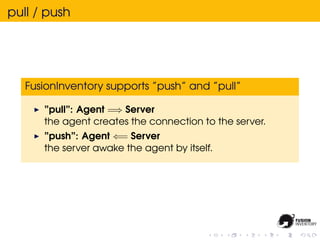
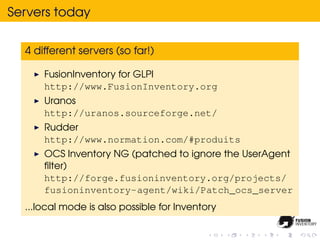
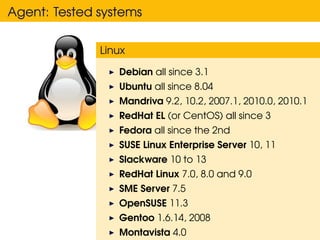
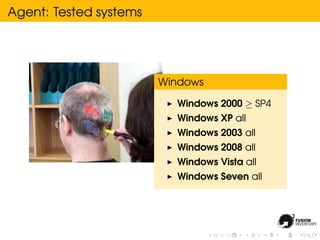
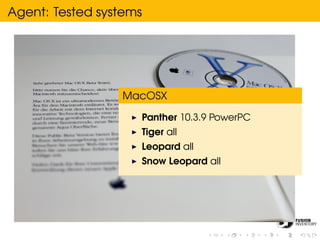
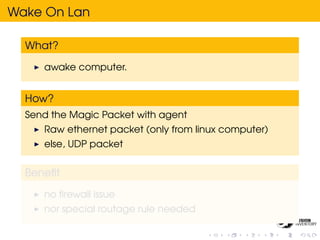
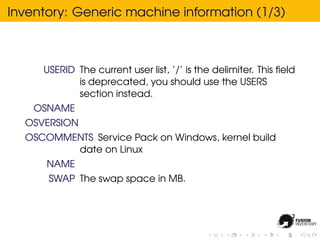
FusionInventory is an open source project that allows for asset management through the use of agents installed on endpoints that report inventory and status information to servers. It supports a wide range of operating systems and can perform network discovery, remote SNMP inventory, software deployment, and wake on LAN functions. The agent is installed directly on endpoints while servers integrate with asset management systems like GLPI. Installation of both the agent and servers is straightforward.





![Why JSON (1/2)
GET http : / / s r v /? action=getConfig&machineid=foobar
{
” httpd ” : {
” ip ” : ” 0 . 0 . 0 . 0 ” ,
” trust ” : [
”127.0.0.1”
],
” port ” : 62354
}
}](https://image.slidesharecdn.com/fusioninventory-rmll-2011-110711171403-phpapp01/85/Fusioninventory-rmll-2011-96-320.jpg)