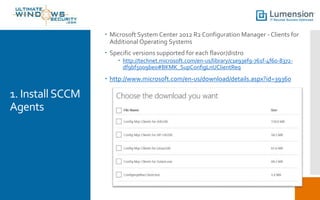
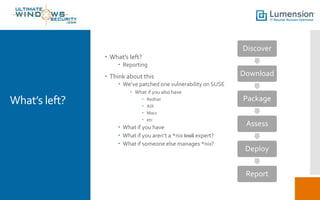
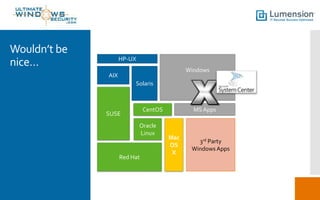
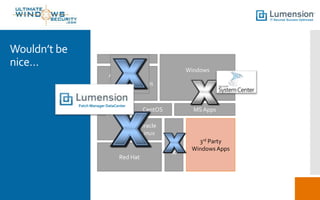
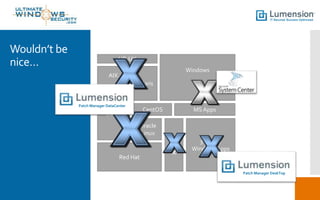
The document discusses the use of System Center Configuration Manager 2012 R2 for patching Linux, Unix, and Mac systems in a compliant and secure manner. It outlines an 8-step process for patch management including installation of SCCM agents, patch selection, and deployment, while emphasizing the need for unified reporting and compliance across various operating systems. Additionally, it highlights the limitations of current manual patching processes and the need for a centralized solution that integrates functionality for diverse systems.