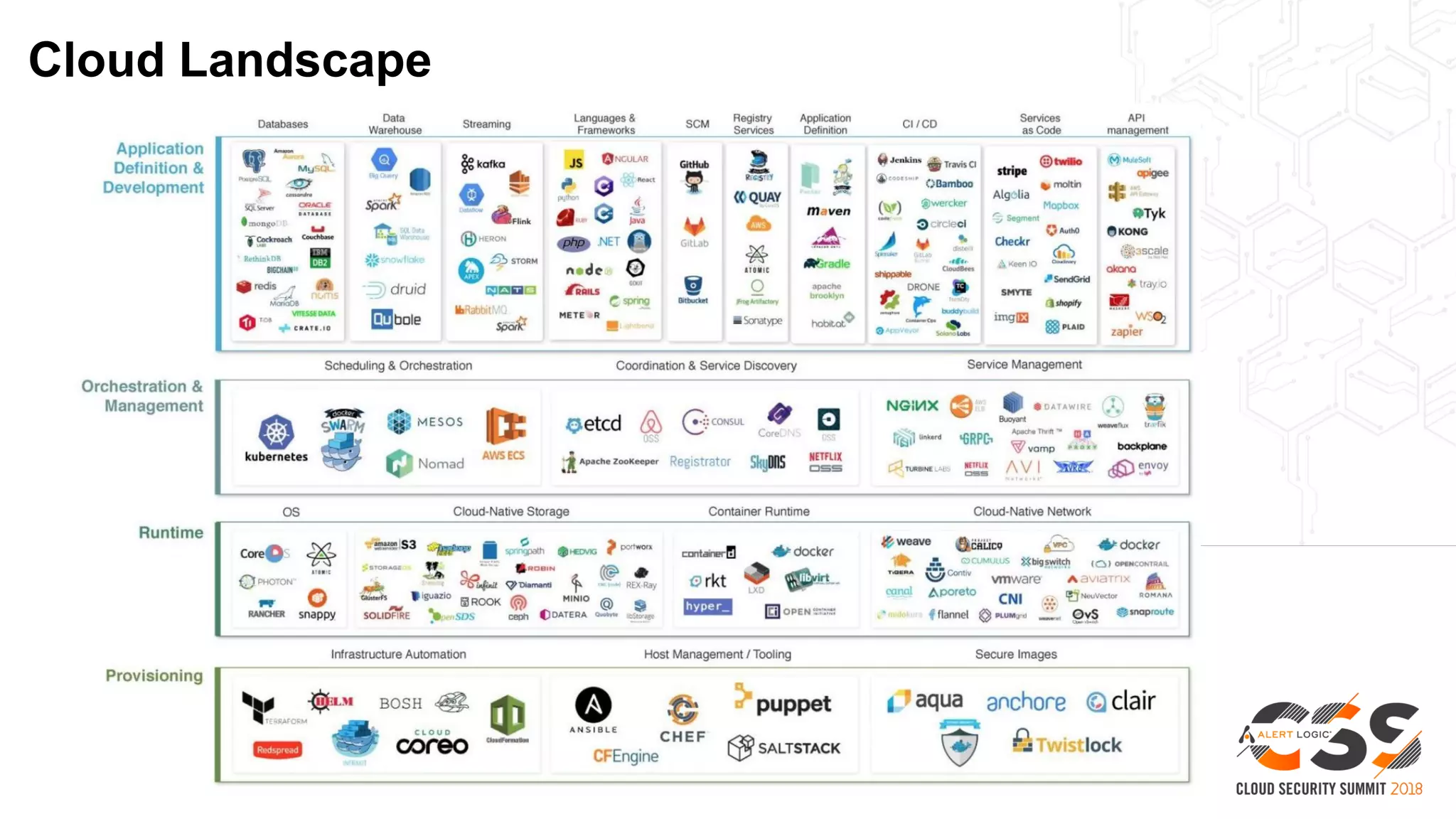
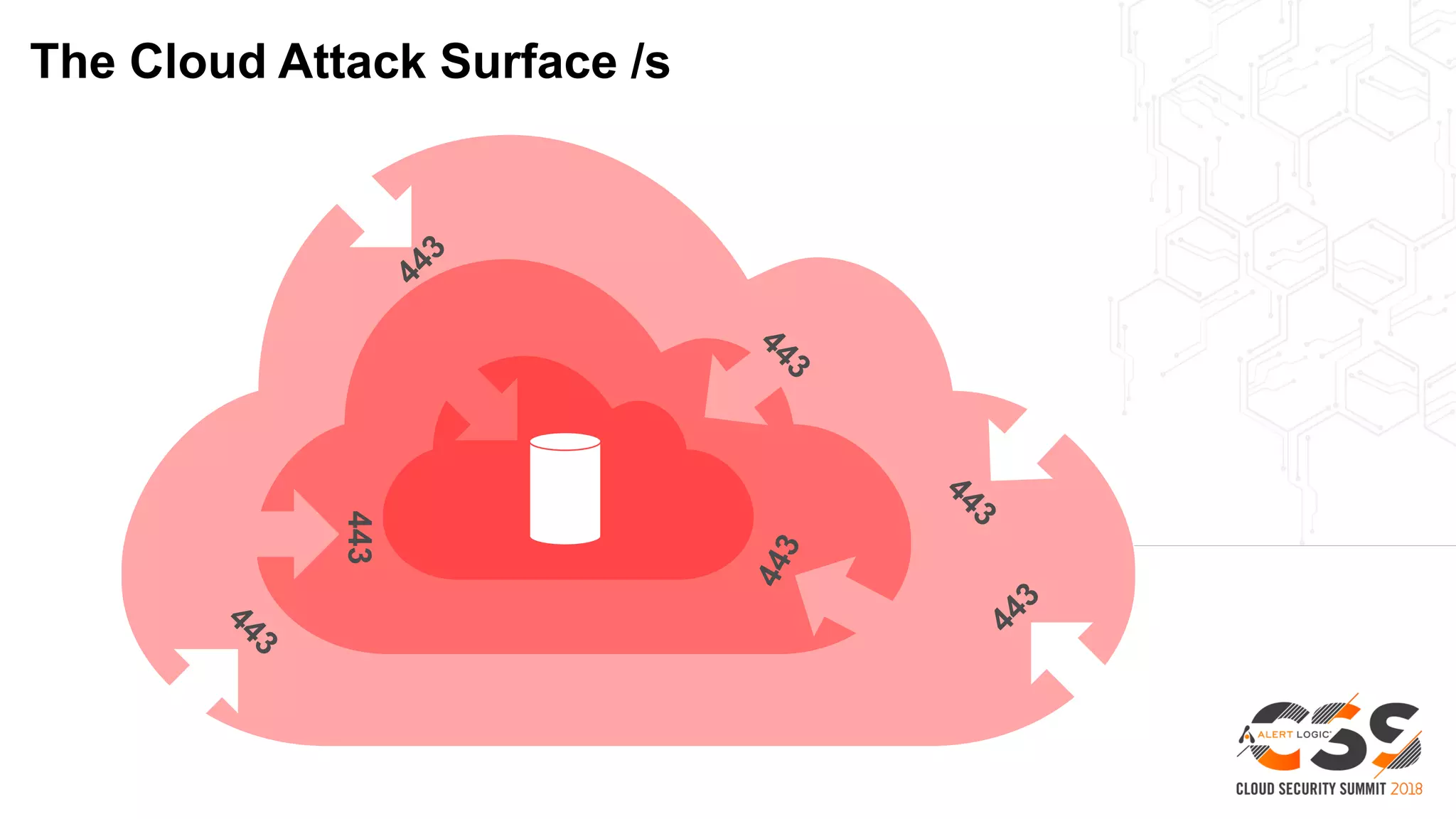
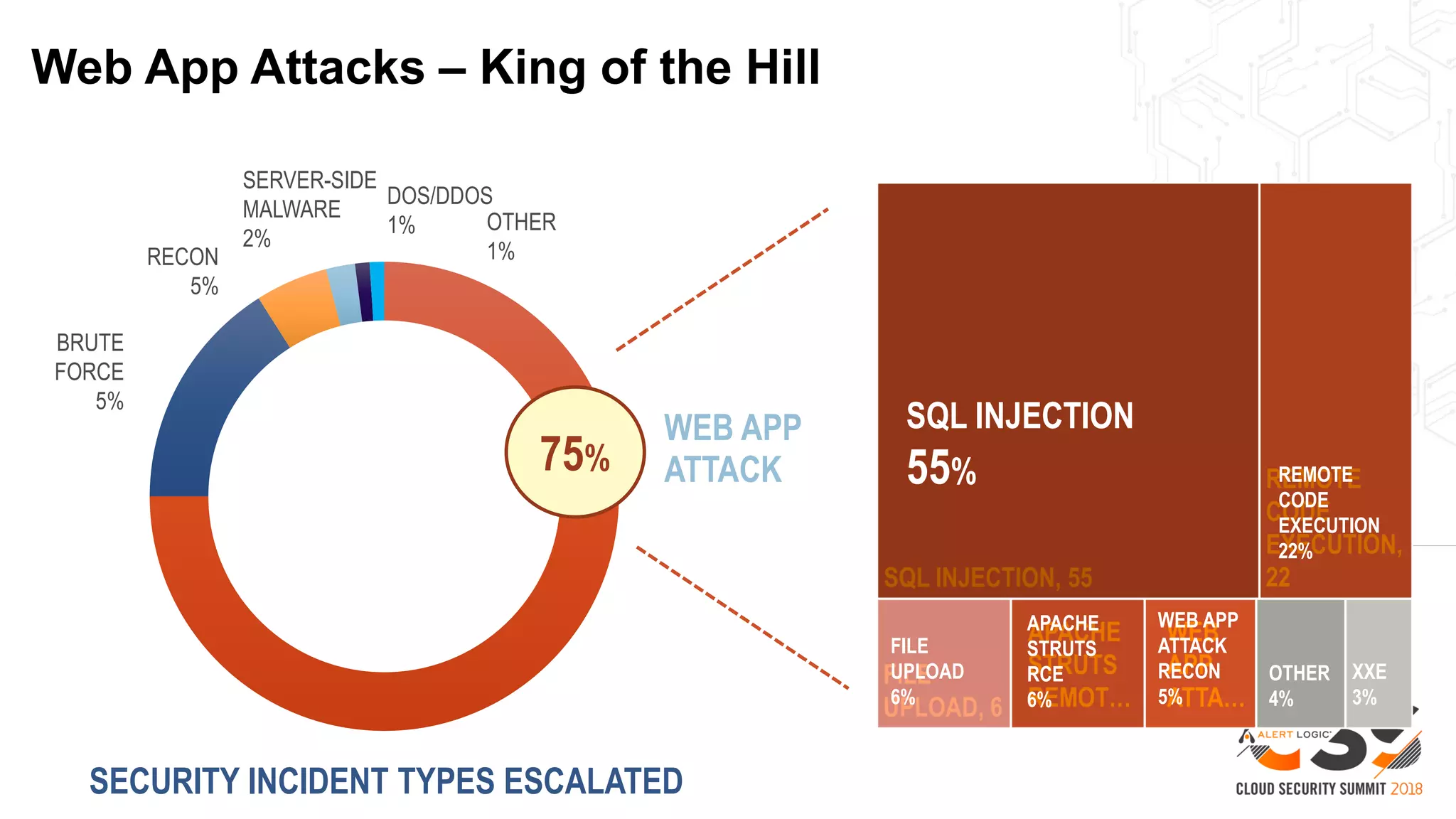
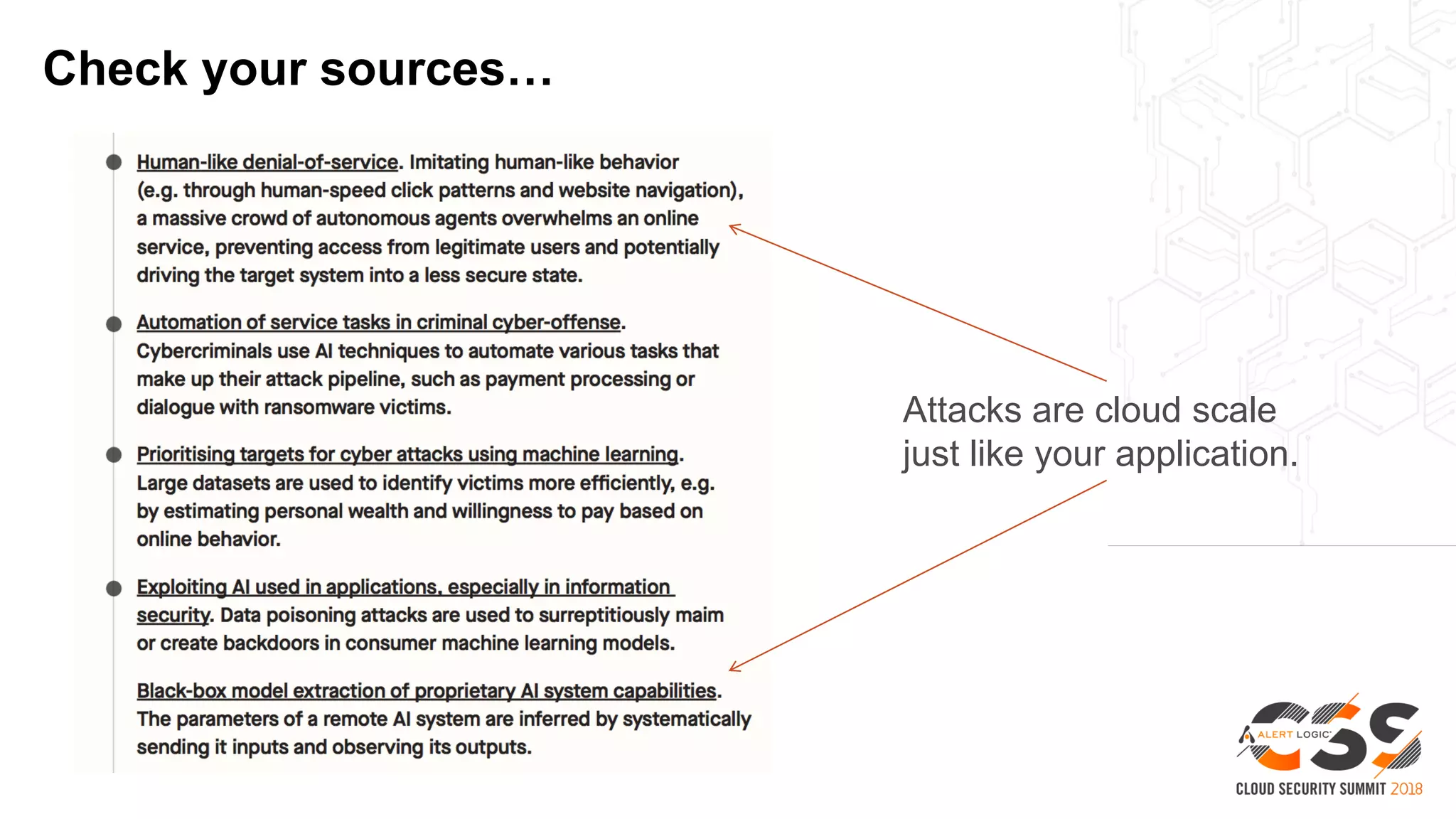
