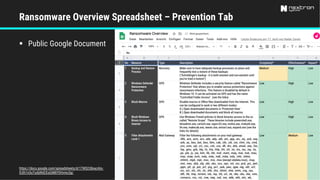
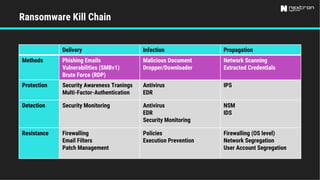
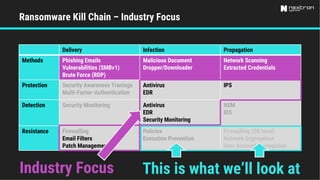
This document discusses low-effort ransomware resistance measures that can have high impact. It recommends blocking executable downloads from uncategorized domains, enforcing web proxies, and blocking workstation-to-workstation communication. These three measures are estimated to avert around 90%, 60%, and greatly reduce the impact of attacks, respectively. The document also notes challenges such as many remote workers and lack of asset management.