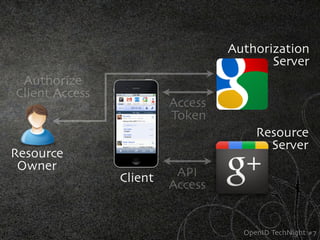
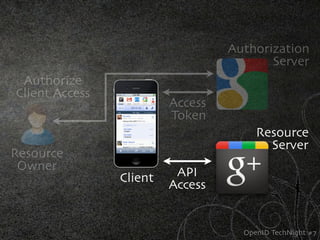
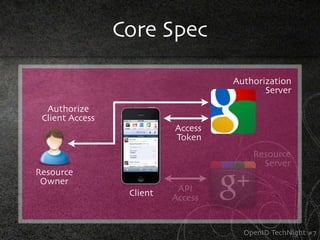
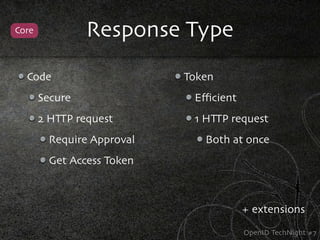
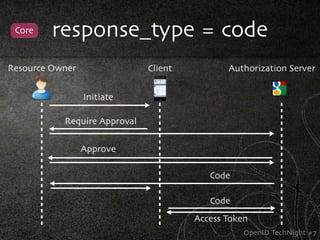
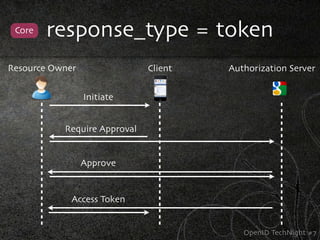
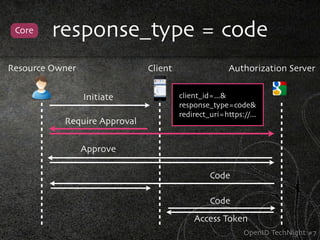
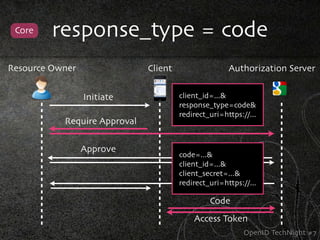
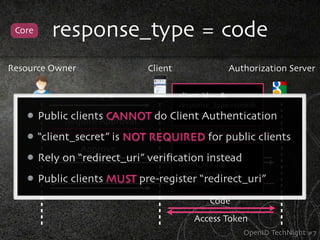
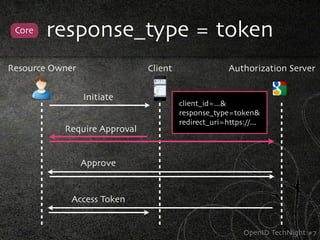
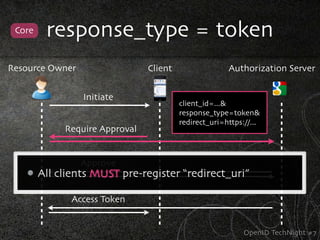
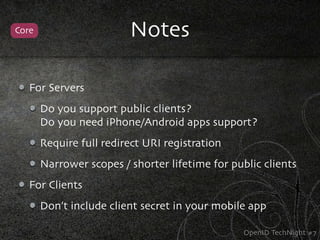
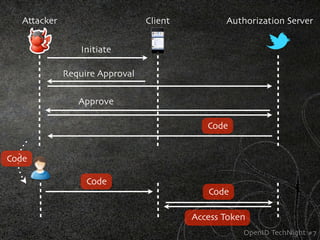
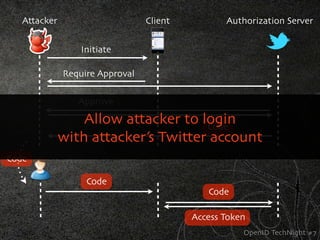
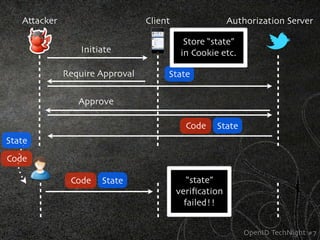
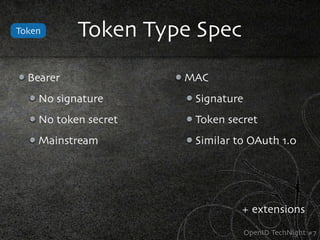
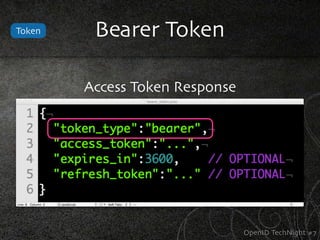
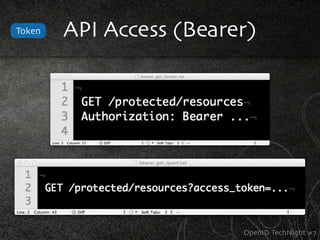
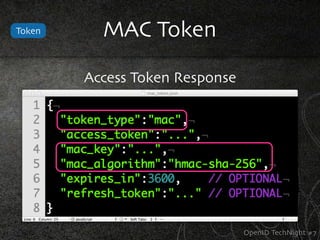
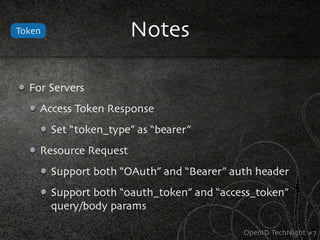
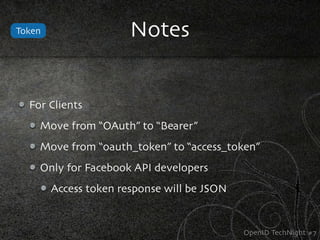
The document discusses OAuth 2.0 and its updates. It provides a brief history of OAuth including versions 1.0 and 2.0. It explains the core specification of OAuth 2.0 including authorization servers, resource owners, clients, access tokens, and response types. It also summarizes the token type specification and security considerations for OAuth implementations.