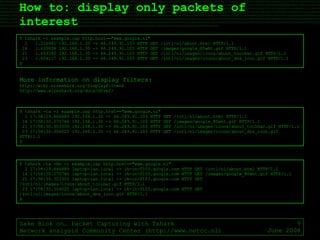
The document is an introduction to using Tshark, the command-line interface version of Wireshark, focusing on basic and advanced packet capturing techniques. It covers how to capture and filter packets, save them to files, and read them back, as well as how to display specific packets of interest and show full packet details. It provides example commands and captures to demonstrate these functionalities.
![How to: capture packets Sake Blok on… Packet Capturing with Tshark Network analysis Community Center (http://www.netcc.nl) June 2008 $ tshark Capturing on Adapter for generic dialup and VPN capture 0 packets captured $ $ tshark -D 1. \Device\NPF_GenericDialupAdapter (Adapter for generic dialup and VPN capture) 2. \Device\NPF_{F8E714B2-428F-4B47-900D-89F7F8FD36CD} (Bluetooth BNEP from TOSHIBA (Microsoft's Packet Scheduler) ) 3. \Device\NPF_{E98FD95C-9205-4947-9BF5-03384D116392} (VMware Virtual Ethernet Adapter) 4. \Device\NPF_{424EA318-CC86-475C-802A-5D52D0C21531} (Broadcom NetXtreme Gigabit Ethernet Driver (Microsoft's Packet Scheduler) ) 5. \Device\NPF_{B730145F-C8D2-4FBA-B729-8092004A80CA} (VMware Virtual Ethernet Adapter) $ $ tshark -i 4 Capturing on Broadcom NetXtreme Gigabit Ethernet Driver (Microsoft's Packet Scheduler) 0.000000 192.168.1.30 -> 192.168.1.10 DNS Standard query A news.google.nl 0.386202 192.168.1.10 -> 192.168.1.30 DNS Standard query response CNAME news.google.com CNAME news.l.google.com A 64.233.183.104 A 64.233.183.99 A 64.233.183.147 0.395150 192.168.1.30 -> 64.233.183.104 TCP 7615 > http [SYN] Seq=0 Win=65535 Len=0 MSS=1460 WS=1 0.407587 64.233.183.104 -> 192.168.1.30 TCP http > 7615 [SYN, ACK] Seq=0 Ack=1 Win=5720 Len=0 MSS=1430 WS=6 0.407667 192.168.1.30 -> 64.233.183.104 TCP 7615 > http [ACK] Seq=1 Ack=1 Win=128000 Len=0 5 packets captured $](https://image.slidesharecdn.com/sakeblokpacketcapturingwithtshark-1212540256140414-9/85/OSTU-Sake-Blok-on-Packet-Capturing-with-Tshark-6-320.jpg)
![How to: filter packets while capturing Sake Blok on… Packet Capturing with Tshark Network analysis Community Center (http://www.netcc.nl) June 2008 $ tshark -i 4 -f "tcp port 80" Capturing on Broadcom NetXtreme Gigabit Ethernet Driver (Microsoft's Packet Scheduler) 0.000000 192.168.1.30 -> 66.249.91.99 TCP 7733 > http [SYN] Seq=0 Win=65535 Len=0 MSS=1460 WS=1 0.014764 66.249.91.99 -> 192.168.1.30 TCP http > 7733 [SYN, ACK] Seq=0 Ack=1 Win=5720 Len=0 MSS=1430 WS=6 0.014805 192.168.1.30 -> 66.249.91.99 TCP 7733 > http [ACK] Seq=1 Ack=1 Win=128000 Len=0 0.014913 192.168.1.30 -> 66.249.91.99 HTTP GET / HTTP/1.1 0.039218 66.249.91.99 -> 192.168.1.30 TCP http > 7733 [ACK] Seq=1 Ack=626 Win=6976 Len=0 0.050645 66.249.91.99 -> 192.168.1.30 TCP [TCP segment of a reassembled PDU] 0.055158 66.249.91.99 -> 192.168.1.30 TCP [TCP segment of a reassembled PDU] 0.055224 192.168.1.30 -> 66.249.91.99 TCP 7733 > http [ACK] Seq=626 Ack=2861 Win=128000 Len=0 0.055409 66.249.91.99 -> 192.168.1.30 HTTP HTTP/1.1 200 OK (text/html) 0.214538 192.168.1.30 -> 66.249.91.99 TCP 7733 > http [ACK] Seq=626 Ack=3017 Win=127844 Len=0 10 packets captured $ Commonly used capture filters: host 1.1.1.1 capture only traffic to and from 1.1.1.1 host 1.1.1.1 and host 2.2.2.2 capture only traffic between 1.1.1.1 and 2.2.2.2 not host 1.1.1.1 capture all traffic except packets to or from 1.1.1.1 tcp port 80 capture only packets to or from port 80 (http traffic) not tcp port 80 capture all traffic except http traffic udp port 53 or tcp port 80 capture all http and dns traffic host 1.1.1.1 and tcp port 80 capture all http traffic to or from host 1.1.1.1 More information on capture filters: http://wiki.wireshark.org/CaptureFilters http://www.tcpdump.org/tcpdump_man.html](https://image.slidesharecdn.com/sakeblokpacketcapturingwithtshark-1212540256140414-9/85/OSTU-Sake-Blok-on-Packet-Capturing-with-Tshark-7-320.jpg)
