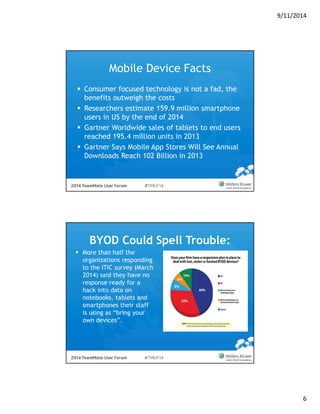
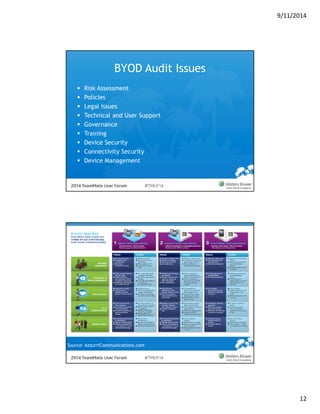
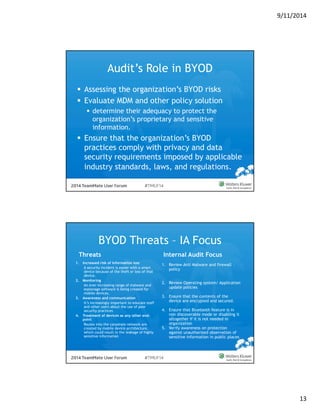
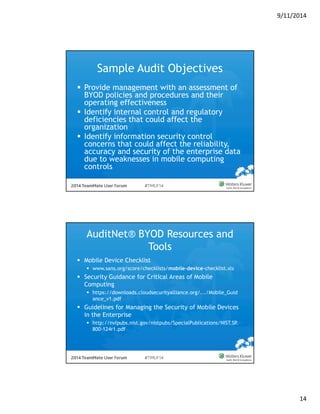
The document provides a comprehensive guide on Bring Your Own Device (BYOD) policies and mobile device management (MDM) for organizations, detailing their risks, internal audit considerations, and controls. It highlights the growing prevalence of BYOD in workplaces, including statistics on employee usage and survey findings related to organizational policies on mobile devices. Additionally, it emphasizes the need for audits, risk assessments, and comprehensive policies to ensure data security and compliance amidst the increasing use of personal devices in professional settings.