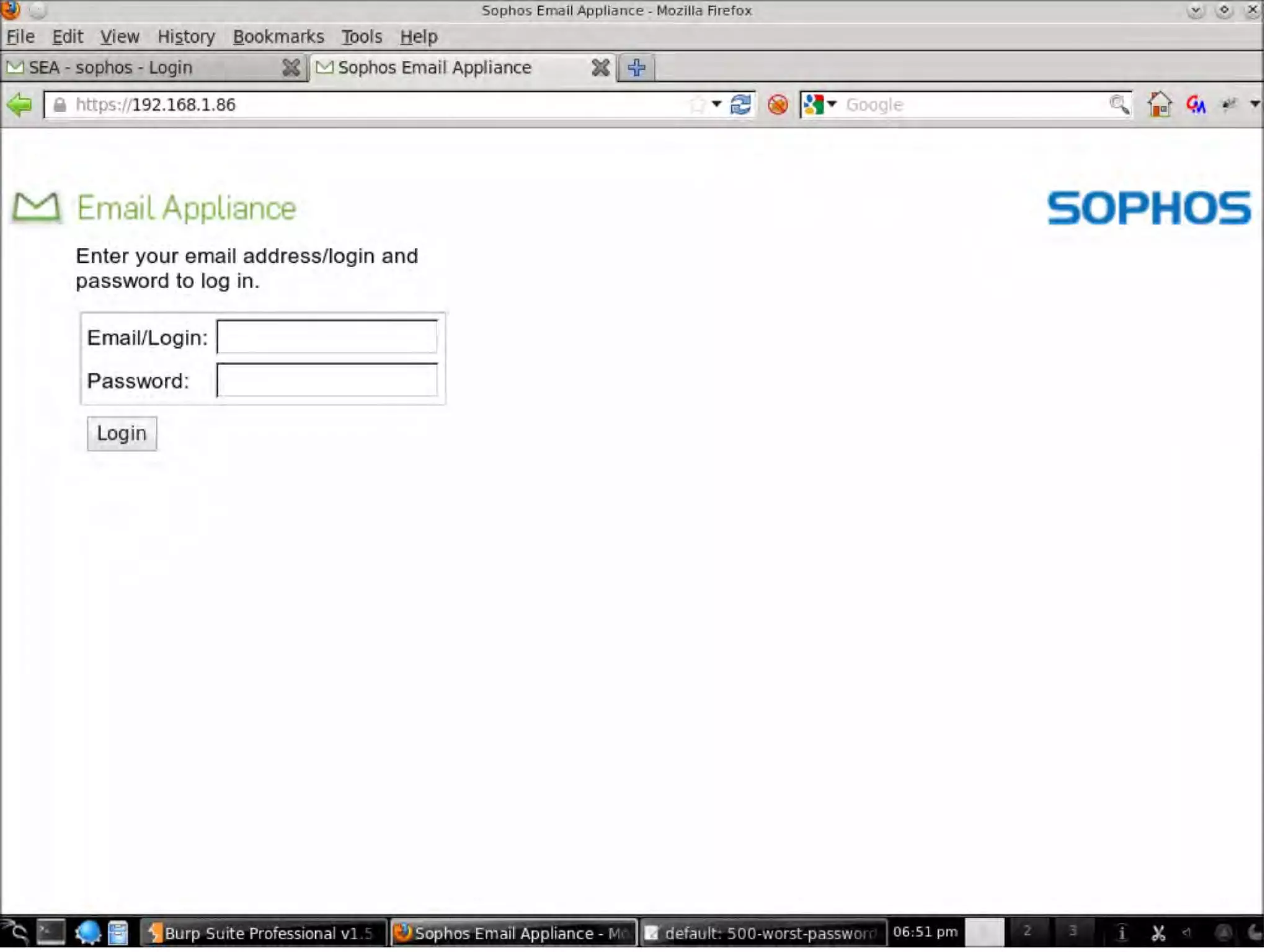
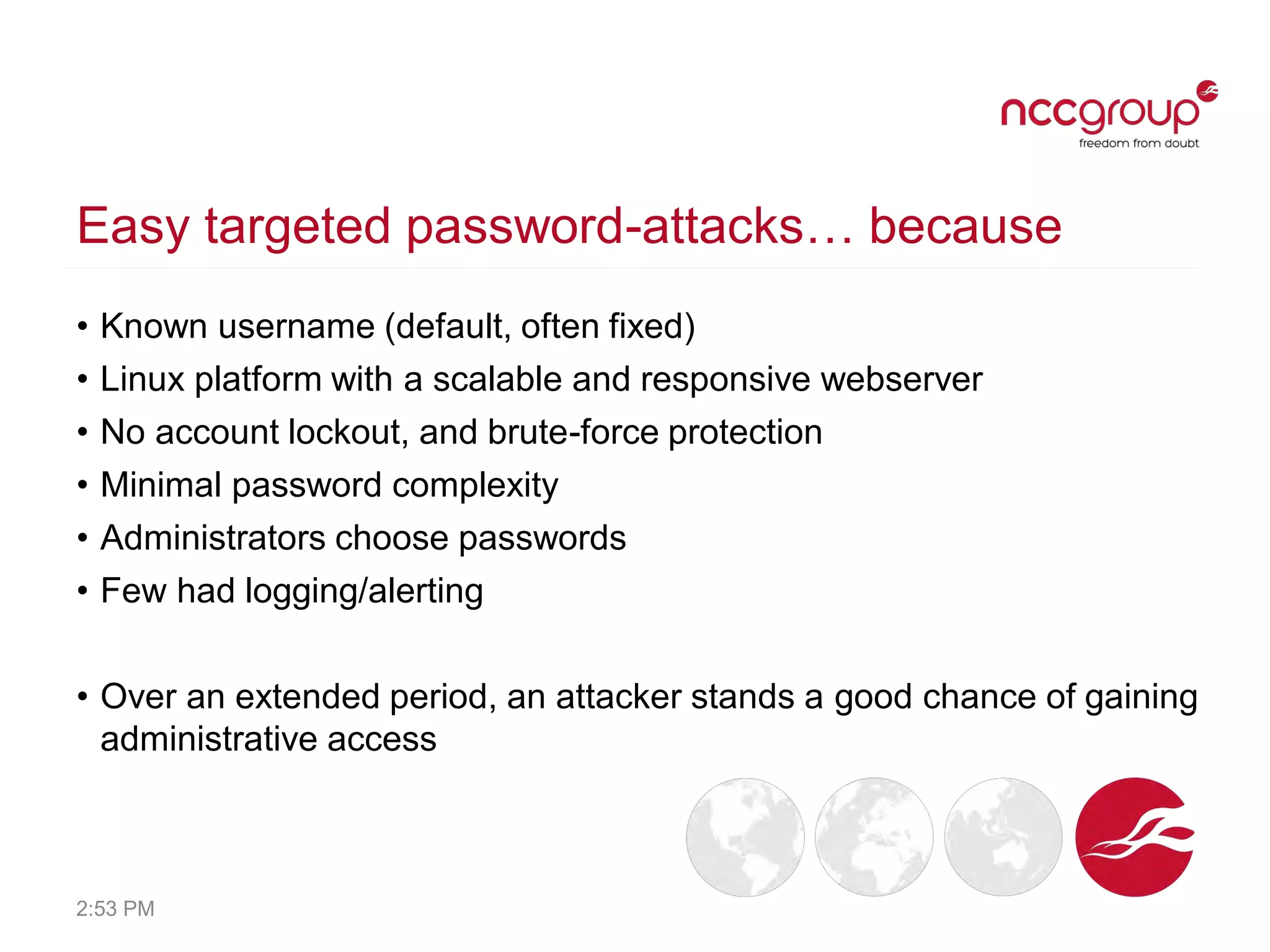
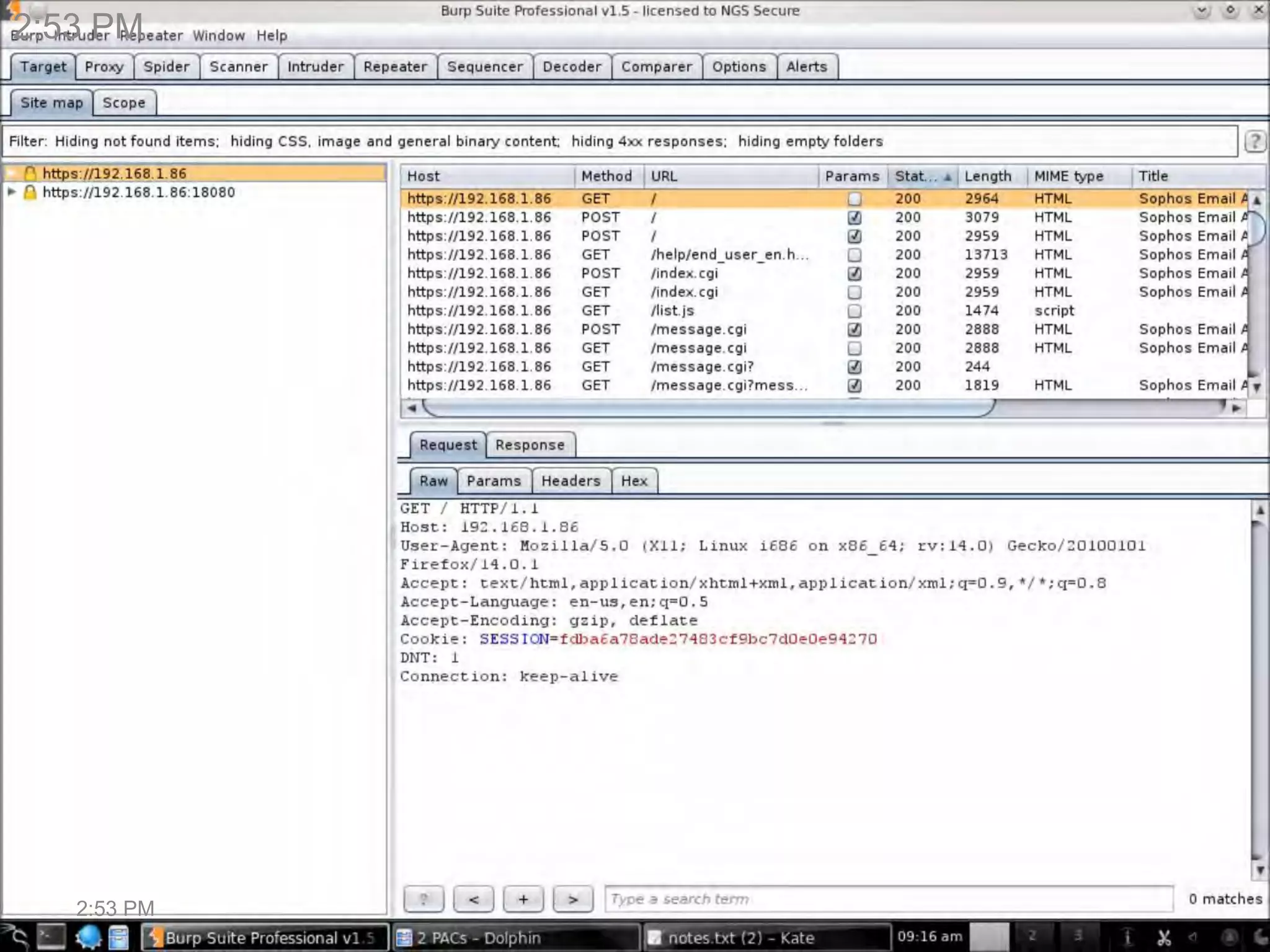
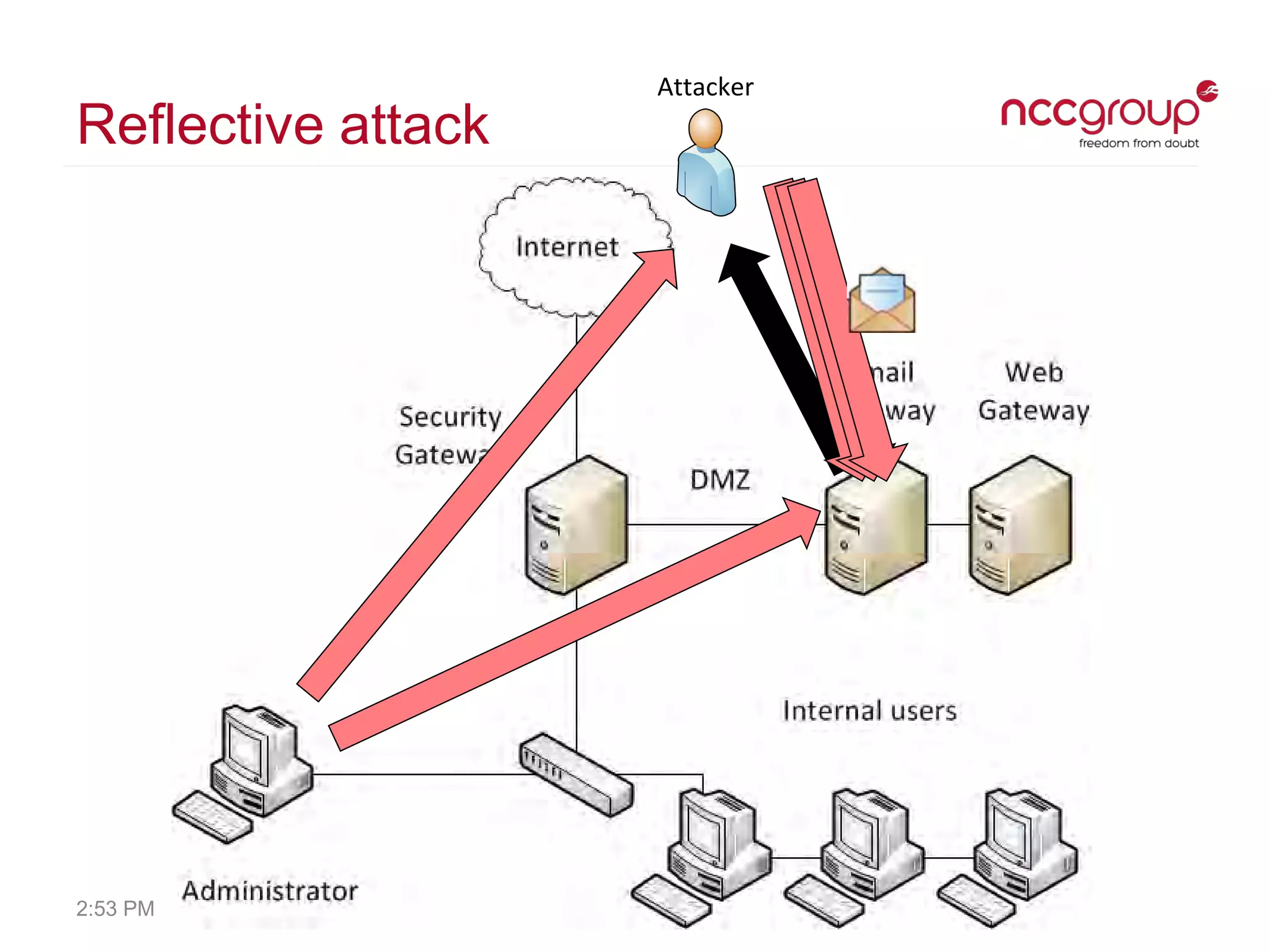
