The document outlines a presentation on transceiver design for single-cell and multi-cell downlink multiuser MIMO systems. It discusses MSE uplink-downlink duality under imperfect CSI, showing that the sum MSE, user MSE, and symbol MSE are dual between the uplink and downlink channels. It demonstrates how to ensure the uplink and downlink MSE values are equal to each other by appropriately setting the transmit covariance matrices. The presentation also covers transceiver design algorithms for coordinated base station systems and generalized duality for multiuser MIMO systems.
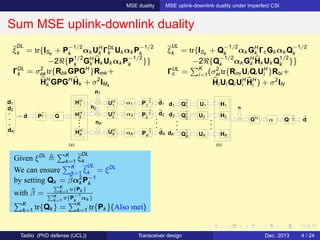
![MSE duality MSE uplink-downlink duality under imperfect CSI
User MSE uplink-downlink duality
(a)
d1
d2
dK
HH
2
HH
K αK
P
−1
2
2
P
−1
2
1
P
−1
2
K
n1
nK
n2
dK
d2
d1
= d GP
1
2
α1HH
1
α2
UH
1
UH
2
UH
K
(b)
d1
GH
d2
dK
Q
1
2
1
Q
1
2
2
Q
1
2
K
H1
H2
HK
n
dQ−1
2α
U1
U2
UK
ξ
DL
k = tr{ISk
+ P
−1/2
k αk UH
k ΓDL
k Uk αk P
−1/2
k
−2ℜ{P
1/2
k GH
k Hk Uk αk P
−1/2
k }}
ΓDL
k = σ2
ek tr{Rbk GPGH
}Rmk +
HH
k GPGH
Hk + σ2
IMk
ξ
UL
k = tr{ISk
+ Q
−1/2
k αk GH
k ΓcGk αk Q
−1/2
k
−2ℜ{Q
−1/2
k αk GH
k Hk Uk Q
1/2
k }}
ΓUL
c = K
i=1(σ2
ei tr{Rmi Ui Qi UH
i }Rbi +
Hi Ui Qi UH
i HH
i ) + σ2
IN
Given ξ
DL
k , ξ
UL
k = ξ
DL
k , K
k=1 tr{Qk } = K
k=1 tr{Pk }(ensured) by Qk = ˜βk α2
k P−1
k
where ˜T · [˜β1, . . . , ˜βK ]T
= σ2
[tr{P1}, . . . , tr{PK }]T
, ˜T is constant
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 5 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-8-320.jpg)
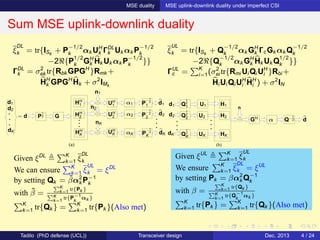
![MSE duality MSE uplink-downlink duality under imperfect CSI
User MSE uplink-downlink duality
(a)
d1
d2
dK
HH
2
HH
K αK
P
−1
2
2
P
−1
2
1
P
−1
2
K
n1
nK
n2
dK
d2
d1
= d GP
1
2
α1HH
1
α2
UH
1
UH
2
UH
K
(b)
d1
GH
d2
dK
Q
1
2
1
Q
1
2
2
Q
1
2
K
H1
H2
HK
n
dQ−1
2α
U1
U2
UK
ξ
DL
k = tr{ISk
+ P
−1/2
k αk UH
k ΓDL
k Uk αk P
−1/2
k
−2ℜ{P
1/2
k GH
k Hk Uk αk P
−1/2
k }}
ΓDL
k = σ2
ek tr{Rbk GPGH
}Rmk +
HH
k GPGH
Hk + σ2
IMk
ξ
UL
k = tr{ISk
+ Q
−1/2
k αk GH
k ΓcGk αk Q
−1/2
k
−2ℜ{Q
−1/2
k αk GH
k Hk Uk Q
1/2
k }}
ΓUL
c = K
i=1(σ2
ei tr{Rmi Ui Qi UH
i }Rbi +
Hi Ui Qi UH
i HH
i ) + σ2
IN
Given ξ
DL
k , ξ
UL
k = ξ
DL
k , K
k=1 tr{Qk } = K
k=1 tr{Pk }(ensured) by Qk = ˜βk α2
k P−1
k
where ˜T · [˜β1, . . . , ˜βK ]T
= σ2
[tr{P1}, . . . , tr{PK }]T
, ˜T is constant
Given ξ
UL
k , ξ
DL
k = ξ
UL
k , K
k=1 tr{Pk } = K
k=1 tr{Qk }(ensured) by Pk = βk α2
k Q−1
k
where T · [β1, . . . , βK ]T
= σ2
[tr{Q1}, . . . , tr{QK }]T
, T is constant
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 5 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-9-320.jpg)
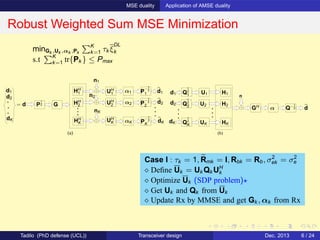
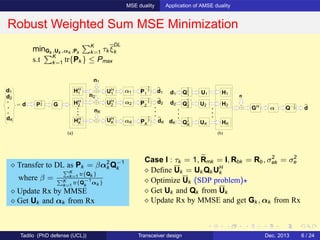
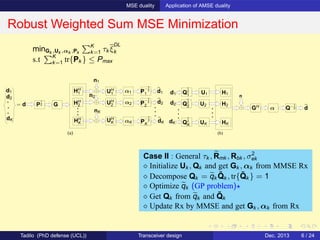
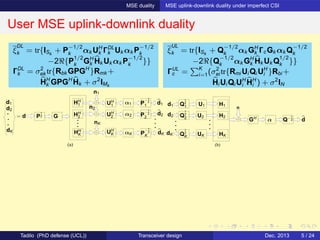
![MSE duality Application of AMSE duality
Robust Weighted Sum MSE Minimization
(a)
d1
d2
dK
HH
2
HH
K αK
P
−1
2
2
P
−1
2
1
P
−1
2
K
n1
nK
n2
dK
d2
d1
= d GP
1
2
α1HH
1
α2
UH
1
UH
2
UH
K
(b)
d1
GH
d2
dK
Q
1
2
1
Q
1
2
2
Q
1
2
K
H1
H2
HK
n
dQ−1
2α
U1
U2
UK
minGk ,Uk ,αk ,Pk
K
k=1 τk ξ
DL
k
s.t K
k=1 tr{Pk } ≤ Pmax
Case II : General τk , Rmk , Rbk , σ2
ek
⋄ Initialize Uk , Qk and get Gk , αk from MMSE Rx
⋄ Decompose Qk = qk
˜Qk , tr{ ˜Qk } = 1
