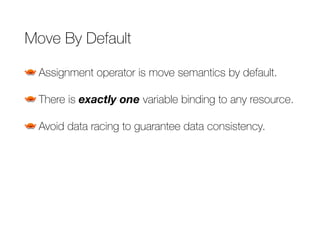
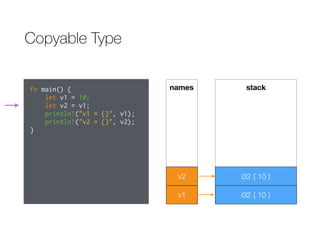
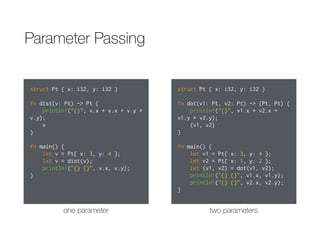
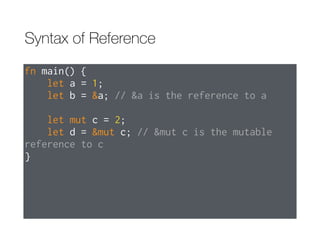
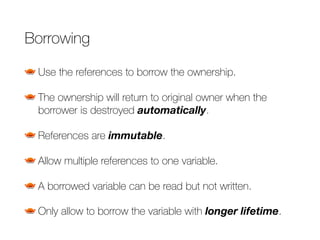
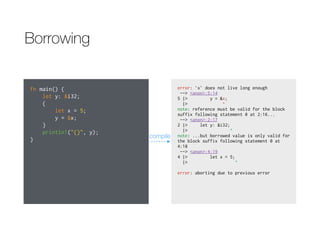
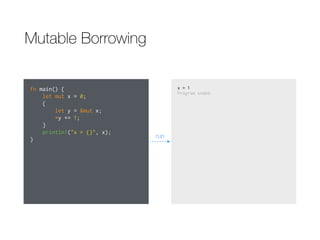
The document discusses Rust's ownership system and borrowing. It explains that variables own the memory for their values, and when a variable goes out of scope that memory is returned. References allow borrowing values without transferring ownership. References must live shorter than the values they reference. Mutable references also allow changing borrowed values, but there can only be one mutable reference at a time.
![郭⾄至軒 [:kuoe0]
Mozilla
kuoe0.tw@gmail.com
Ownership
System in Rust
2016/07/12 @摩茲⼯工寮](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-1-320.jpg)
![4.8 Ownership[link]](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-2-320.jpg)

![Variable & Memory
Stack
Heap
fn main() {
let v = vec![1, 2, 3];
}
dynamic memory
static memory](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-4-320.jpg)
![Variable & Memory
Stack
Heap
fn main() {
let v = vec![1, 2, 3];
}
dynamic memory
static memory
When the variable is destroyed…](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-5-320.jpg)
![fn main() {
let v = vec![1, 2, 3];
}
Variable & Memory
Stack
Heap
dynamic memory
static memory
All related resources will be destroyed, too!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-6-320.jpg)
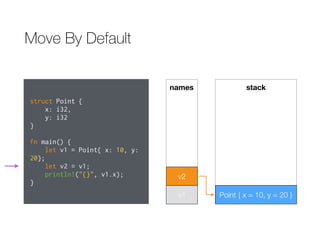
![Move By Default
struct Point {
x: i32,
y: i32
}
fn main() {
let v1 = Point{ x: 10, y:
20};
let v2 = v1;
println!("{}", v1.x);
}
error: use of moved value: `v1.x` [--explain
E0382]
--> <anon>:9:20
8 |> let v2 = v1;
|> -- value moved here
9 |> println!("{}", v1.x);
|> ^^^^ value used here
after move
<std macros>:2:27: 2:58: note: in this
expansion of format_args!
<std macros>:3:1: 3:54: note: in this
expansion of print! (defined in <std macros>)
<anon>:9:5: 9:26: note: in this expansion of
println! (defined in <std macros>)
note: move occurs because `v1` has type
`Point`, which does not implement the `Copy`
trait
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-8-320.jpg)
![Move By Default
struct Point {
x: i32,
y: i32
}
fn main() {
let v1 = Point{ x: 10, y:
20};
let v2 = v1;
println!("{}", v1.x);
}
error: use of moved value: `v1.x` [--explain
E0382]
--> <anon>:9:20
8 |> let v2 = v1;
|> -- value moved here
9 |> println!("{}", v1.x);
|> ^^^^ value used here
after move
<std macros>:2:27: 2:58: note: in this
expansion of format_args!
<std macros>:3:1: 3:54: note: in this
expansion of print! (defined in <std macros>)
<anon>:9:5: 9:26: note: in this expansion of
println! (defined in <std macros>)
note: move occurs because `v1` has type
`Point`, which does not implement the `Copy`
trait
error: aborting due to previous error
compile
Use of moved value!
v1.x](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-9-320.jpg)


