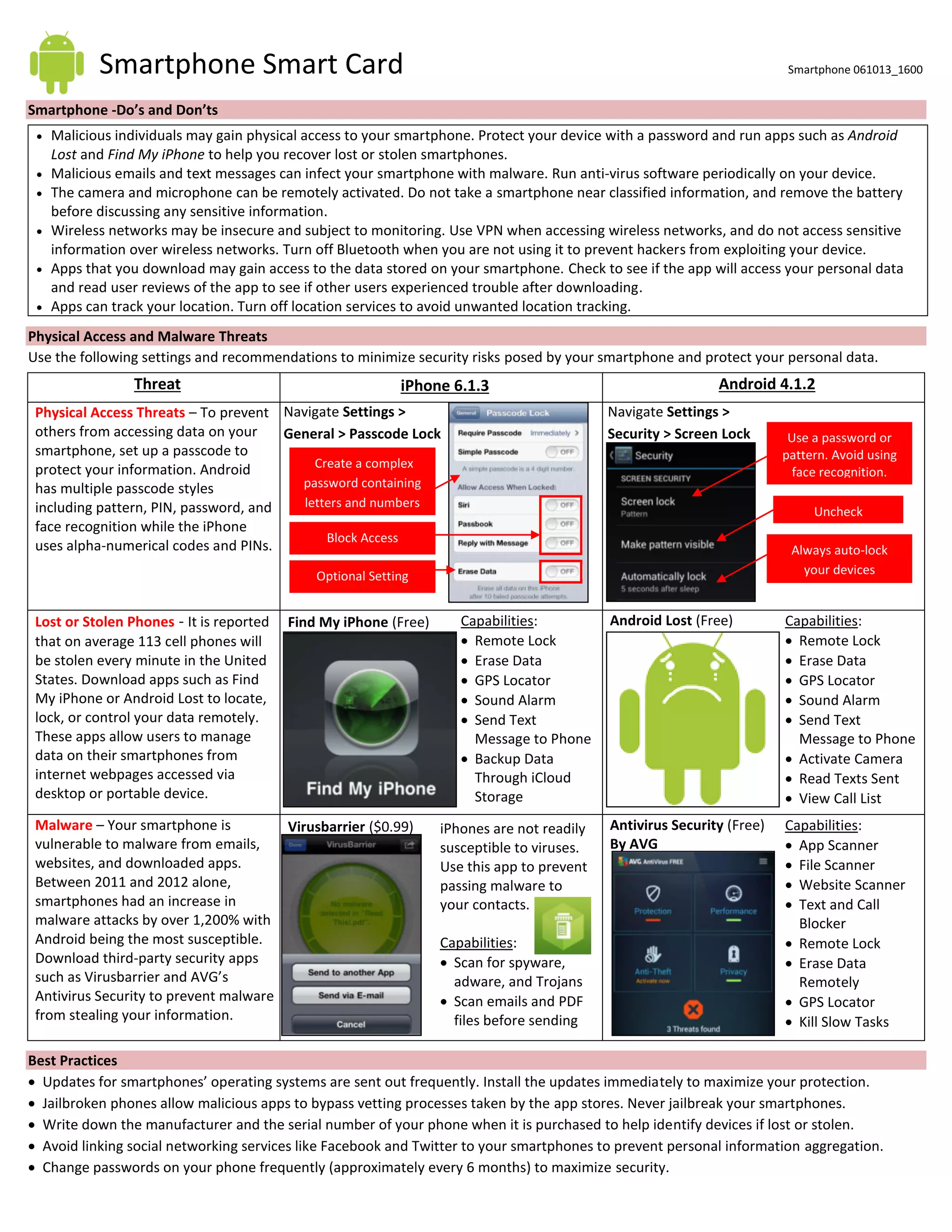
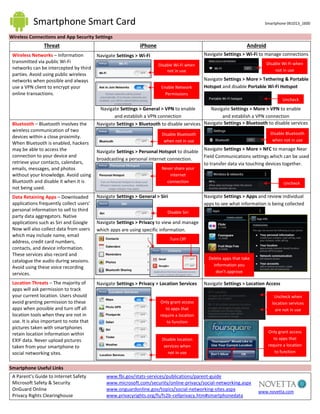
Malicious individuals and malware pose threats to smartphones. To protect your device and data: use passwords and antivirus software, enable remote tracking apps in case your phone is lost or stolen, and be cautious when using public WiFi or downloading apps. Limit what personal data apps can access and disable location services when not in use.