⋄ Optimize qk (GP problem)⋆
⋄ Get Qk from qk and ˜Qk
⋄ Update Rx by MMSE and get Gk , αk from Rx
⋄ Transfer to DL as Pk = βk α2
k Q−1
k
where T · [β1, . . . , βK ]T
=
σ2
[tr{Q1}, . . . , tr{QK }]T
T Constant
⋄ Update Rx by MMSE
⋄ Get Uk and αk from Rx
⋄ Switch to UL and iterate
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 6 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-14-320.jpg)
![Transceiver design for Coordinated BS Systems Block diagram and Problem formulation
Coordinated BS Block Diagram
Assumptions:
The lth BS precods the overall data d = [d1, · · · , dK ] by Bl
The kth MS uses the receiver Wk to recover its data dk
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 9 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-17-320.jpg)
![Transceiver design for Coordinated BS Systems Block diagram and Problem formulation
Coordinated BS Block Diagram
Assumptions:
The lth BS precods the overall data d = [d1, · · · , dK ] by Bl
The kth MS uses the receiver Wk to recover its data dk
ˆdk = WH
k ( L
l=1 HH
lk Bl d + nk )
= WH
k (HH
k Bd + nk )
where HH
k = [HH
1k , · · · , HH
Lk ]
B = [B1; · · · ; BL]
⋄ Interpreted as a gaint MIMO
⋄ Treated like conventional MIMO BUT with
per BS power constraint Or
per BS antenna power constraint
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 9 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-18-320.jpg)
![Transceiver design for Coordinated BS Systems Block diagram and Problem formulation
System Model and Problem Statement
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
max{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ωki Rki
s.t [
K
k=1 Bk BH
k ]n,n ≤ Pn, ∀n
Rki = log2 (ξ−1
ki )
ξki = wH
ki (HH
k BBH
Hk + σ2
k I)wki
−2ℜ{wH
ki HH
k bki } + 1
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 10 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-19-320.jpg)
![Transceiver design for Coordinated BS Systems Block diagram and Problem formulation
System Model and Problem Statement
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
max{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ωki Rki
s.t [
K
k=1 Bk BH
k ]n,n ≤ Pn, ∀n
Rki = log2 (ξ−1
ki )
ξki = wH
ki (HH
k BBH
Hk + σ2
k I)wki
−2ℜ{wH
ki HH
k bki } + 1
Reexpressed as
min{bs,ws}S
w=1
S
s=1 ξωs
s
s.t [
S
s=1 bsbH
s ]n,n ≤ Pn, ∀n
ξs = wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws
−2ℜ{wH
s
˜HH
s bs} + 1
⋄ Non linear and non convex
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 10 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-20-320.jpg)
![Transceiver design for Coordinated BS Systems Block diagram and Problem formulation
System Model and Problem Statement
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
max{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ωki Rki
s.t [
K
k=1 Bk BH
k ]n,n ≤ Pn, ∀n
Rki = log2 (ξ−1
ki )
ξki = wH
ki (HH
k BBH
Hk + σ2
k I)wki
−2ℜ{wH
ki HH
k bki } + 1
Reexpressed as
min{bs,ws}S
w=1
S
s=1 ξωs
s
s.t [
S
s=1 bsbH
s ]n,n ≤ Pn, ∀n
ξs = wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws
−2ℜ{wH
s
˜HH
s bs} + 1
⋄ Non linear and non convex
Existing iterative algorithm[1]
⋄ Solve this problem as it is
⋄ Complexity per iteration :