![How to: save the packets to a file and read packets from a file Sake Blok on… Packet Capturing with Tshark Network analysis Community Center (http://www.netcc.nl) June 2008 $ tshark -i 4 -w example.cap Capturing on Broadcom NetXtreme Gigabit Ethernet Driver (Microsoft's Packet Scheduler) 24 $ $ tshark -i 4 -S -w example.cap Capturing on Broadcom NetXtreme Gigabit Ethernet Driver (Microsoft's Packet Scheduler) 0.000000 192.168.1.30 -> 66.249.91.147 TCP 7799 > http [ACK] Seq=1 Ack=1 Win=63921 Len=0 3.124075 192.168.1.30 -> 66.249.91.147 HTTP GET / HTTP/1.1 3.155090 66.249.91.147 -> 192.168.1.30 TCP [TCP segment of a reassembled PDU] 3.159533 66.249.91.147 -> 192.168.1.30 TCP [TCP segment of a reassembled PDU] 3.159577 192.168.1.30 -> 66.249.91.147 TCP 7799 > http [ACK] Seq=626 Ack=2861 Win=64000 Len=0 3.159951 66.249.91.147 -> 192.168.1.30 HTTP HTTP/1.1 200 OK (text/html) 3.281214 192.168.1.30 -> 66.249.91.147 TCP 7799 > http [ACK] Seq=626 Ack=3019 Win=63921 Len=0 7 packets captured $ $ tshark -r example.cap 1 0.000000 192.168.1.30 -> 66.249.91.147 TCP 7799 > http [ACK] Seq=1 Ack=1 Win=63921 Len=0 2 3.124075 192.168.1.30 -> 66.249.91.147 HTTP GET / HTTP/1.1 3 3.155090 66.249.91.147 -> 192.168.1.30 TCP [TCP segment of a reassembled PDU] 4 3.159533 66.249.91.147 -> 192.168.1.30 TCP [TCP segment of a reassembled PDU] 5 3.159577 192.168.1.30 -> 66.249.91.147 TCP 7799 > http [ACK] Seq=626 Ack=2861 Win=64000 Len=0 6 3.159951 66.249.91.147 -> 192.168.1.30 HTTP HTTP/1.1 200 OK (text/html) 7 3.281214 192.168.1.30 -> 66.249.91.147 TCP 7799 > http [ACK] Seq=626 Ack=3019 Win=63921 Len=0 $](https://image.slidesharecdn.com/sakeblokpacketcapturingwithtshark-1212540256140414-9/85/OSTU-Sake-Blok-on-Packet-Capturing-with-Tshark-8-320.jpg)
![How to: show full packet details (1) Sake Blok on… Packet Capturing with Tshark Network analysis Community Center (http://www.netcc.nl) June 2008 $ tshark -r example.cap -V -R "frame.number==2" Frame 2 (1021 bytes on wire, 1021 bytes captured) Arrival Time: Jun 1, 2008 17:58:29.866889000 [Time delta from previous captured frame: 1.216981000 seconds] [Time delta from previous displayed frame: 1.216981000 seconds] [Time since reference or first frame: 1.216981000 seconds] Frame Number: 2 Frame Length: 1021 bytes Capture Length: 1021 bytes [Frame is marked: False] [Protocols in frame: eth:ip:tcp:http] Ethernet II, Src: Dell_aa:c3:72 (00:1c:23:aa:c3:72), Dst: JuniperN_bb:d1:32 (00:12:1e:bb:d1:32) Destination: JuniperN_bb:d1:32 (00:12:1e:bb:d1:32) Address: JuniperN_bb:d1:32 (00:12:1e:bb:d1:32) .... ...0 .... .... .... .... = IG bit: Individual address (unicast) .... ..0. .... .... .... .... = LG bit: Globally unique address (factory default) Source: Dell_aa:c3:72 (00:1c:23:aa:c3:72) Address: Dell_aa:c3:72 (00:1c:23:aa:c3:72) .... ...0 .... .... .... .... = IG bit: Individual address (unicast) .... ..0. .... .... .... .... = LG bit: Globally unique address (factory default) Type: IP (0x0800) Internet Protocol, Src: 192.168.1.30 (192.168.1.30), Dst: 66.249.91.103 (66.249.91.103) Version: 4 Header length: 20 bytes Differentiated Services Field: 0x00 (DSCP 0x00: Default; ECN: 0x00) 0000 00.. = Differentiated Services Codepoint: Default (0x00) .... ..0. = ECN-Capable Transport (ECT): 0 .... ...0 = ECN-CE: 0 Total Length: 1007 Identification: 0xbbfa (48122) Flags: 0x04 (Don't Fragment) 0... = Reserved bit: Not set .1.. = Don't fragment: Set ..0. = More fragments: Not set Fragment offset: 0 Time to live: 128 Protocol: TCP (0x06) Header checksum: 0xdae7 [correct] [Good: True] [Bad : False] Source: 192.168.1.30 (192.168.1.30) Destination: 66.249.91.103 (66.249.91.103) Transmission Control Protocol, Src Port: senomix02 (8053), Dst Port: http (80), Seq: 1, Ack: 1, Len: 967 Source port: senomix02 (8053) Destination port: http (80) Sequence number: 1 (relative sequence number) [Next sequence number: 968 (relative sequence number)] Acknowledgement number: 1 (relative ack number) Header length: 20 bytes Flags: 0x18 (PSH, ACK) 0... .... = Congestion Window Reduced (CWR): Not set .0.. .... = ECN-Echo: Not set ..0. .... = Urgent: Not set ...1 .... = Acknowledgment: Set .... 