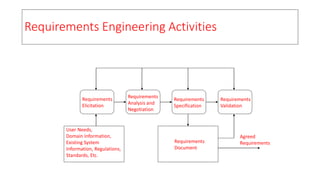
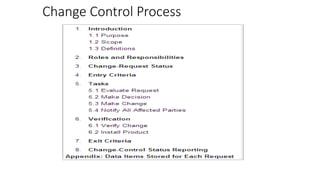
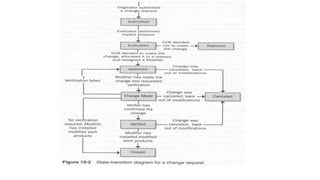
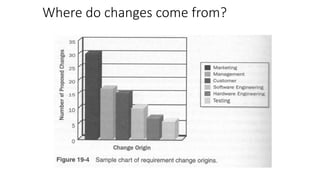
The document outlines the process and importance of requirements management in system development, including activities such as requirements elicitation, analysis, specification, and validation. It highlights the inevitability of changing requirements due to various factors like evolving user knowledge, organizational changes, and external conditions, emphasizing the need for traceability and effective change management processes. Additionally, it explores the characteristics of stable vs. volatile requirements and the necessity of utilizing tools to manage and track requirements effectively.