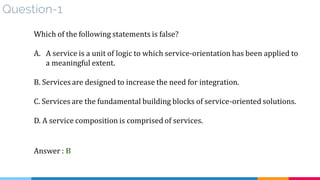
This document provides an overview of a 5-day course on service-oriented architecture (SOA). The course covers fundamental SOA concepts, SOA technology, design and architecture. It introduces SOA as a set of Lego blocks and discusses how SOA relates to enterprise architecture. The document outlines the course calendar and provides brief introductions to SOA certifications and reference materials.




















































































![process modeling [1. Functional decomposition]
Purpose : How can a large business problem be solved without having to build a
standalone body of solution logic?
Solution :
▪ To apply service-orientation, we first must break down a business process by
functionally decomposing it into a set of desirable actions
▪ Functional decomposition is Application of the separation of concerns theory.](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-99-320.jpg)
![process modeling [1. Functional decomposition]
Impacts :
▷ Require attention on interconnectivity, security, reliability, and maintenance
between distributed solution logics
▷ If the quality of the business process definition is poor, then the resulting
concerns will form a weak foundation for subsequent service definition.
Relationships :
▷ Functional Decomposition forms the basis for all of the patterns
▷ Prepares the concerns that are subsequently addressed by solution logic that
begins to take shape with the application of Service Encapsulation](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-100-320.jpg)
![process modeling [2. service encapsulation]
Purpose : How can solution logic be made available as a resource of the enterprise?
Solution :
▪ Solution logic can be encapsulated by and exposed as a service (positioned as enterprise resource)
▪ Solution logic capable of functioning beyond the boundary for which it is initially delivered
▪ enterprise where individual solutions use logic encapsulated as services and vice versa ( as shared
services )](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-101-320.jpg)
![process modeling [2. service encapsulation]
Application : ( identify solution logic that can be encapsulate)
▪ Does logic contain functionality useful to parts of the enterprise outside of the current
application boundary? ( if yes , logic increased value potential to be enterprise resources )
▪ Does logic designed to leverage enterprise resourcesalso have the potential to become an
enterprise resource? ( after agnostic logic is initially separated , it will be clear if new logic can
leverage existing enterprise resource , if so , some or all of its functionality can also be
positioned as an enterprise resource)
▪ Does implementation of logic require hard
constraints that make it impractical or
impossible to position logic as an effective
enterprise resource?
(may be real-world limitations prevent
from being encapsulated as a service)](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-102-320.jpg)
![process modeling [2. service encapsulation]
If service-orientation design principles cannot be applied to a meaningful extent,
then logic not likely justify for service encapsulation
Relationships :
▪ For encapsulated solution logic to become effective member of service inventory, it needs
to be further shaped by other patterns and principles
▪ Encapsulated solution logic subsequently grouped into
• Single service ( non-agnostic context) [ entity – utility]
• OR multi-purpose services ( Agnostic context) [ task – orchestration ]](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-103-320.jpg)
![process modeling [3. agnostic context]
Purpose : How can multi-purpose service logic be positioned as an effective enterprise resource?
Solution :
▪ Isolate logic that is not specific to one purpose into separate services with distinct agnostic
contexts
▪ positions reusable solution logic at an enterprise level
▪ Apply service reusability principle](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-104-320.jpg)
![process modeling [3. agnostic context]
Application :
▪ Subset of the solution logic being further decomposed and then distributed into services with
specific agnostic contexts
▪ Agnostic logic is defined and continually refined into a set of candidate service contexts.
▪ form the basis of Entity Abstraction and UtilityAbstraction
Impacts :
▪ Increase quantity of services required to solve a
given problem
▪ Leads to additional design considerations and
performance overhead associated with service
compositions.
▪ The governance effort increased
▪ Also the governance of the overall architecture is also
impacted as the quantity of agnostic services
within an inventory grows.](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-105-320.jpg)
![process modeling [3. agnostic context]
Relationships :
▪ Closest relationship is between Agnostic Context and Agnostic Capability
▪ Other patterns apply specialized variations on agnostic context such as Entity
Abstraction and Utility Abstraction](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-106-320.jpg)
![process modeling [4. agnostic capability]
Purpose: How can multipurpose service logic be made effectively consumable and composable ?
Solution : Agnostic service logic is partitioned into a set of well-defined capabilities that address
common concerns not specific to any one problem](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-107-320.jpg)
![process modeling [4. agnostic capability]
Relationships :
Considered a continuation of Agnostic Context](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-108-320.jpg)
![process modeling [4. agnostic capability]
After applying Entity Abstraction :](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-109-320.jpg)
![process modeling [4. agnostic capability]
After applying Utility Abstraction :](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-110-320.jpg)
![process modeling [4. agnostic capability] Sample
Service definitions, each with capabilities that address processing
requirements of specific business process
After furtherservice modeling, the definitions
are refined with agnostic capabilities.](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-111-320.jpg)
![process modeling [5. non-agnostic context]
Purpose : How can single-purpose service logic be positioned as an effective enterprise resource?
Solution :
Non-agnostic solution logic suitable for service encapsulation can be located within services
that reside as official members of a service inventory](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-112-320.jpg)
![process modeling [5. non-agnostic context]
Application :
▷ Non-agnostic service logic is shaped via the same governing design principles as agnostic
Services
▷ Most commonly applied in combination with Process Abstraction
▷ No rules as to whether this pattern should be applied before or after Agnostic Context
Impacts :
▷ Initial delivery will be more expensive and
more time-consuming
▷ The ultimate ROI can therefore be significantly
lower than with agnostic services](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-113-320.jpg)
![process modeling [5. non-agnostic context]
Relationships :
Non-Agnostic Context is subsequent to Service Encapsulation
Based on task-centric service models so major relation with process abstraction and
process centralization patterns](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-114-320.jpg)
![process modeling [5. non-agnostic context]
After applying Process Abstraction :](https://image.slidesharecdn.com/1-181125140412/85/SOA-Next-Generation-V1-1-115-320.jpg)