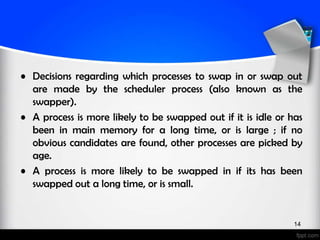
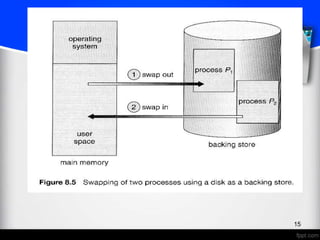
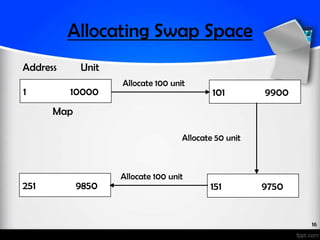
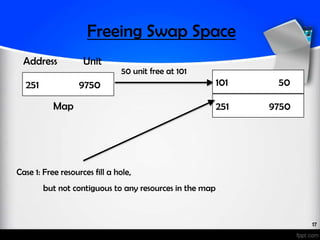
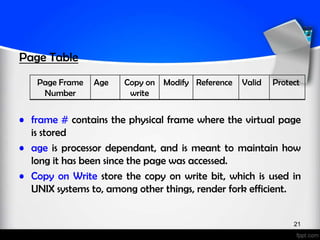
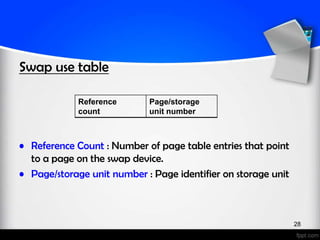
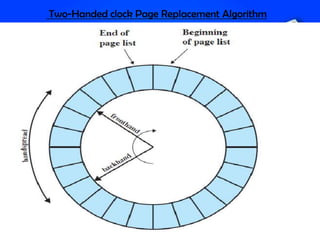
This document provides an overview of UNIX memory management. It discusses the history of UNIX and how it evolved from earlier systems like Multics. It describes swapping as an early technique for virtual memory management in UNIX and how demand paging was later introduced. Key concepts discussed include page tables, page replacement algorithms like two-handed clock, and the kernel memory allocator.