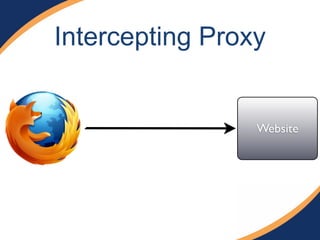
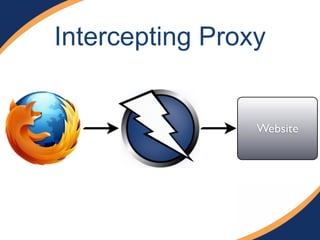
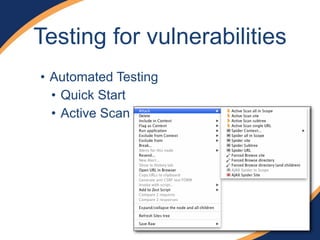
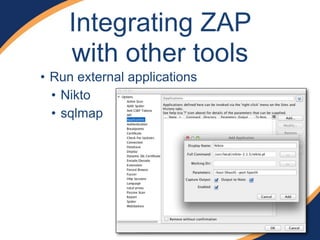
This document discusses using the OWASP Zed Attack Proxy (ZAP) tool to find vulnerabilities in web applications. ZAP is a free and open-source web application penetration testing tool that can be used to conduct both automated and manual testing of applications. The document provides an overview of ZAP's features, how to install and configure it, how to test applications for vulnerabilities using both automated and direct methods, and how to integrate ZAP with other tools.