The document summarizes the main components of a computer system:
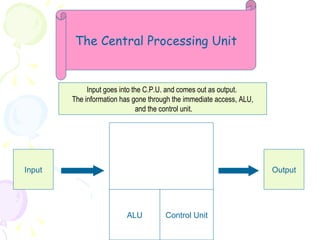
- The central processing unit (CPU) controls the system and includes an arithmetic logic unit, control unit, and memory unit. It processes input and outputs results as it coordinates operations.
- Computers operate at high speeds measured in hertz or megahertz. Modern computers can perform millions of operations per second.
- Computers use binary digits (bits) represented as 0s and 1s to store and process all information digitally. Memory comes in two main types: random access memory (RAM) stores temporary data while read only memory (ROM) permanently stores basic startup instructions.