O( (N + S)(2NS + 1)2
(2S2
+ 2NS + S))
+O(K ˜M2.376
) + CGP
[1] Shi, S., Schubert, M., and Boche, H. ”Per-antenna power constrained rate optimization
for multiuser MIMO systems”, Proc. WSA, Belrin, Germany, Feb., 2008.
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 10 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-21-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Problem Reformulation
min{bs,ws}S
s=1
S
s=1 ξωs
s , s.t [
S
s=1 bsbH
s ]n,n ≤ Pn, ∀n
ξs = wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 11 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-22-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Problem Reformulation
min{bs,ws}S
s=1
S
s=1 ξωs
s , s.t [
S
s=1 bsbH
s ]n,n ≤ Pn, ∀n
ξs = wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1
Key facts
⋄
S
s=1 fs, fs > 0 ≡
min{νs}S
s=1
1
S
S
s=1 fsνs
S
s.t
S
s=1 νs = 1, νs ≥ 0
⋄ abω
, a, b > 0, 0 < ω < 1 ≡
minτ>0 κ(aγ
τ + bτµ
)
γ = 1
1−ω , µ = 1
ω − 1, κ = ωµ(1−ω)
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 11 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-23-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Problem Reformulation
min{bs,ws}S
s=1
S
s=1 ξωs
s , s.t [
S
s=1 bsbH
s ]n,n ≤ Pn, ∀n
ξs = wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1
Key facts
⋄
S
s=1 fs, fs > 0 ≡
min{νs}S
s=1
1
S
S
s=1 fsνs
S
s.t
S
s=1 νs = 1, νs ≥ 0
⋄ abω
, a, b > 0, 0 < ω < 1 ≡
minτ>0 κ(aγ
τ + bτµ
)
γ = 1
1−ω , µ = 1
ω − 1, κ = ωµ(1−ω)
Reformulate WSR max problem as
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 11 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-24-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Centralized Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 12 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-25-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Centralized Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
⋄ For fixed B : Optimize ws, νs, τs (closed form solution)
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 12 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-26-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Centralized Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
⋄ For fixed B : Optimize ws, νs, τs (closed form solution)
⋄ For fixed ws, νs, τs : Optimize bs (SDP problem)
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 12 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-27-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Centralized Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
Repeat
⋄ For fixed B : Optimize ws, νs, τs (closed form solution)
⋄ For fixed ws, νs, τs : Optimize bs (SDP problem)
Until Convergence
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 12 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-28-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Centralized Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
Repeat
⋄ For fixed B : Optimize ws, νs, τs (closed form solution)
⋄ For fixed ws, νs, τs : Optimize bs (SDP problem)
Until Convergence
Computational complexity
Exist : O(K ˜M2.376
) + O( (N + S)(2NS + 1)2
(2S2
+ 2NS + S)) + CGP per ite
Prop : O(K ˜M2.376
) + O(
√
N + 1(2NS + 1)2
(2S2
+ 2NS)) per ite (Better!)
