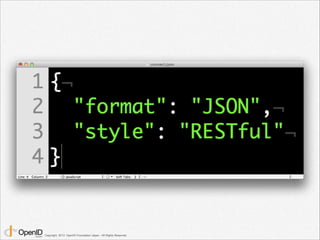
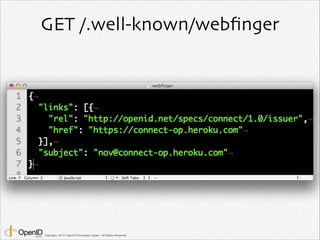
The document is a presentation on OpenID Connect 101 by Nov Matake of OpenID Foundation Japan. It provides an overview of OpenID Connect, including how it uses OAuth 2.0 with an added identity layer, the code flow process, ID tokens and their contents, scopes, discovery, and dynamic client registration. It also discusses password leaks, two-factor authentication, and security best practices.