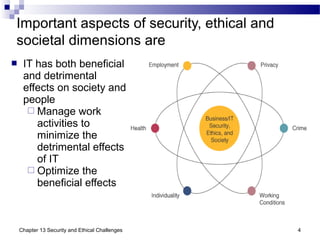
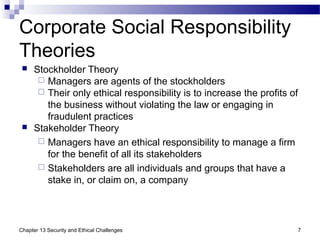
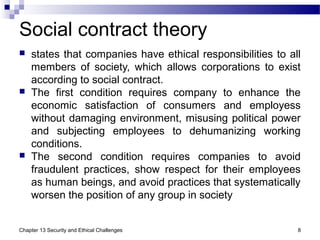
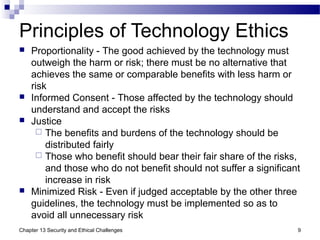
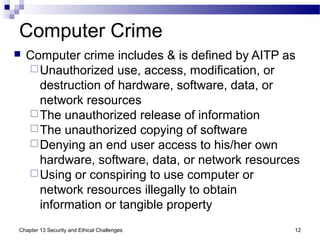
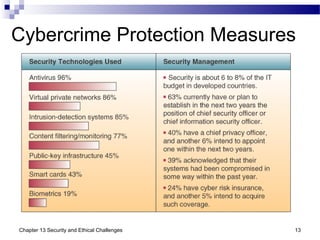
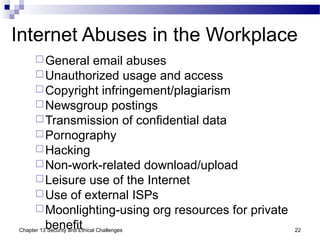
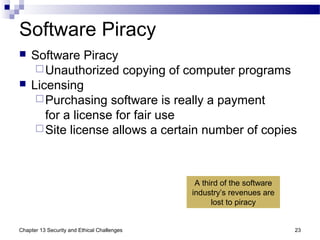
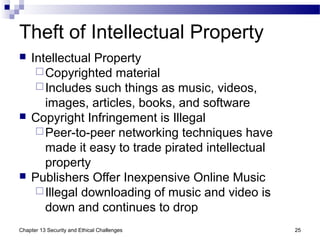
This document discusses several security, ethical, and privacy challenges related to information technology. It covers topics like cyberscams, hacking, software piracy, viruses, privacy issues, and computer monitoring in the workplace. It also examines the responsibilities of businesses and professionals to maintain ethical standards regarding issues like monitoring employee communications, customer data protection, and preventing cybercrime.