Embed presentation
Downloaded 10 times
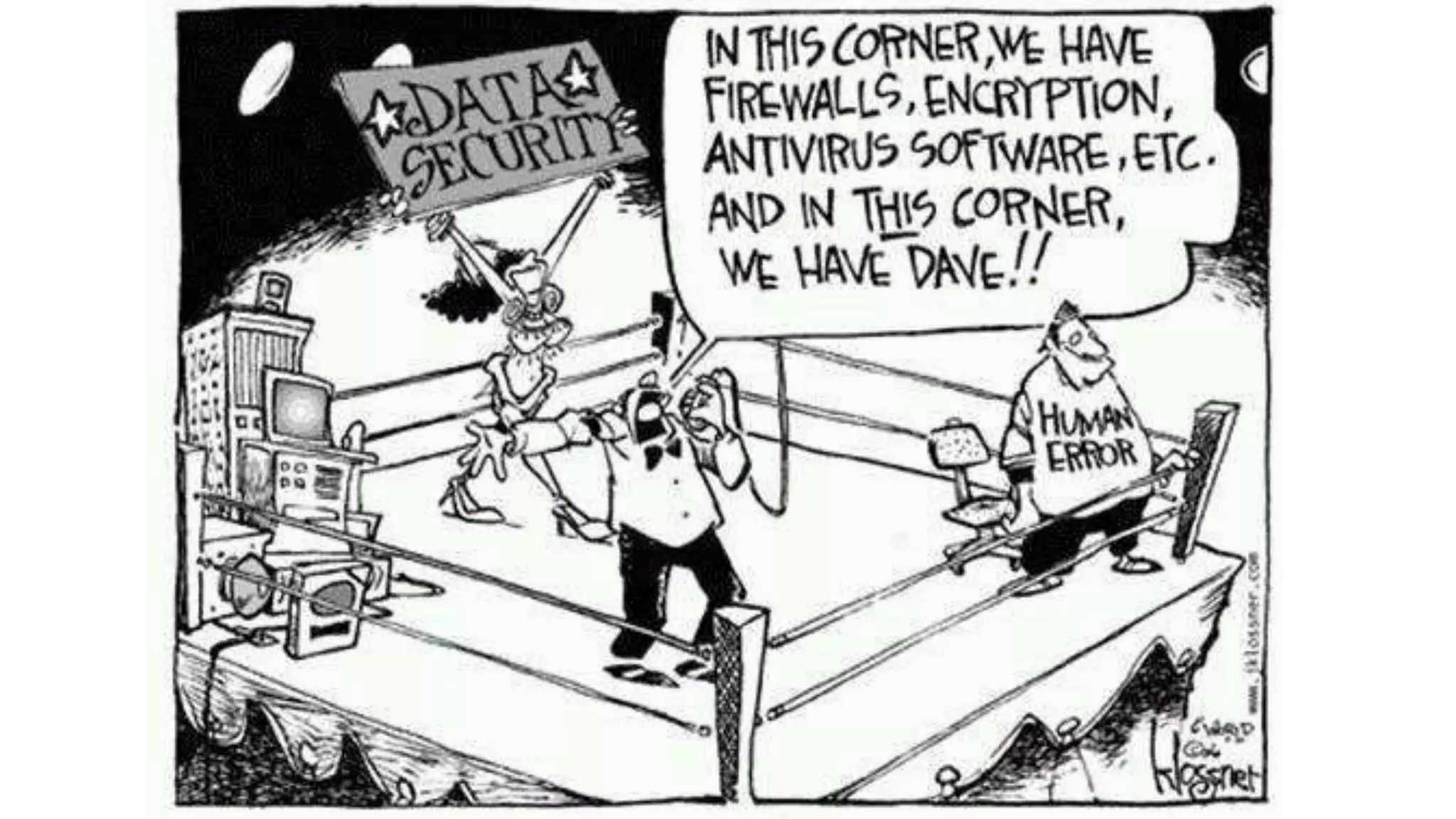




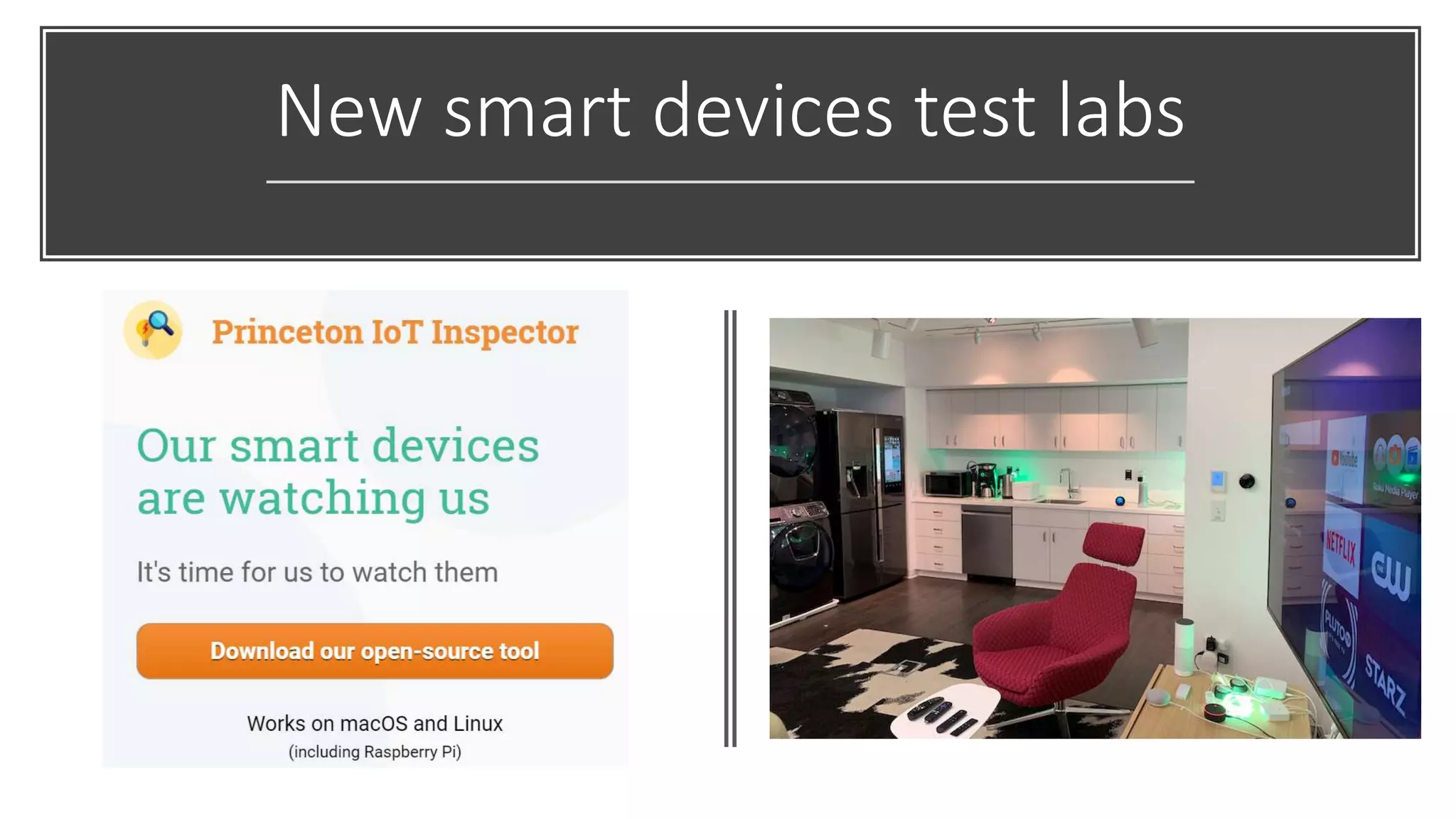

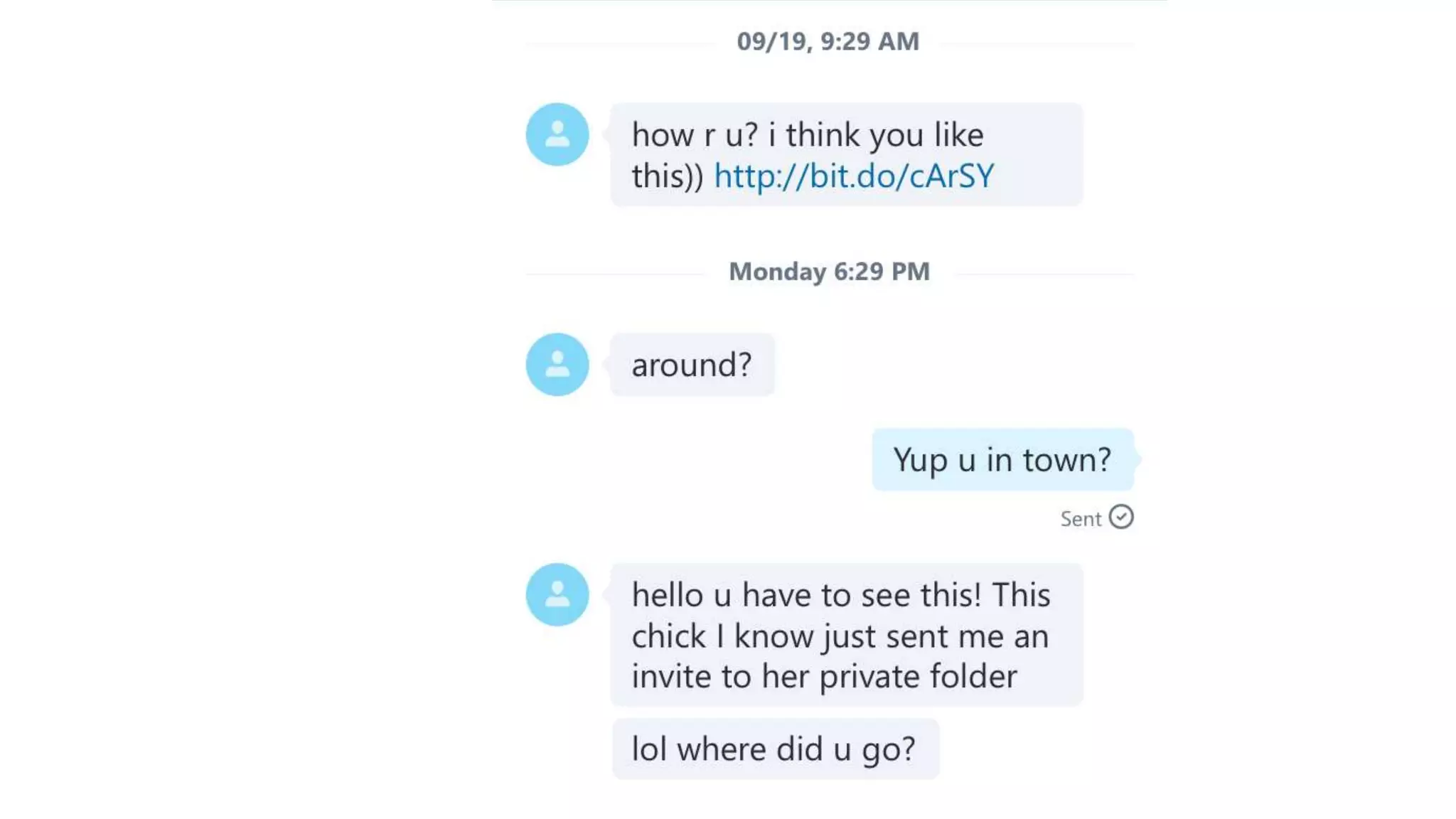

