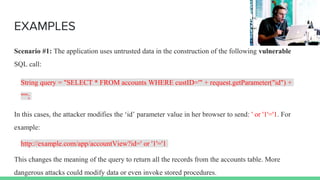
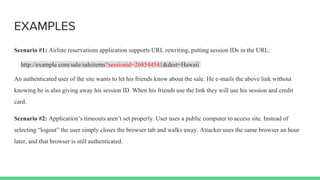
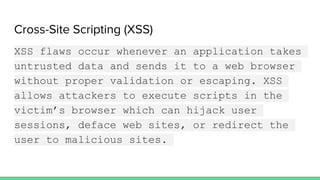
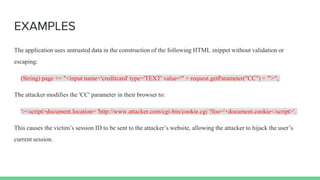
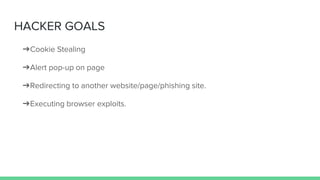
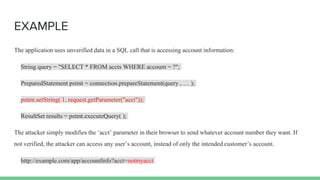
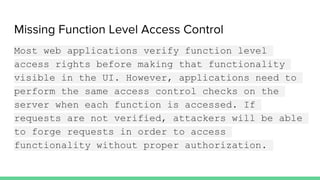
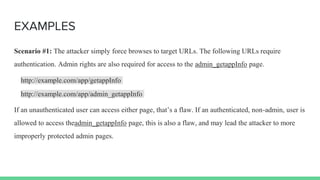
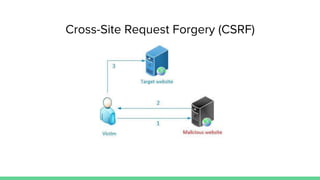
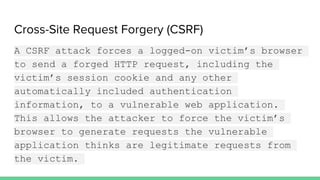
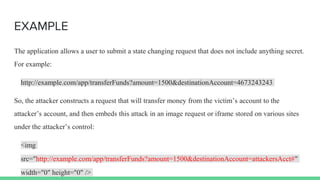
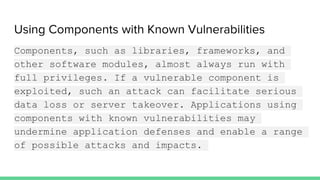
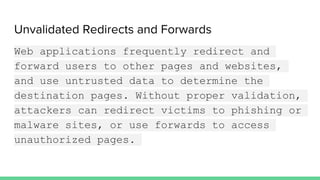
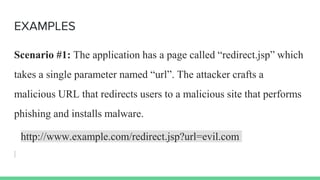
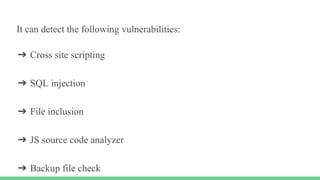
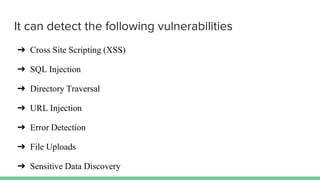
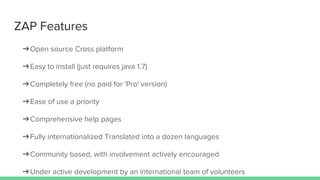
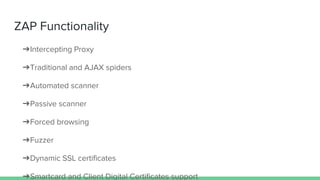
The document discusses various security vulnerabilities in web applications, including injection flaws, broken authentication, cross-site scripting (XSS), and insecure direct object references. It provides examples of how attackers exploit these vulnerabilities to gain unauthorized access, manipulate data, and compromise user sessions, along with hacker goals for each type of attack. The document also mentions tools for scanning web applications for these vulnerabilities.