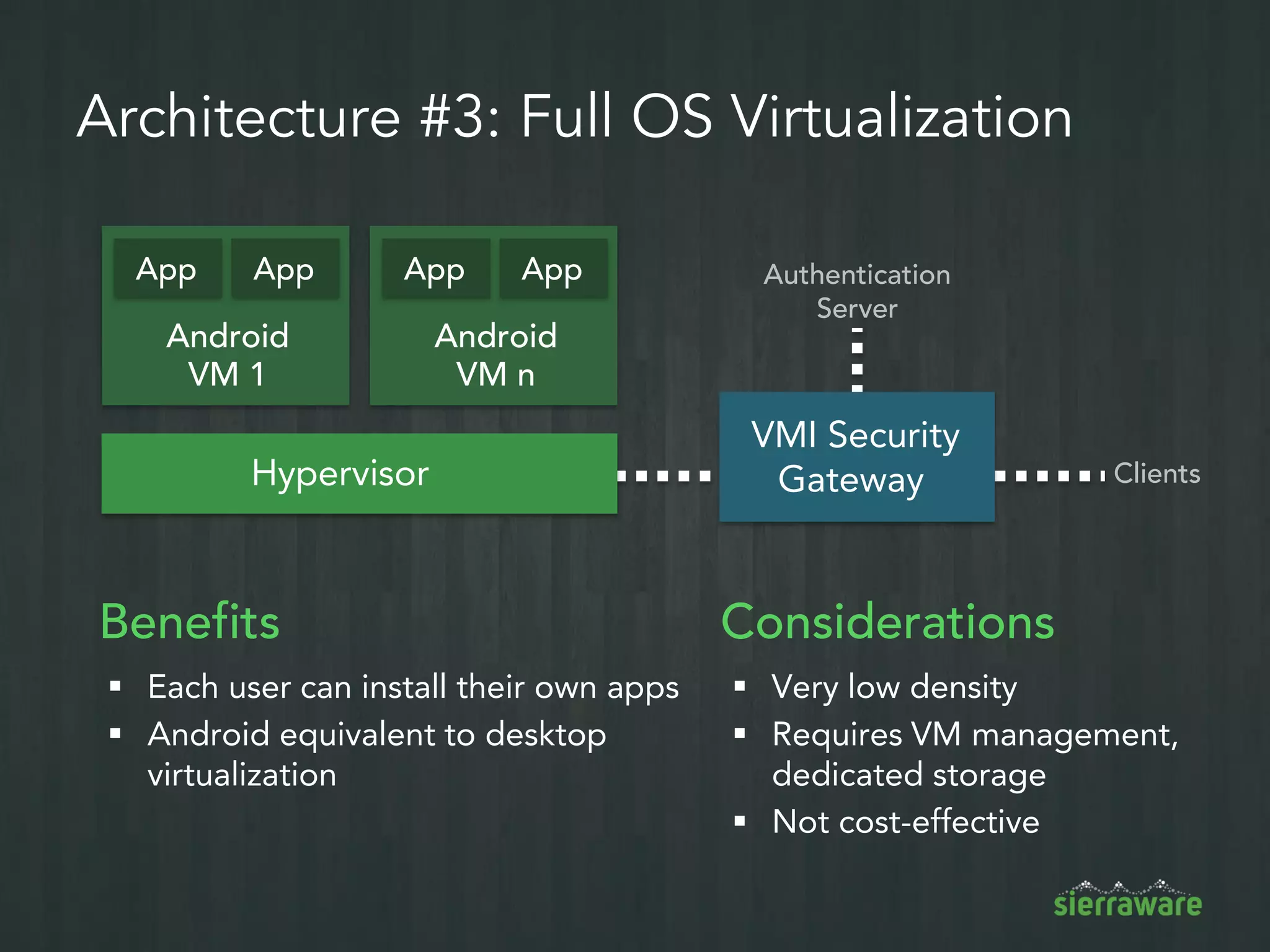
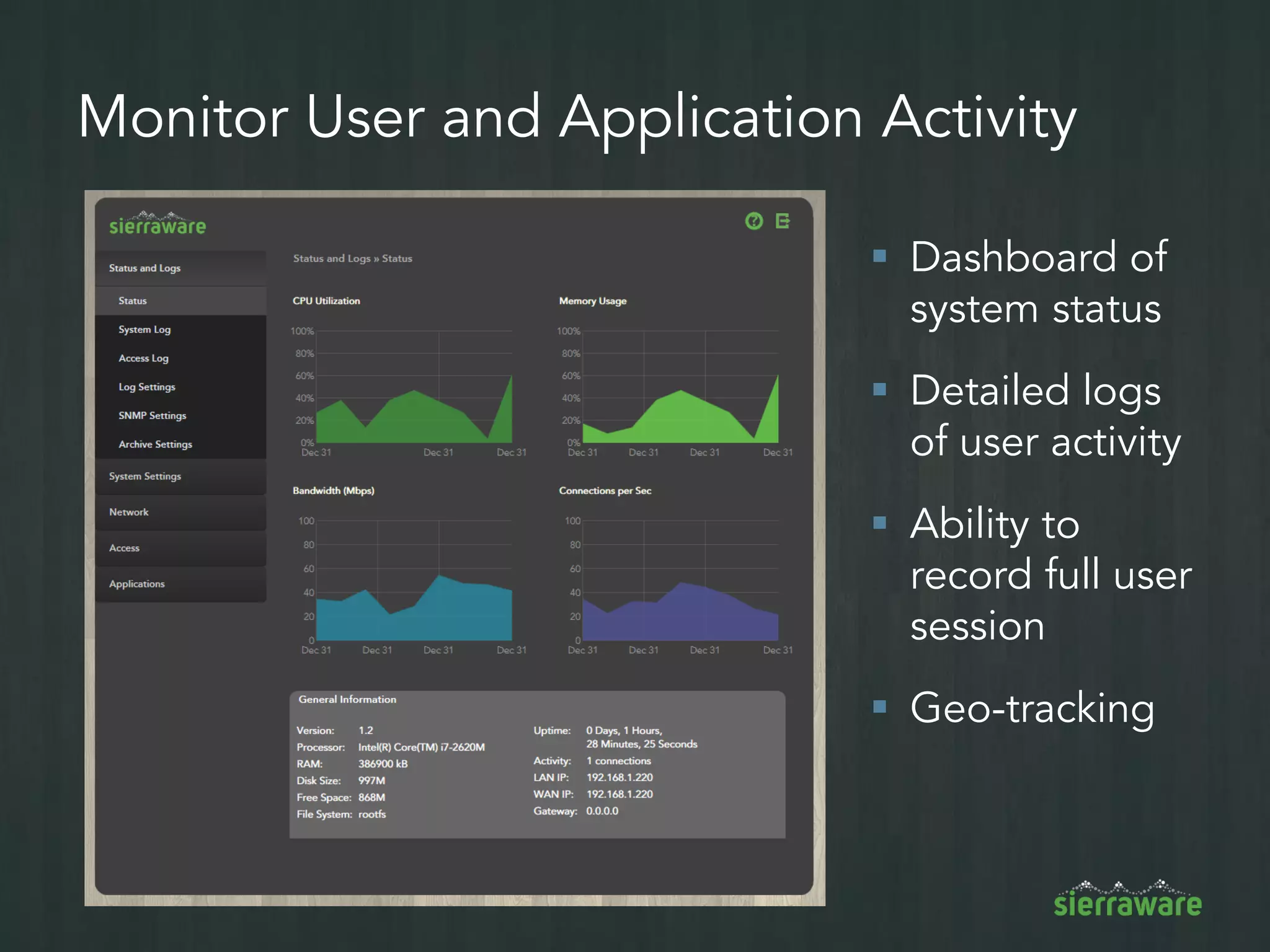
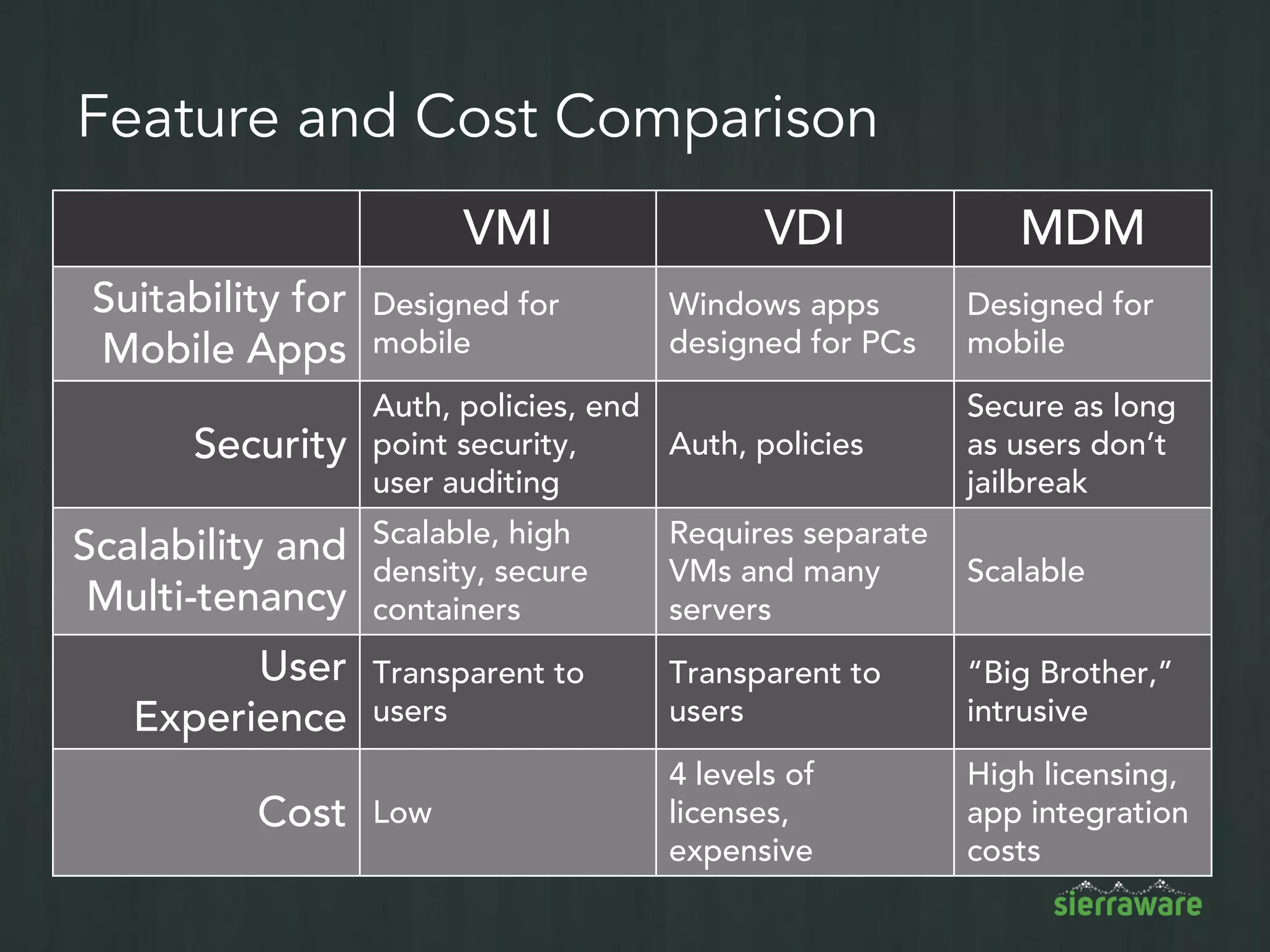
The document discusses the benefits of Virtual Mobile Infrastructure (VMI) as a solution for organizations implementing Bring Your Own Device (BYOD) policies, highlighting its efficiency in managing mobile applications while ensuring security. It outlines the risks associated with mobile devices and emphasizes VMI's capabilities, such as centralized app management, strong authentication, and compliance with regulations like HIPAA. Additionally, it details the architecture and features of its SIERRA VMI service to enhance mobile security and reduce costs.