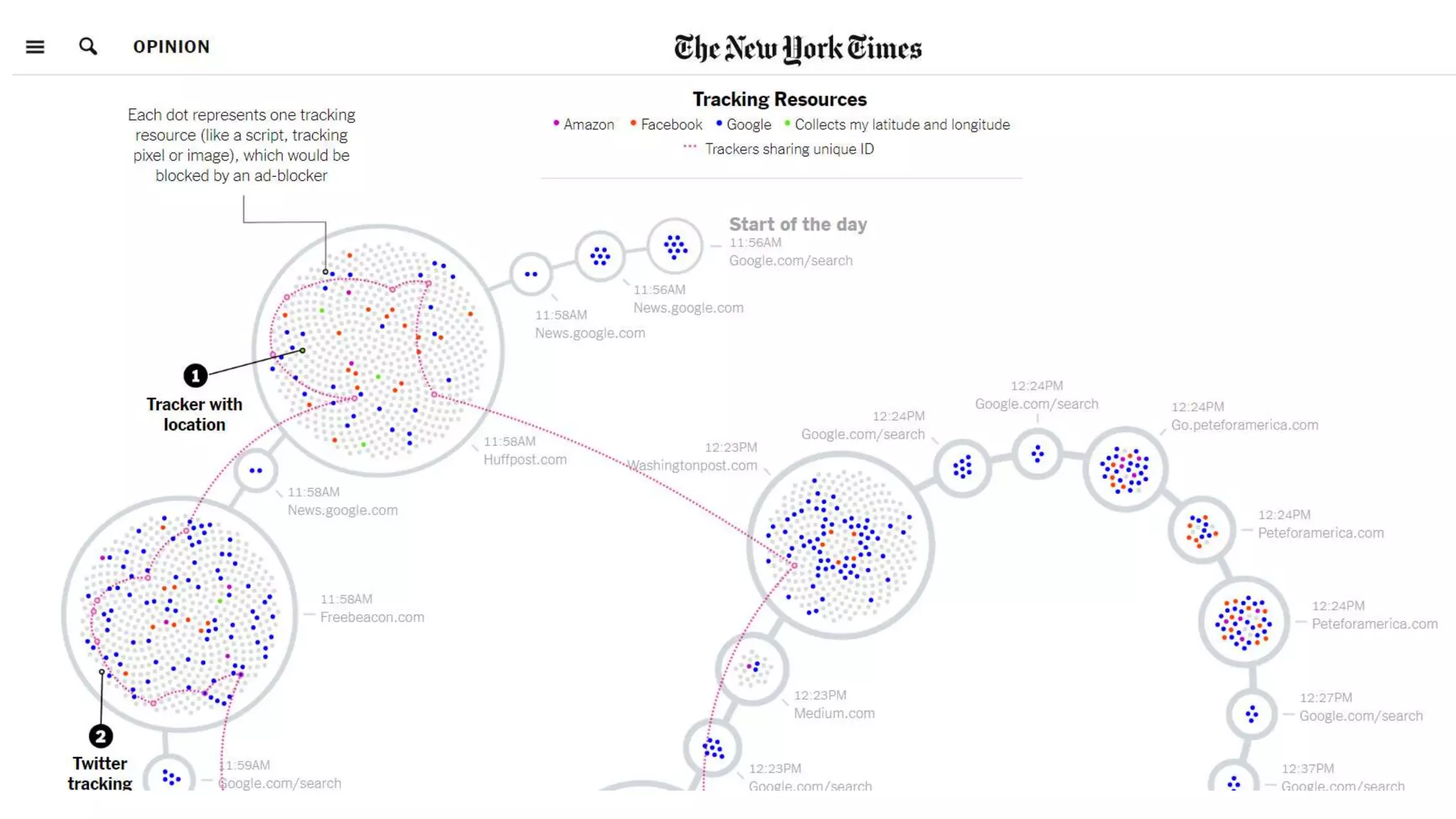

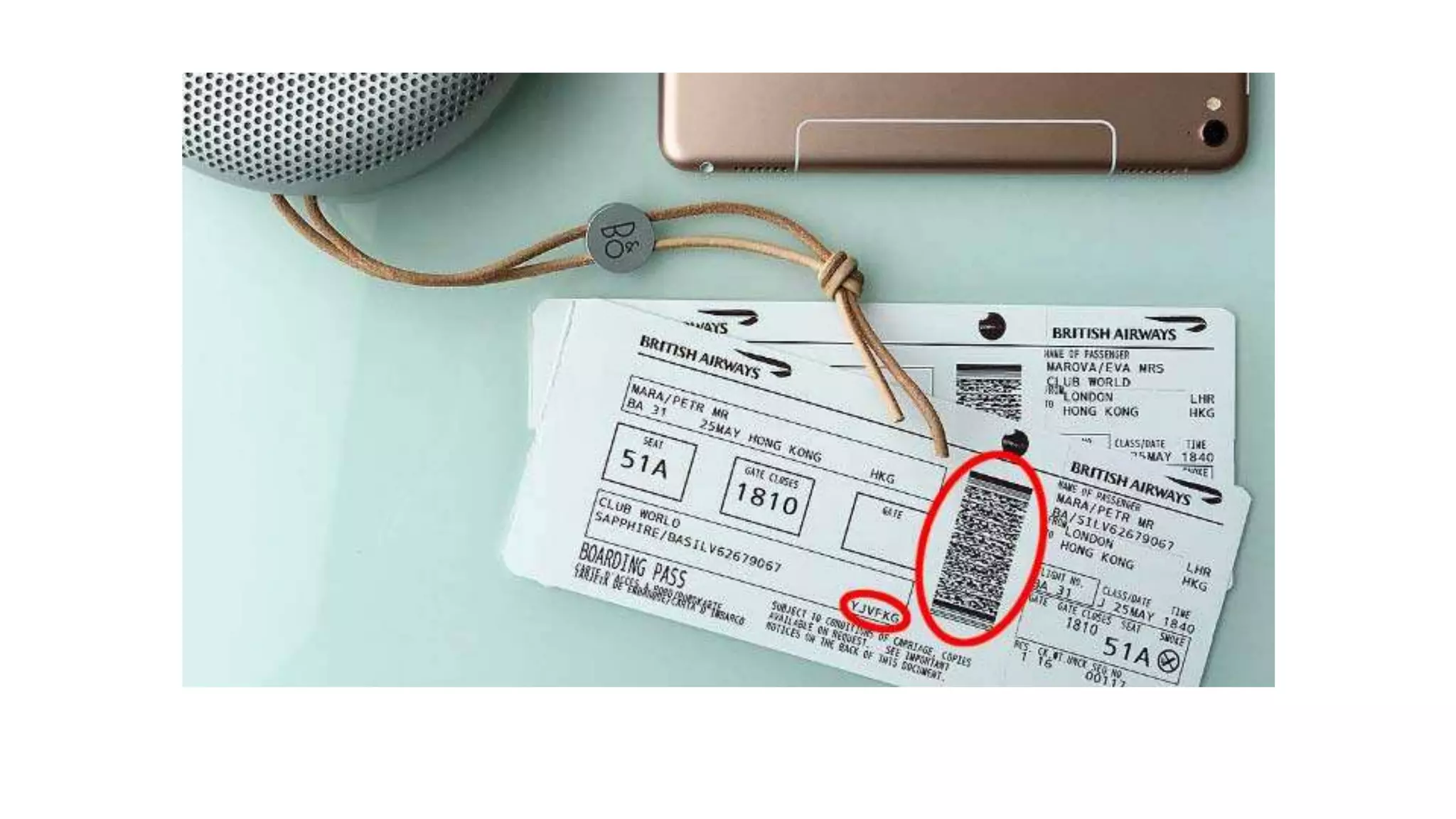



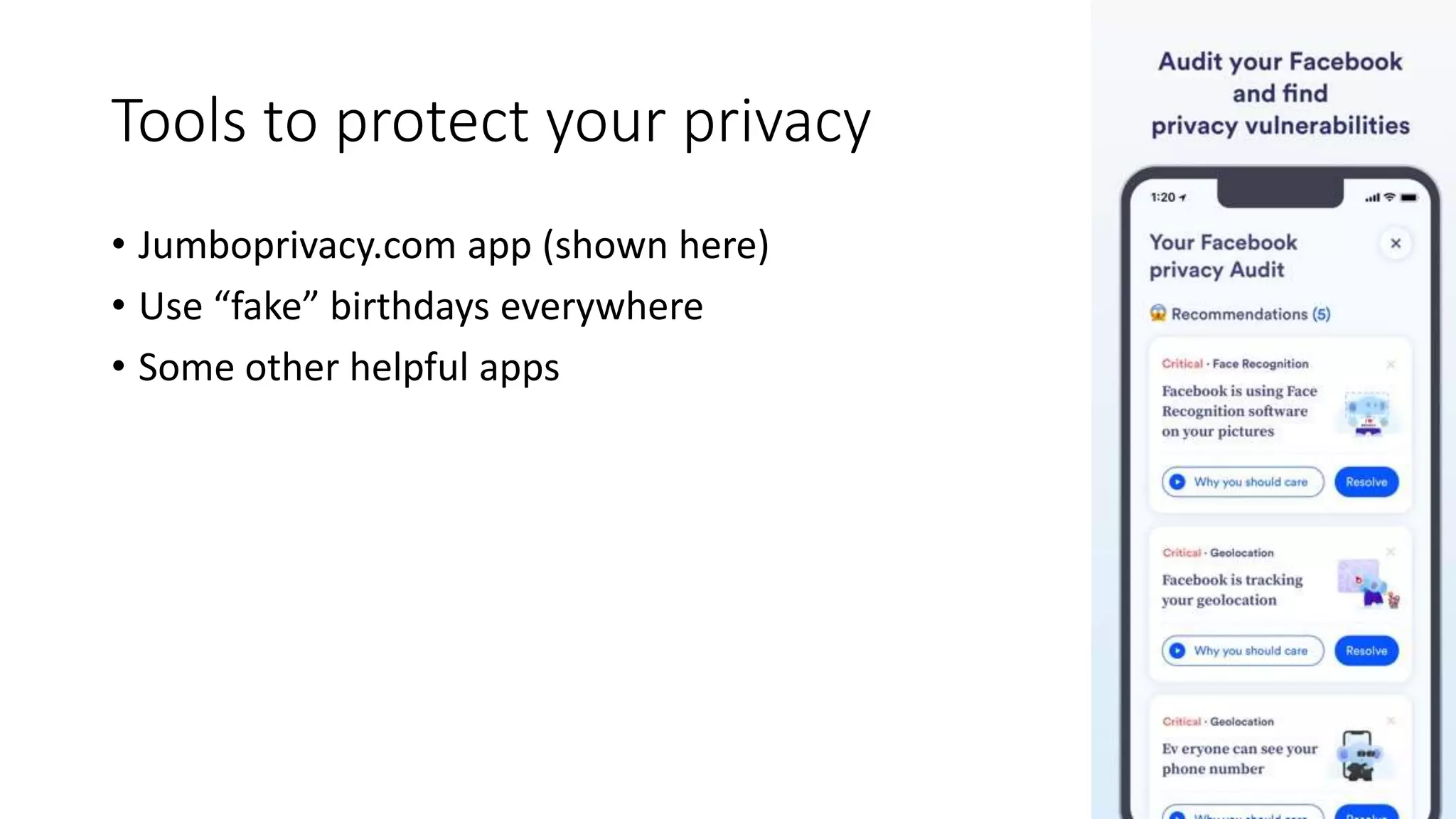