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 12 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-29-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Distributed Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 13 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-30-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Distributed Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
⋄ For fixed B : Same as centralized
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 13 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-31-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Distributed Algorithm
Reformulated WSR max problem
minτs,νs,bs,ws
S
s=1 κs[νγs
s
τs
+ τµs
s (wH
s (˜HH
s BBH ˜Hs + ˜σ2
s I)ws − 2ℜ{wH
s
˜HH
s bs} + 1)]
s.t [
S
s=1 bsbH
s ]n,n ≤ pn,
S
s=1 νs = 1, νs > 0, τs > 0 ∀s, n
⋄ For fixed B : Same as centralized
For fixed ws, νs, τs
⋄ Formulate bs optimization as SDP
⋄ Get dual of SDP : ({λn ≥ 0}N
n=1 are dual variables)
⋄ Apply MFM and get λi iteratively by
⋄ λ⋆
i = |¯gi |/
√
pi , g⋆
i = λ(RRH
+ λ)−1
fi
where ¯gi is ith row of [g1, g2, · · · , gN ] (i.e., needs inner iteration)
R, fi are constants
⋄ Compute optimal bs by employing {λ⋆
i }N
i=1
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 13 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-32-320.jpg)
![Transceiver design for Coordinated BS Systems Proposed Algorithms
Proposed Distributed Algorithm
⋄ For fixed B : Same as centralized
For fixed ws, νs, τs
⋄ Formulate bs optimization as SDP
⋄ Get dual of SDP : ({λn ≥ 0}N
n=1 are dual variables)
⋄ Apply MFM and get λi iteratively by
⋄ λ⋆
i = |¯gi |/
√
pi , g⋆
i = λ(RRH
+ λ)−1
fi
where ¯gi is ith row of [g1, g2, · · · , gN ] (i.e., needs inner iteration)
R, fi are constants
⋄ Compute optimal bs by employing {λ⋆
i }N
i=1
Computational complexity
Exist : O(K ˜M2.376
) + O( (N + S)(2NS + 1)2
(2S2
+ 2NS + S)) + CGP per ite
Pro (cent) : O(K ˜M2.376
) + O(
√
N + 1(2NS + 1)2
(2S2
+ 2NS)) per ite
Pro (dist) : O(K ˜M2.376
) + inner ite × O(N2.376
) per ite (Much better!)