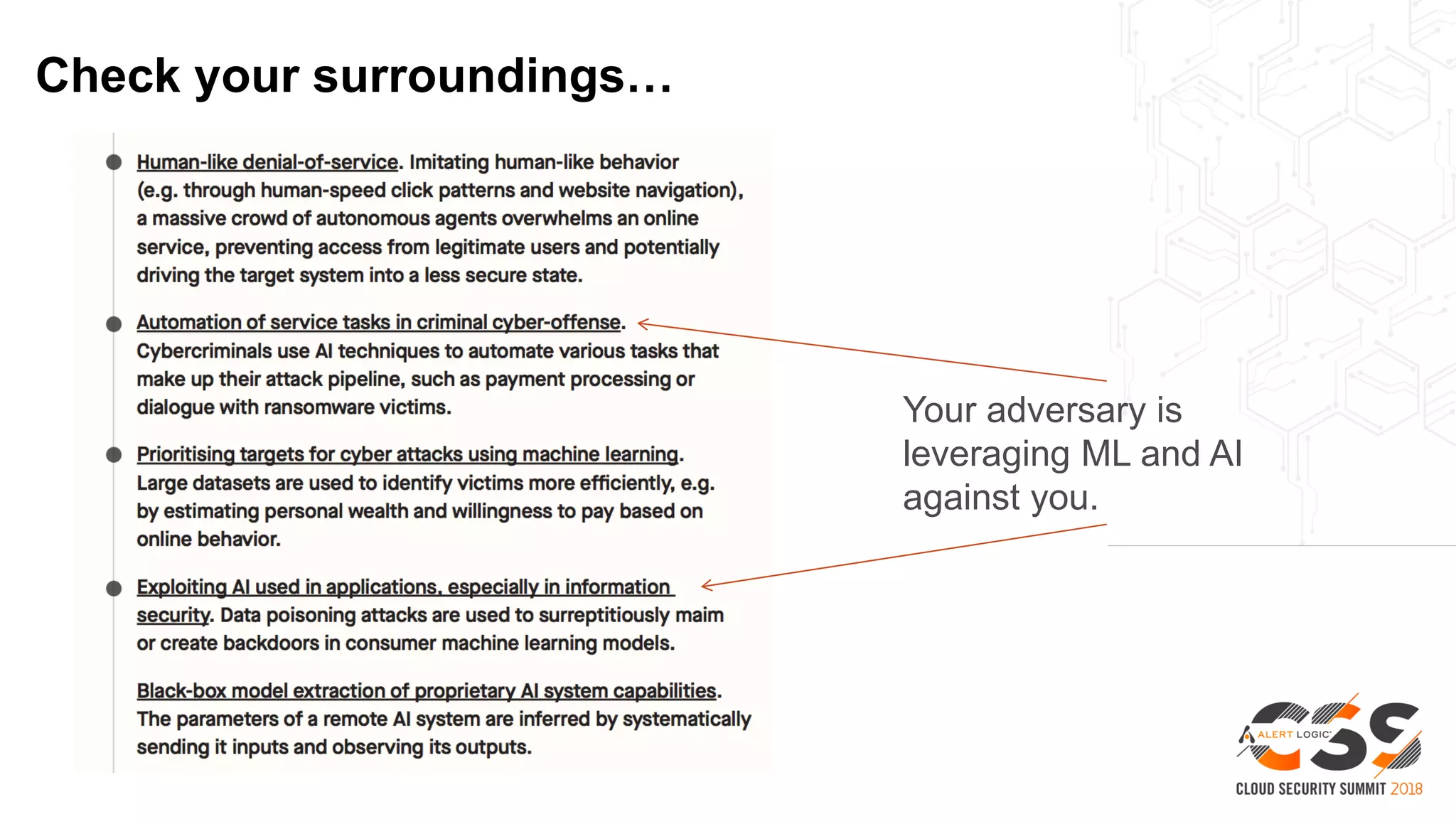
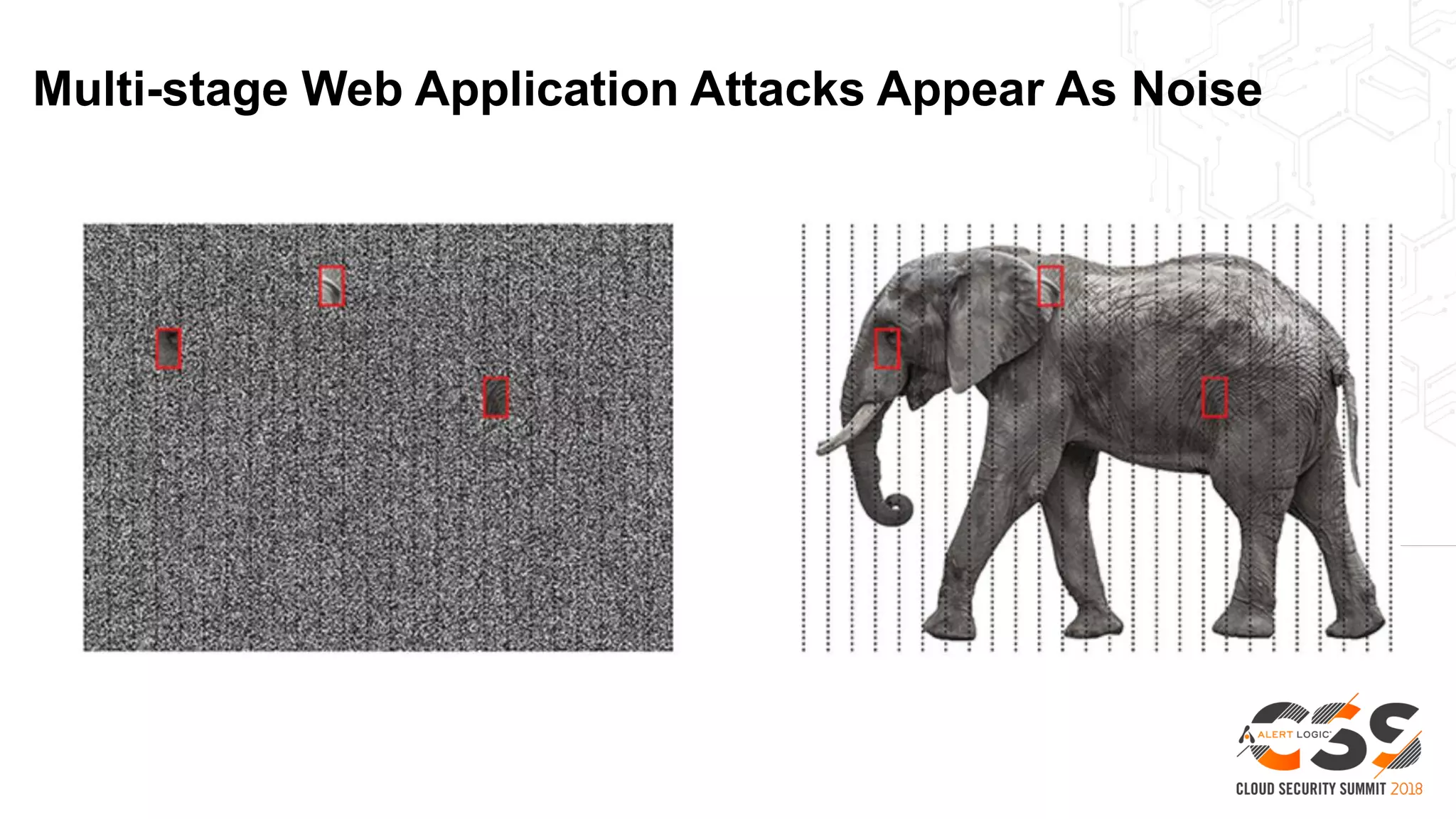
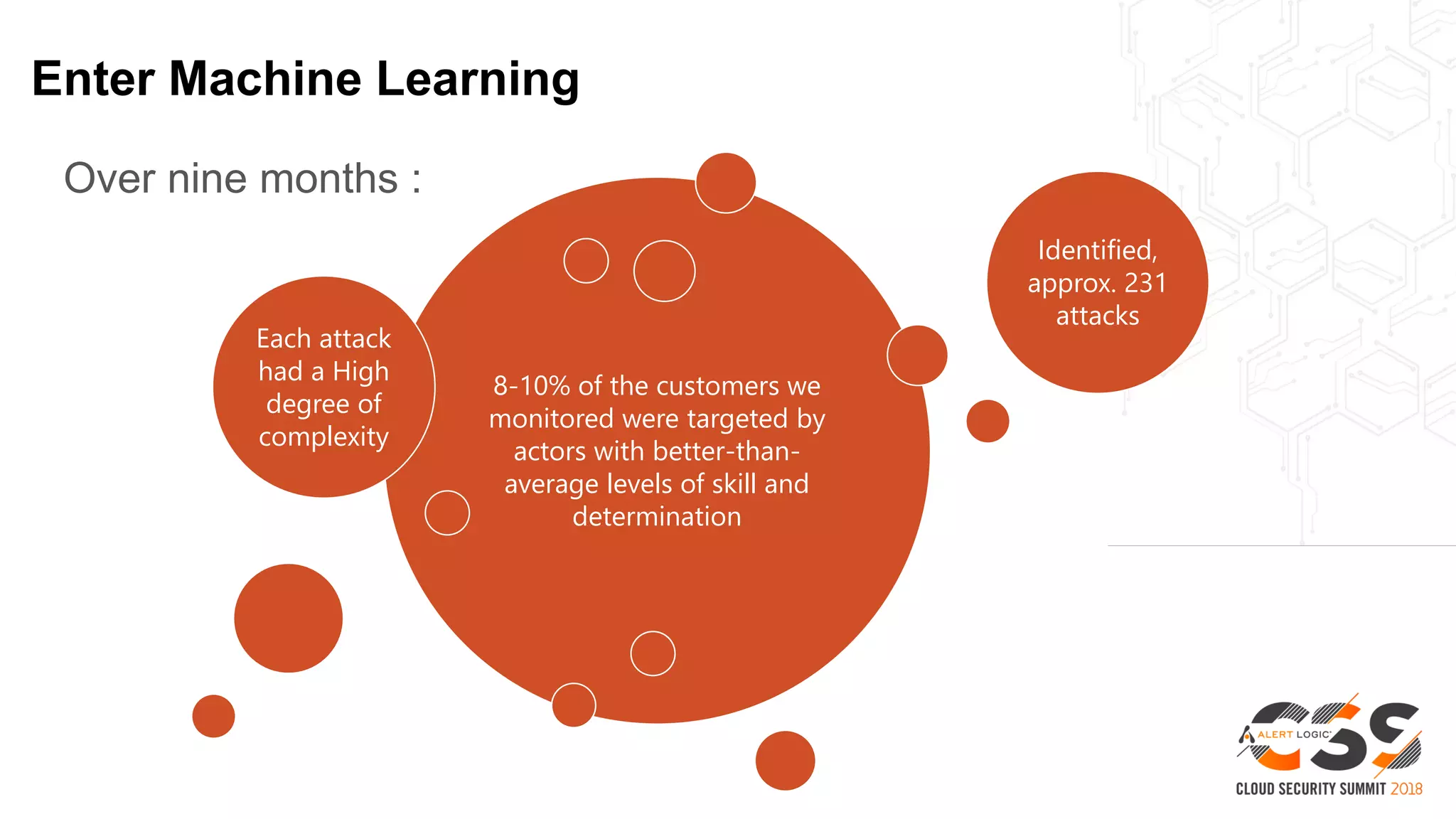
