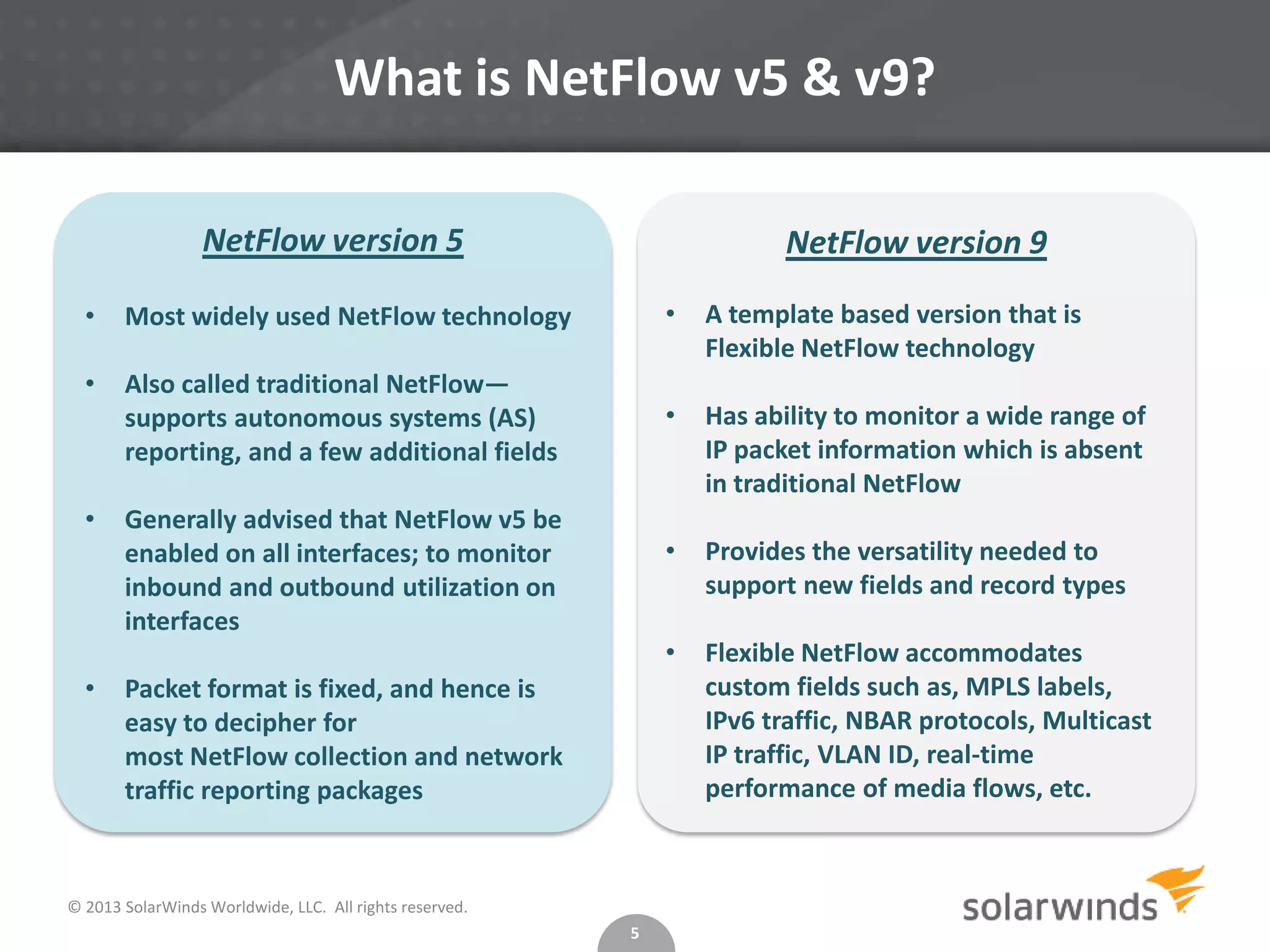
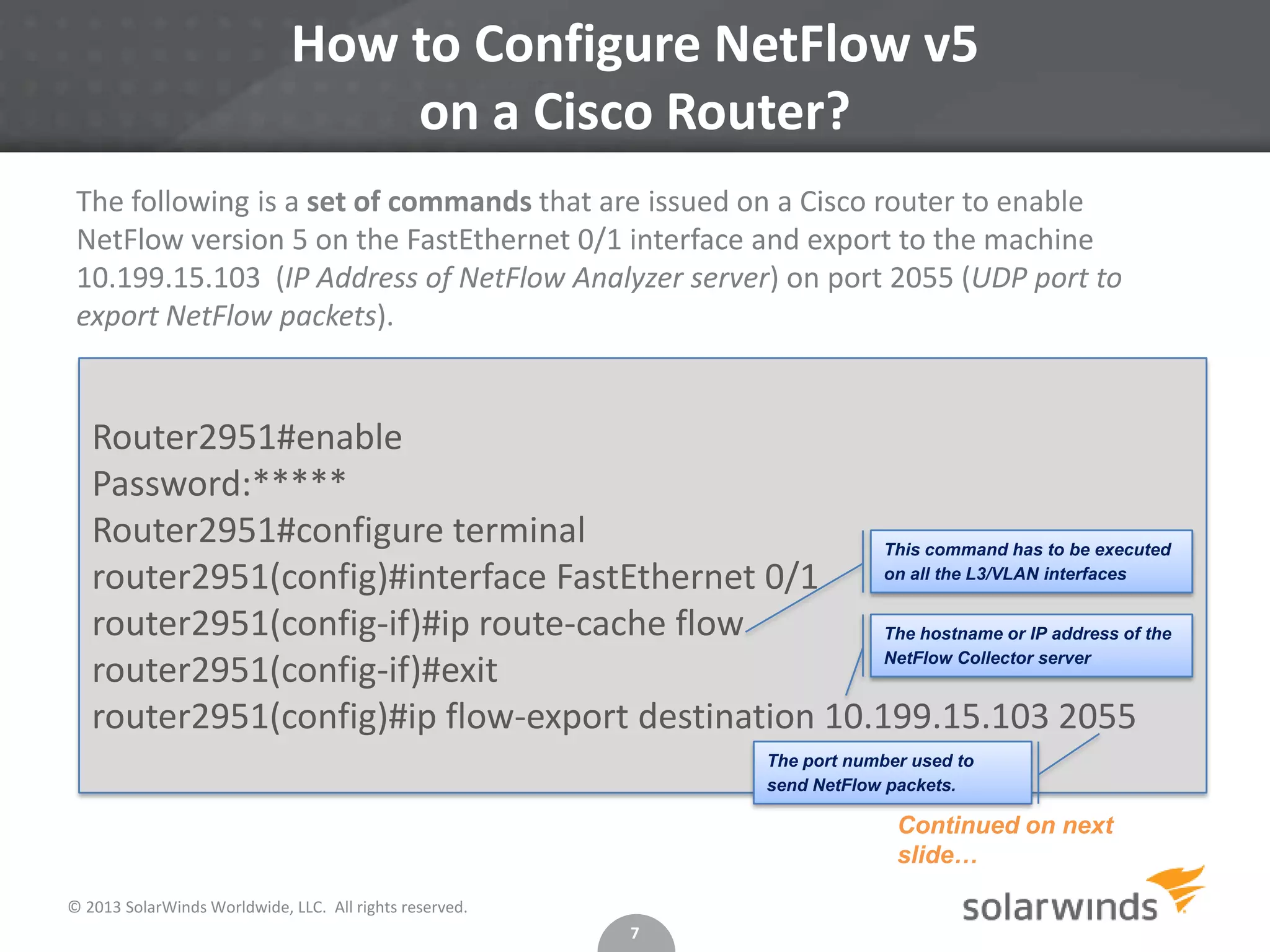
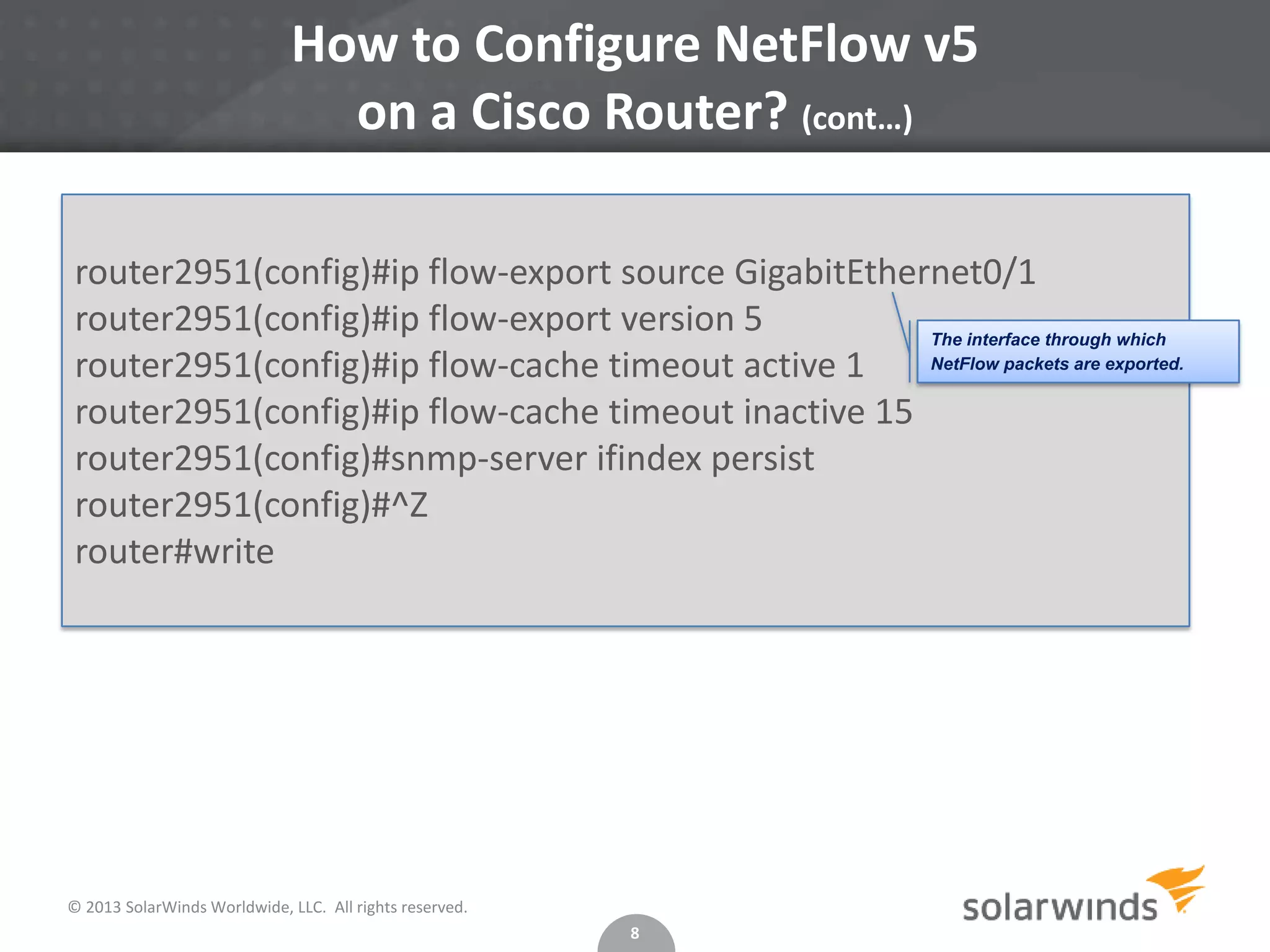