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 13 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-33-320.jpg)
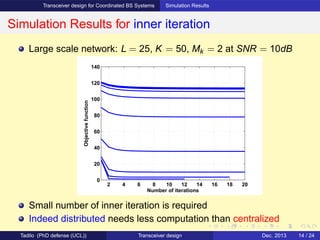
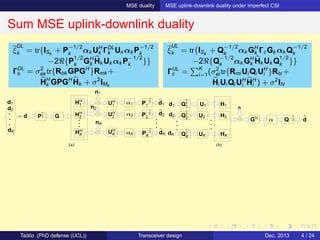
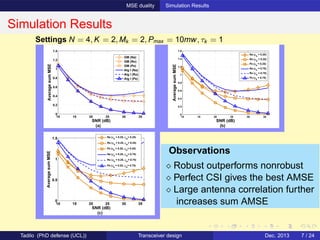
![Transceiver design for Coordinated BS Systems Simulation Results
Comparison of Proposed and Existing Algorithms
Set N = 4, L = 2, K = 4, Mk = 2, ω = [.6, .4, .5, .8, .25, .8, .46, .28]
5 10 15 20 25
4
5
6
7
8
9
10
11
12
Number of iterations
Weightedsumrate(bps/Hz)
SNR=10dB
Proposed centralized algorithm
Proposed distributed algorithm
Existing algorithm [1]
0 5 10 15 20
4
6
8
10
12
14
16
18
20
22
SNR (dB)
Weightedsumrate(bps/Hz)
Proposed centralized algorithm
Proposed distributed algorithm
Existing algorithm [1]
Proposed algorithms have faster convergence than existing
Proposed algorithms have slightly higher WSR than existing
Distributed algorithm achieves the same WSR as centralized
[1] Shi, S., Schubert, M., and Boche, H. ”Per-antenna power constrained rate optimization
for multiuser MIMO systems”, Proc. WSA, Belrin, Germany, Feb., 2008.
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 15 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-35-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
System Model and Problem Statements
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
Objectives
To solve P1 and P2 by MSE duality approach
To show the benefits of the MSE duality solution approach
To show the extension of the duality for solving other transceiver
design problems
P1 : minBk ,Wk
K
k=1
Sk
i=1 ηki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki , ∀n, k, i
P2 : min{Bk ,Wk }K
k=1
max ρki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki , ∀n, k, i
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 17 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-37-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
Existing MSE Uplink-downlink Duality (Revisited)
(a)
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
(b)
H1
H2
HK
n
TH
V1
V2
VK
d
d1
d2
dK
The duality can maintain ξDL
ki = ξUL
ki
The duality cannot ensure [ K
k=1 Bk BH
k ]n,n ≤ ˘pn and bH
kibki ≤ ˘pki
P1 : min{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ηki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
P2 : min{Bk ,Wk }K
k=1
max ρki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 18 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-38-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
New MSE Downlink-Interference Duality
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
V1
V2
nI
1S1
nI
K1
nI
KSK
nI
11
tH
KSK
tH
K1
tH
1S1
tH
11
H111
H11S1
H21S1
H1KSK
H1K1
HKK1
HK1S1
H2K1
HKKSK
ˆdK1
ˆd11
VK
HK11
H2KSK
H211
d1
ˆdKSK
ˆd1S1
d2
dK
P1 : min{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ηki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 19 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-39-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
New MSE Downlink-Interference Duality
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
V1
V2
nI
1S1
nI
K1
nI
KSK
nI
11
tH
KSK
tH
K1
tH
1S1
tH
11
H111
H11S1
H21S1
H1KSK
H1K1
HKK1
HK1S1
H2K1
HKKSK
ˆdK1
ˆd11
VK
HK11
H2KSK
H211
d1
ˆdKSK
ˆd1S1
d2
dK
P1 : min{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ηki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
⋄ Initialize Bk and update Wk by MMSE
Repeat
Transformation (DL to Interference)
⋄ Set dI
ki ∼ (0, ηki ), nI
ki ∼ (0, Ψ + µki I), Ψ = diag(ψn)
⋄ Get ψn, µki iteratively
Key we show that ψn, µki > 0 always exist!
⋄ Set vki = wki and update tki by MMSE
Transformation (Interference to DL)
⋄ Set bki = βtki , β2
=
K
i=1
Si
j=1
ηij wH
ij
Ri wij
K
i=1
Si
j=1
tH
ij
(Ψ+µij I)tij
⋄ Update Wk by MMSE
Until convergence
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 19 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-40-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
New MSE Downlink-Interference Duality
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
V1
V2
nI
1S1
nI
K1
nI
KSK
nI
11
tH
KSK
tH
K1
tH
1S1
tH
11
H111
H11S1
H21S1
H1KSK
H1K1
HKK1
HK1S1
H2K1
HKKSK
ˆdK1
ˆd11
VK
HK11
H2KSK
H211
d1
ˆdKSK
ˆd1S1
d2
dK
P1 : min{Bk ,Wk }K
k=1
K
k=1
Sk
i=1 ηki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
⋄ Initialize Bk and update Wk by MMSE
Repeat
Transformation (DL to Interference)
⋄ Set dI
ki ∼ (0, ηki ), nI
ki ∼ (0, Ψ + µki I), Ψ = diag(ψn)
⋄ Get ψn, µki iteratively
Key we show that ψn, µki > 0 always exist!