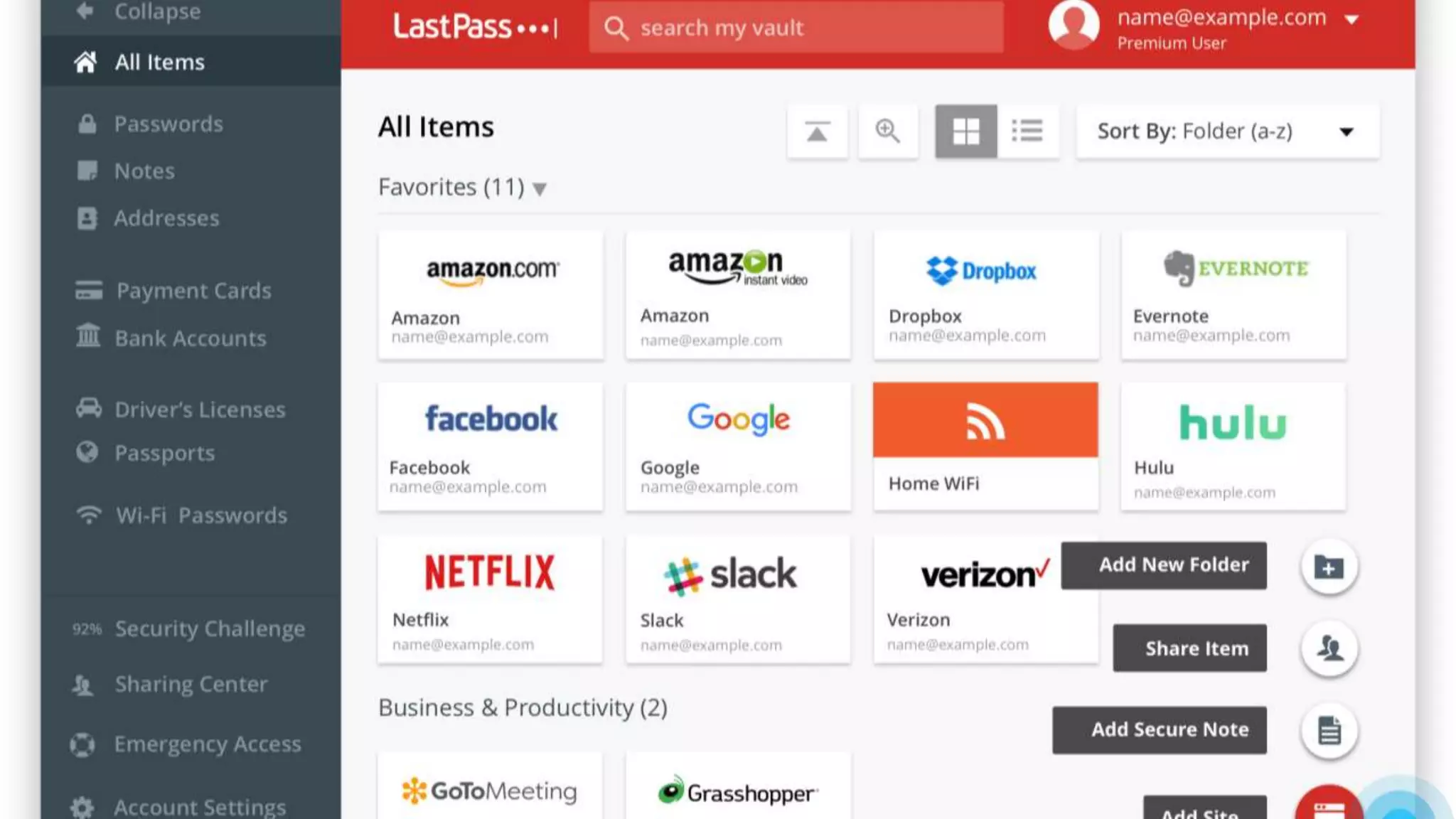


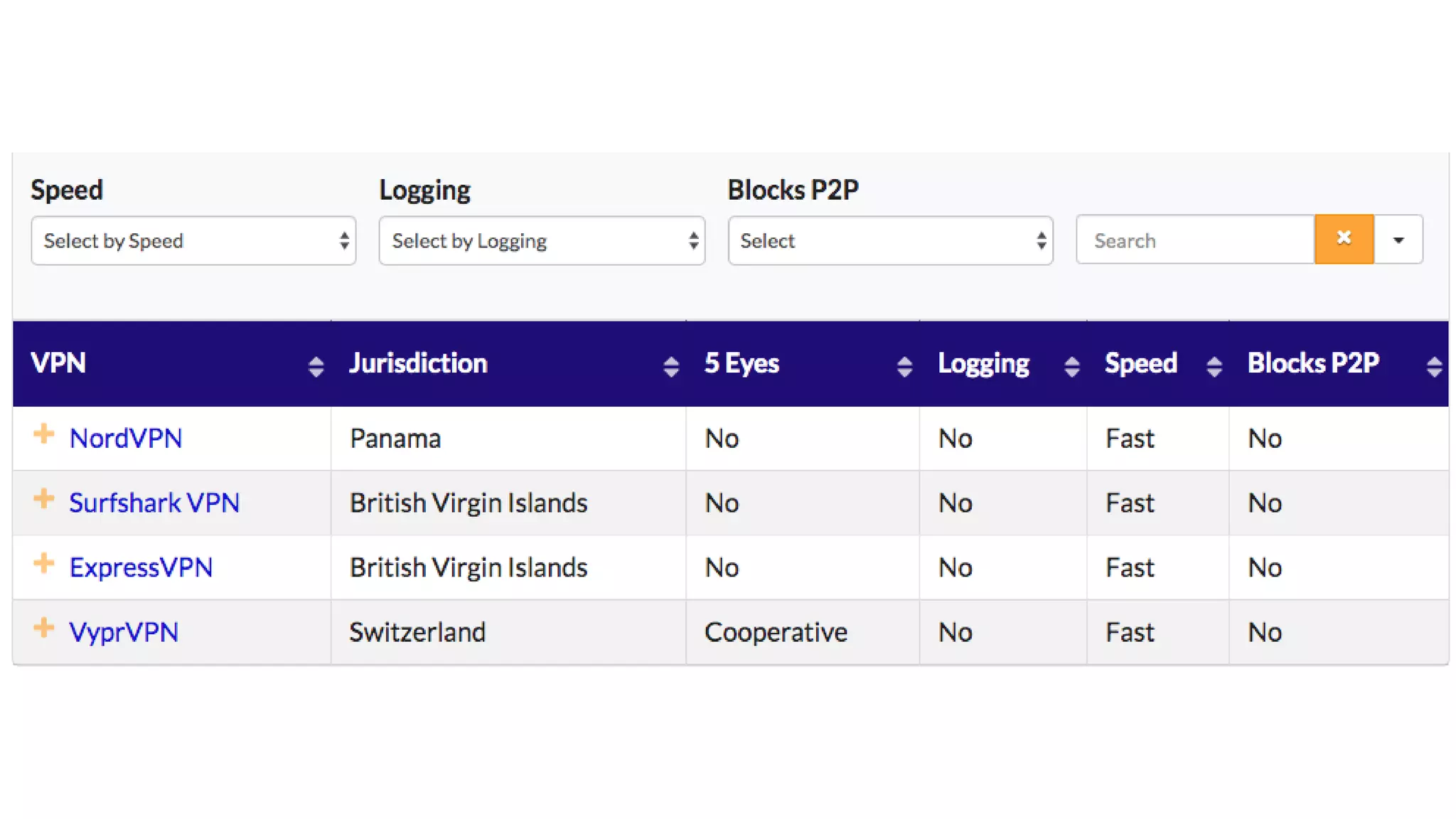






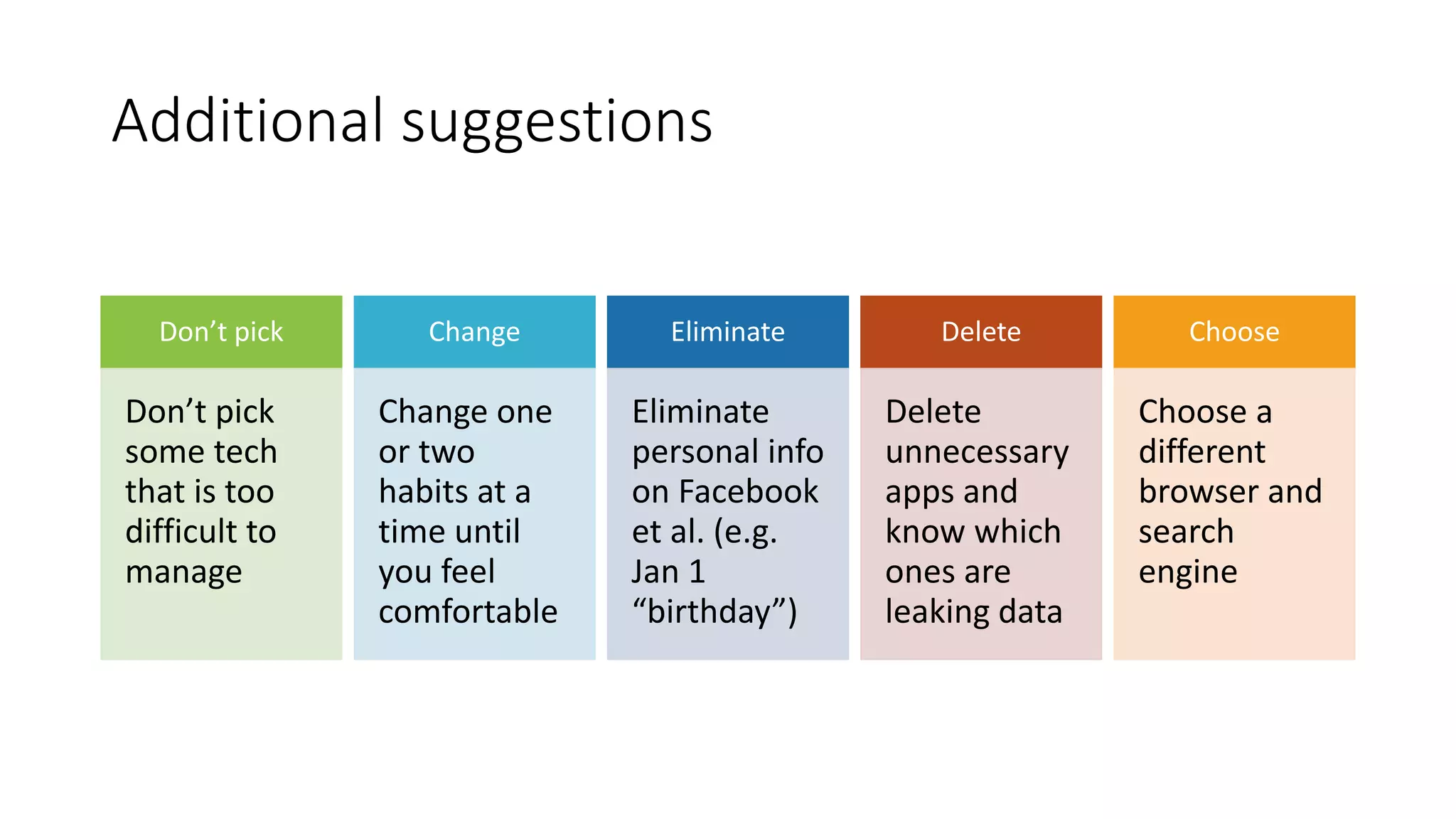


