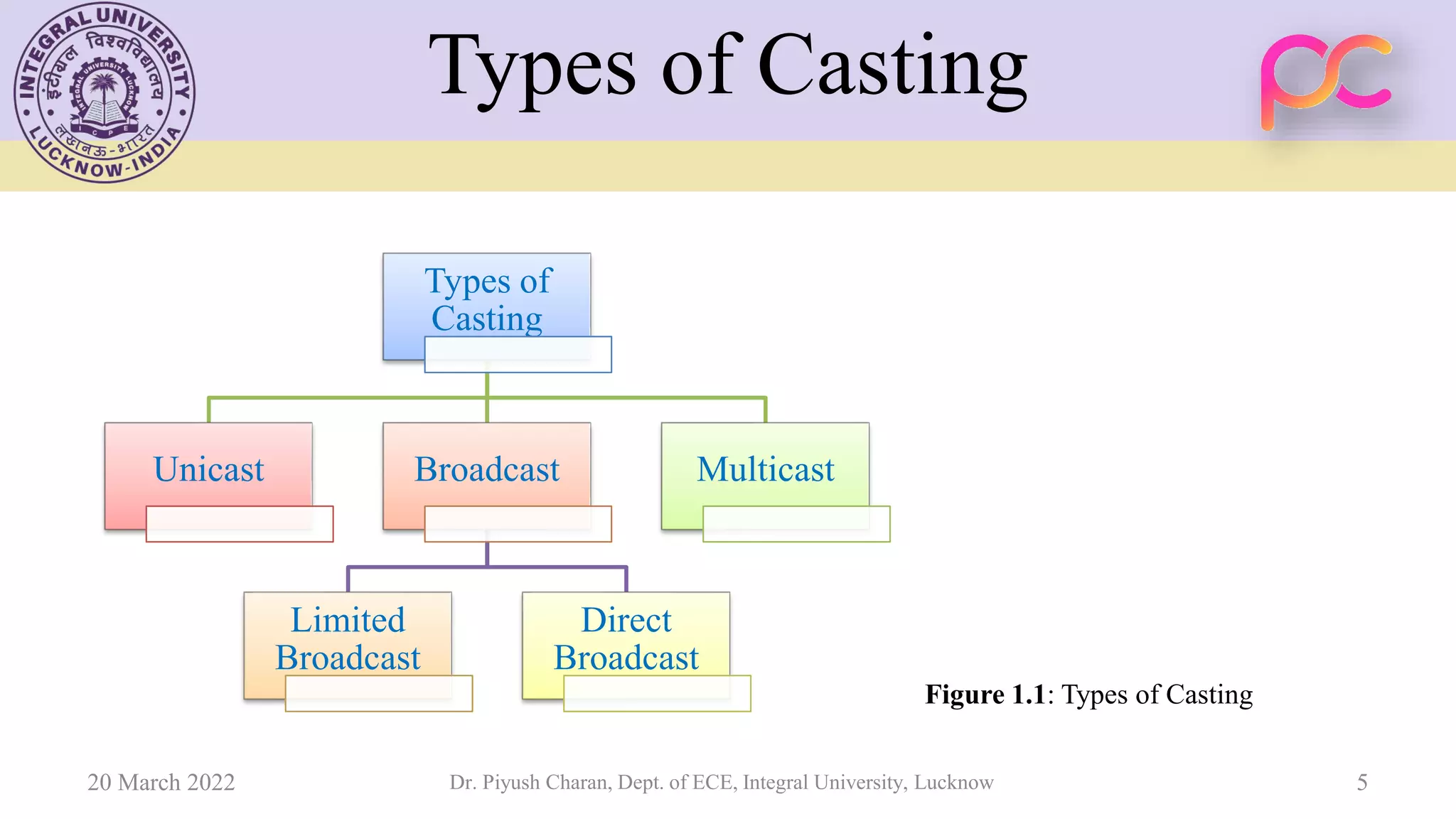
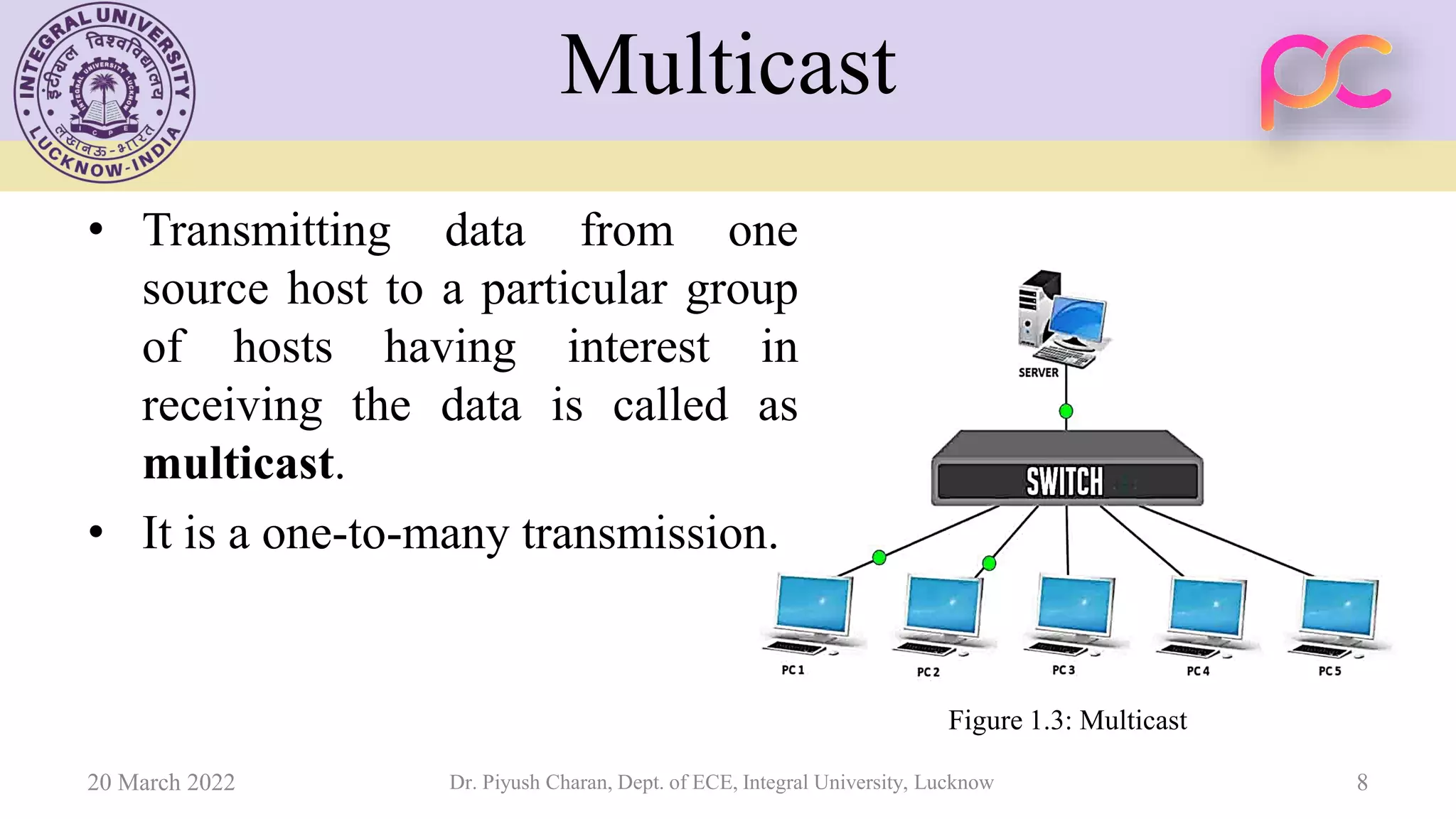
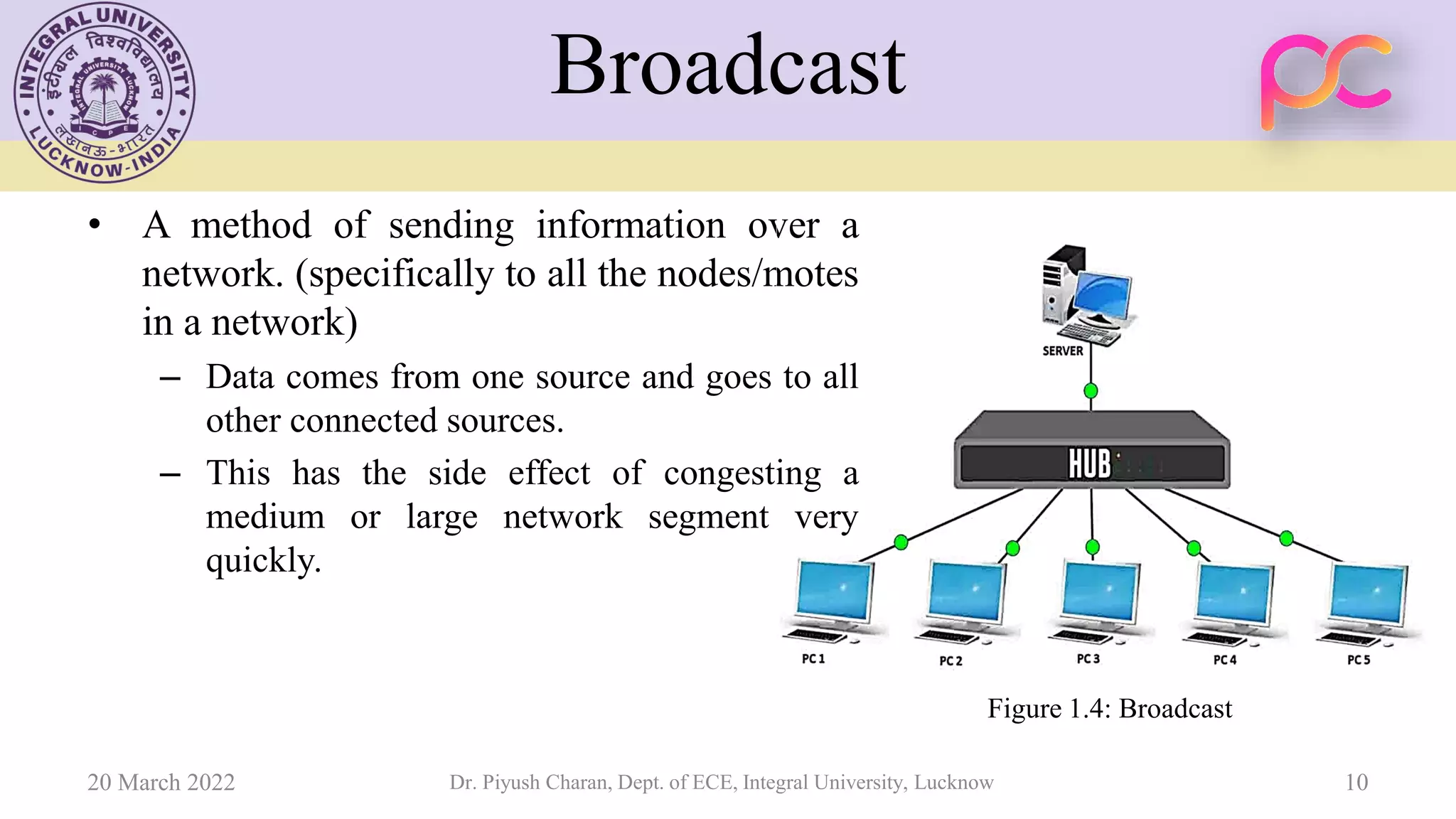