⋄ Set vki = wki and update tki by MMSE
Transformation (Interference to DL)
⋄ Set bki = βtki , wki =
vki
β
, β2
=
K
i=1
Si
j=1
ηij wH
ij
Ri wij
K
i=1
Si
j=1
tH
ij
(Ψ+µij I)tij
⋄ Decompose Bk = Gk P
1/2
k
, Wk = Gk P
−1/2
k
αk
⋄ Optimize Pk (increases convergence speed)
⋄ Again update Bk = Gk P
1/2
k
and Wk by MMSE
Until convergence
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 19 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-41-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
New MSE Downlink-Interference Duality
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
V1
V2
nI
1S1
nI
K1
nI
KSK
nI
11
tH
KSK
tH
K1
tH
1S1
tH
11
H111
H11S1
H21S1
H1KSK
H1K1
HKK1
HK1S1
H2K1
HKKSK
ˆdK1
ˆd11
VK
HK11
H2KSK
H211
d1
ˆdKSK
ˆd1S1
d2
dK
P2 : min{Bk ,Wk }K
k=1
max ρki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 19 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-42-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
New MSE Downlink-Interference Duality
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
V1
V2
nI
1S1
nI
K1
nI
KSK
nI
11
tH
KSK
tH
K1
tH
1S1
tH
11
H111
H11S1
H21S1
H1KSK
H1K1
HKK1
HK1S1
H2K1
HKKSK
ˆdK1
ˆd11
VK
HK11
H2KSK
H211
d1
ˆdKSK
ˆd1S1
d2
dK
P2 : min{Bk ,Wk }K
k=1
max ρki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
⋄ Initialize Bk and update Wk by MMSE
Repeat
Transformation (DL to Interference)
⋄ Set dI
ki ∼ (0, 1), nI
ki ∼ (0, Ψ + µki I), Ψ = diag(ψn)
⋄ Get ψn, µki iteratively
⋄ Get ¯β2
[ ¯β2
11, · · · ¯β2
KSK
] as ¯β2
= ¯Zx
x = [ψ1, · · · , ψN , µ11, · · · , µKSK
], ¯Z is constant
⋄ Set vki = ¯βki wki and update tki by MMSE
Transformation (Interference to DL)
⋄ Get β2
[β2
11, · · · β2
KSK
] as β2
= Zx, Z is constant
Key we show that ψn, µki , ¯β2
ki , β2
ki > 0 always exist!
⋄ Set bki = βki tki and update Wk by MMSE
Until convergence
Unbalanced weighted MSE
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 19 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-43-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality System Model and Problem Statements
New MSE Downlink-Interference Duality
d2
d1 HH
1
HH
2
HH
K
WH
2
n1
nK
n2
WH
K
WH
1
d1
d2
dK
= d B
dK
V1
V2
nI
1S1
nI
K1
nI
KSK
nI
11
tH
KSK
tH
K1
tH
1S1
tH
11
H111
H11S1
H21S1
H1KSK
H1K1
HKK1
HK1S1
H2K1
HKKSK
ˆdK1
ˆd11
VK
HK11
H2KSK
H211
d1
ˆdKSK
ˆd1S1
d2
dK
P2 : min{Bk ,Wk }K
k=1
max ρki ξDL
ki
s.t [
K
k=1 Bk BH
k ]n,n ≤ ˘pn,
bH
ki bki ≤ ˘pki
⋄ Initialize Bk and update Wk by MMSE
Repeat
Transformation (DL to Interference)
⋄ Set dI
ki ∼ (0, 1), nI
ki ∼ (0, Ψ + µki I), Ψ = diag(ψn)
⋄ Get ψn, µki iteratively
⋄ Get ¯β2
[ ¯β2
11, · · · ¯β2
KSK
] as ¯β2
= ¯Zx
x = [ψ1, · · · , ψN , µ11, · · · , µKSK
], ¯Z is constant
⋄ Set vki = ¯βki wki and update tki by MMSE
Transformation (Interference to DL)
⋄ Get β2
[β2
11, · · · β2
KSK
] as β2
= Zx, Z is constant
Key we show that ψn, µki , ¯β2
ki , β2
ki > 0 always exist!
