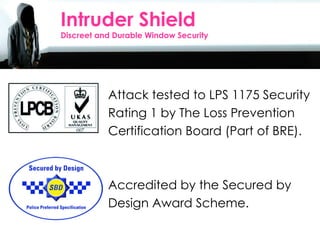
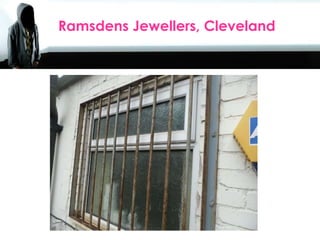
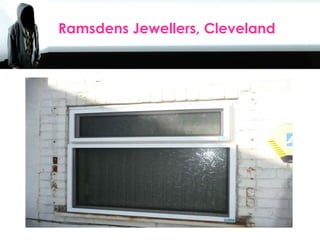
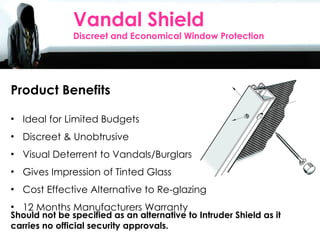
The document outlines various window security solutions that provide discreet, effective protection against vandalism and intrusions. Products like Intruder Shield and Vision Shield offer durable and cost-effective alternatives to traditional security measures, appealing to a wide range of customers such as schools and businesses. A site survey and sample installation are available, with options for extended warranties and payment plans for local authorities.