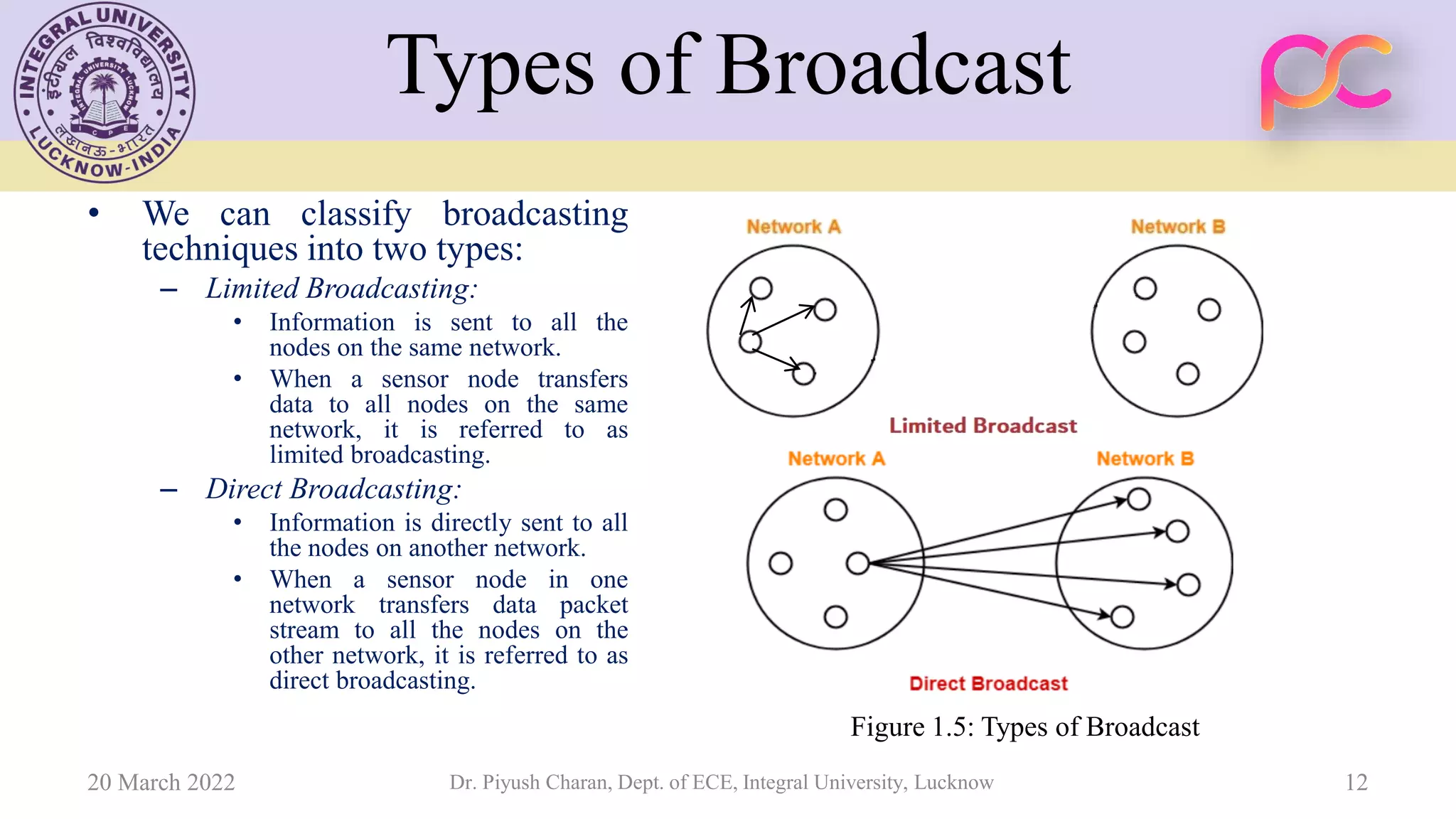
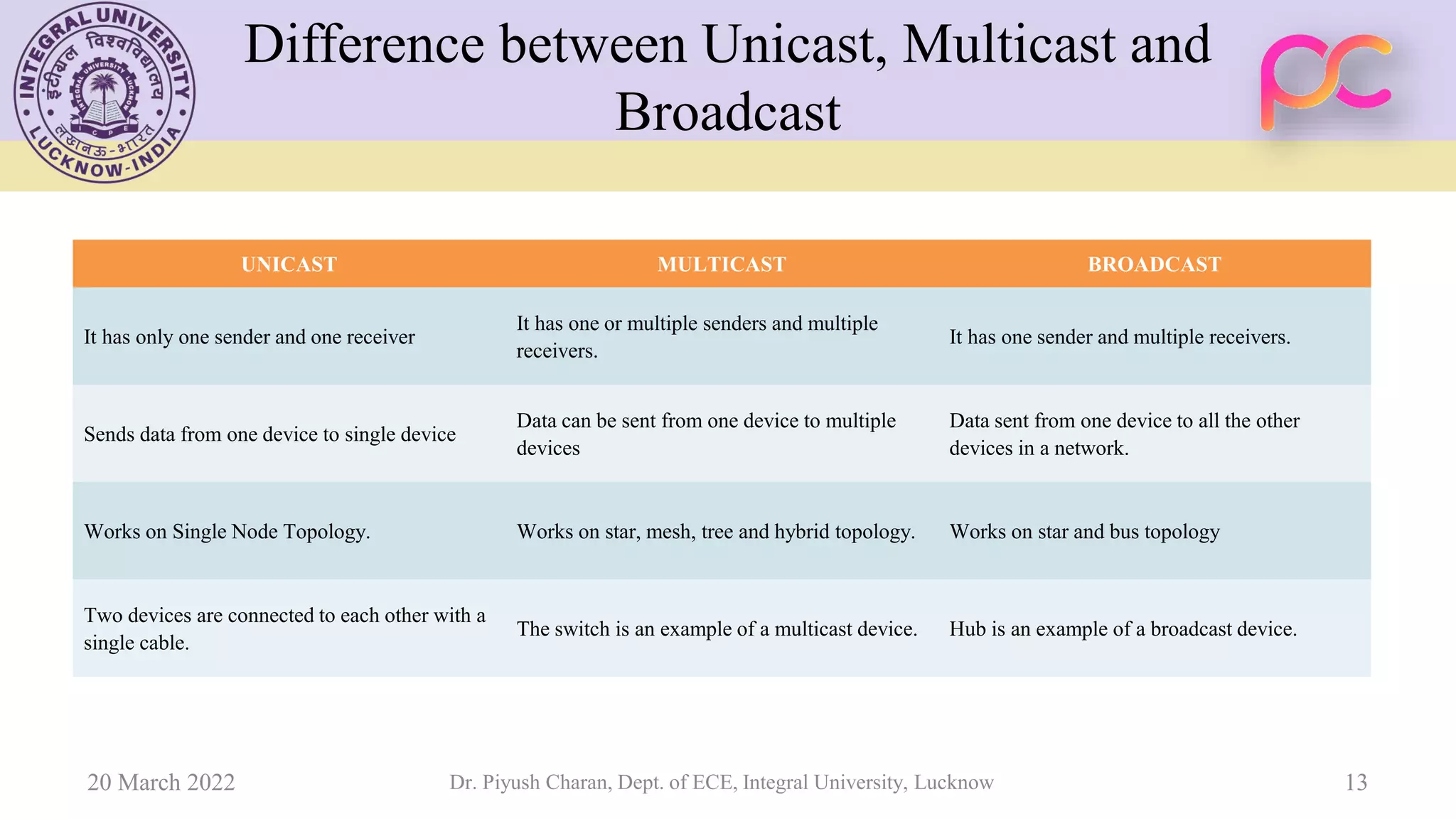
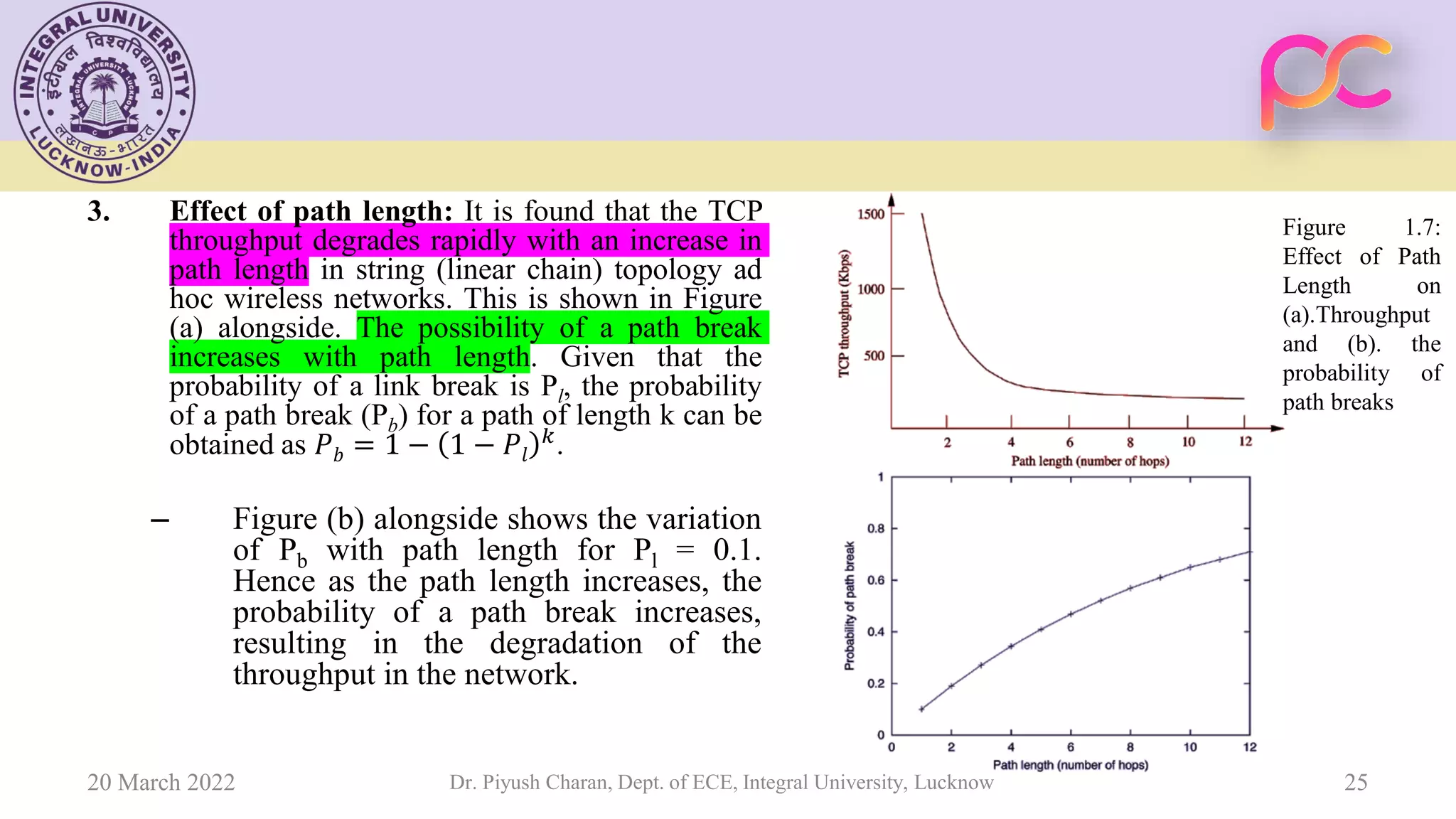
