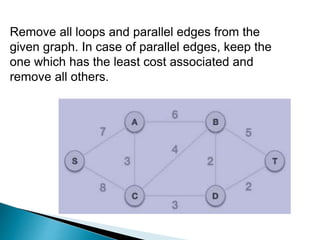
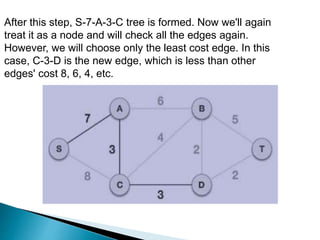
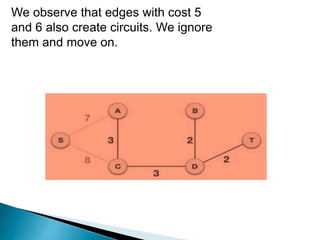
Prim's algorithm finds a minimum spanning tree of a graph using a greedy approach. It treats the nodes as a single tree and adds new nodes from the graph one by one, choosing the connection with the lowest weight at each step. This grows the tree until all nodes are included. Kruskal's algorithm also uses greedy approach but treats the graph as separate trees that merge as it adds edges from lowest to highest weight while ensuring no cycles are formed.