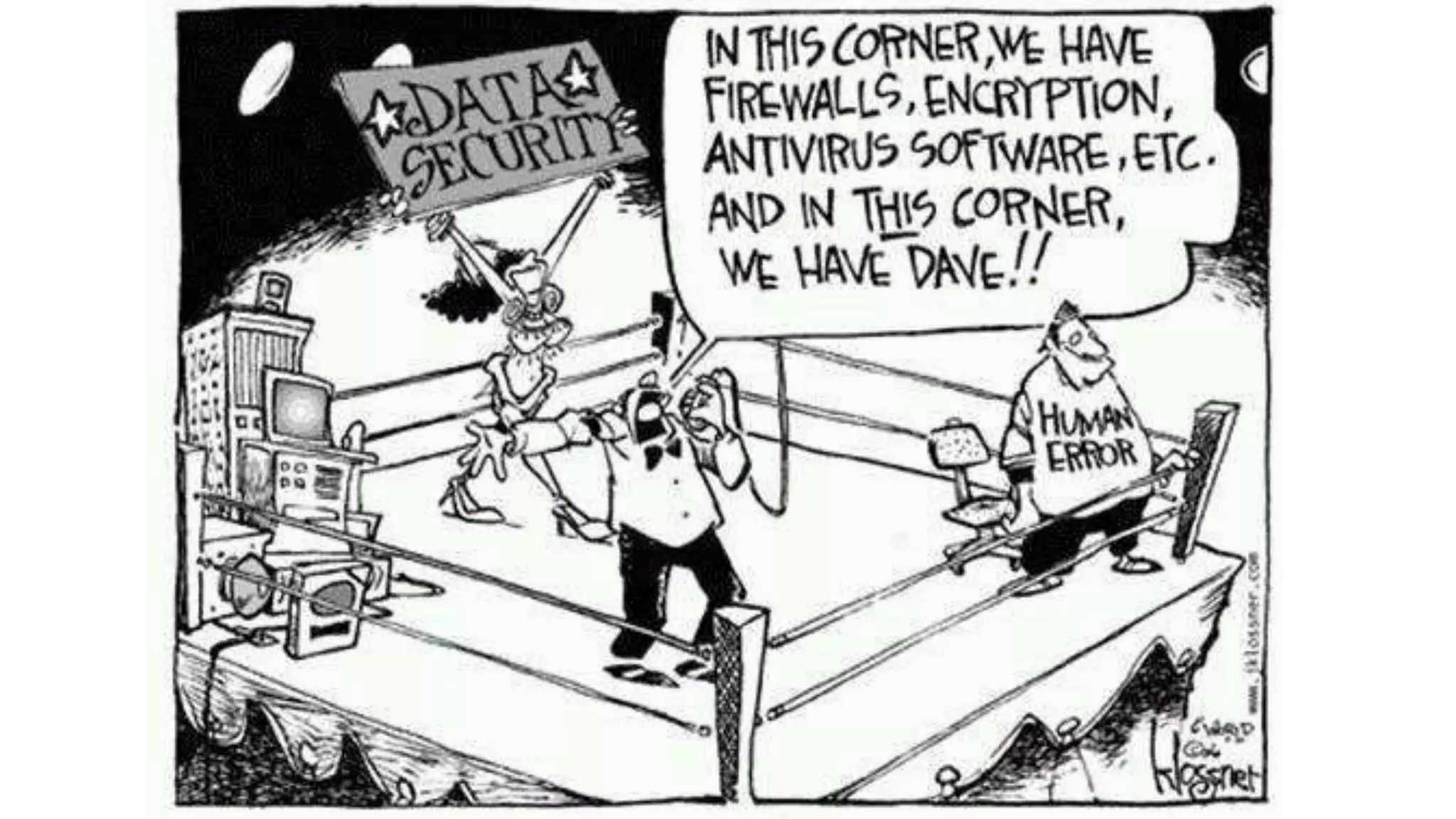
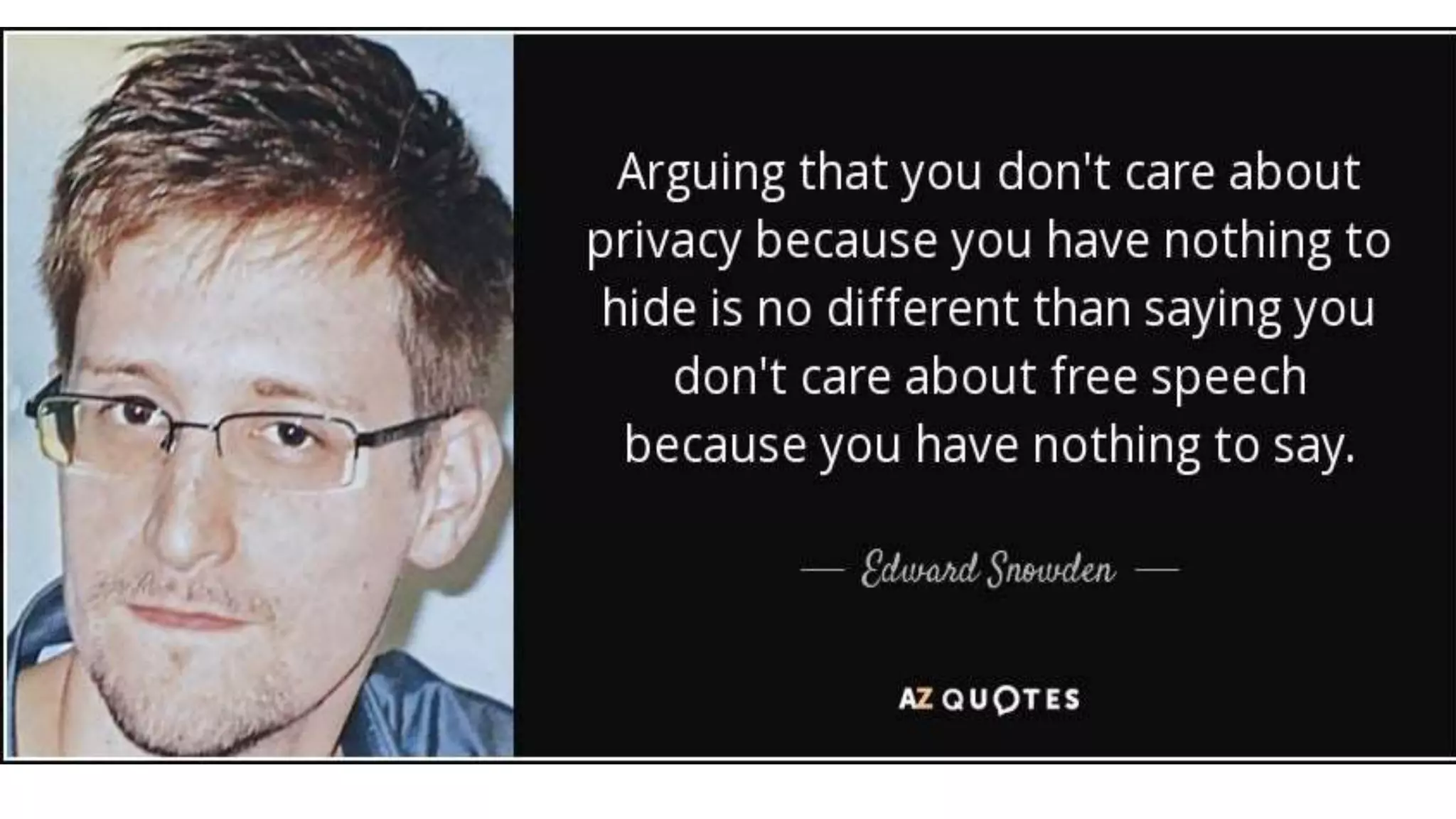
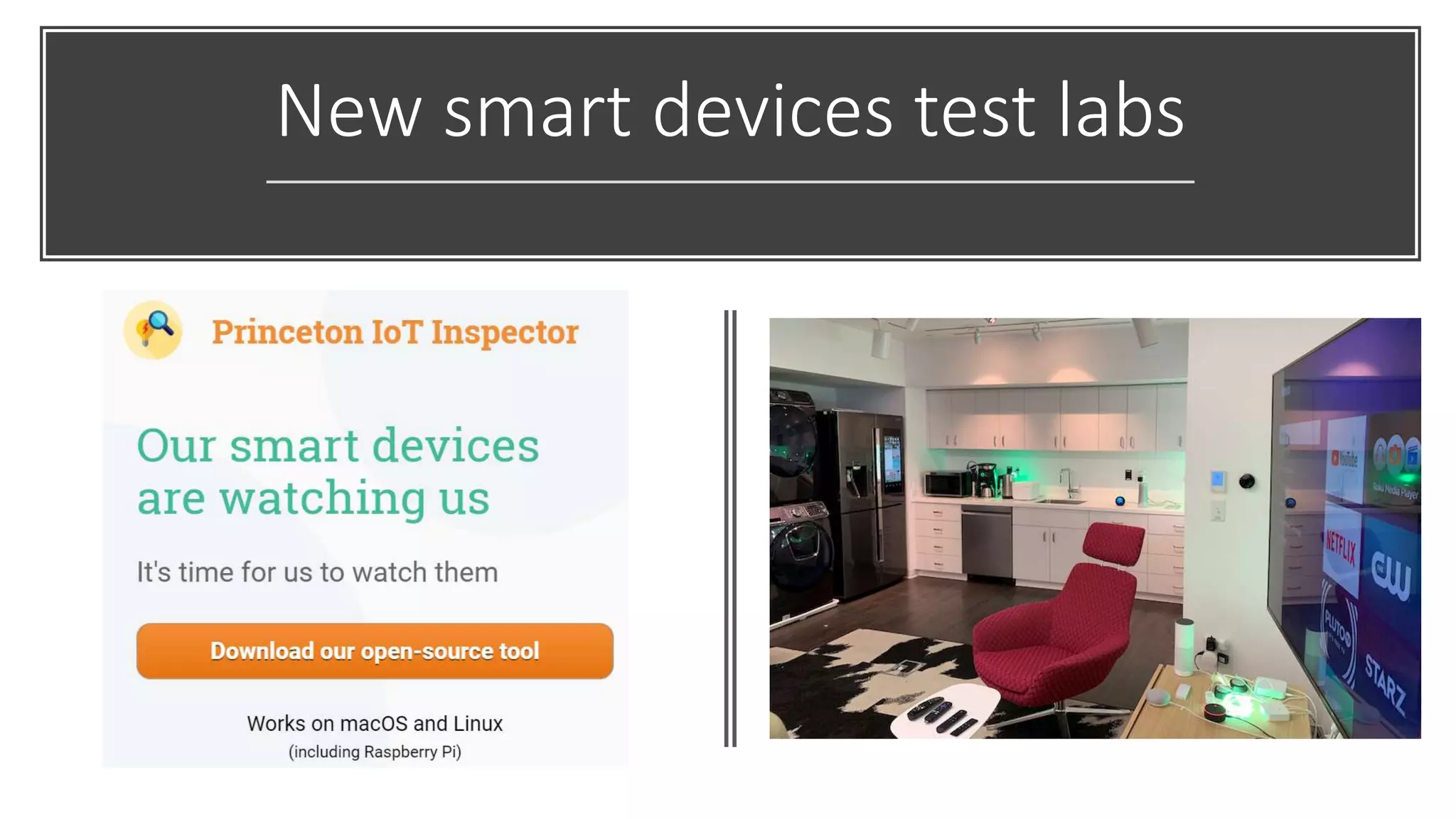
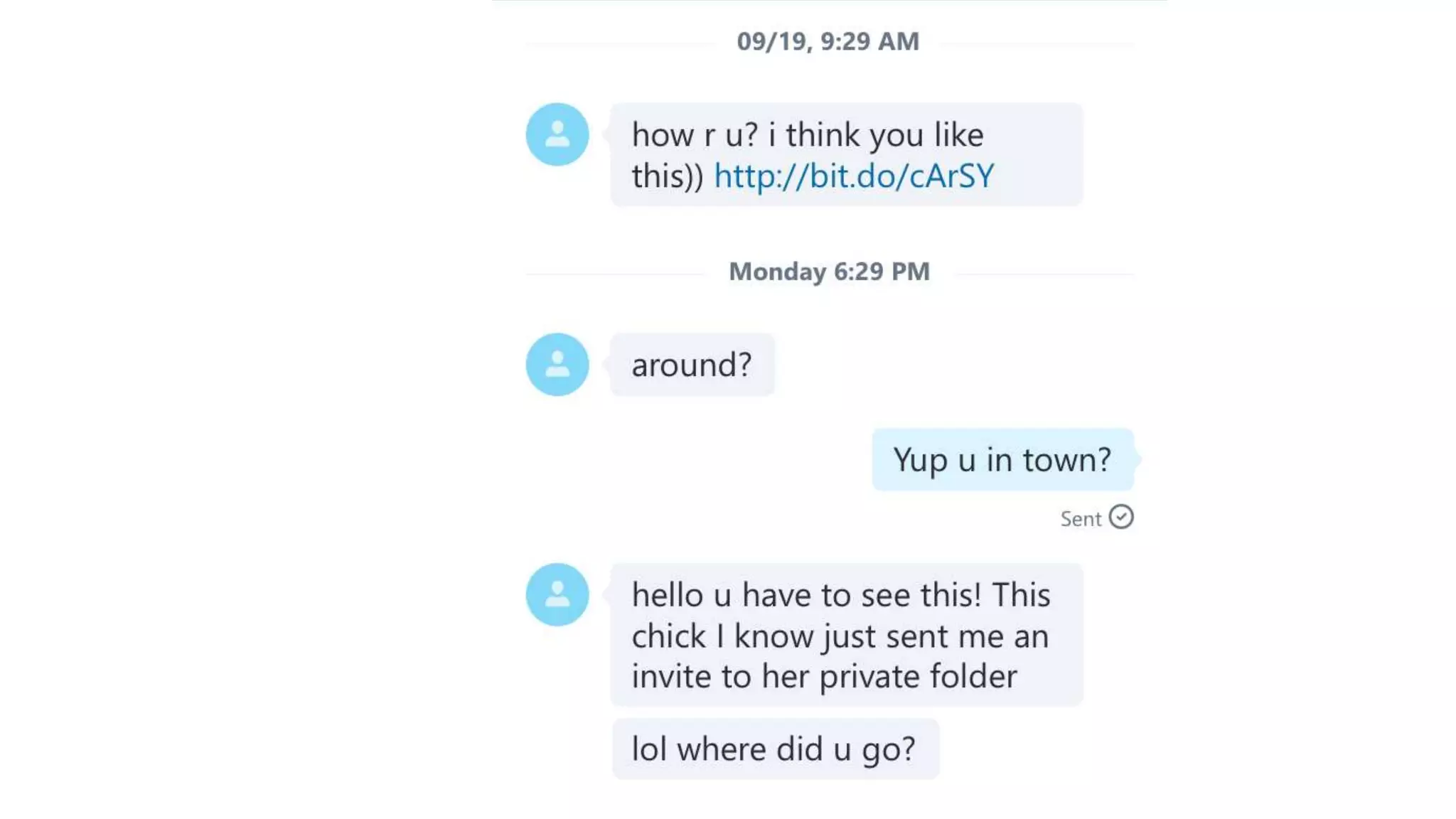
