Security
•Download as PPT, PDF•
0 likes•460 views
The document discusses various methods for ensuring security in information systems and networks. It describes encryption techniques that scramble data during transmission and can only be unscrambled by authorized users with public and private keys. It also discusses firewalls that filter access to internal networks from the internet and intranets to deter hacking. Finally, it outlines other security measures like antivirus software, access controls, backup systems, and audits to evaluate security policies and ensure proper protections are in place.
Report
Share
Report
Share
Recommended
Materi Kuliah Umum Kapita Selekta : Internet Of Things

Materi kuliah umum Kapita Selekta kedua, 8 Desember 2014 di Universitas Telkom. Materi : Internet Of Things. Referensi di keempat buku saya.
Sistem informasi penjualan minimarket berintegrasi barcode reader menggunakan

Seiring dengan pertumbuhan ekonomi Indonesia yang maju dan berkembang pesat khususnya di kota-kota besar, telah terjadi perubahan diberbagai sektor, termasuk dibidang industri retail dan produksi serta pada kegiatan eceran di Indonesia yang telah berkembang menjadi usaha yang berskala besar. Perkembangan bisnis eceran yang pesat ini tidak lepas dan faktor meningkatnya jumlah penduduk Indonesia dan juga meningkatnya pendapatan perkapita penduduk yang menyebabkan taraf hidup masyarakat semakin meningkat, hal ini membawa dampak kepada pola perilaku belanja masyarakat, dimana semakin meningkatnya taraf hidup maka tuntutan akan pemenuhan kebutuhan akan semakin meningkat juga.
Recommended
Materi Kuliah Umum Kapita Selekta : Internet Of Things

Materi kuliah umum Kapita Selekta kedua, 8 Desember 2014 di Universitas Telkom. Materi : Internet Of Things. Referensi di keempat buku saya.
Sistem informasi penjualan minimarket berintegrasi barcode reader menggunakan

Seiring dengan pertumbuhan ekonomi Indonesia yang maju dan berkembang pesat khususnya di kota-kota besar, telah terjadi perubahan diberbagai sektor, termasuk dibidang industri retail dan produksi serta pada kegiatan eceran di Indonesia yang telah berkembang menjadi usaha yang berskala besar. Perkembangan bisnis eceran yang pesat ini tidak lepas dan faktor meningkatnya jumlah penduduk Indonesia dan juga meningkatnya pendapatan perkapita penduduk yang menyebabkan taraf hidup masyarakat semakin meningkat, hal ini membawa dampak kepada pola perilaku belanja masyarakat, dimana semakin meningkatnya taraf hidup maka tuntutan akan pemenuhan kebutuhan akan semakin meningkat juga.
PRESENTASI CYBERSECURITY REKTOR

PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR |
Analisa pengembangan sistem aplikasi krl access

Analisis pengembangan sistem aplikasi bertujuan untuk memperbaiki eror dan meningkatkan kinerja sistem aplikasi krl access.
Perkembangan Komputer Dari Generasi Ke Generasi

Sistem Komputer
Perkembangan Komputer Dari Generasi Ke Generasi
Analisis Algoritma - Notasi Asimptotik

Materi ini menjelaskan tentang konsep notasi asimptotik untuk pengklasifikasian efisiensi waktu di algoritma.
Ketoprak_PPT ADT Stack dan Queue.pptx

1. Buat program untuk mengkonvesi dari bilang desimal ke representasi bilangan biner menggunakan program stack di atas. 2. Kembangkan program di atas dengan membuat stack yang berisi Object sehingga isi Stack dapat diisi sembarang object seperti object Double, objeck Buku dan lain sebaginya. Dengan potongan program driver sebagaimana gambar 5 dan class Buku sebagaimna gambar 6 akan menghasilkan keluaran sebagaimana gambar 7
compTIA guide to get the CERTIFICATION EMERSON EDUARDO RODRIGUES

Complete guide to get the certification compTIA which I got.
Emerson Eduardo Rodrigues
More Related Content
What's hot
PRESENTASI CYBERSECURITY REKTOR

PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR | PRESENTASI CYBERSECURITY REKTOR |
Analisa pengembangan sistem aplikasi krl access

