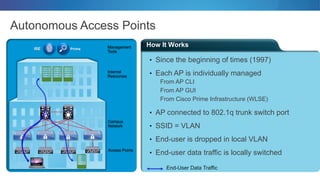
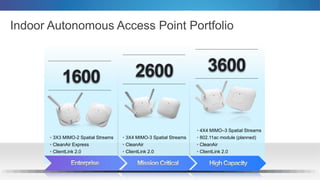
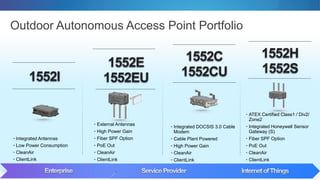
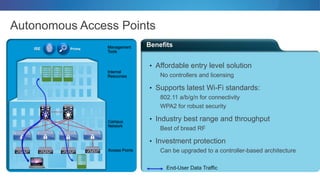
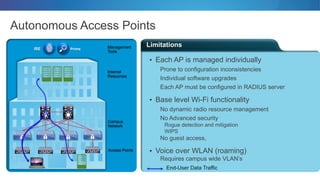
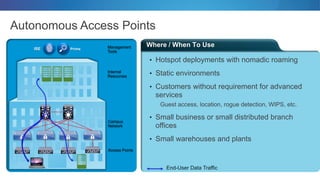
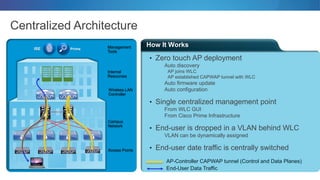
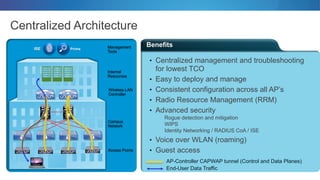
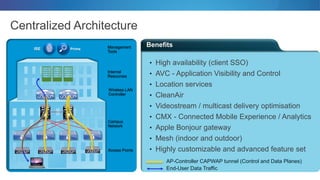
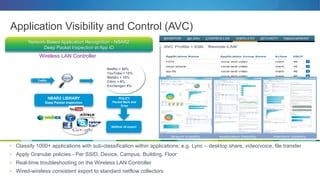
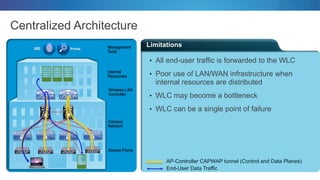
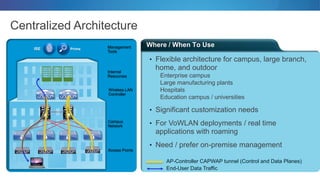
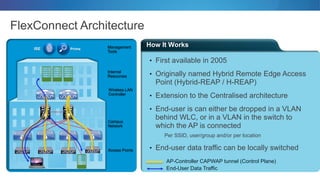
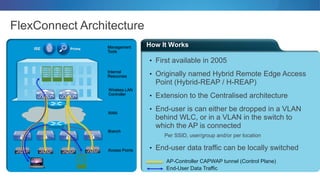
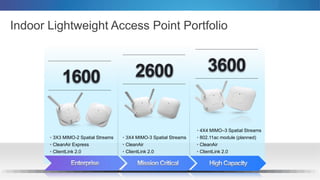
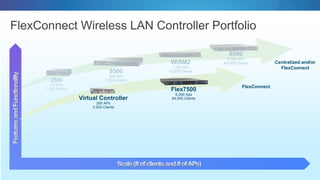
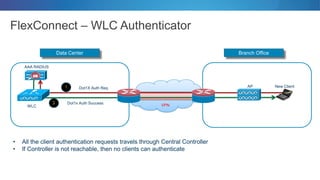
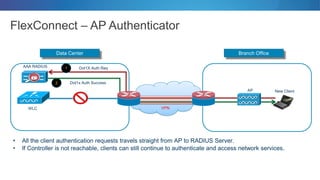
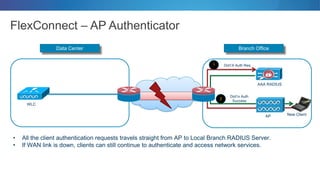
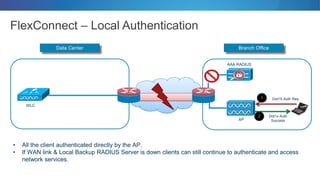
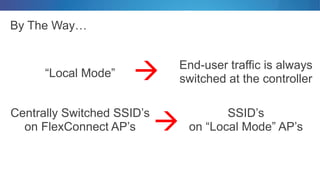
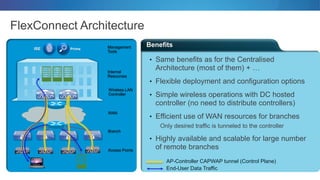
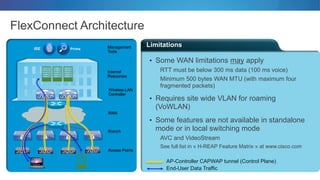
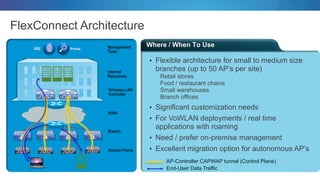
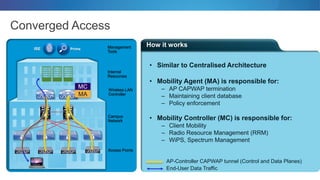
