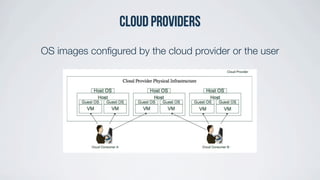
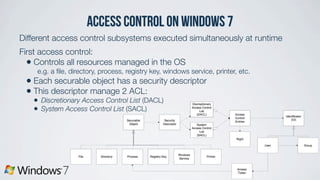
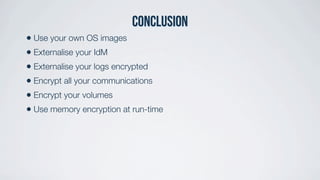
The article analyzes the security measures of Windows 7 and Linux in cloud computing, focusing on aspects such as authentication, authorization, network security, privacy, and encryption. It emphasizes the importance of using personal OS images and externalizing identity management and logs for enhanced security. The authors criticize current practices and suggest improvements, highlighting the need for robust security measures in Infrastructure as a Service (IaaS) environments.
















![Criticisms
• “IaaS cloud provider use different solutions such as Openstack, Cloudstack,
Amazon EC2 [...]”
Amazon EC2 is a IaaS cloud provider itself, not a solution for IaaS provider.
• “[...] it requires the cloud provider to allow customers to manage DNS servers
to resolve the hostnames inside the virtual infrastructure.”
Anyone can create and manage their own DNS servers and DNS zones,
customer just needs the possibility to customize DNS reverses.
• Some advises have a limited application (e.g. FireWire, USB, TPM)
• No explanations of the choice of SELinux](https://image.slidesharecdn.com/co899-presentation-vg66-130915095446-phpapp01/85/UKC-Feb-2013-Analyzing-the-security-of-Windows-7-and-Linux-for-cloud-computing-42-320.jpg)