Analisis pengembangan sistem aplikasi bertujuan untuk memperbaiki eror dan meningkatkan kinerja sistem aplikasi krl access.
Perkembangan Komputer Dari Generasi Ke Generasi

Sistem Komputer
Perkembangan Komputer Dari Generasi Ke Generasi
Analisis Algoritma - Notasi Asimptotik

Materi ini menjelaskan tentang konsep notasi asimptotik untuk pengklasifikasian efisiensi waktu di algoritma.
Ketoprak_PPT ADT Stack dan Queue.pptx

1. Buat program untuk mengkonvesi dari bilang desimal ke representasi bilangan biner menggunakan program stack di atas. 2. Kembangkan program di atas dengan membuat stack yang berisi Object sehingga isi Stack dapat diisi sembarang object seperti object Double, objeck Buku dan lain sebaginya. Dengan potongan program driver sebagaimana gambar 5 dan class Buku sebagaimna gambar 6 akan menghasilkan keluaran sebagaimana gambar 7
What's hot (20)
Similar to Security
compTIA guide to get the CERTIFICATION EMERSON EDUARDO RODRIGUES

Complete guide to get the certification compTIA which I got.
Emerson Eduardo Rodrigues
Ijcatr04061002

The technology behind information systems in today’s world has been embedded in nearly every aspect of our lives. Thus, the idea of securing our information systems and/or computer networks has become very paramount. Owing to the significance of computer networks in transporting the information and knowledge generated by the increased diversity and sophistication of computational machinery, it would be very imperative to engage the services of network security professionals to manage the resources that are passed through the various terminals (end points) of the these network, so as to achieve a maximum reliability of the information passed, making sure that this is achieved without creating a discrepancy between the security and usability of such network. This paper examines the various techniques involved in securely maintaining the safe states of an active computer network, its resources and the information it carries. We examined techniques of compromising an information system by breaking into the system without authorised access (Hacking), we also looked at the various phases of digital analysis of an already compromised system, and then we investigated the tools and techniques for digitally analysing a compromised system in other to bring it back to a safe state.
Security and Ethical Challenges Contributors Kim Wanders.docx

Security and Ethical Challenges
Contributors: Kim Wandersee, Les Pang
Computer Security
Computer Security Goals
Computer security must be viewed in a holistic manner and provide an end-to-end protection
as data moves through its lifecycle. Data originates from a user or sensor, passes over a
network to reach a computing system that hosts software. This computer system has software
and processes the data and stores in in a storage device. That data is backed up on a device
and finally archived. The elements that handle the data need to be secure. Computer security
pertains to all the means to protect the confidentiality, integrity, availability, authenticity,
utility, and possession of data throughout its lifecycle.
Confidentiality: A security principle that
works to ensure that data is not disclosed to
unauthorized persons.
Integrity: A security principle that makes sure
that information and systems are not
modified maliciously or accidentally.
Availability: A security principle that assures
reliable and timely access to data and
resources by authorized individuals.
Authenticity: A security principle that the
data, transactions, communications or
documents are genuine, valid, and not
fraudulent.
Utility: A security principle that addresses
that the information is usable for its intended
purpose. .
Possession: A security principle that works to
ensure that data remains under the control of
the authorized individuals.
Figure 1. Parkerian Hexad (PH) security model.
The Parerian Hexad (PH) model expands on the Confidentiality, Integrity, and Availability (CIA)
triad that has been the basic model of Information Security for over 20 years. This framework is
used to list all aspects of security at a basic level. It provides a complete security framework to
provide the means for information owners to protect their information from any adversaries
and vulnerabilities. It adds Authenticity, Utility, and Possession to CIA triad security model. It
addresses security aspects for data throughout its lifecycle.
The Center for Internet Security has identified 20 controls necessary to protect an organization
from known cyber-attack. The first 5 controls will provide effective defense against the most
common cyber-attacks, approximately 85% of attacks. The 5 controls are:
1. Inventory of Authorized and Devices
2. Inventory of Authorized and Unauthorized Software
3. Secure Configurations for Hardware and Software
4. Continuous Vulnerability Assessment and Remediation
5. Controlled User of Administrative Privileges
A full explanation of all 20 controls is available at the Center for Internet Security website.
Search for CIS controls.
Security Standards and Regulations
The National Institute of Standards and Technology (NIST), Computer Security Division, provides
security standards in its Federal Information Processing Standards (.
Security and Ethical Challenges Contributors Kim Wanders.docx

