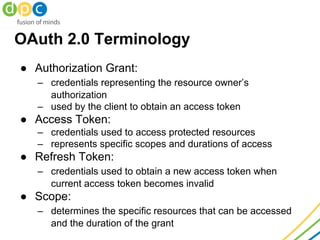
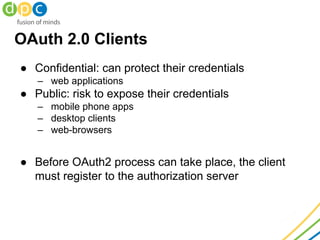
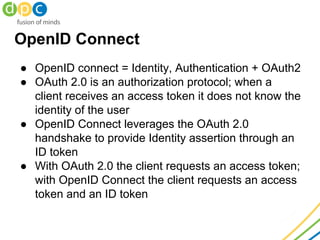
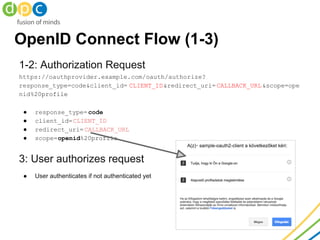
The document covers the topics of OAuth 2.0, OpenID Connect, and JSON Web Tokens (JWT), outlining their functionalities in authorizing and authenticating users. OAuth 2.0 presents methods for secure resource access via tokens while addressing common security issues. OpenID Connect builds on OAuth 2.0 to provide user identity verification through an ID token, and the document also includes flow diagrams and practical implementation details.