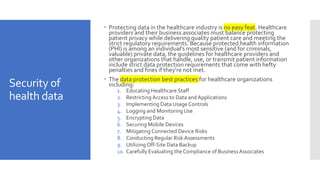
The document discusses the critical components of health informatics related to information privacy, security, ethics, and bioinformatics. It emphasizes the importance of protecting health data through various means such as confidentiality, integrity, and availability, while outlining practical security measures that healthcare organizations should implement. Additionally, it addresses the role of education, access controls, risk assessments, and technology in enhancing the security of healthcare information systems.