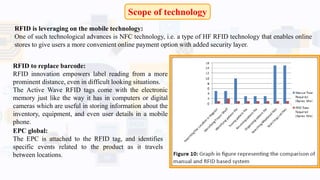
RFID (Radio Frequency Identification) technology uses radio waves for data transfer, allowing for the identification and tracking of objects without physical contact. It consists of active tags, which have their own power supply and can be read from longer distances, and passive tags, which derive power from nearby readers. The technology is increasingly applied across various sectors, including supply chain management, healthcare, and access control, while facing challenges such as privacy concerns and return on investment.