![Parameter Passing
struct Pt { x: i32 }
fn square(v: Pt) {
println!("{}", v.x * v.x);
}
fn main() {
let v = Pt{ x: 3 };
square(v);
println!("{}", v.x);
}
error: use of moved value: `v.x` [--explain
E0382]
--> <anon>:10:20
9 |> square(v);
|> - value moved here
10 |> println!("{}", v.x);
|> ^^^ value used here
after move
<std macros>:2:27: 2:58: note: in this
expansion of format_args!
<std macros>:3:1: 3:54: note: in this
expansion of print! (defined in <std macros>)
<anon>:10:5: 10:25: note: in this expansion
of println! (defined in <std macros>)
note: move occurs because `v` has type `Pt`,
which does not implement the `Copy` trait
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-18-320.jpg)
![Parameter Passing
struct Pt { x: i32 }
fn square(v: Pt) {
println!("{}", v.x * v.x);
}
fn main() {
let v = Pt{ x: 3 };
square(v);
println!("{}", v.x);
}
error: use of moved value: `v.x` [--explain
E0382]
--> <anon>:10:20
9 |> square(v);
|> - value moved here
10 |> println!("{}", v.x);
|> ^^^ value used here
after move
<std macros>:2:27: 2:58: note: in this
expansion of format_args!
<std macros>:3:1: 3:54: note: in this
expansion of print! (defined in <std macros>)
<anon>:10:5: 10:25: note: in this expansion
of println! (defined in <std macros>)
note: move occurs because `v` has type `Pt`,
which does not implement the `Copy` trait
error: aborting due to previous error
compile
v.x
Use of moved value!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-19-320.jpg)
![4.9 Reference and Borrowing[link]](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-20-320.jpg)

![Borrowing
fn main() {
let mut x = 0;
{
let y = &x;
x += 1;
println!("{}", y);
}
println!("{}", x);
}
error: cannot assign to `x` because it is
borrowed [--explain E0506]
--> <anon>:5:9
4 |> let y = &x;
|> - borrow of `x` occurs
here
5 |> x += 1;
|> ^^^^^^ assignment to borrowed
`x` occurs here
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-24-320.jpg)
![Borrowing
fn main() {
let mut x = 0;
{
let y = &x;
x += 1;
println!("{}", y);
}
println!("{}", x);
}
error: cannot assign to `x` because it is
borrowed [--explain E0506]
--> <anon>:5:9
4 |> let y = &x;
|> - borrow of `x` occurs
here
5 |> x += 1;
|> ^^^^^^ assignment to borrowed
`x` occurs here
error: aborting due to previous error
compile
x += 1;
Cannot write the borrowed variable!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-25-320.jpg)






![Mutable Borrowing
fn main() {
let mut x = 0;
{
let y = &mut x;
let z = &mut x;
*y += 1;
}
println!("x = {}", x);
}
error: cannot borrow `x` as mutable more than
once at a time [--explain E0499]
--> <anon>:5:22
4 |> let y = &mut x;
|> - first mutable
borrow occurs here
5 |> let z = &mut x;
|> ^ second mutable
borrow occurs here
6 |> *y += 1;
7 |> }
|> - first borrow ends here
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-34-320.jpg)
![Mutable Borrowing
fn main() {
let mut x = 0;
{
let y = &mut x;
let z = &mut x;
*y += 1;
}
println!("x = {}", x);
}
error: cannot borrow `x` as mutable more than
once at a time [--explain E0499]
--> <anon>:5:22
4 |> let y = &mut x;
|> - first mutable
borrow occurs here
5 |> let z = &mut x;
|> ^ second mutable
borrow occurs here
6 |> *y += 1;
7 |> }
|> - first borrow ends here
error: aborting due to previous error
compile
let z = &mut x;
Cannot borrow x as mutable reference more than once!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-35-320.jpg)
![Mutable Borrowing
fn main() {
let mut x = 0;
{
let y = &mut x;
let z = &x;
*y += 1;
}
println!("x = {}", x);
}
error: cannot borrow `x` as immutable because
it is also borrowed as mutable [--explain
E0502]
--> <anon>:6:18
4 |> let y = &mut x;
|> - mutable borrow
occurs here
5 |> *y += 1;
6 |> let z = &x;
|> ^ immutable borrow
occurs here
7 |> }
|> - mutable borrow ends here
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-36-320.jpg)
![Mutable Borrowing
fn main() {
let mut x = 0;
{
let y = &mut x;
let z = &x;
*y += 1;
}
println!("x = {}", x);
}
error: cannot borrow `x` as immutable because
it is also borrowed as mutable [--explain
E0502]
--> <anon>:6:18
4 |> let y = &mut x;
|> - mutable borrow
occurs here
5 |> *y += 1;
6 |> let z = &x;
|> ^ immutable borrow
occurs here
7 |> }
|> - mutable borrow ends here
error: aborting due to previous error
compile
let z = &x;
Cannot borrow the variable been borrowed as a mutable reference!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-37-320.jpg)
![Mutable Borrowing
fn main() {
let mut x = 0;
{
let y = &mut x;
let z = x + 1;
}
println!("x = {}", x);
}
error: cannot use `x` because it was mutably
borrowed [E0503]
--> <anon>:5:17
5 |> let z = x + 1;
|> ^
note: borrow of `x` occurs here
--> <anon>:4:22
4 |> let y = &mut x;
|> ^
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-38-320.jpg)
![Mutable Borrowing
fn main() {
let mut x = 0;
{
let y = &mut x;
let z = x + 1;
}
println!("x = {}", x);
}
error: cannot use `x` because it was mutably
borrowed [E0503]
--> <anon>:5:17
5 |> let z = x + 1;
|> ^
note: borrow of `x` occurs here
--> <anon>:4:22
4 |> let y = &mut x;
|> ^
error: aborting due to previous error
compile
let z = x + 1;
Cannot access the variable been borrowed as a mutable reference.](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-39-320.jpg)