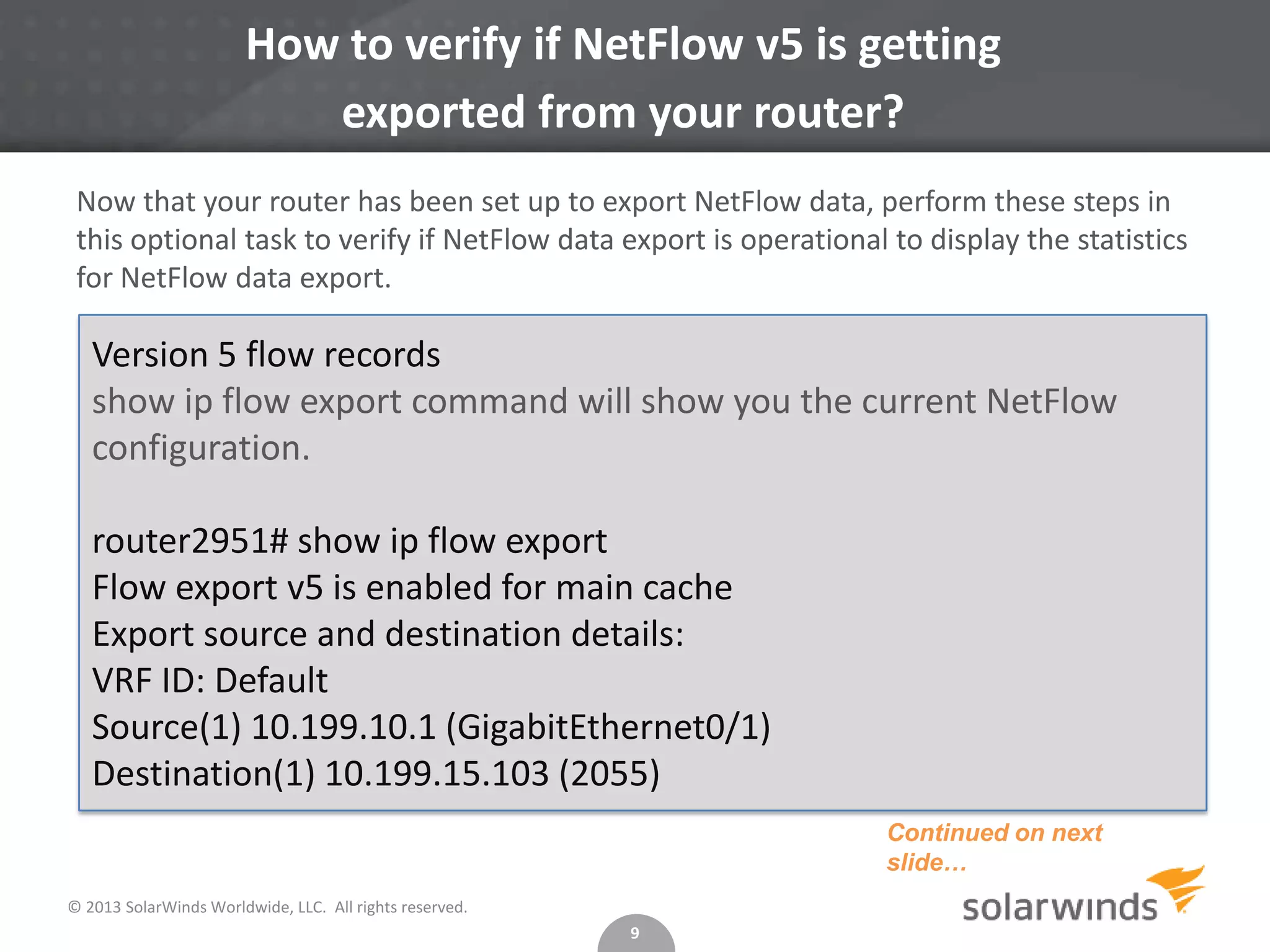
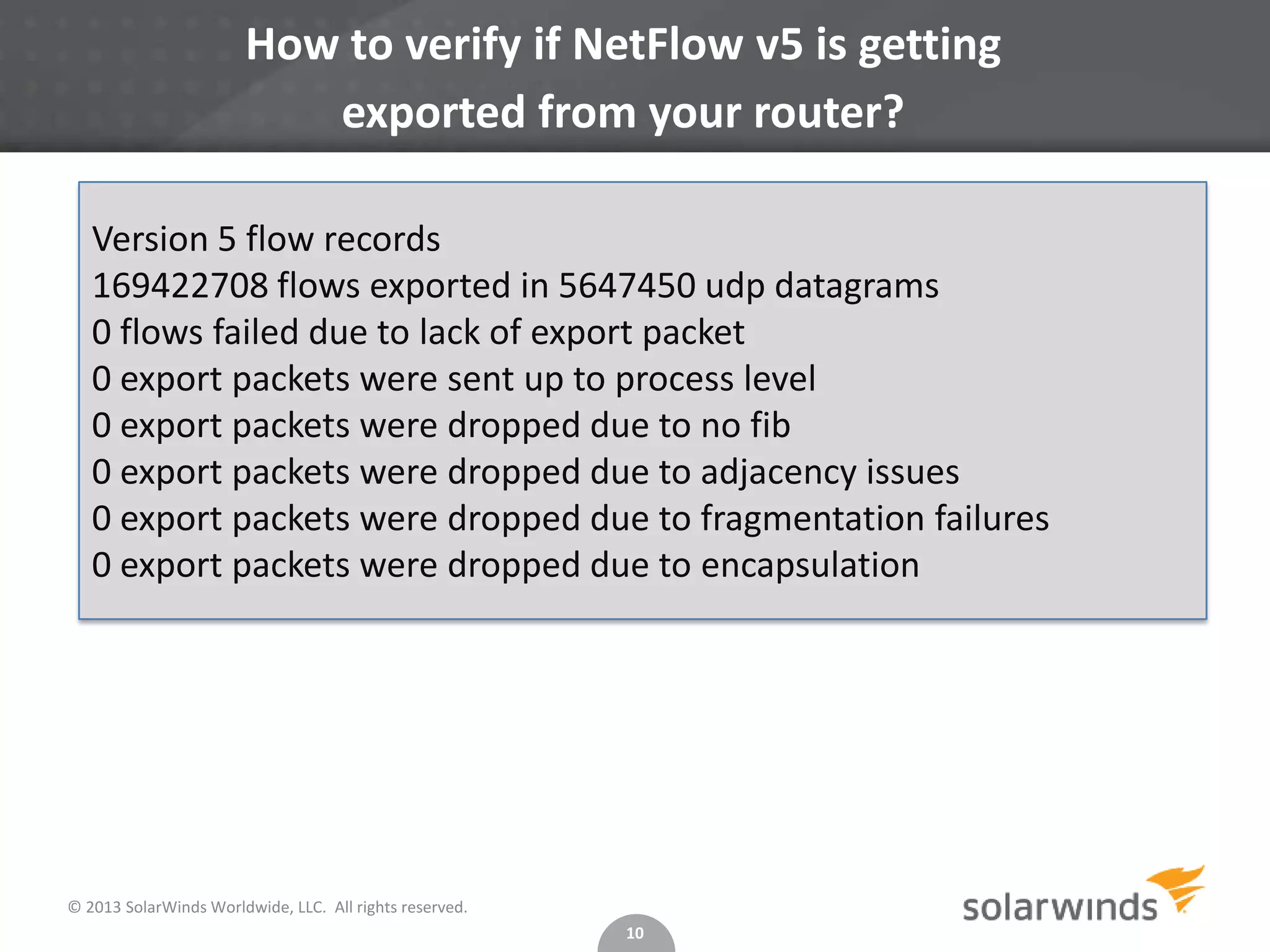
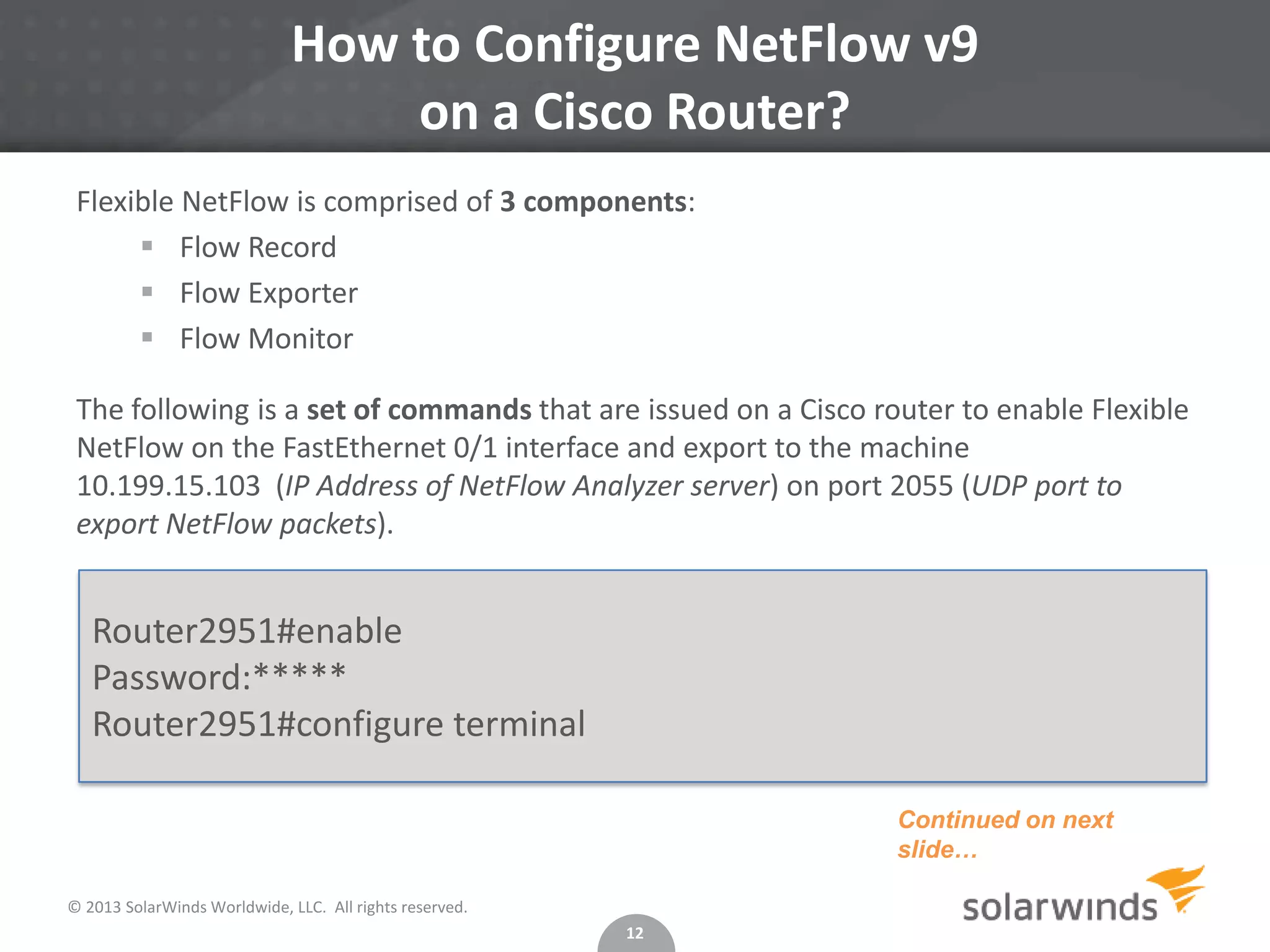