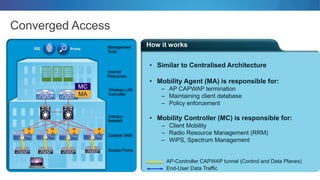
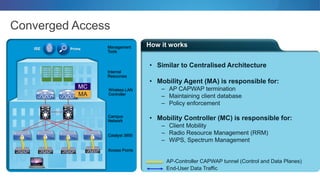
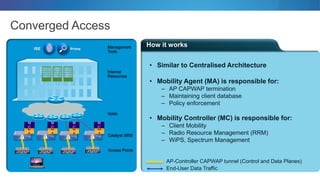
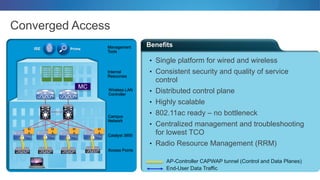
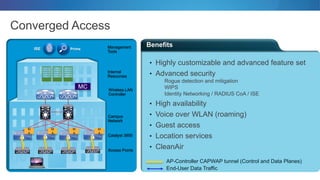
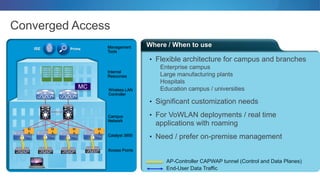
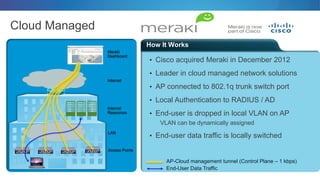
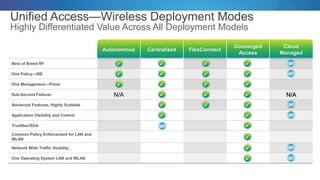
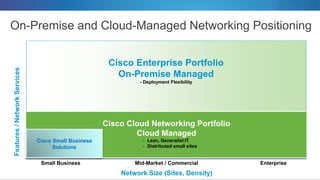
This document discusses different wireless network architectures from Cisco, including autonomous access points, centralized architecture, and FlexConnect architecture. Autonomous access points are managed individually while centralized architecture uses wireless LAN controllers for centralized management. FlexConnect is an extension of centralized that allows some local switching and control at remote branch sites for better WAN efficiency and high availability when the connection to the main controller fails. The document provides details on how each architecture works, available access point and controller options, benefits and limitations of each.