⋄ Set bki = βki tki , wki = vki /βki and decompose
Bk = Gk P
1/2
k
, Wk = Gk P
−1/2
k
αk
⋄ Optimize Pk , −Ensures balanced weighted MSE
−Increases convergence speed
⋄ Again update Bk = Gk P
1/2
k
and Wk by MMSE
Until convergence
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 19 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-44-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality Simulation Results
Simulation Results
10 15 20 25 30 35
0
0.1
0.2
0.3
0.4
0.5
0.6
0.7
0.8
0.9
1
SNR (dB)
WeightedsumMSE
Proposed Duality
Algorithm in [1]
−25 −20 −15 −10 −5 0
7.5
8
8.5
9
9.5
10
σav
2
(dB)
TotalBSpower
Proposed Duality
Algorithm in [1]
10 15 20 25 30 35
0
0.05
0.1
0.15
0.2
0.25
SNR (dB)
MaximumsymbolMSE
Proposed Duality
Algorithm in [1]
−25 −20 −15 −10 −5 0
7
7.5
8
8.5
9
9.5
10
σ
av
2
(dB)
TotalBSpower
Proposed Duality
Algorithm in [1]
Settings N = 4, K = 2, Mk = 2, ˘pki = 2.5mw, ˘pn = 2.5mw, ηki = ρki = 1
[1] Shi, S., Schubert, M., Vucic, N., and Boche, H. ”MMSE Optimization with Per-Base-Station Power
Constraints for Network MIMO Systems”, Proc. IEEE ICC, Beijing, China, May, 2008.
P1
P2
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 20 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-45-320.jpg)
![Transceiver design for multiuser MIMO systems: Generalized duality Simulation Results
Simulation Results
10 15 20 25 30 35
0
0.1
0.2
0.3
0.4
0.5
0.6
0.7
0.8
0.9
1
SNR (dB)
WeightedsumMSE
Proposed Duality
Algorithm in [1]
−25 −20 −15 −10 −5 0
7.5
8
8.5
9
9.5
10
σav
2
(dB)
TotalBSpower
Proposed Duality
Algorithm in [1]
10 15 20 25 30 35
0
0.05
0.1
0.15
0.2
0.25
SNR (dB)
MaximumsymbolMSE
Proposed Duality
Algorithm in [1]
−25 −20 −15 −10 −5 0
7
7.5
8
8.5
9
9.5
10
σ
av
2
(dB)
TotalBSpower
Proposed Duality
Algorithm in [1]
Settings N = 4, K = 2, Mk = 2, ˘pki = 2.5mw, ˘pn = 2.5mw, ηki = ρki = 1
[1] Shi, S., Schubert, M., Vucic, N., and Boche, H. ”MMSE Optimization with Per-Base-Station Power
Constraints for Network MIMO Systems”, Proc. IEEE ICC, Beijing, China, May, 2008.
P1
P2
Complexity (P1)
Proposed duality O(N2.376
) + O(KM2.376
) + CGP (≡ Linear programming)
Algorithm in [1] O( (N + KM + 1)(2MKN + 1)2
(2(MK)2
+ 4NMK)) + O(KM2.376
)
Complexity (P2)
Proposed duality O(N2.376
) + O(KM2.376
) + CGP (≡ Linear programming)
Algorithm in [1] O( (N + KM + 1)(2MKN + 1)2
(2(MK)2
+ 4NMK)) + O(KM2.376
)
Tadilo (PhD defense (UCL)) Transceiver design Dec. 2013 20 / 24](https://image.slidesharecdn.com/phdprivatedefense-140607143127-phpapp01/85/Transceiver-design-for-single-cell-and-multi-cell-downlink-multiuser-MIMO-systems-46-320.jpg)