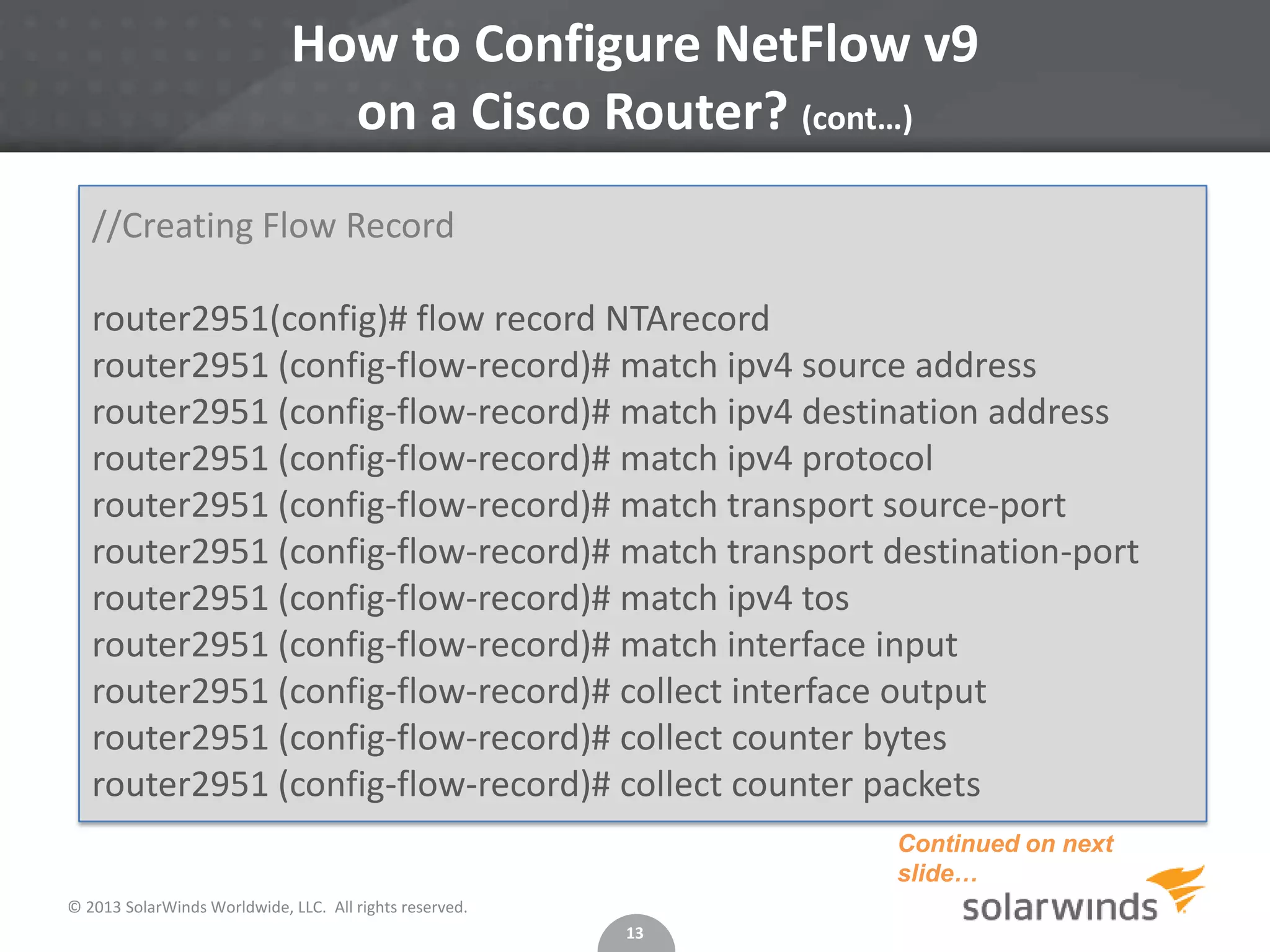
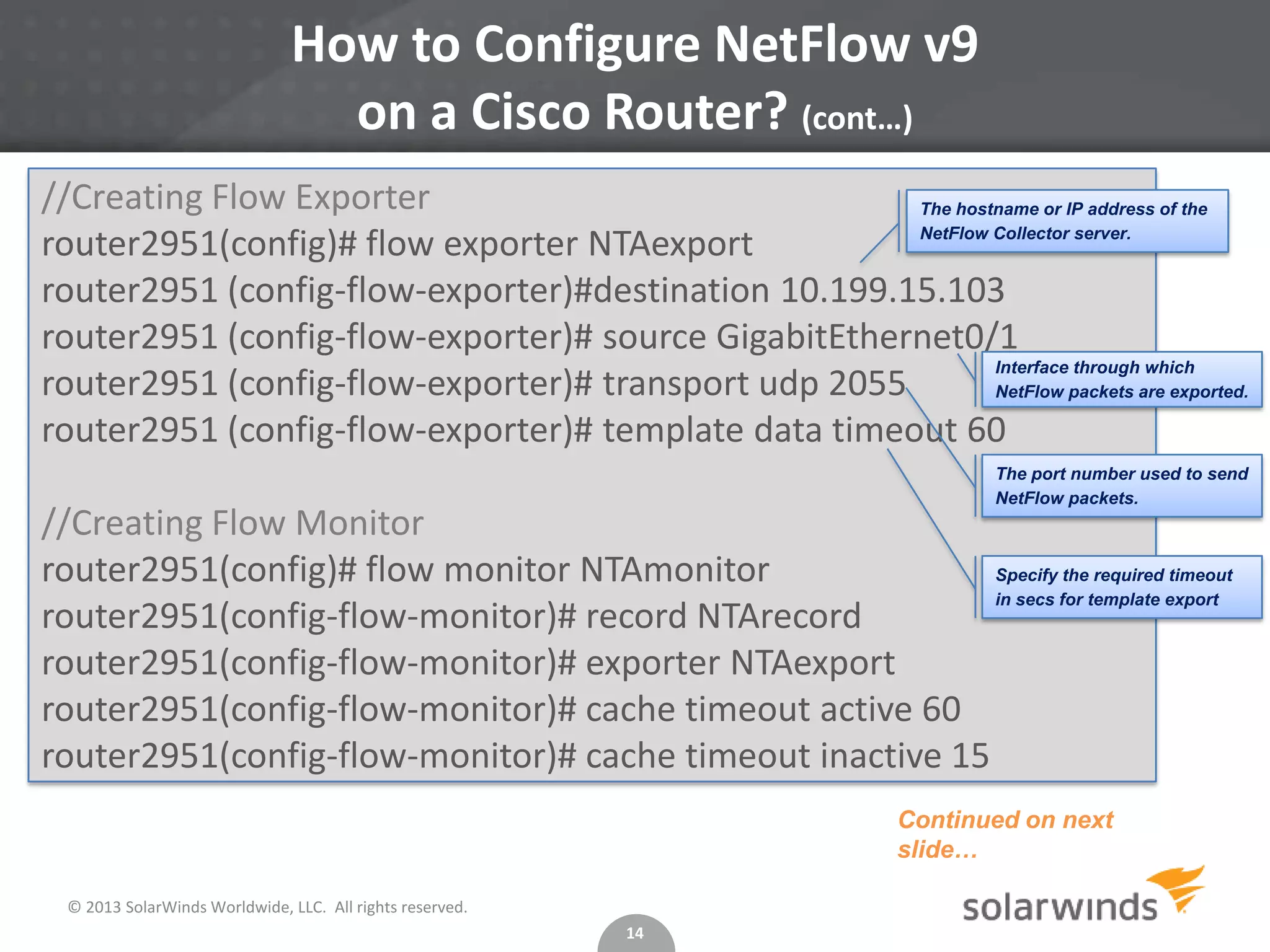
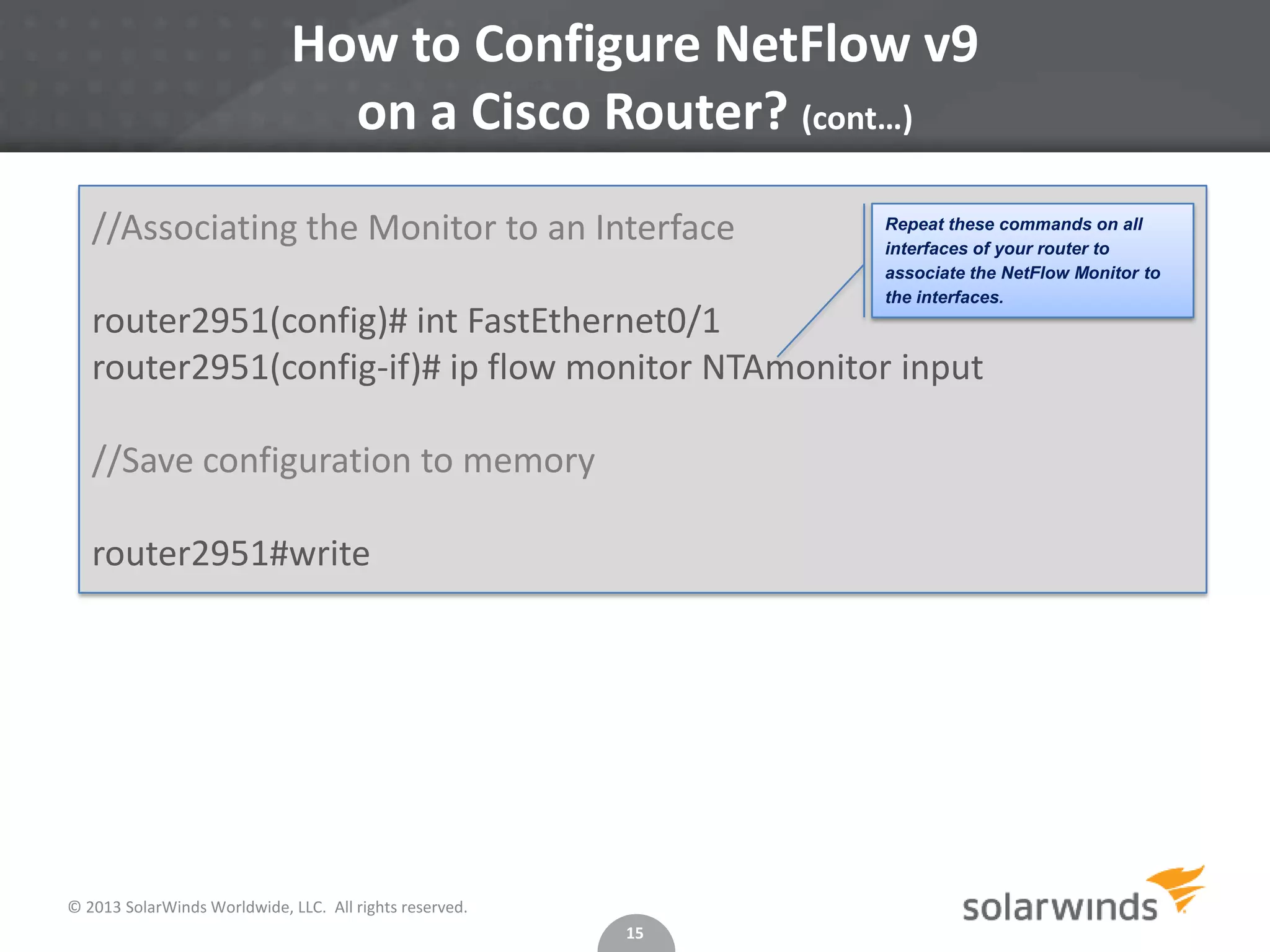
