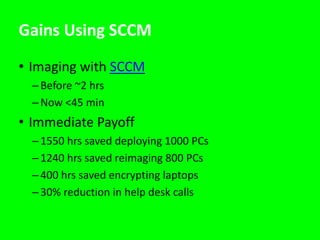
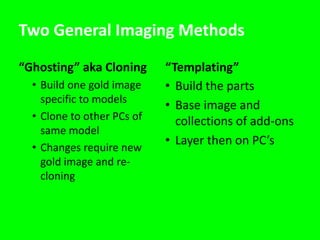
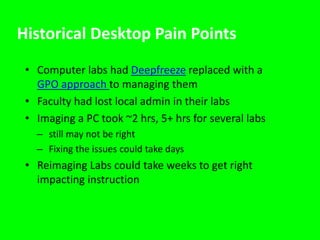
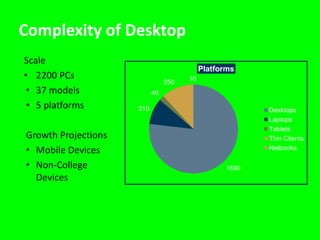
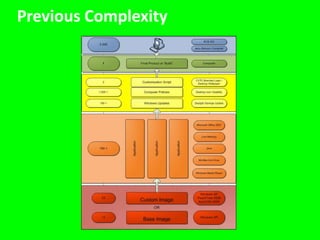
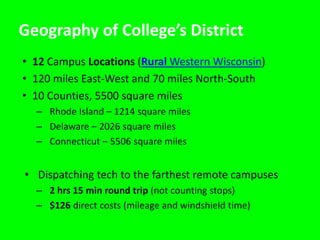
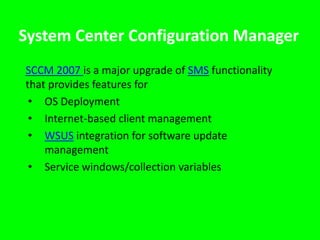
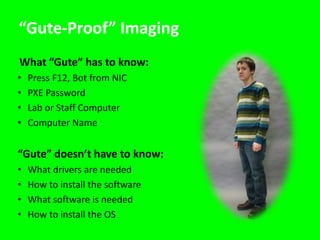
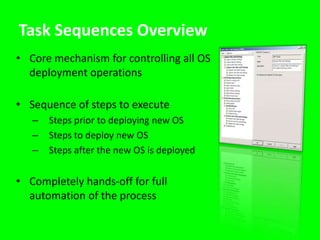
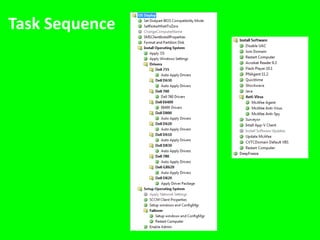
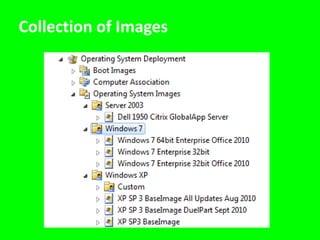
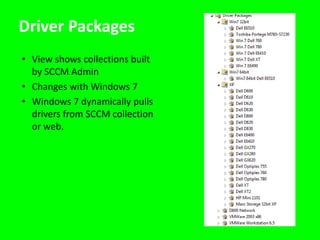
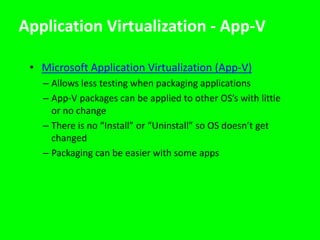
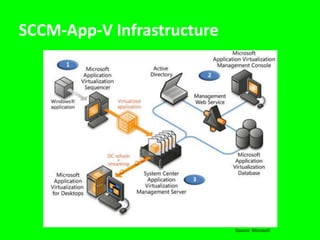
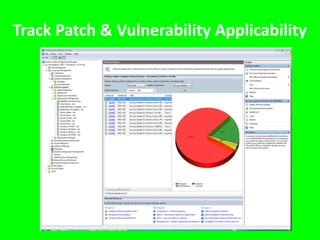
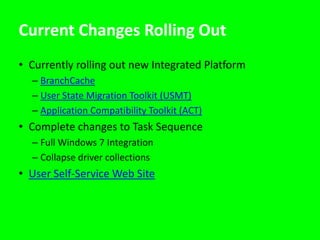
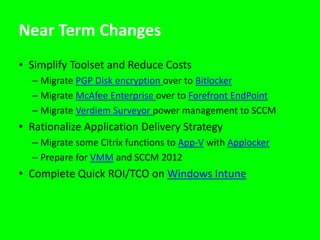
The document discusses how a college enhanced its desktop imaging and management strategy using Microsoft’s System Center Configuration Manager (SCCM) to boost user satisfaction and lower support costs. Key improvements include a significant reduction in imaging time, help desk calls, and overall support demand through automation and simplified processes. The presentation outlines the transition to a more efficient desktop management system, highlighting the advantages of SCCM in managing applications and updates.