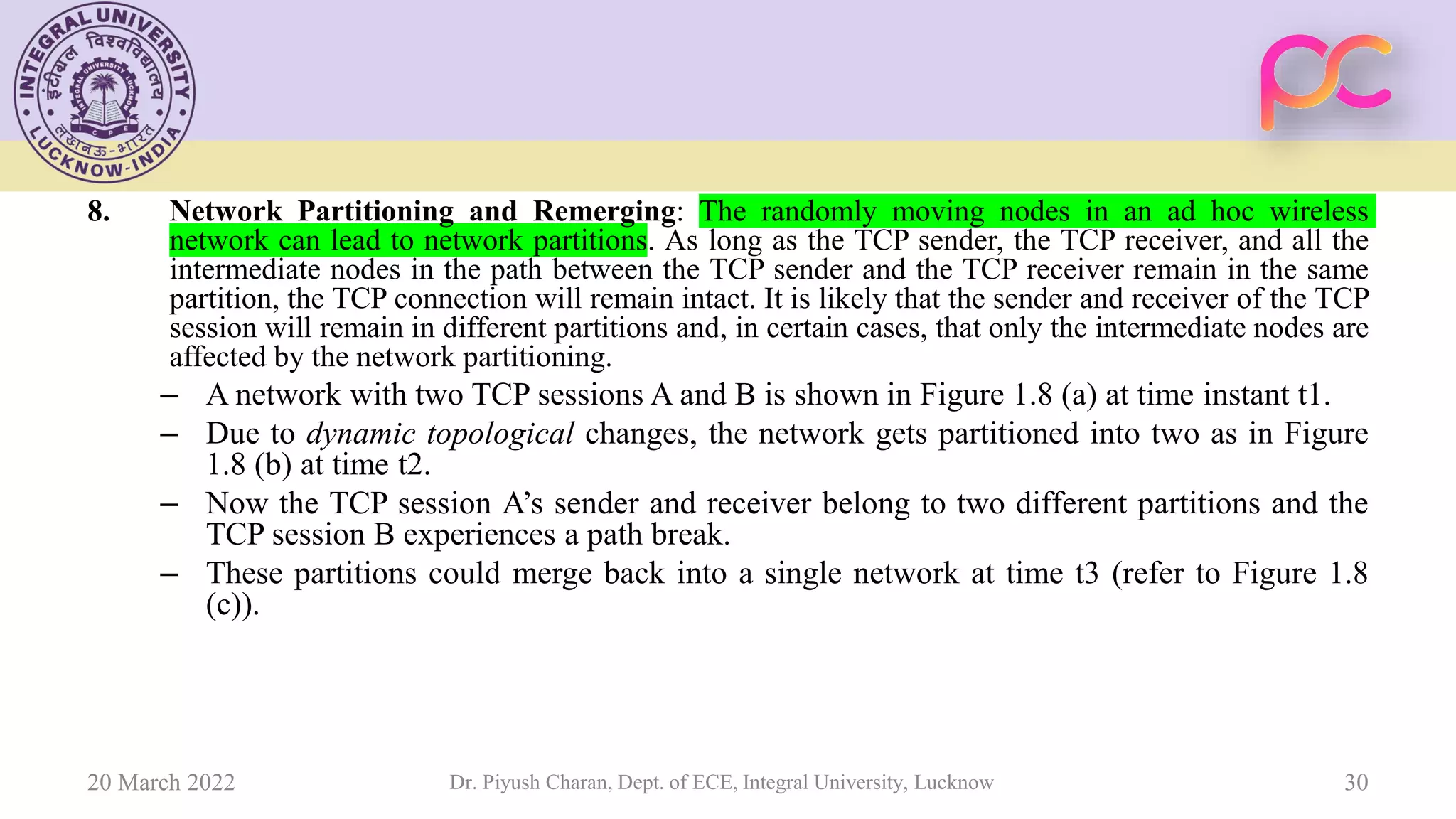
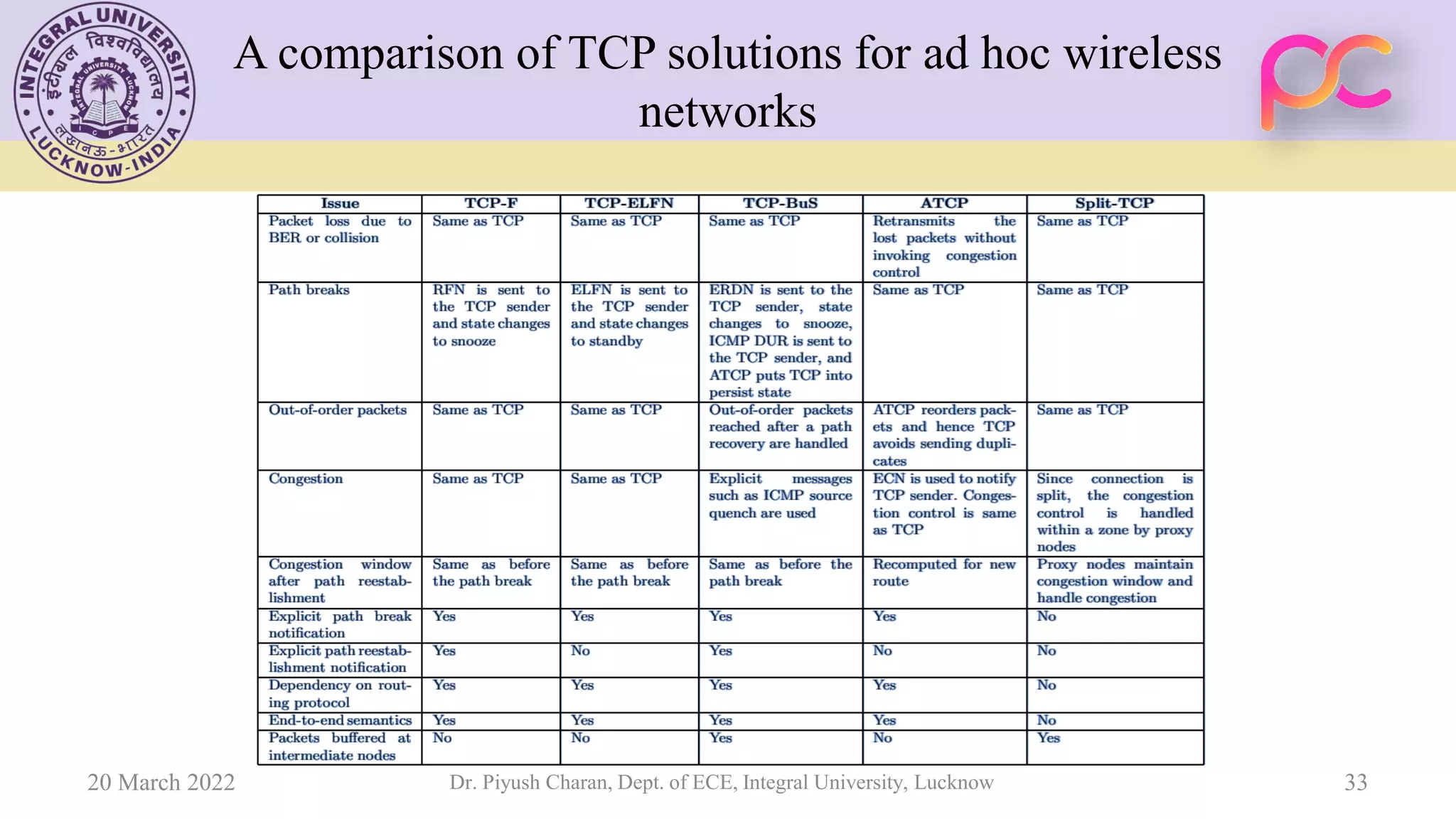
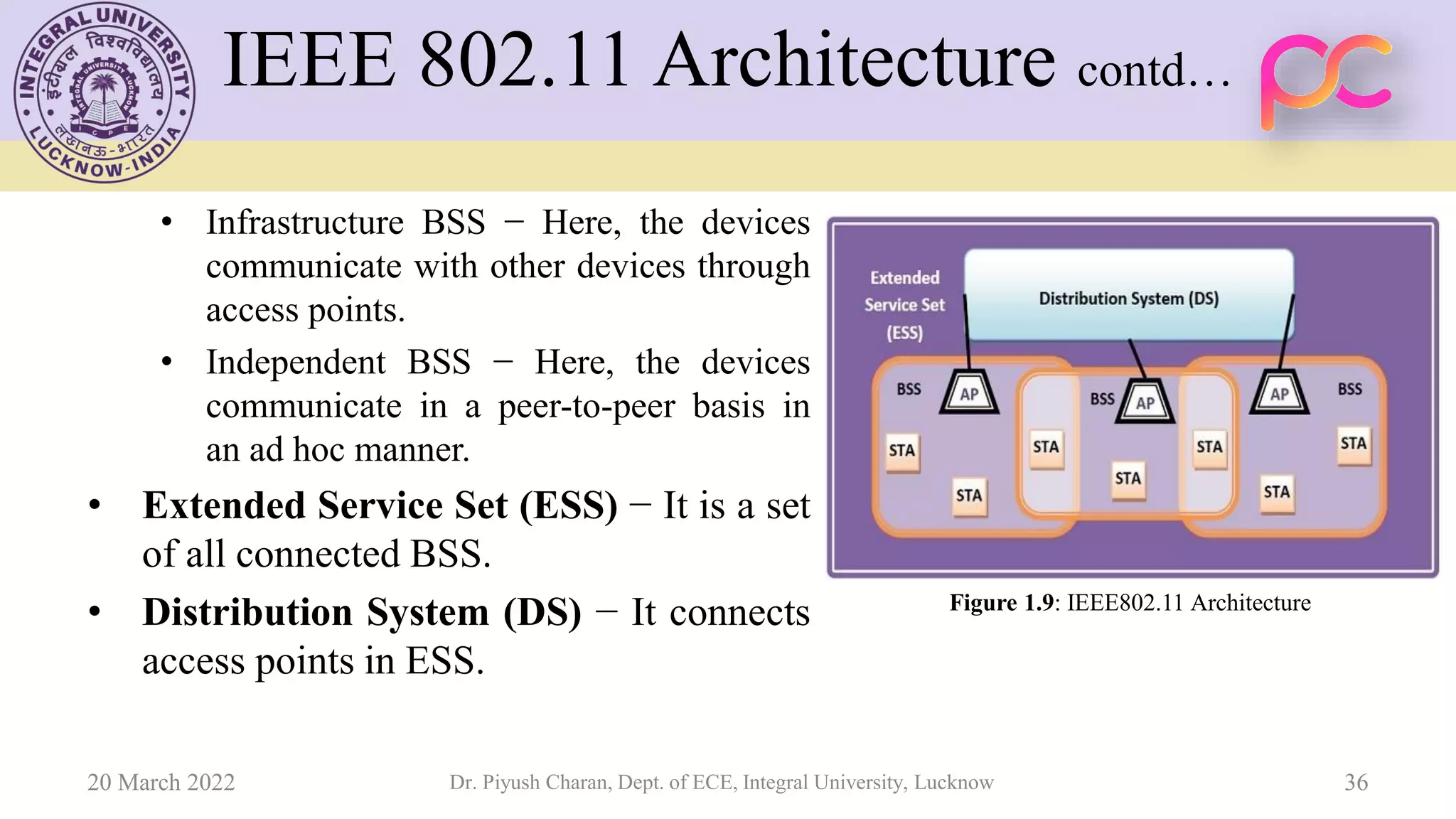
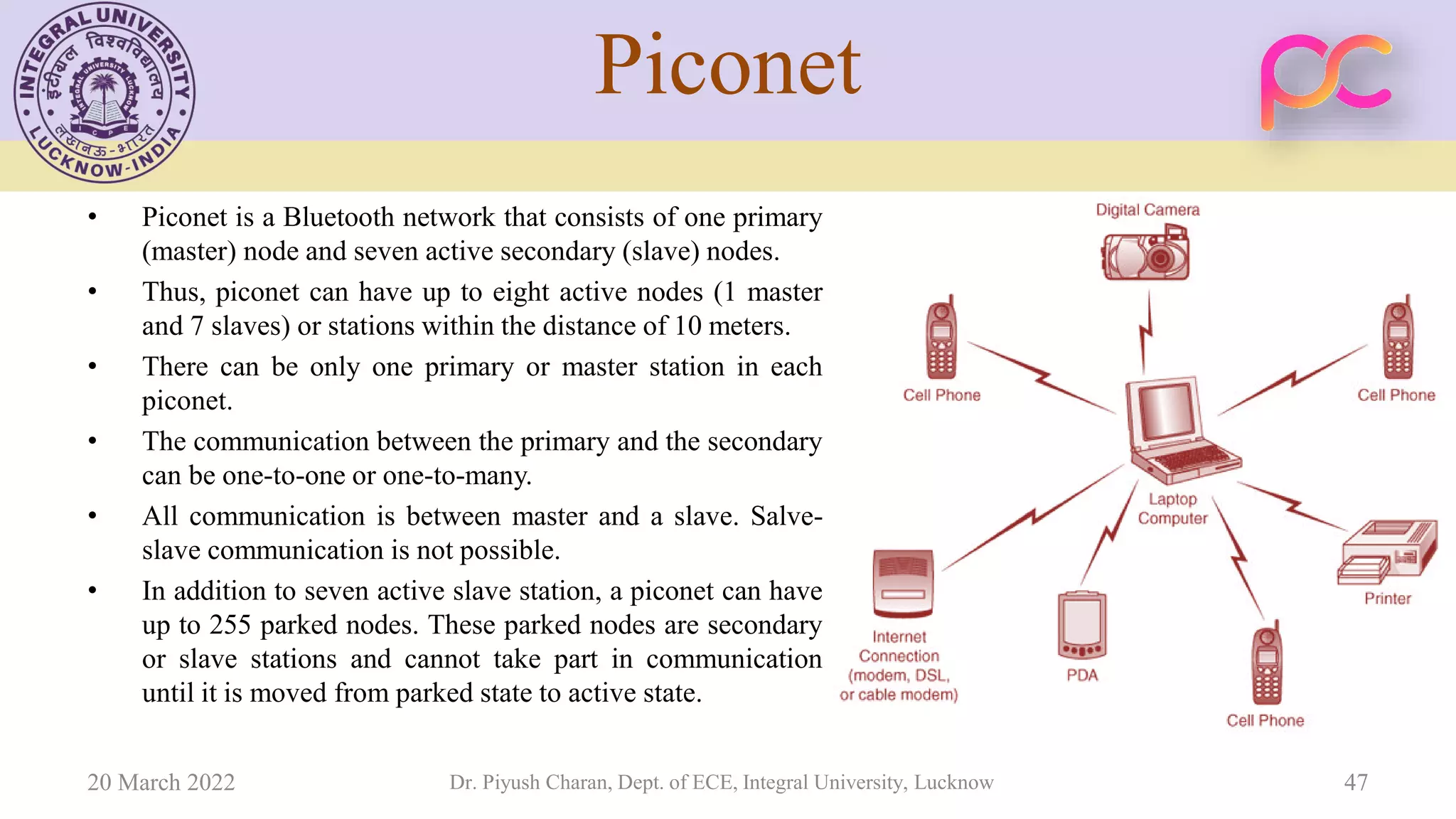