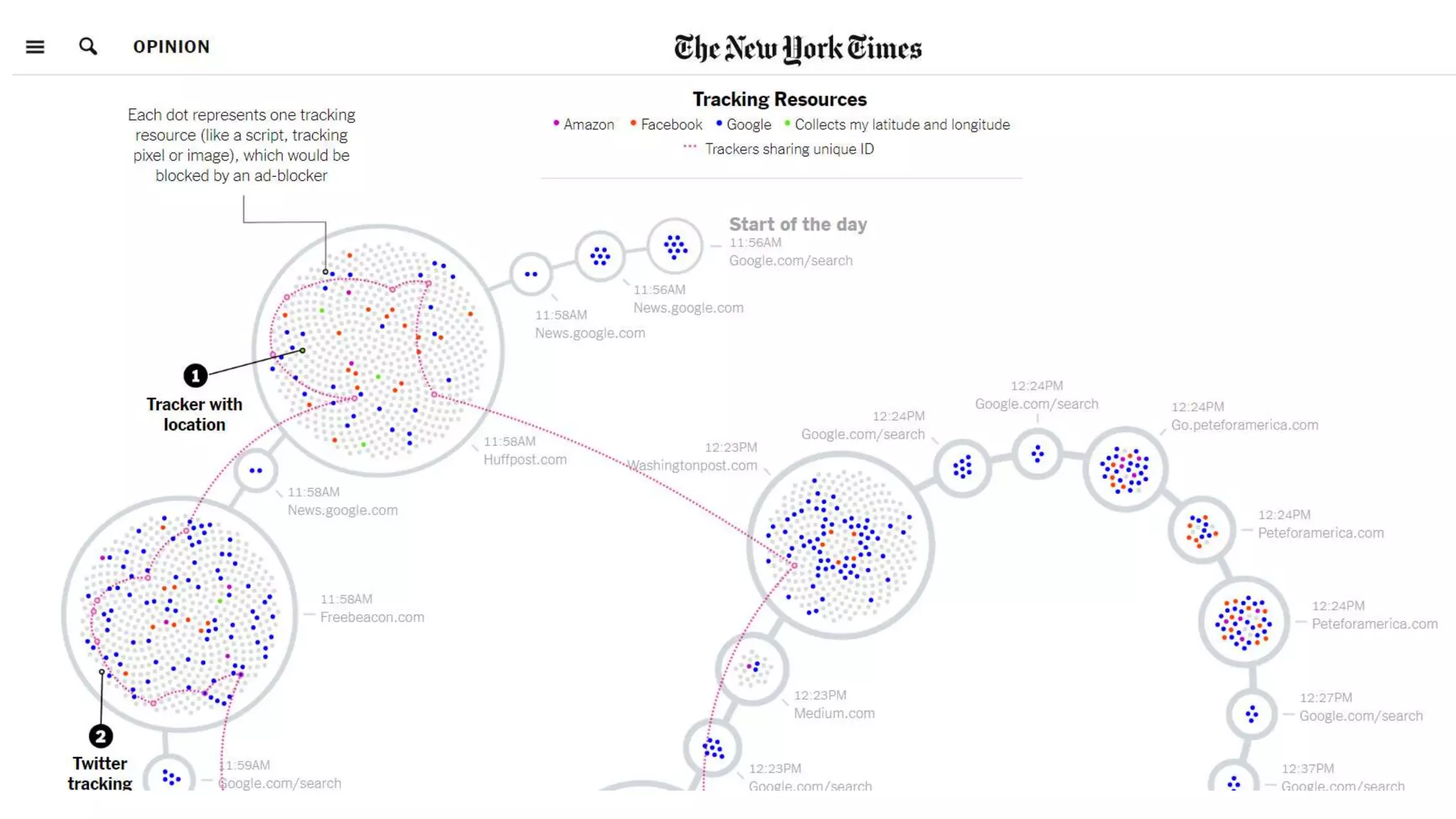
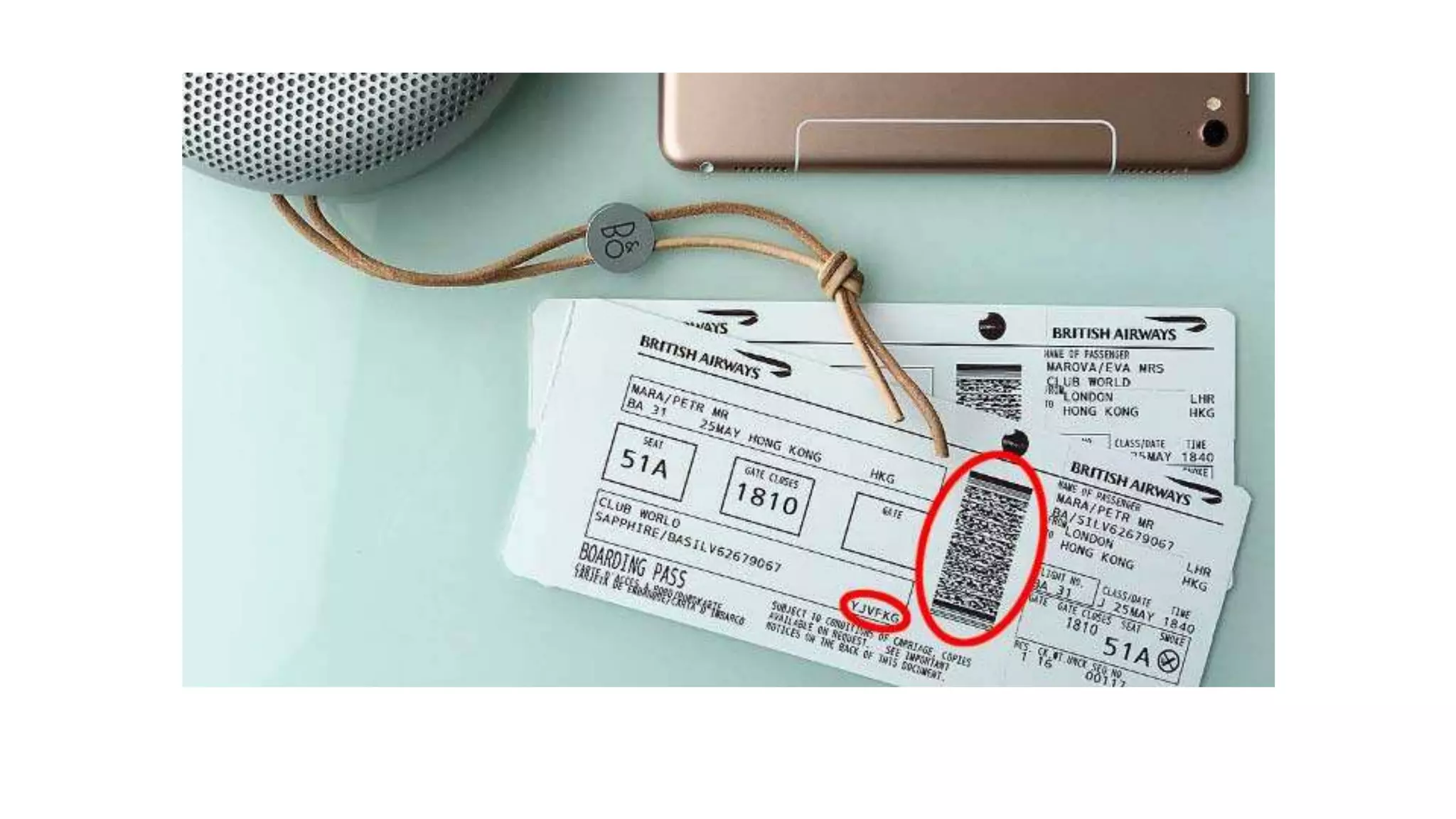
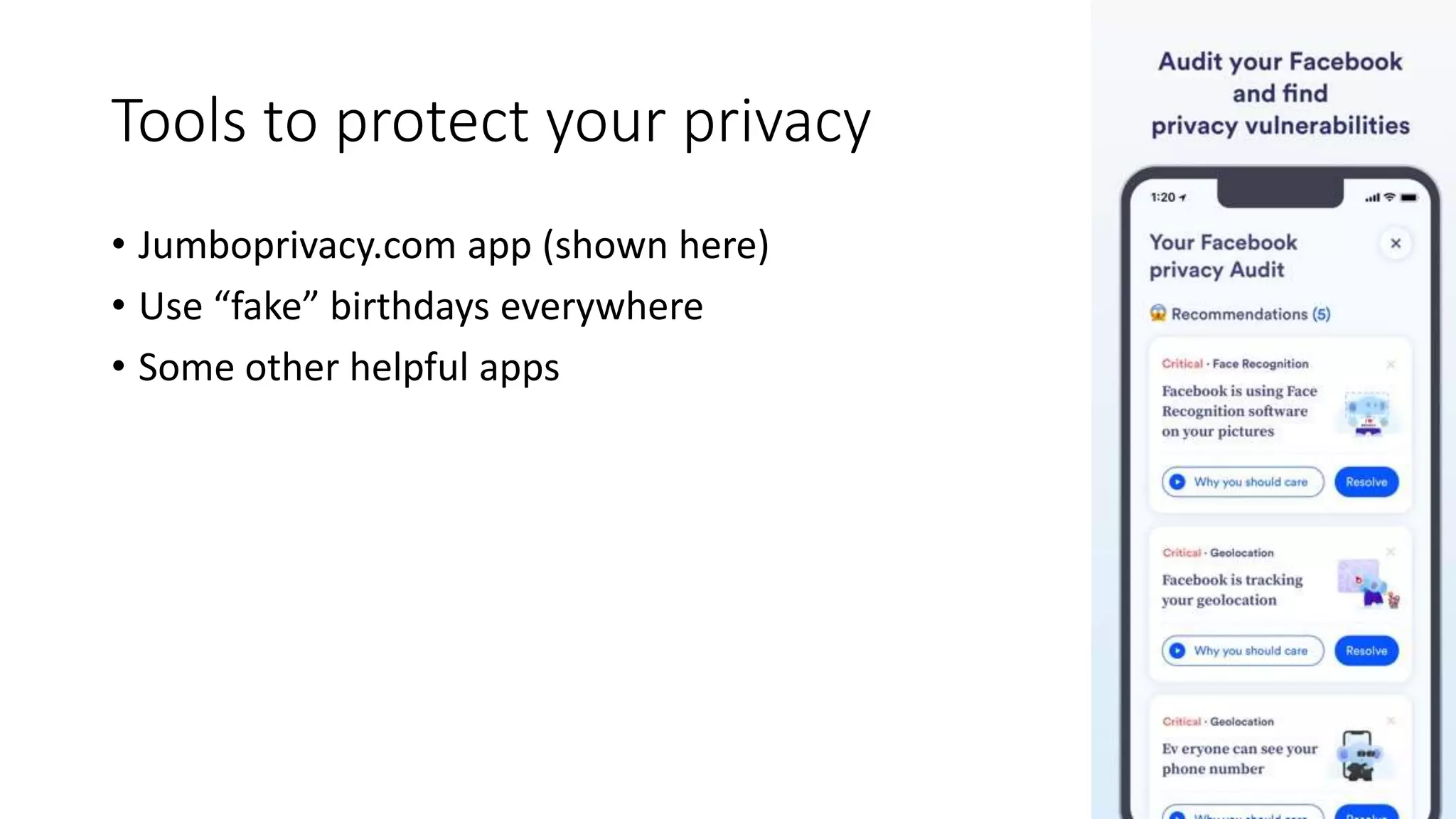
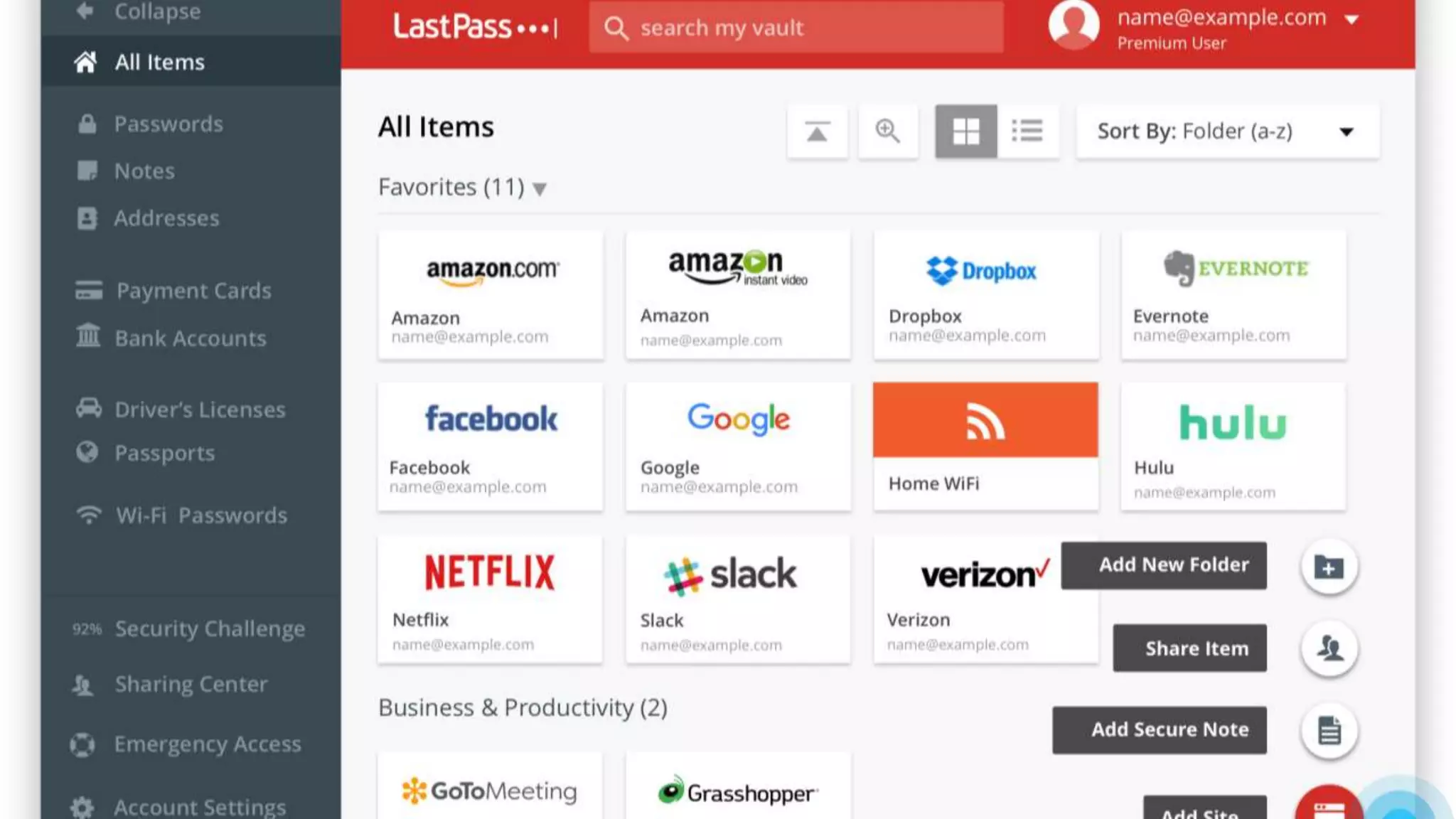