1... = Push: Set .... .0.. = Reset: Not set .... ..0. = Syn: Not set .... ...0 = Fin: Not set Window size: 63921 Checksum: 0x6408 [validation disabled] [Good Checksum: False] [Bad Checksum: False] Hypertext Transfer Protocol GET /intl/nl/about.html HTTP/1.1\r\n Request Method: GET Request URI: /intl/nl/about.html Request Version: HTTP/1.1 Host: www.google.nl\r\n User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.8.1.14) Gecko/20080404 Firefox/2.0.0.14\r\n Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5\r\n Accept-Language: en-us,en;q=0.5\r\n Accept-Encoding: gzip,deflate\r\n Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7\r\n Keep-Alive: 300\r\n Connection: keep-alive\r\n Referer: http://www.google.nl/webhp?hl=nl&tab=vw\r\n [truncated] Cookie: __utma=117705887.1086025020.1212335899.1212335899.1212335899.1; __utmb=117705887; __utmc=117705887; __utmz=1 17705887.1212335899.1.1.utmccn=(referral)|utmcsr=google.nl|utmcct=/webhp|utmcmd=referral; PREF=ID=35e15b106e56f If-Modified-Since: Fri, 18 Jan 2008 18:40:26 GMT\r\n Cache-Control: max-age=0\r\n \r\n $](https://image.slidesharecdn.com/sakeblokpacketcapturingwithtshark-1212540256140414-9/85/OSTU-Sake-Blok-on-Packet-Capturing-with-Tshark-10-320.jpg)
![How to: show full packet details (2) Sake Blok on… Packet Capturing with Tshark Network analysis Community Center (http://www.netcc.nl) June 2008 Internet Protocol, Src: 192.168.1.30 (192.168.1.30), Dst: 66.249.91.103 (66.249.91.103) Version: 4 Header length: 20 bytes Differentiated Services Field: 0x00 (DSCP 0x00: Default; ECN: 0x00) 0000 00.. = Differentiated Services Codepoint: Default (0x00) .... ..0. = ECN-Capable Transport (ECT): 0 .... ...0 = ECN-CE: 0 Total Length: 1007 Identification: 0xbbfa (48122) Flags: 0x04 (Don't Fragment) 0... = Reserved bit: Not set .1.. = Don't fragment: Set ..0. = More fragments: Not set Fragment offset: 0 Time to live: 128 Protocol: TCP (0x06) Header checksum: 0xdae7 [correct] [Good: True] [Bad : False] Source: 192.168.1.30 (192.168.1.30) Destination: 66.249.91.103 (66.249.91.103)](https://image.slidesharecdn.com/sakeblokpacketcapturingwithtshark-1212540256140414-9/85/OSTU-Sake-Blok-on-Packet-Capturing-with-Tshark-11-320.jpg)
![How to: show full packet details (3) Sake Blok on… Packet Capturing with Tshark Network analysis Community Center (http://www.netcc.nl) June 2008 Hypertext Transfer Protocol GET /intl/nl/about.html HTTP/1.1\r\n Request Method: GET Request URI: /intl/nl/about.html Request Version: HTTP/1.1 Host: www.google.nl\r\n User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.8.1.14) Gecko/20080404 Firefox/2.0.0.14\r\n Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5\r\n Accept-Language: en-us,en;q=0.5\r\n Accept-Encoding: gzip,deflate\r\n Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7\r\n Keep-Alive: 300\r\n Connection: keep-alive\r\n Referer: http://www.google.nl/webhp?hl=nl&tab=vw\r\n [truncated] Cookie: __utma=117705887.1086025020.1212335899.1212335899.1212335899.1; __utmb=117705887; __utmc=117705887; __utmz=1 17705887.1212335899.1.1.utmccn=(referral)|utmcsr=google.nl|utmcct=/webhp|utmcmd=referral; PREF=ID=35e15b106e56f If-Modified-Since: Fri, 18 Jan 2008 18:40:26 GMT\r\n Cache-Control: max-age=0\r\n \r\n](https://image.slidesharecdn.com/sakeblokpacketcapturingwithtshark-1212540256140414-9/85/OSTU-Sake-Blok-on-Packet-Capturing-with-Tshark-12-320.jpg)