Security and Ethical Challenges
Contributors: Kim Wandersee, Les Pang
Computer Security
Computer Security Goals
Computer security must be viewed in a holistic manner and provide an end-to-end protection
as data moves through its lifecycle. Data originates from a user or sensor, passes over a
network to reach a computing system that hosts software. This computer system has software
and processes the data and stores in in a storage device. That data is backed up on a device
and finally archived. The elements that handle the data need to be secure. Computer security
pertains to all the means to protect the confidentiality, integrity, availability, authenticity,
utility, and possession of data throughout its lifecycle.
Confidentiality: A security principle that
works to ensure that data is not disclosed to
unauthorized persons.
Integrity: A security principle that makes sure
that information and systems are not
modified maliciously or accidentally.
Availability: A security principle that assures
reliable and timely access to data and
resources by authorized individuals.
Authenticity: A security principle that the
data, transactions, communications or
documents are genuine, valid, and not
fraudulent.
Utility: A security principle that addresses
that the information is usable for its intended
purpose. .
Possession: A security principle that works to
ensure that data remains under the control of
the authorized individuals.
Figure 1. Parkerian Hexad (PH) security model.
The Parerian Hexad (PH) model expands on the Confidentiality, Integrity, and Availability (CIA)
triad that has been the basic model of Information Security for over 20 years. This framework is
used to list all aspects of security at a basic level. It provides a complete security framework to
provide the means for information owners to protect their information from any adversaries
and vulnerabilities. It adds Authenticity, Utility, and Possession to CIA triad security model. It
addresses security aspects for data throughout its lifecycle.
The Center for Internet Security has identified 20 controls necessary to protect an organization
from known cyber-attack. The first 5 controls will provide effective defense against the most
common cyber-attacks, approximately 85% of attacks. The 5 controls are:
1. Inventory of Authorized and Devices
2. Inventory of Authorized and Unauthorized Software
3. Secure Configurations for Hardware and Software
4. Continuous Vulnerability Assessment and Remediation
5. Controlled User of Administrative Privileges
A full explanation of all 20 controls is available at the Center for Internet Security website.
Search for CIS controls.
Security Standards and Regulations
The National Institute of Standards and Technology (NIST), Computer Security Division, provides
security standards in its Federal Information Processing Standards ( ...
Security and management

security concepts ,goals of computer security , problem and requirements ,identifying the assets ,identifying the threats, identifying the impacts, vulnerability ,user authentication ,security system and facilities ,system access control , password management ,privileged user management ,user account management ,data resource protection, sensitive system protection ,cryptography ,intrusion detection ,computer-security classification
Chapter 5.pptx

we have made this like computer application course material which is so functionable and any one can use it to develop your technological concept skill.
We Belete And Tadelech
IRJET- Image Steganography using Pixel Pattern Matching in Cloud Data Sto...

https://irjet.net/archives/V7/i3/IRJET-V7I3121.pdf
Similar to Security (20)
compTIA guide to get the CERTIFICATION EMERSON EDUARDO RODRIGUES

compTIA guide to get the CERTIFICATION EMERSON EDUARDO RODRIGUES
Security and Ethical Challenges Contributors Kim Wanders.docx

Security and Ethical Challenges Contributors Kim Wanders.docx
Security and Ethical Challenges Contributors Kim Wanders.docx

Security and Ethical Challenges Contributors Kim Wanders.docx
Security Holes and Vulnerabilities in Corporate Network_Pre Null Meet Kolkata

Security Holes and Vulnerabilities in Corporate Network_Pre Null Meet Kolkata
IRJET- Image Steganography using Pixel Pattern Matching in Cloud Data Sto...

IRJET- Image Steganography using Pixel Pattern Matching in Cloud Data Sto...
More from Dr. Vardhan choubey
More from Dr. Vardhan choubey (20)
Recently uploaded
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection -Introduction to Social Dreaming
#Systems Psychodynamics
#Innovation
#Creativity
#Consultancy
#Coaching
Pitch Deck Teardown: RAW Dating App's $3M Angel deck

Pitch Deck Teardown: RAW Dating App's $3M Angel deck
Accpac to QuickBooks Conversion Navigating the Transition with Online Account...