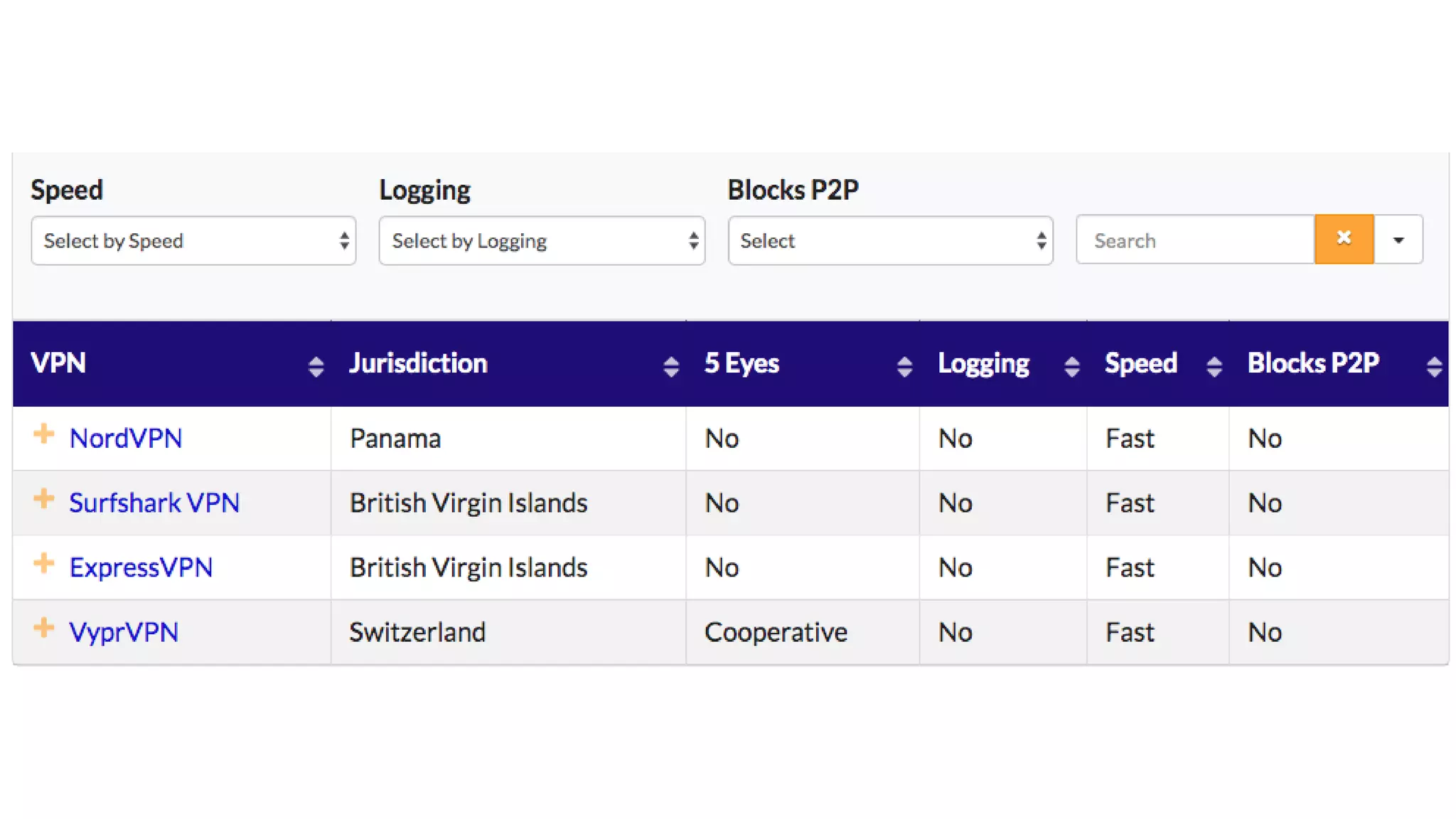
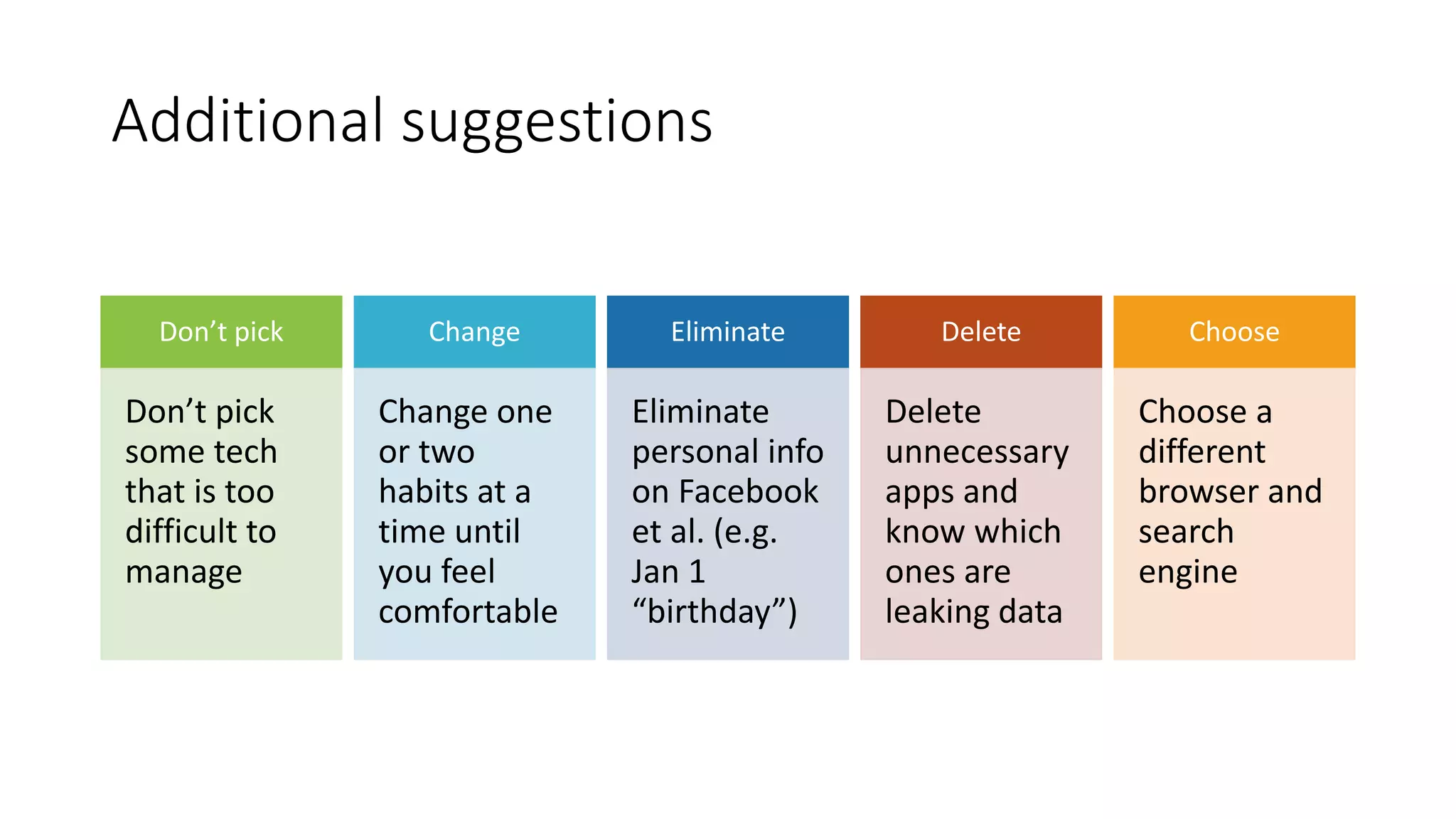
The document emphasizes the importance of protecting digital privacy and includes a security quiz to assess personal habits. It offers practical advice such as using privacy tools, managing passwords, and being cautious with personal information on social media. The author, David Strom, encourages adopting small changes in behavior for better online safety.