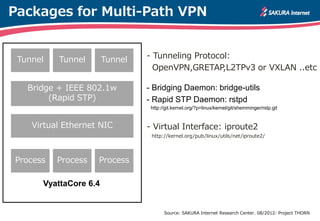
This document provides an overview of multi-path VPN technologies. It discusses using Linux bridge, Rapid STP, virtual Ethernet NICs, and tunneling protocols like OpenVPN and L2TPv3 to enable multi-path VPNs across multiple cloud providers. It also covers related topics like performance benchmarking and tuning the Linux kernel for improved throughput.
![Tunneling Performance Analysis
[System: Intel(R) Core(TM) i7-3930K CPU @ 3.20GHz / 32GB DDR3-DIMM]
[Traffic Generater: *pktgen, **iperf. Traffic Monitor: vnstat]
VXLAN on UNKOWN-DEVICE (IPoEth) 4.79 Gbit/s**
Mellanox ConnectX3 10GbE-NIC (IPoEth) 9.93 Gbit/s*
Mellanox ConnectX3 40GbE-NIC (IPoEth) 27.45 Gbit/s*
Mellanox ConnectX3 FDR10-HCA (IPoIB) 29.56 Gbit/s**
(Gbit/sec) (Packet/sec)
820Kpps (MTU 1,500)
882Kpps (MTU 1,500)
2.28Mpps (MTU 1,500)
61Kpps (MTU 65,520)
High is Faster Low is Better
OpenVPN on FDR10-HCA (IPoIB) 0.24 Gbit/s*
GRETAP on FDR10-HCA (IPoIB) 5.41 Gbit/s*
L2TPv3 on FDR10-HCA (IPoIB) 10.65 Gbit/s*
N/A
N/A
N/A
Source: SAKURA Internet Research Center. 07/2012: Project THORN](https://image.slidesharecdn.com/ricc-vyatta-20130831-n-matsumoto-130830233417-phpapp01/85/VYATTA-VPN-10-320.jpg)

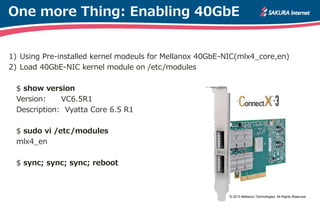
![40GbE-NIC Status Check
$ show interfaces ethernet eth1 physical
Settings for eth1:
Supported ports: [ TP ]
:
Speed: 40000Mb/s
Duplex: Full
Port: Twisted Pair
:
Link detected: yes
driver: mlx4_en
version: 2.0 (Dec 2011)
firmware-version: 2.10.800
bus-info: 0000:01:00.0
© 2013 Mellanox Technologies. All Rights Reserved.](https://image.slidesharecdn.com/ricc-vyatta-20130831-n-matsumoto-130830233417-phpapp01/85/VYATTA-VPN-18-320.jpg)
![40GbE-NIC module Check
$ sudo modinfo mlx4_en
filename: /lib/modules/3.3.8-1-586-vyatta/.../mellanox/mlx4/mlx4_en.ko
version: 2.0 (Dec 2011)
license: Dual BSD/GPL
description: Mellanox ConnectX HCA Ethernet driver
author: Liran Liss, Yevgeny Petrilin
srcversion: 142AB5E074EB35EDB627247
depends: mlx4_core
intree: Y
vermagic: 3.3.8-1-586-vyatta SMP mod_unload modversions 586
parm: inline_thold:threshold for using inline data (int)
parm: udp_rss:Enable RSS for incomming UDP traffic or disabled (0)...
parm: pfctx:Priority based Flow Control policy on TX[7:0]. Per prio...
parm: pfcrx:Priority based Flow Control policy on RX[7:0]. Per prio...](https://image.slidesharecdn.com/ricc-vyatta-20130831-n-matsumoto-130830233417-phpapp01/85/VYATTA-VPN-20-320.jpg)