![Thinking in Scopes(cont’)
fn main() {
let mut x = 0;
let y = &mut x;
*y += 1;
println!("x = {}", x);
}
error: cannot borrow `x` as immutable because
it is also borrowed as mutable [--explain
E0502]
--> <anon>:5:24
3 |> let y = &mut x;
|> - mutable borrow occurs
here
4 |> *y += 1;
5 |> println!("x = {}", x);
|> ^ immutable
borrow occurs here
6 |> }
|> - mutable borrow ends here
<std macros>:2:27: 2:58: note: in this
expansion of format_args!
<std macros>:3:1: 3:54: note: in this
expansion of print! (defined in <std macros>)
<anon>:5:5: 5:27: note: in this expansion of
println! (defined in <std macros>)
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-41-320.jpg)
![Thinking in Scopes(cont’)
fn main() {
let mut x = 0;
let y = &mut x;
*y += 1;
println!("x = {}", x);
}
error: cannot borrow `x` as immutable because
it is also borrowed as mutable [--explain
E0502]
--> <anon>:5:24
3 |> let y = &mut x;
|> - mutable borrow occurs
here
4 |> *y += 1;
5 |> println!("x = {}", x);
|> ^ immutable
borrow occurs here
6 |> }
|> - mutable borrow ends here
<std macros>:2:27: 2:58: note: in this
expansion of format_args!
<std macros>:3:1: 3:54: note: in this
expansion of print! (defined in <std macros>)
<anon>:5:5: 5:27: note: in this expansion of
println! (defined in <std macros>)
error: aborting due to previous error
compile
println!("x = {}", x);
Immutable borrow occurs here!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-42-320.jpg)
![Iterator Invalidation
fn main() {
let mut v = vec![1, 2, 3];
for i in &v {
println!("{}", i);
v.push(34);
}
}
error: cannot borrow `v` as mutable because
it is also borrowed as immutable [--explain
E0502]
--> <anon>:6:9
4 |> for i in &v {
|> - immutable borrow occurs
here
5 |> println!("{}", i);
6 |> v.push(34);
|> ^ mutable borrow occurs here
7 |> }
|> - immutable borrow ends here
error: aborting due to previous error
compile](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-43-320.jpg)
![Iterator Invalidation
fn main() {
let mut v = vec![1, 2, 3];
for i in &v {
println!("{}", i);
v.push(34);
}
}
error: cannot borrow `v` as mutable because
it is also borrowed as immutable [--explain
E0502]
--> <anon>:6:9
4 |> for i in &v {
|> - immutable borrow occurs
here
5 |> println!("{}", i);
6 |> v.push(34);
|> ^ mutable borrow occurs here
7 |> }
|> - immutable borrow ends here
error: aborting due to previous error
compile
v.push(34);
push(&mut self, …) try to borrow v as a mutable reference!](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-44-320.jpg)
![4.10 Lifetimes[link]](https://image.slidesharecdn.com/ownershipsysteminrust-160712142150/85/Ownership-System-in-Rust-45-320.jpg)