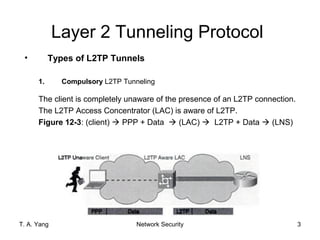
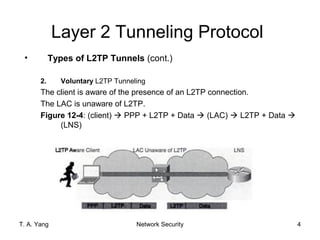
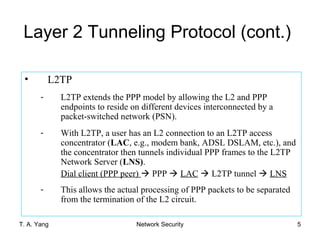
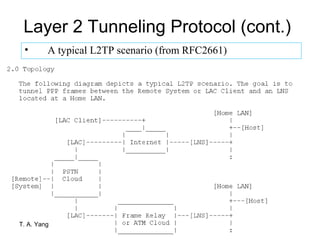
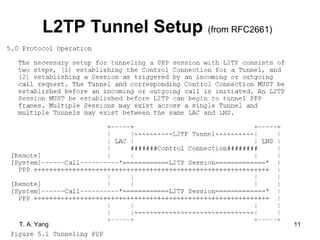
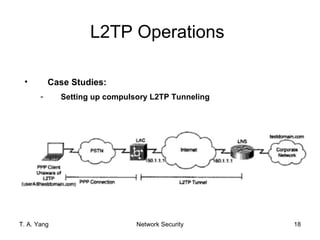
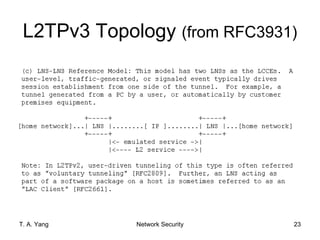
Layer 2 Tunneling Protocol (L2TP) is a network layer VPN protocol that uses IP packets to encapsulate Layer 2 frames. L2TP extends the Point-to-Point Protocol (PPP) by allowing the Layer 2 and PPP endpoints to reside on different devices interconnected by a packet-switched network. L2TP establishes tunnels between an L2TP Access Concentrator (LAC) and an L2TP Network Server (LNS) to transport individual PPP frames across the network. Control connections and sessions are set up between the LAC and LNS to establish L2TP tunnels for transporting PPP data.
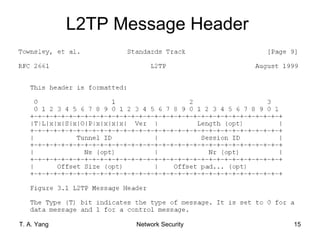
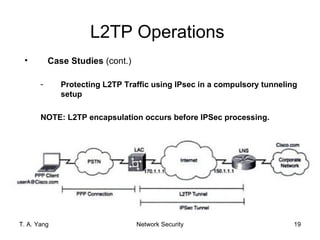
![Layer 2 Tunneling Protocol
(L2TP)
• An example of network layer VPN: use IP packets to
encapsulate Layer 2 frames
• Previous RFC (v2)
- RFC2661 Layer Two Tunneling Protocol L2TP W.
Townsley, A. Valencia, A. Rubens, G. Pall, G. Zorn,
B. Palter. August 1999 (PROPOSED STANDARD)
- A standard method for tunneling Point-to-Point Protocol (PPP)
[RFC1661] sessions
- Note: L2TP has since been adopted for tunneling a number of
other L2 protocols (e.g., Ethernet, Frame Relay, etc). L2TPv3
[RFC3931]
T. A. Yang Network Security 1](https://image.slidesharecdn.com/l2tp-130129090722-phpapp02/75/L2-tp-1-2048.jpg)
![Point-to-Point Protocol (PPP [RFC1661])
- PPP defines an encapsulation mechanism for transporting
multiprotocol packets across layer 2 (L2) point-to-point links.
- PPP relies on the Link Control Protocol (LCP) for establishing,
configuring, and testing the data-link connection.
- It has a family of Network Control Protocols (NCPs) for
establishing and configuring different network-layer protocols.
- Typically, a user obtains a L2 connection to a Network Access
Server (NAS) using one of a number of techniques (e.g., dialup
POTS, ISDN, ADSL, etc.) and then runs PPP over that connection.
- Example: A customer uses a dialup modem or a DSL line to
connect to the ISP or the company’s modem pool.
Dial client (PPP peer) PPP NAS (e.g., ISP)
- In such a configuration, the L2 termination point and PPP session
endpoint reside on the same physical device (i.e., the NAS).
T. A. Yang Network Security 2](https://image.slidesharecdn.com/l2tp-130129090722-phpapp02/85/L2-tp-2-320.jpg)