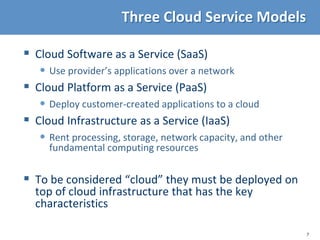
The document provides an introduction to cloud security, including a review of cloud computing, a discussion of common security challenges in cloud environments, and an overview of the top threats to cloud computing. It describes key characteristics of cloud computing like on-demand access and elastic resources, and different cloud service models including infrastructure as a service, platform as a service, and software as a service. Security issues related to virtualization, multi-tenancy, and the use of application programming interfaces are also discussed.






















![25
OS Platform: A Model
OS platform: same for all
applications on a system
E,g,, classical OS kernel
Libraries/frameworks:
packaged code used by
multiple applications
Applications/services.
May interact and serve
one another.
OS mediates access to shared resources.
That requires protection and isolation.
[RAD Lab]
Protection boundary
API
API](https://image.slidesharecdn.com/introcloudsecurity-silver-230308112125-bc0623d6/85/Introduction-to-Cloud-Security-pptx-25-320.jpg)