This article provides a comprehensive guide on how to
effectively manage the convert Accpac to QuickBooks , with a particular focus on utilizing online accounting services to streamline the process.
Digital Transformation in PLM - WHAT and HOW - for distribution.pdf

Presentation describing the Digital Transformation for PLM in the context of a Dassault Systemes portfolio.
Enterprise Excellence is Inclusive Excellence.pdf

Enterprise excellence and inclusive excellence are closely linked, and real-world challenges have shown that both are essential to the success of any organization. To achieve enterprise excellence, organizations must focus on improving their operations and processes while creating an inclusive environment that engages everyone. In this interactive session, the facilitator will highlight commonly established business practices and how they limit our ability to engage everyone every day. More importantly, though, participants will likely gain increased awareness of what we can do differently to maximize enterprise excellence through deliberate inclusion.
What is Enterprise Excellence?
Enterprise Excellence is a holistic approach that's aimed at achieving world-class performance across all aspects of the organization.
What might I learn?
A way to engage all in creating Inclusive Excellence. Lessons from the US military and their parallels to the story of Harry Potter. How belt systems and CI teams can destroy inclusive practices. How leadership language invites people to the party. There are three things leaders can do to engage everyone every day: maximizing psychological safety to create environments where folks learn, contribute, and challenge the status quo.
Who might benefit? Anyone and everyone leading folks from the shop floor to top floor.
Dr. William Harvey is a seasoned Operations Leader with extensive experience in chemical processing, manufacturing, and operations management. At Michelman, he currently oversees multiple sites, leading teams in strategic planning and coaching/practicing continuous improvement. William is set to start his eighth year of teaching at the University of Cincinnati where he teaches marketing, finance, and management. William holds various certifications in change management, quality, leadership, operational excellence, team building, and DiSC, among others.
What are the main advantages of using HR recruiter services.pdf

HR recruiter services offer top talents to companies according to their specific needs. They handle all recruitment tasks from job posting to onboarding and help companies concentrate on their business growth. With their expertise and years of experience, they streamline the hiring process and save time and resources for the company.
Putting the SPARK into Virtual Training.pptx

This 60-minute webinar, sponsored by Adobe, was delivered for the Training Mag Network. It explored the five elements of SPARK: Storytelling, Purpose, Action, Relationships, and Kudos. Knowing how to tell a well-structured story is key to building long-term memory. Stating a clear purpose that doesn't take away from the discovery learning process is critical. Ensuring that people move from theory to practical application is imperative. Creating strong social learning is the key to commitment and engagement. Validating and affirming participants' comments is the way to create a positive learning environment.
Discover the innovative and creative projects that highlight my journey throu...

Discover the innovative and creative projects that highlight my journey through Full Sail University. Below, you’ll find a collection of my work showcasing my skills and expertise in digital marketing, event planning, and media production.
Filing Your Delaware Franchise Tax A Detailed Guide

As a business owner in Delaware, staying on top of your tax obligations is paramount, especially with the annual deadline for Delaware Franchise Tax looming on March 1. One such obligation is the annual Delaware Franchise Tax, which serves as a crucial requirement for maintaining your company’s legal standing within the state. While the prospect of handling tax matters may seem daunting, rest assured that the process can be straightforward with the right guidance. In this comprehensive guide, we’ll walk you through the steps of filing your Delaware Franchise Tax and provide insights to help you navigate the process effectively.
Affordable Stationery Printing Services in Jaipur | Navpack n Print

Looking for professional printing services in Jaipur? Navpack n Print offers high-quality and affordable stationery printing for all your business needs. Stand out with custom stationery designs and fast turnaround times. Contact us today for a quote!
The Parable of the Pipeline a book every new businessman or business student ...