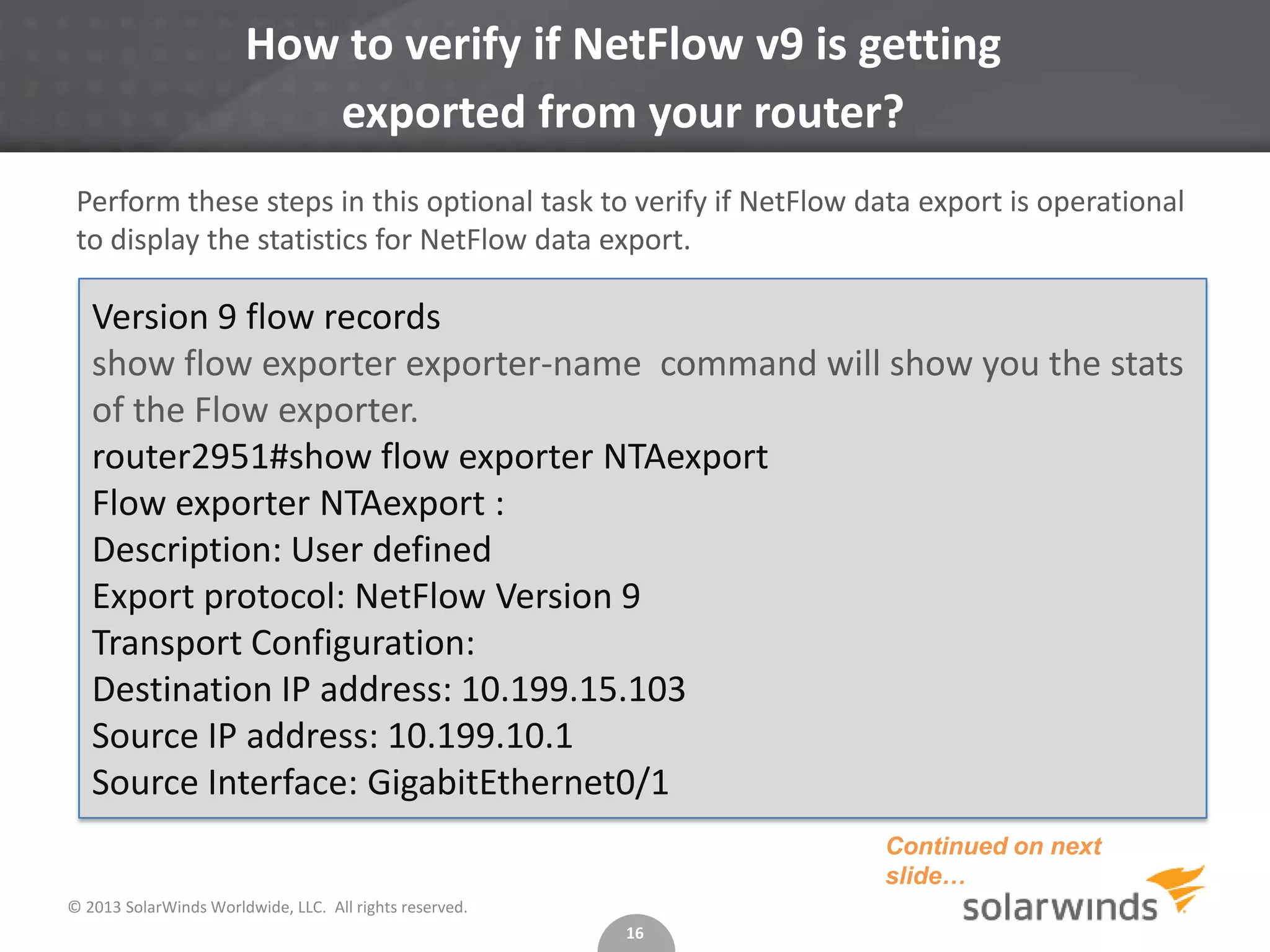
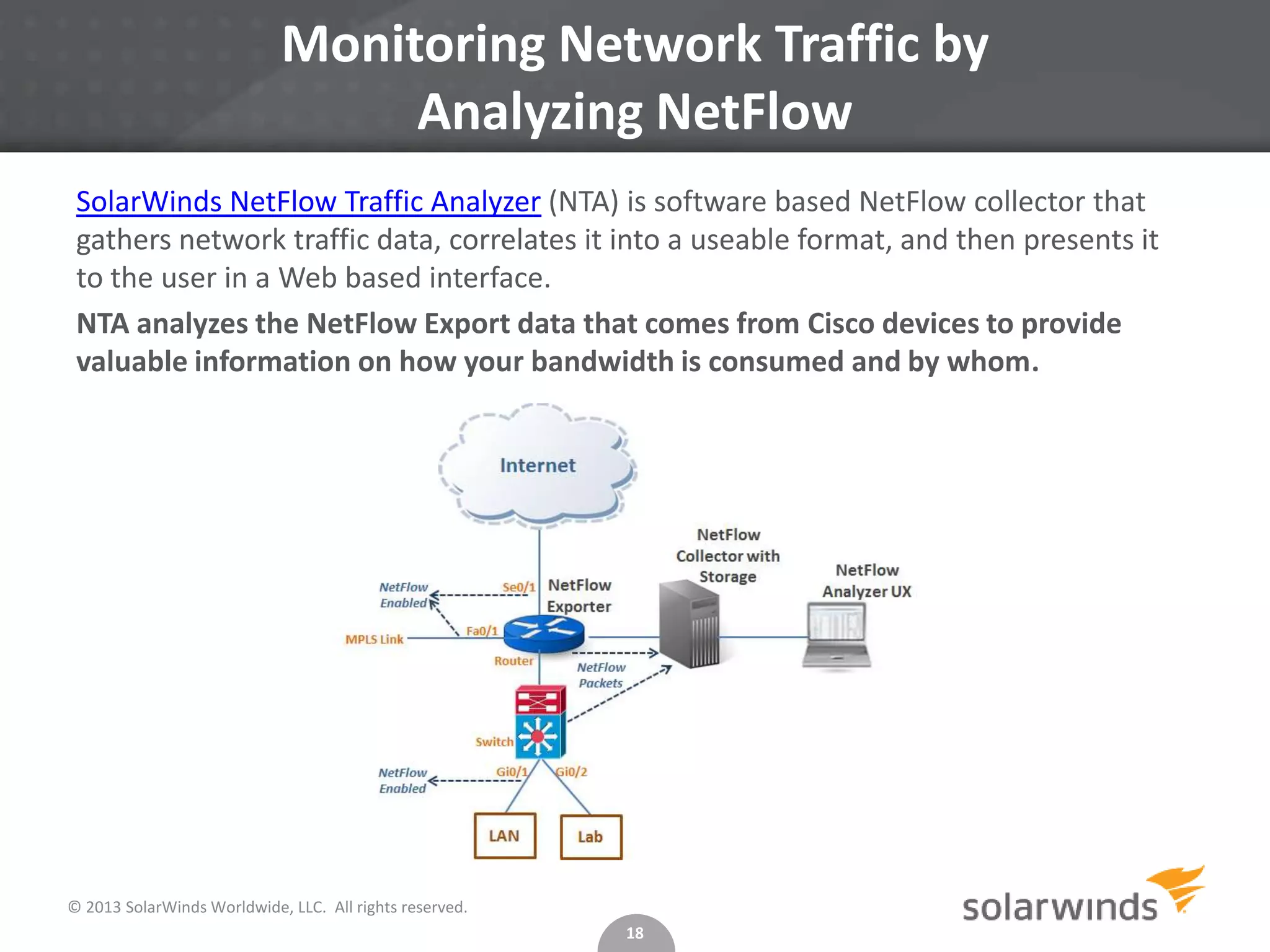
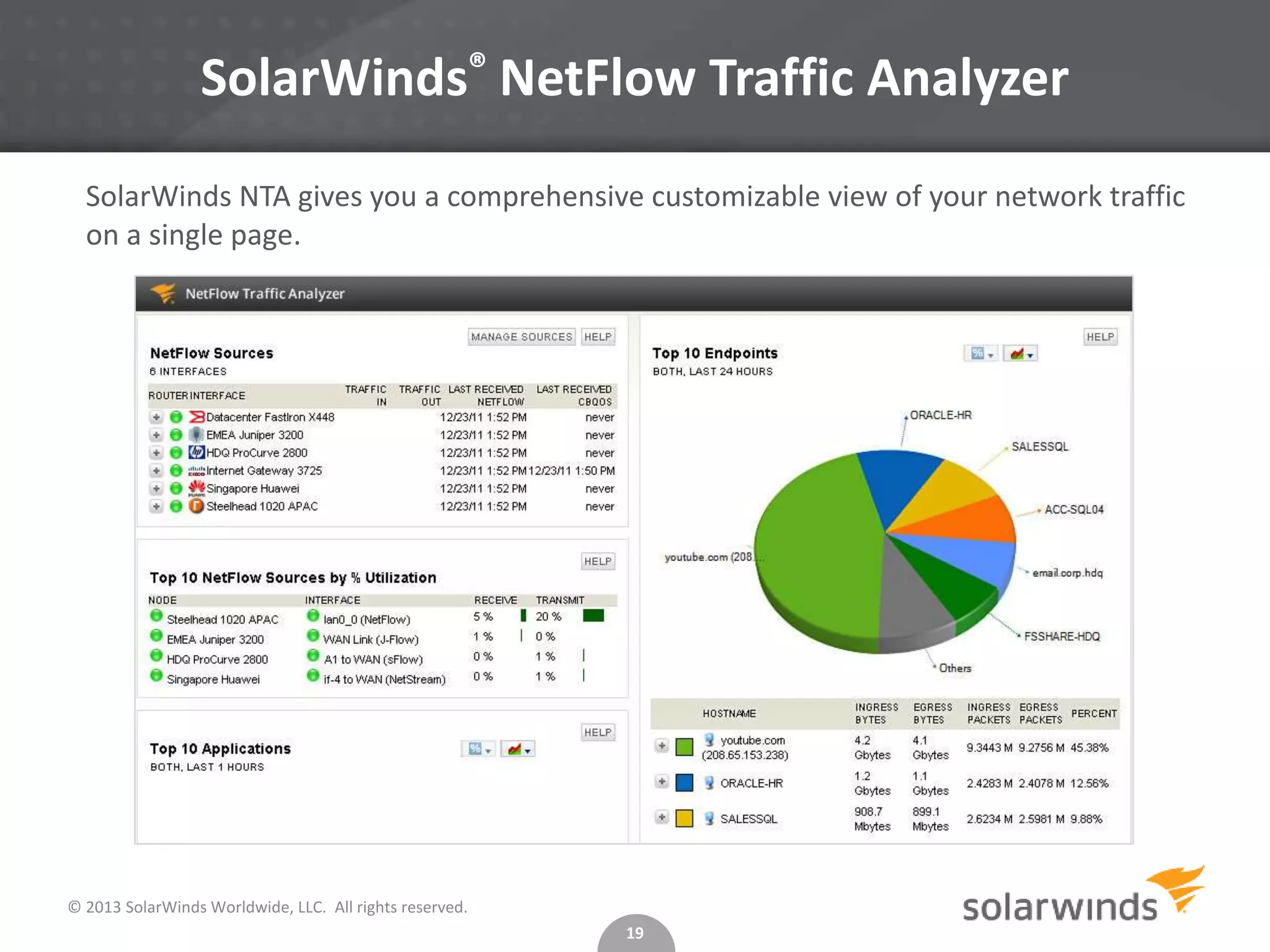
This document provides instructions for configuring NetFlow versions 5 and 9 on Cisco routers to monitor network traffic. It explains that NetFlow collects IP traffic data, what versions 5 and 9 are, and how to configure each version on a router by specifying the collector server, export port, and interfaces. It also describes how to verify the NetFlow export and how tools like SolarWinds NetFlow Traffic Analyzer analyze exported data to provide network usage insights.