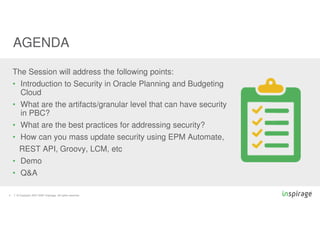
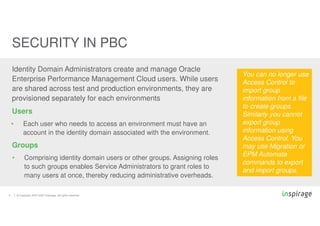
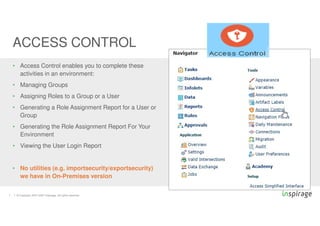
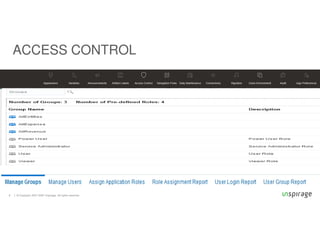
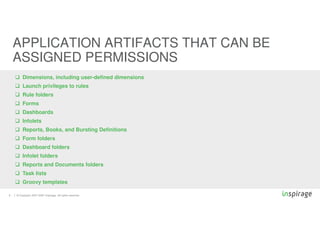
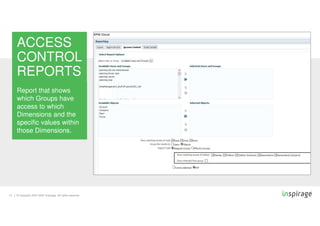
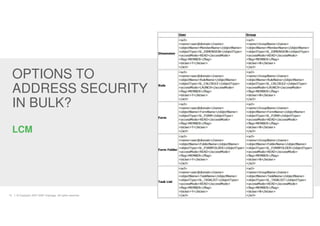
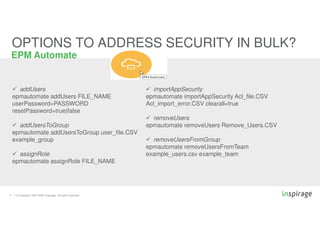
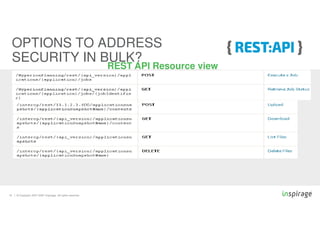
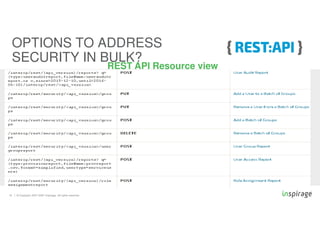
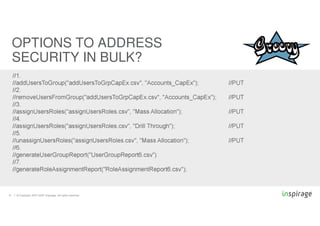
The document outlines the automation of security management in Oracle Planning and Budgeting Cloud Services (PBC), detailing aspects such as user roles, group management, and security best practices. It discusses how to manage users and groups, the concept of cell-level security, and various options available for bulk security updates using tools like EPM Automate and REST API. Additionally, it covers the process of applying security measures, including the management of predefined roles and access control reports.