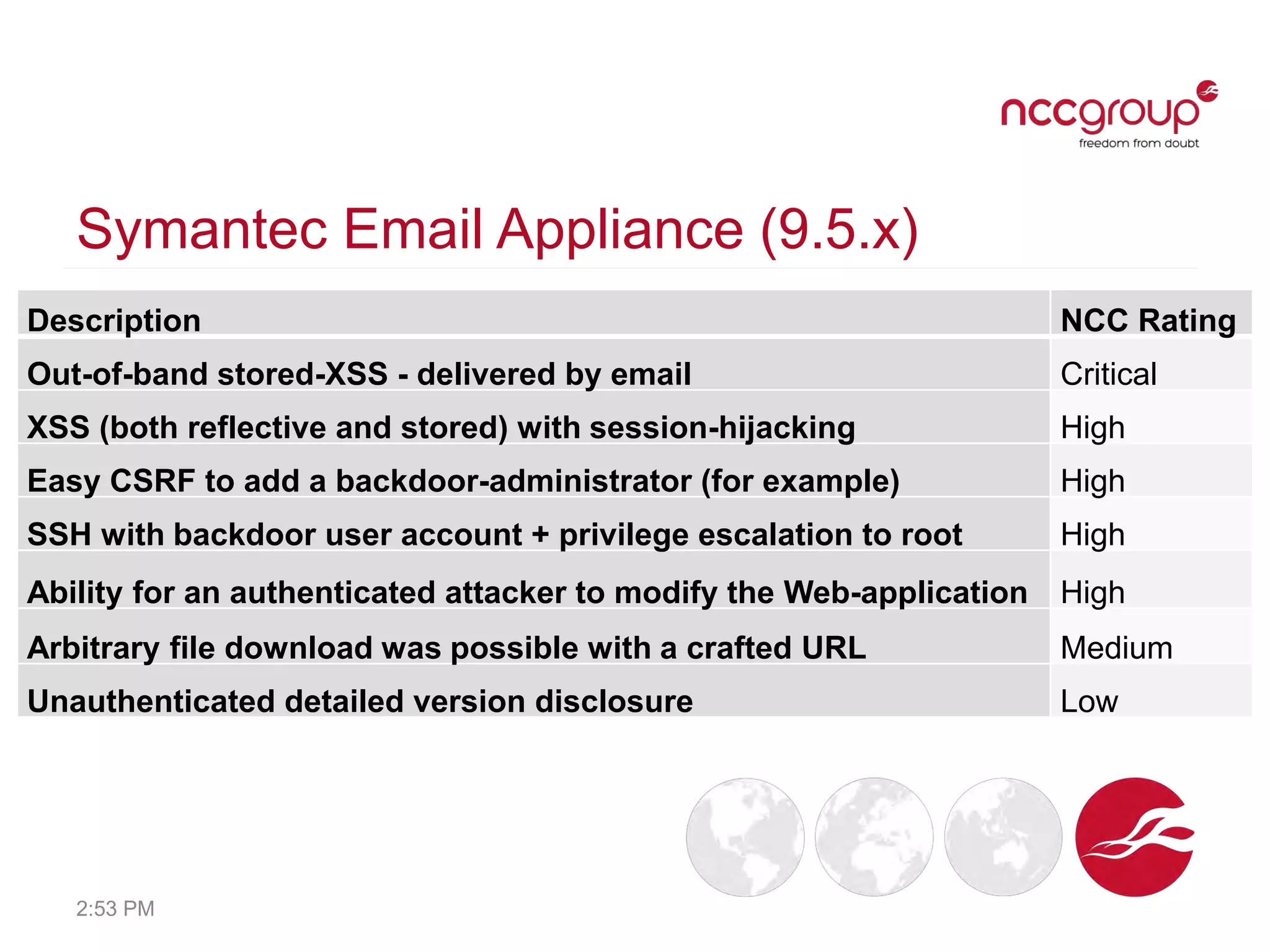
The document discusses security vulnerabilities found in various security appliance products. It describes easy password attacks, cross-site scripting vulnerabilities with session hijacking, lack of account lockouts, and other issues found across email/web filtering, firewall, and remote access appliances from vendors like Barracuda, Symantec, Trend Micro, Sophos, Citrix, and others. Many appliances were found to have command injection flaws allowing root access. Vendors' responses to reported vulnerabilities varied, with some issues getting addressed within months while others saw no fixes. The author advocates defense-in-depth practices and keeping appliances updated with vendor patches.