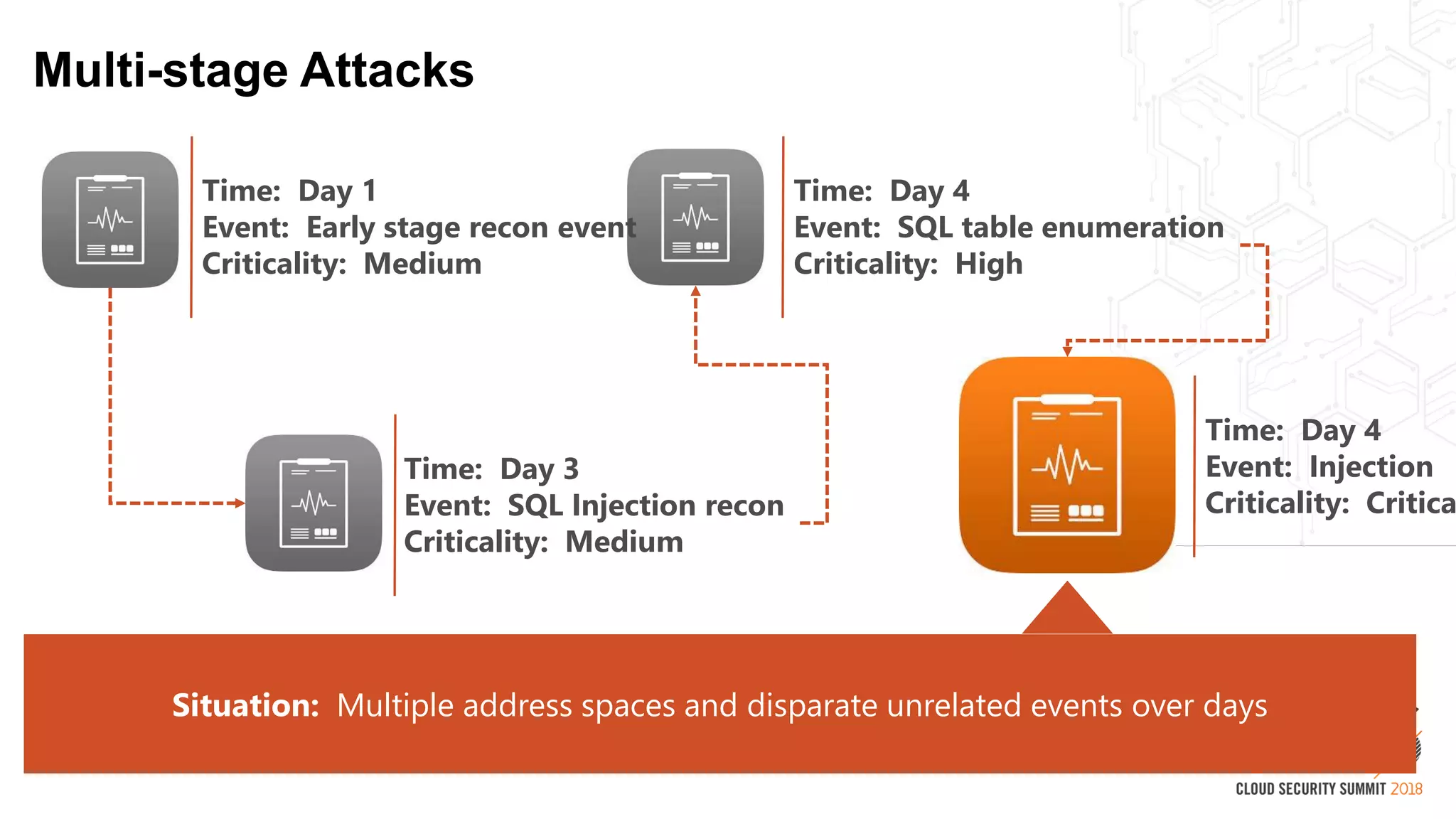
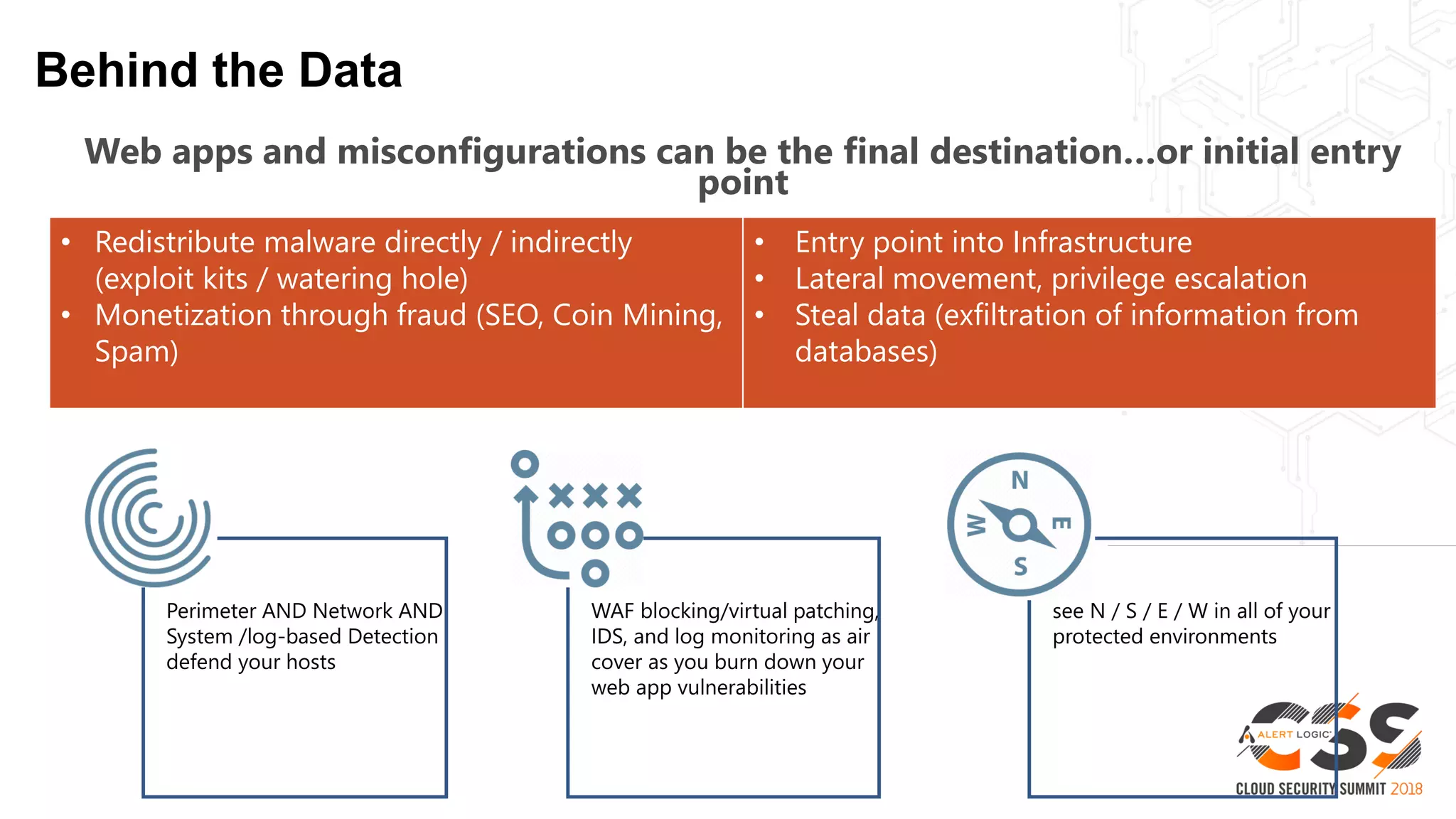
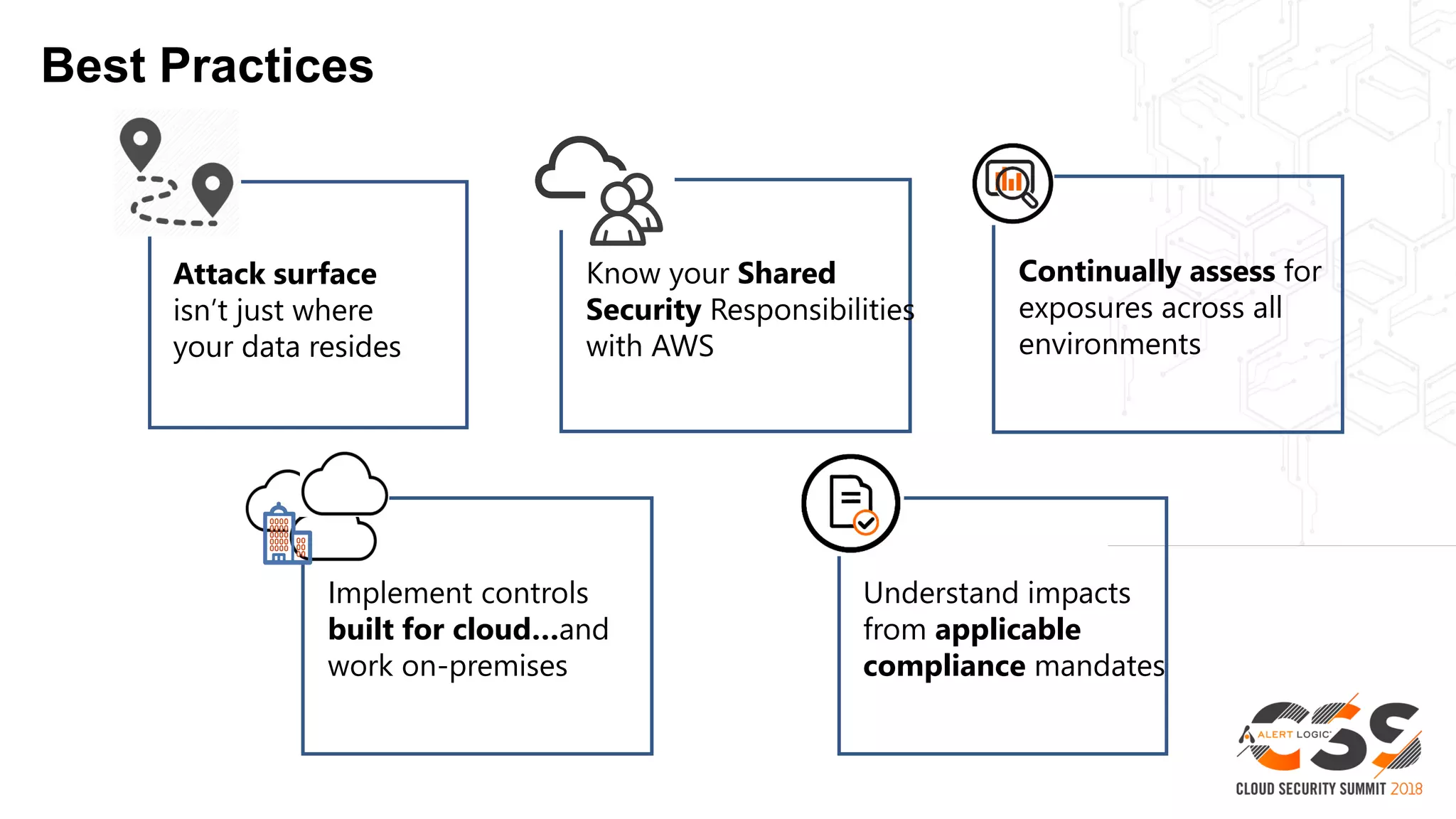
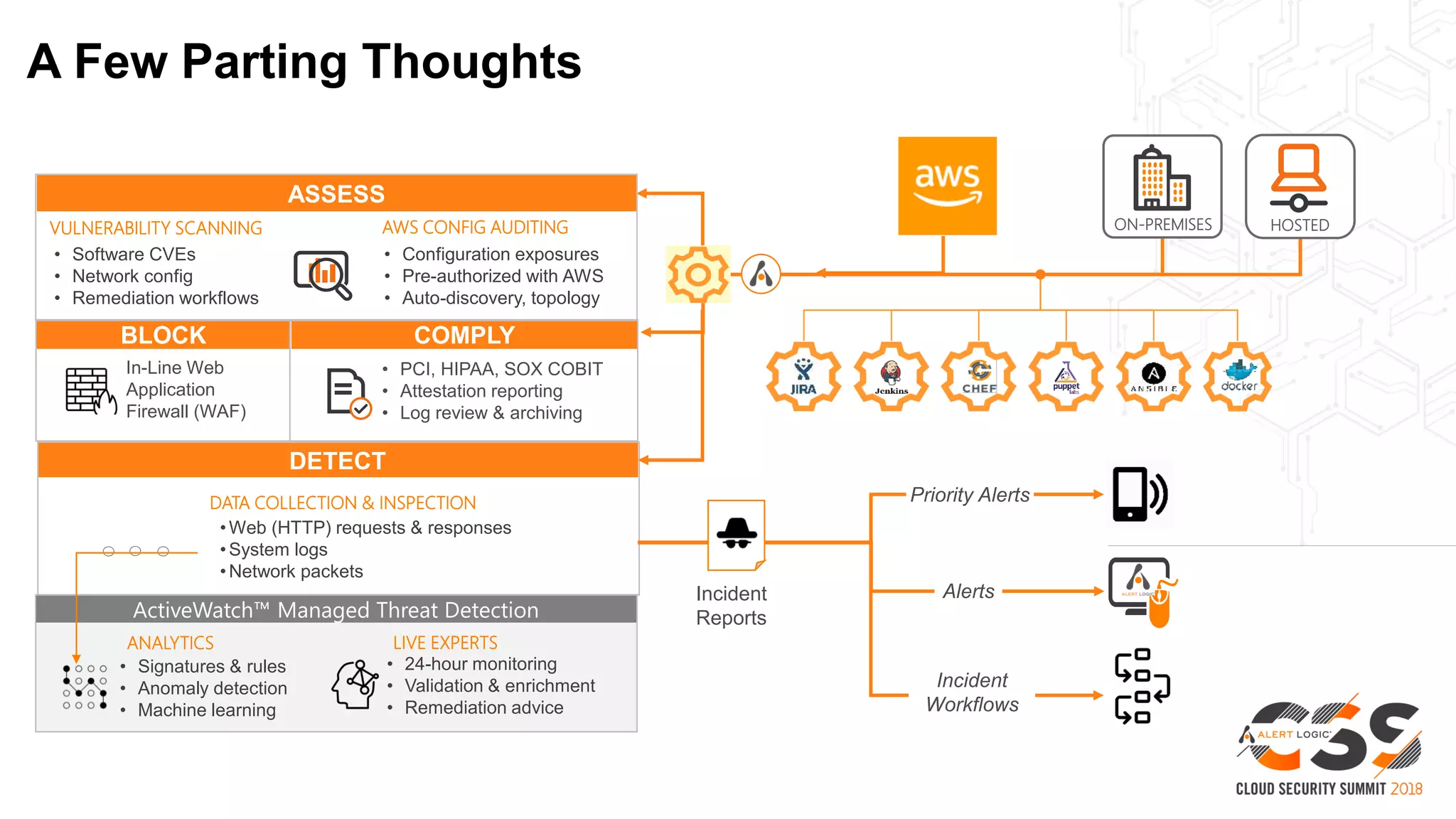
