i) The document discusses security and control of information systems, including objectives to explain why protection is needed, assess value, and evaluate frameworks and tools. It outlines challenges like confidentiality, authentication, integrity and availability.
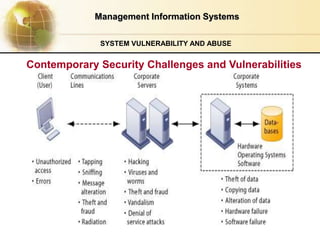
ii) It describes vulnerabilities like viruses, hacking, and weaknesses of internet technologies. System threats include spyware, denial of service attacks, and identity theft.
iii) Effective security requires management frameworks including risk assessment, policies, auditing, and ensuring business continuity during disasters. Technologies involve access control, encryption, firewalls and intrusion detection.