The-Parable of the Pipeline a book every new businessman or business student must read before diving into real world of business.
Role of Remote Sensing and Monitoring in Mining

Remote sensing and monitoring are changing the mining industry for the better. These are providing innovative solutions to long-standing challenges. Those related to exploration, extraction, and overall environmental management by mining technology companies Odisha. These technologies make use of satellite imaging, aerial photography and sensors to collect data that might be inaccessible or from hazardous locations. With the use of this technology, mining operations are becoming increasingly efficient. Let us gain more insight into the key aspects associated with remote sensing and monitoring when it comes to mining.
5 Things You Need To Know Before Hiring a Videographer

Dive into this presentation to discover the 5 things you need to know before hiring a videographer in Toronto.
Sustainability: Balancing the Environment, Equity & Economy

[Note: This is a partial preview. To download this presentation, visit:
https://www.oeconsulting.com.sg/training-presentations]
Sustainability has become an increasingly critical topic as the world recognizes the need to protect our planet and its resources for future generations. Sustainability means meeting our current needs without compromising the ability of future generations to meet theirs. It involves long-term planning and consideration of the consequences of our actions. The goal is to create strategies that ensure the long-term viability of People, Planet, and Profit.
Leading companies such as Nike, Toyota, and Siemens are prioritizing sustainable innovation in their business models, setting an example for others to follow. In this Sustainability training presentation, you will learn key concepts, principles, and practices of sustainability applicable across industries. This training aims to create awareness and educate employees, senior executives, consultants, and other key stakeholders, including investors, policymakers, and supply chain partners, on the importance and implementation of sustainability.
LEARNING OBJECTIVES
1. Develop a comprehensive understanding of the fundamental principles and concepts that form the foundation of sustainability within corporate environments.
2. Explore the sustainability implementation model, focusing on effective measures and reporting strategies to track and communicate sustainability efforts.
3. Identify and define best practices and critical success factors essential for achieving sustainability goals within organizations.
CONTENTS
1. Introduction and Key Concepts of Sustainability
2. Principles and Practices of Sustainability
3. Measures and Reporting in Sustainability
4. Sustainability Implementation & Best Practices
To download the complete presentation, visit: https://www.oeconsulting.com.sg/training-presentations
Lookback Analysis

Explore our most comprehensive guide on lookback analysis at SafePaaS, covering access governance and how it can transform modern ERP audits. Browse now!
Business Valuation Principles for Entrepreneurs

This insightful presentation is designed to equip entrepreneurs with the essential knowledge and tools needed to accurately value their businesses. Understanding business valuation is crucial for making informed decisions, whether you're seeking investment, planning to sell, or simply want to gauge your company's worth.
Recently uploaded (20)
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection with Social Dreaming
Pitch Deck Teardown: RAW Dating App's $3M Angel deck

Pitch Deck Teardown: RAW Dating App's $3M Angel deck
Accpac to QuickBooks Conversion Navigating the Transition with Online Account...

Accpac to QuickBooks Conversion Navigating the Transition with Online Account...
Digital Transformation in PLM - WHAT and HOW - for distribution.pdf

Digital Transformation in PLM - WHAT and HOW - for distribution.pdf
What are the main advantages of using HR recruiter services.pdf

What are the main advantages of using HR recruiter services.pdf
Discover the innovative and creative projects that highlight my journey throu...

Discover the innovative and creative projects that highlight my journey throu...
Filing Your Delaware Franchise Tax A Detailed Guide

Filing Your Delaware Franchise Tax A Detailed Guide
Affordable Stationery Printing Services in Jaipur | Navpack n Print

Affordable Stationery Printing Services in Jaipur | Navpack n Print
The Parable of the Pipeline a book every new businessman or business student ...

The Parable of the Pipeline a book every new businessman or business student ...
chapter 10 - excise tax of transfer and business taxation

chapter 10 - excise tax of transfer and business taxation
5 Things You Need To Know Before Hiring a Videographer