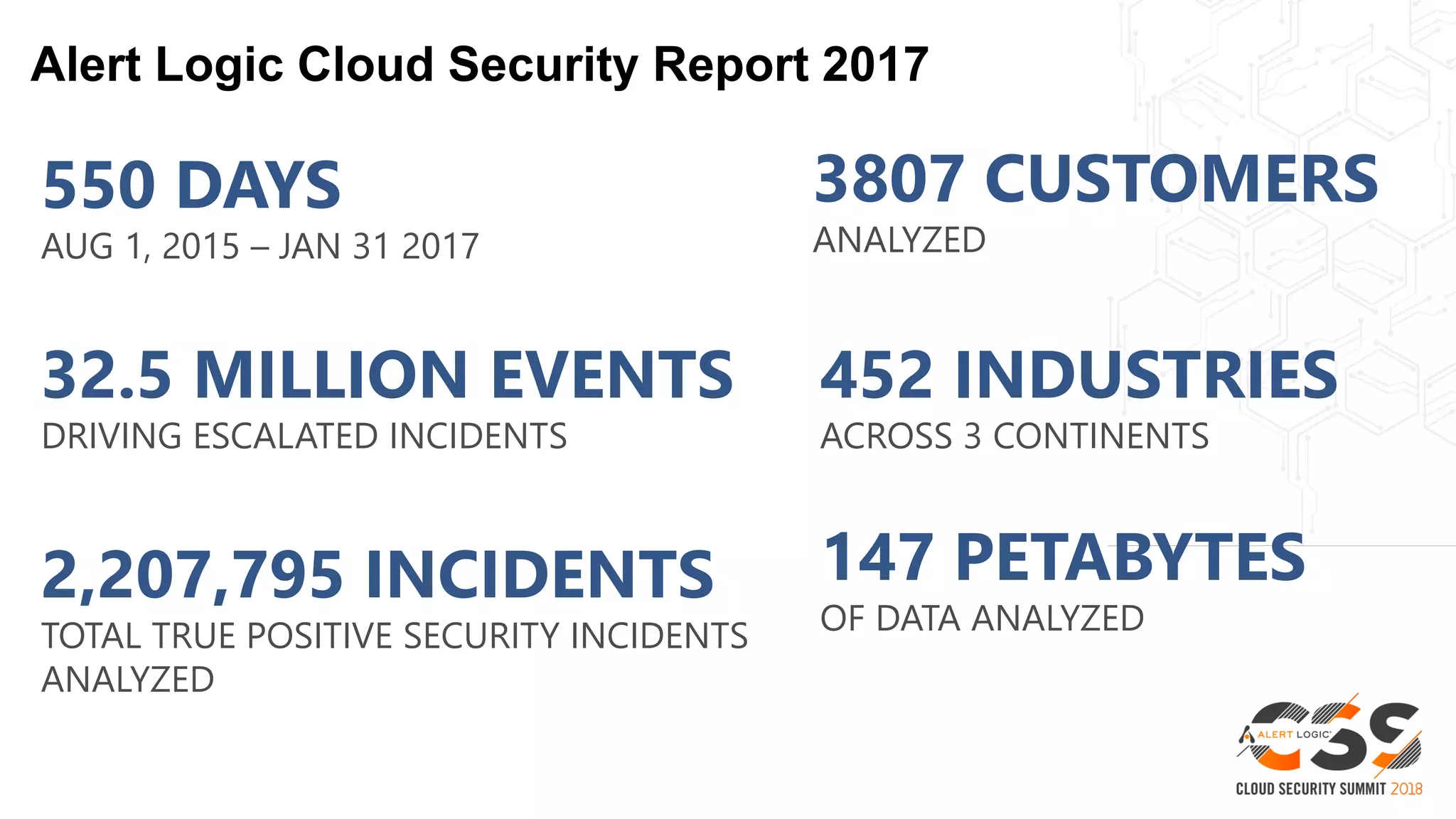
This document discusses security in the cloud and recommends best practices. It notes that while AWS provides many security tools, customers are still responsible for 95% of security failures due to human error. It then outlines various attack types like SQL injection and remote code execution that target web applications. The document recommends leveraging machine learning and multiple detection techniques to identify multi-stage attacks. It emphasizes the need to secure the entire attack surface, including on-premises environments, and highlights services like Alert Logic that provide 24/7 monitoring, analytics, and security experts to help detect and respond to threats.