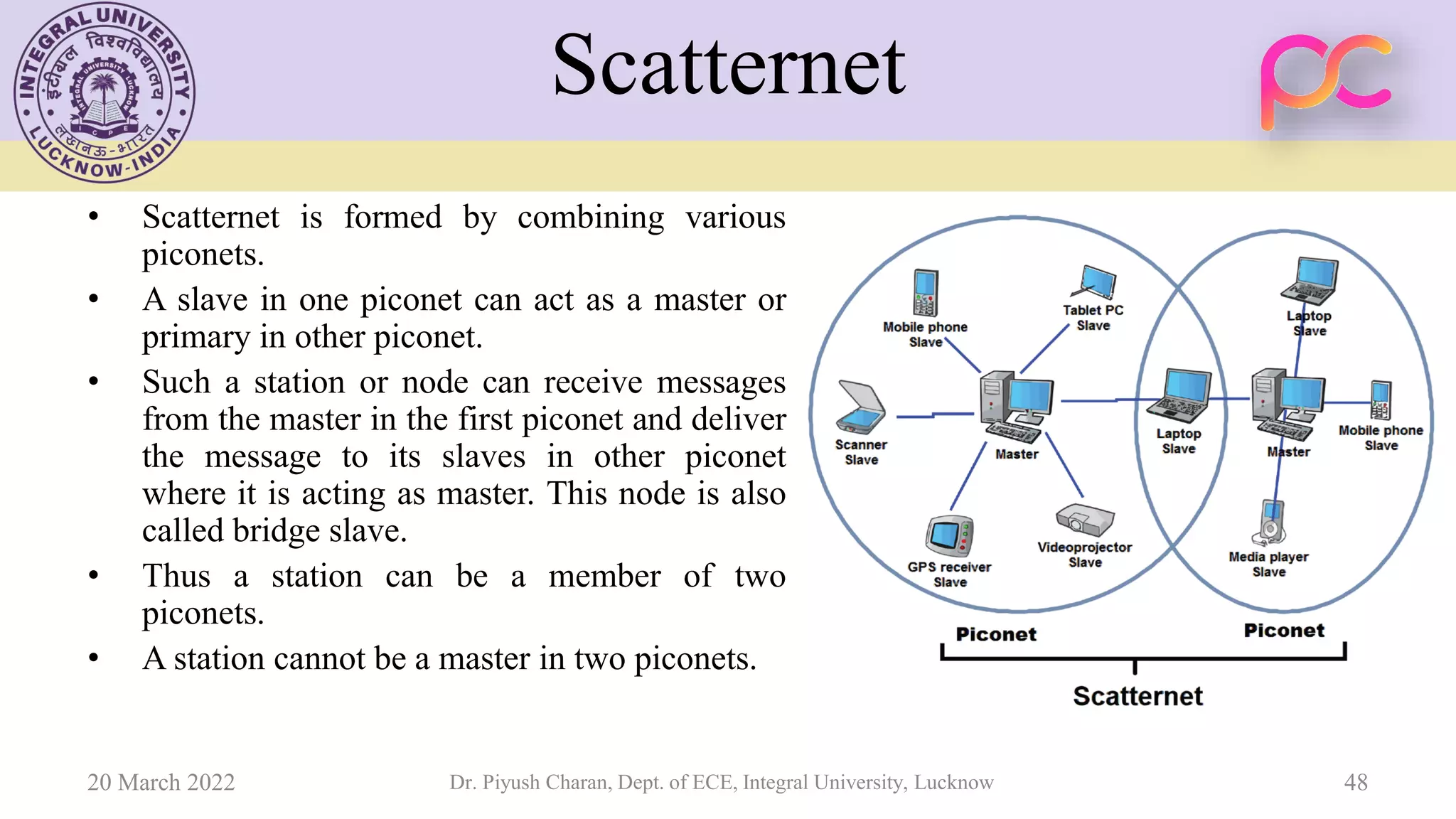
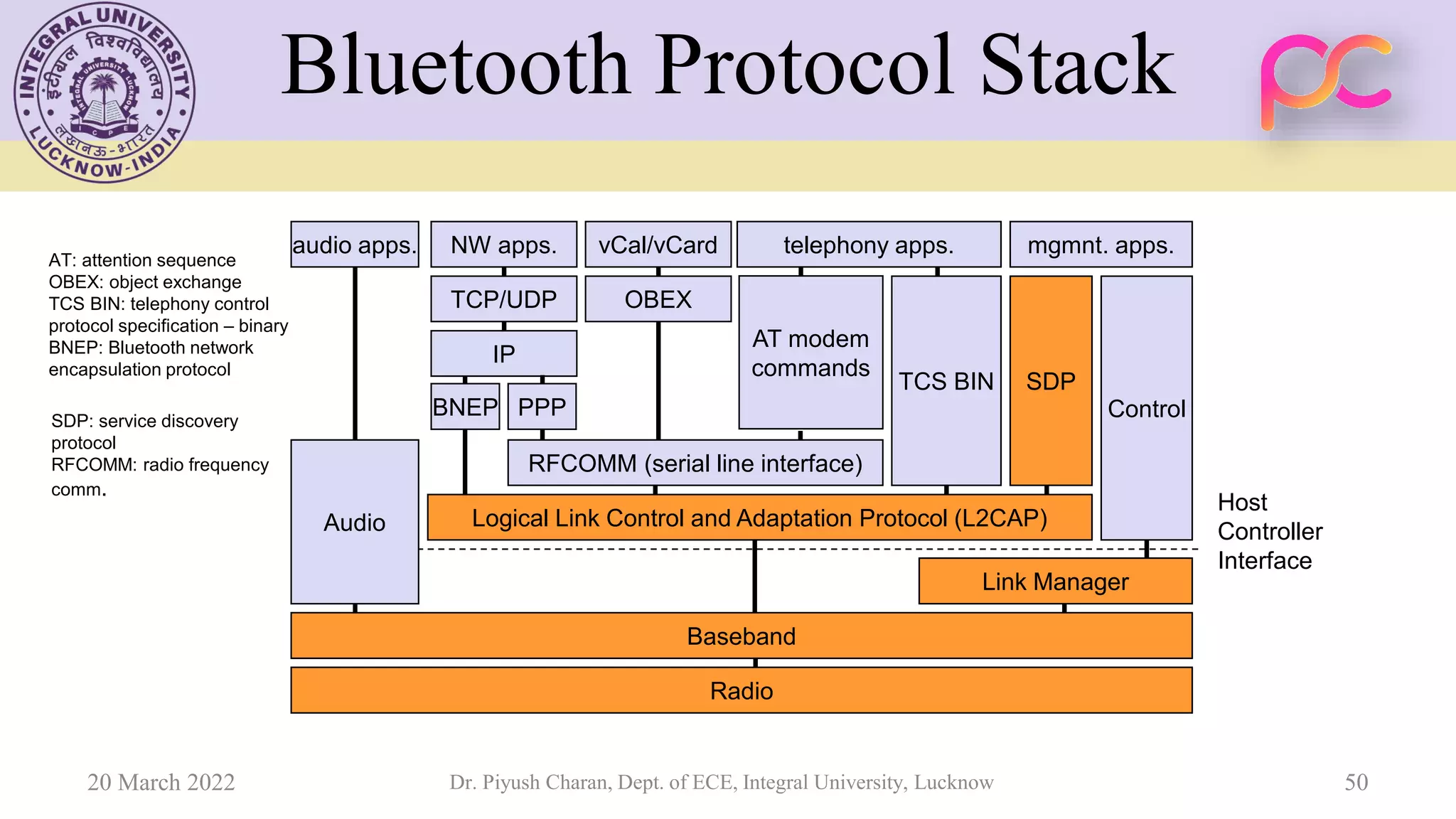
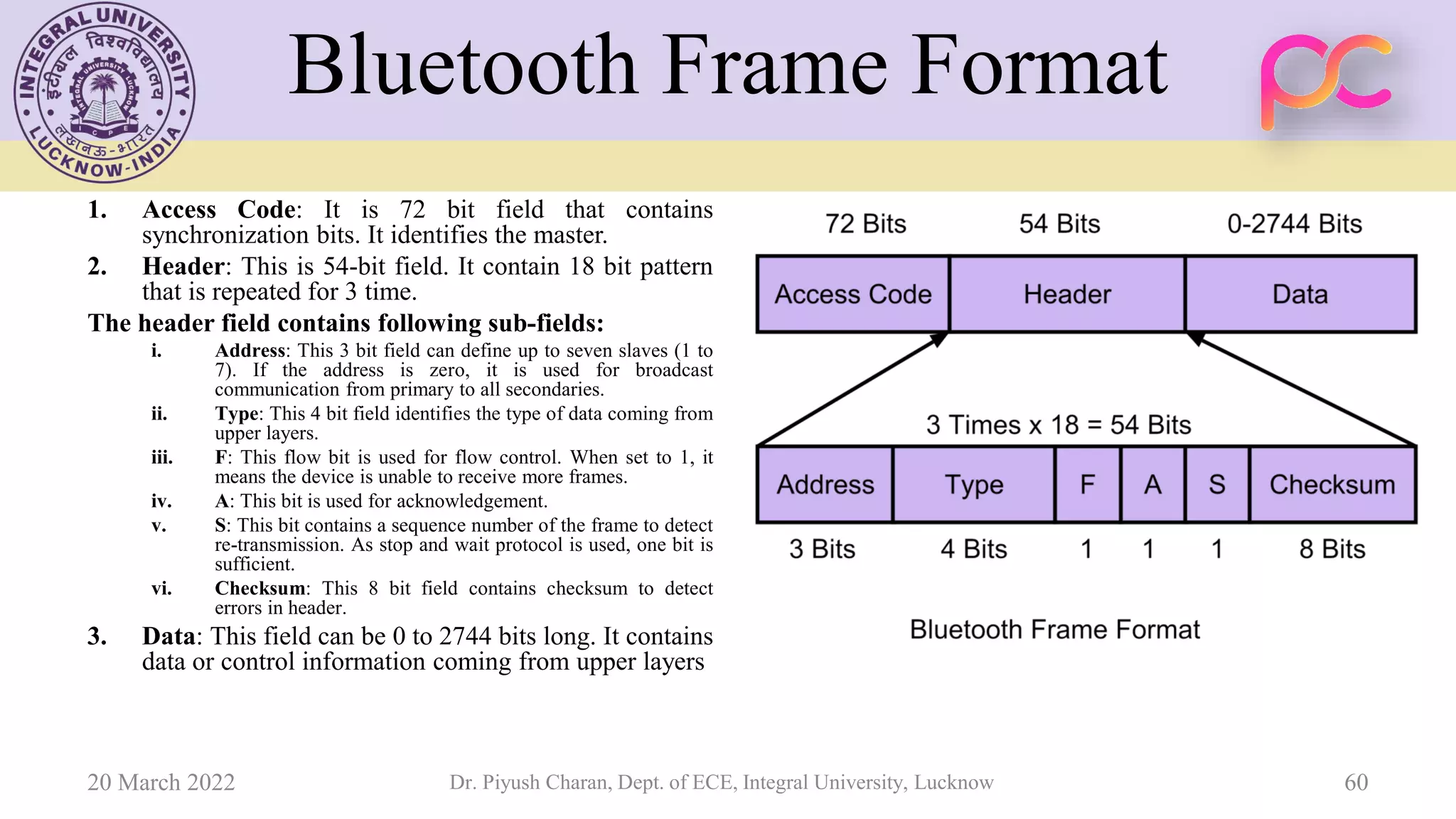
This document provides lecture notes on wireless standards for mobile ad-hoc and sensor networks. It covers topics such as broadcasting and multicasting, including issues like broadcast storms and network flooding avoidance. It also discusses TCP over mobile ad hoc networks, addressing challenges from mobility and network partitions. Additional sections cover wireless LAN specifications and protocols, Bluetooth specifications and operations, and casting techniques such as unicast, multicast and broadcast.