5 Things You Need To Know Before Hiring a Videographer
Sustainability: Balancing the Environment, Equity & Economy

Sustainability: Balancing the Environment, Equity & Economy
Security
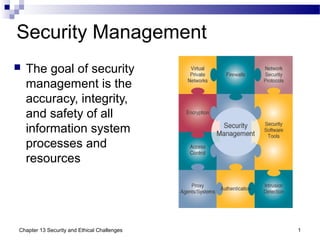
- 1. Security Management The goal of security management is the accuracy, integrity, and safety of all information system processes and resources 1Chapter 13 Security and Ethical Challenges
- 2. Internetworked Security Defenses Encryption Data is transmitted in scrambled form It is unscrambled by computer systems for authorized users only The most widely used method uses a pair of public and private keys unique to each individual Note: Each system has two keys public and private. Public is available to all. Suppose computer 1 tries to communicate with computer 2 then it will encrypt message using public key of computer 2. computer 2 will open it using its private key. Messages encrypted by public key will be opened by private key only and vice versa. 2Chapter 13 Security and Ethical Challenges
- 3. Public/Private Key Encryption 3Chapter 13 Security and Ethical Challenges
- 4. Internetworked Security Defenses Firewalls A gatekeeper system that protects a company’s intranets and other computer networks from intrusion Provides a filter and safe transfer point for access to/from the Internet and other networks Important for individuals who connect to the Internet with DSL or cable modems Can deter hacking, but cannot prevent it 4Chapter 13 Security and Ethical Challenges
- 5. Internet and Intranet Firewalls 5Chapter 13 Security and Ethical Challenges
- 6. Denial of Service Attacks Denial of service attacks depend on three layers of networked computer systems The victim’s website The victim’s Internet service provider Zombie or slave computers that have been commandeered by the cybercriminals. These are mostly unguarded computers. 6Chapter 13 Security and Ethical Challenges
- 7. Defending Against Denial of Service At Zombie Machines Set and enforce security policies Scan for vulnerabilities At the ISP Monitor and block traffic spikes Traffic spikes are peak on web sites and often causes crash. Content delivery** network kind of distributed systems help in controlling traffic At the Victim’s Website Create backup servers and network connections 7Chapter 13 Security and Ethical Challenges
- 8. A content delivery network (CDN) is a system of distributed servers (network) that deliver webpages and other Web content to a user based on the geographic locations of the user. The closer the CDN server is to the user geographically, the faster the content will be delivered to the user. Chapter 13 Security and Ethical Challenges 8
- 9. Internetworked Security Defenses Email Monitoring Use of content monitoring software that scans for troublesome words that might compromise corporate security Virus Defenses Centralize the updating and distribution of antivirus software Use a security suite that integrates virus protection with firewalls, Web security, and content blocking features 9Chapter 13 Security and Ethical Challenges
- 10. Other Security Measures Security Codes Multilevel password system Encrypted passwords Smart cards with microprocessors Backup Files Duplicate files of data or programs Security Monitors Monitor the use of computers and networks Protects them from unauthorized use, fraud, and destruction Biometrics Computer devices measure physical traits that make each individual unique Voice recognition, fingerprints, retina scan 10Chapter 13 Security and Ethical Challenges
- 11. Computer Failure Controls Prevents computer failures or minimizes its effects Preventive maintenance Arrange backups with a disaster recovery organization Computer system fails because of electrical supplies, telecommunication problems, virsuses, Chapter 13 Security and Ethical Challenges 11
- 12. Other Security Measures In the event of a system failure, fault-tolerant systems have redundant processors, peripherals, and software that provide Fail-over capability: shifts to back up components Fail-save capability: the system continues to operate at the same level Fail-soft capability: the system continues to operate at a reduced but acceptable level A disaster recovery plan contains formalized procedures to follow in the event of a disaster Which employees will participate What their duties will be What hardware, software, and facilities will be used Priority of applications that will be processed Use of alternative facilities Offsite storage of databases 12Chapter 13 Security and Ethical Challenges
- 13. Information System Controls Methods and devices that attempt to ensure the accuracy, validity, and propriety of information system activities 13Chapter 13 Security and Ethical Challenges
- 14. Information system controls are methods and devices that attempt to ensure the accuracy, validity and propriety of information system activities. Control total make total of all inputs OR outputs Checkpoints ensure that required information is available for processing Hardware control is control of communication between various parts of system. It is mostly job of operating system. Chapter 13 Security and Ethical Challenges 14
- 15. Auditing IT Security IT Security Audits Performed by internal or external auditors Review and evaluation of security measures and management policies Goal is to ensure that that proper and adequate measures and policies are in place 15Chapter 13 Security and Ethical Challenges
- 16. Protecting Yourself from Cybercrime 16Chapter 13 Security and Ethical Challenges
- 17. Chapter 13 Security and Ethical Challenges 17