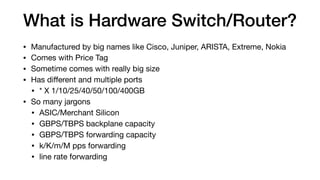
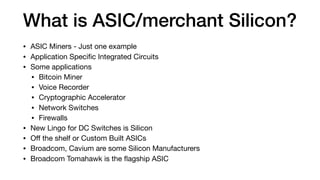
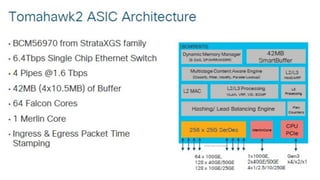
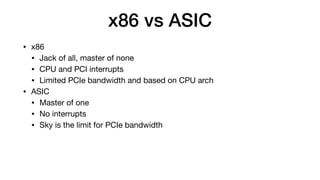
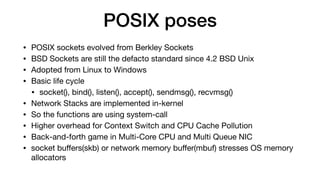
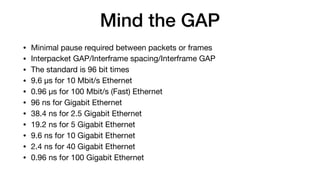
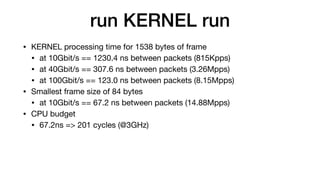
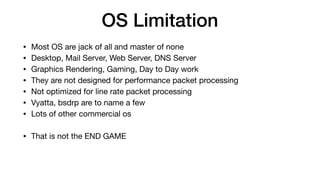
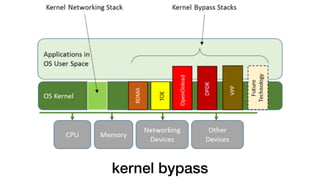
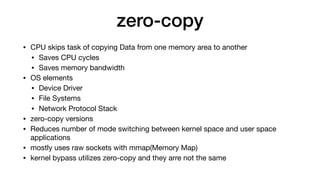
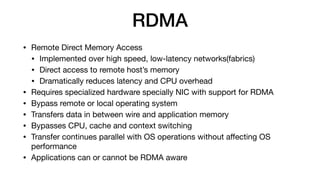
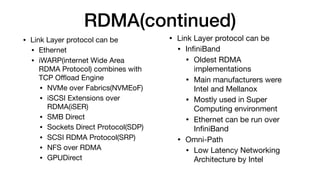
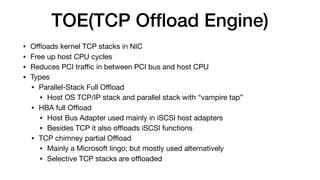
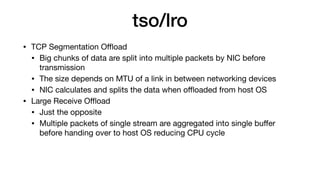
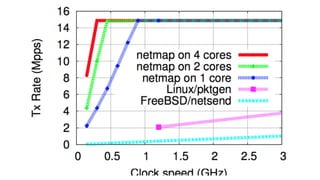
This document discusses various topics related to high-performance packet processing, including software and hardware switches/routers, ASICs, kernel bypass techniques like DPDK and netmap, and frameworks like pf_ring and FD.IO. It compares x86 CPUs to ASICs, discusses challenges of packet processing on general-purpose OSes, and explains how techniques like zero-copy, RDMA, and TCP offloading can improve performance.