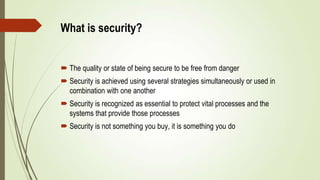
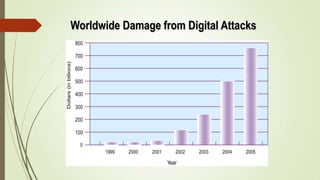
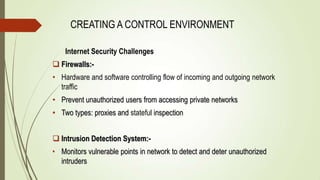
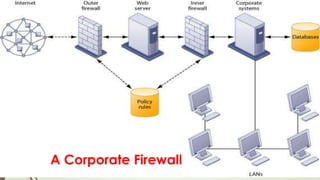
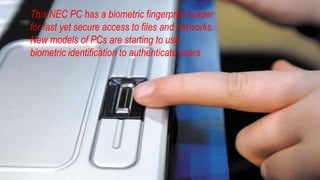
The document discusses securing management information systems. It covers topics such as what security is, vulnerabilities, threats and attacks. It also discusses why systems are vulnerable, the business value of security, establishing management frameworks for security, creating a control environment, and management challenges around implementing effective security policies. The overall message is that security should be a high priority that requires commitment from all levels of the organization.