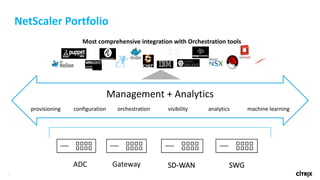
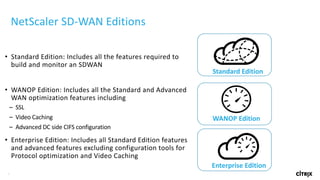
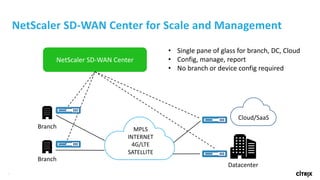
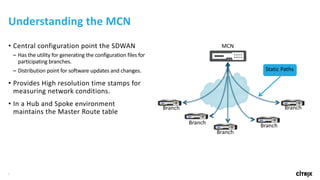
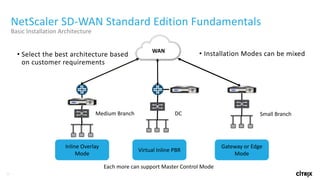
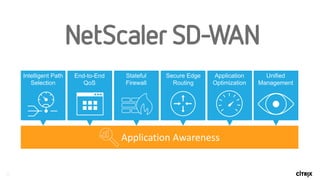
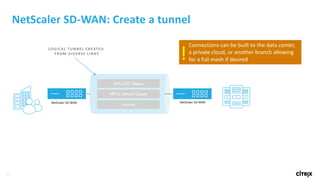
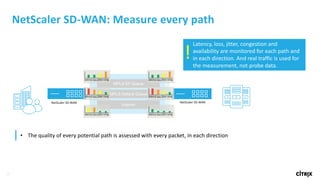
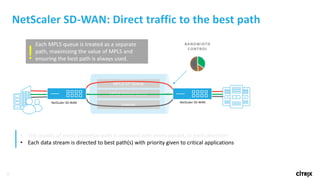
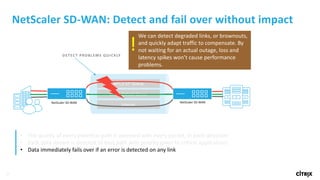
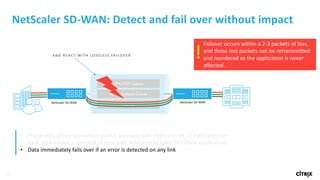
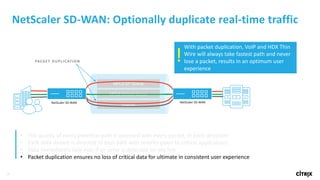
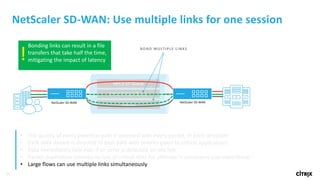
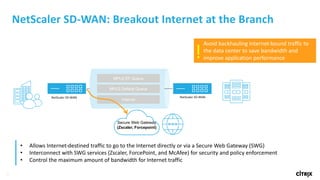
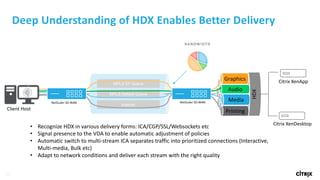
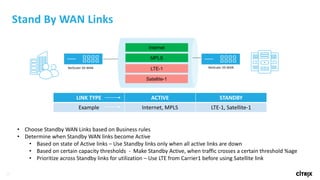
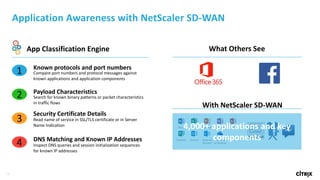
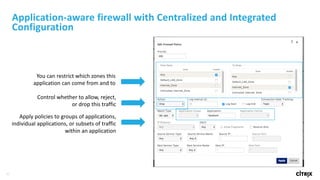
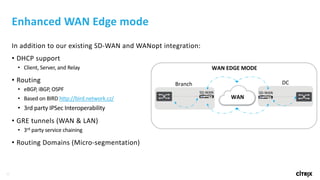
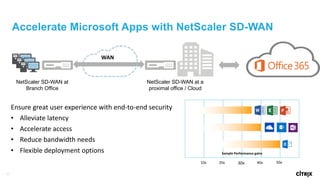
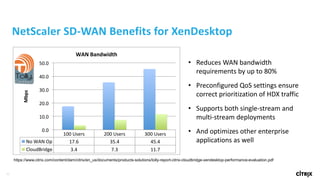
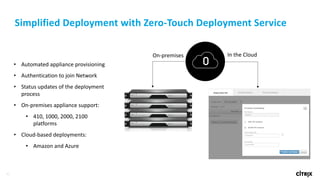
NetScaler SD-WAN provides software-defined wide area networking and cloud access capabilities that are secure, reliable and ensure high application quality. It offers various editions with standard features including bonding multiple WAN circuits into a single logical circuit, monitoring link conditions, and delivering applications over the best circuit. The product provides centralized configuration and management without requiring branch configurations.