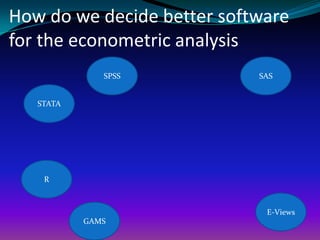
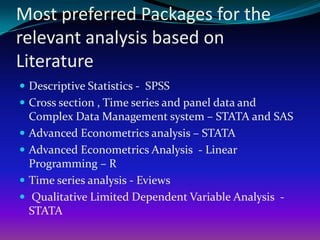
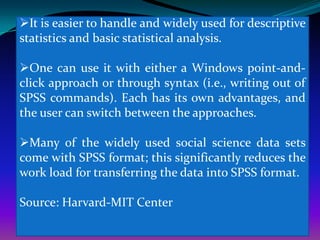
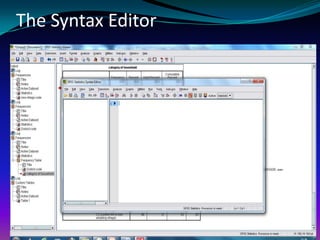
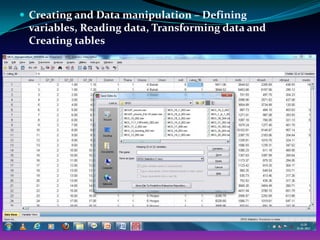
This document provides an introduction to the statistical software packages SPSS and STATA. It discusses why researchers may choose to use each package and highlights some of their key differences and strengths. SPSS is generally best for descriptive statistics and basic analyses, while STATA excels at more advanced econometric techniques and can handle larger datasets. The document also gives overviews of the basic structure and interfaces of each program.