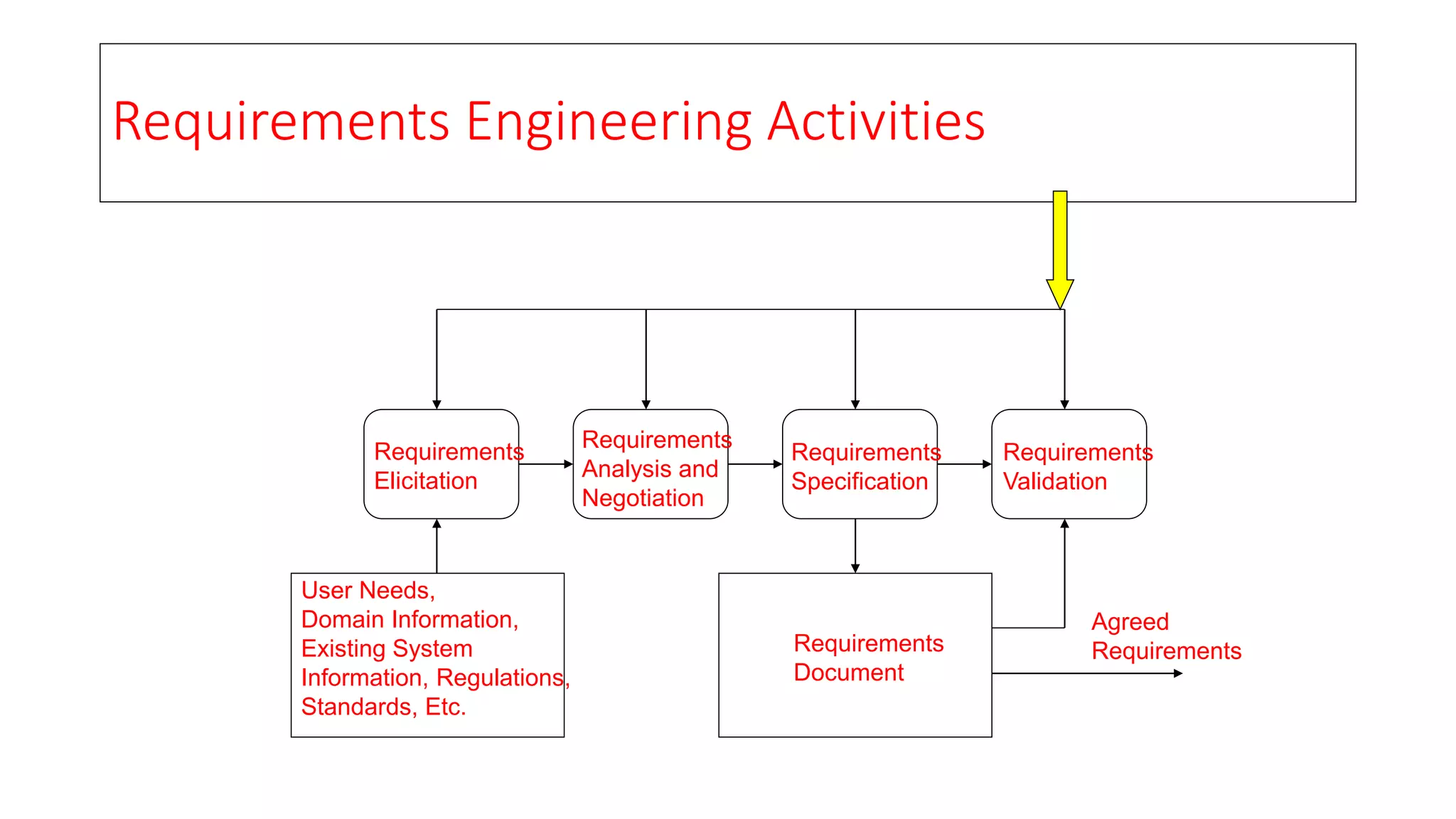
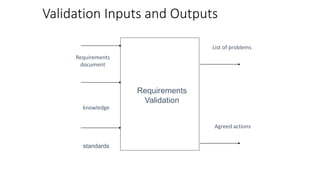
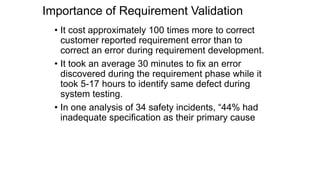
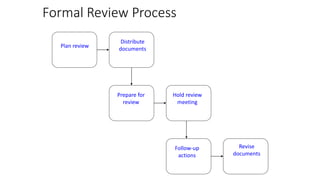
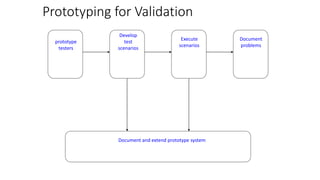
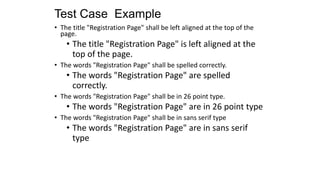
The document outlines the various stages of requirements engineering, including elicitation, analysis, specification, and validation. It emphasizes the importance of clear, complete, and consistent requirements as well as the various techniques for validation and review to ensure the effectiveness of the requirements document. Key processes highlighted include stakeholder consultation, negotiation, problem addressing, and the use of prototypes and testing to confirm requirements align with user needs.