Embed presentation
Downloaded 72 times
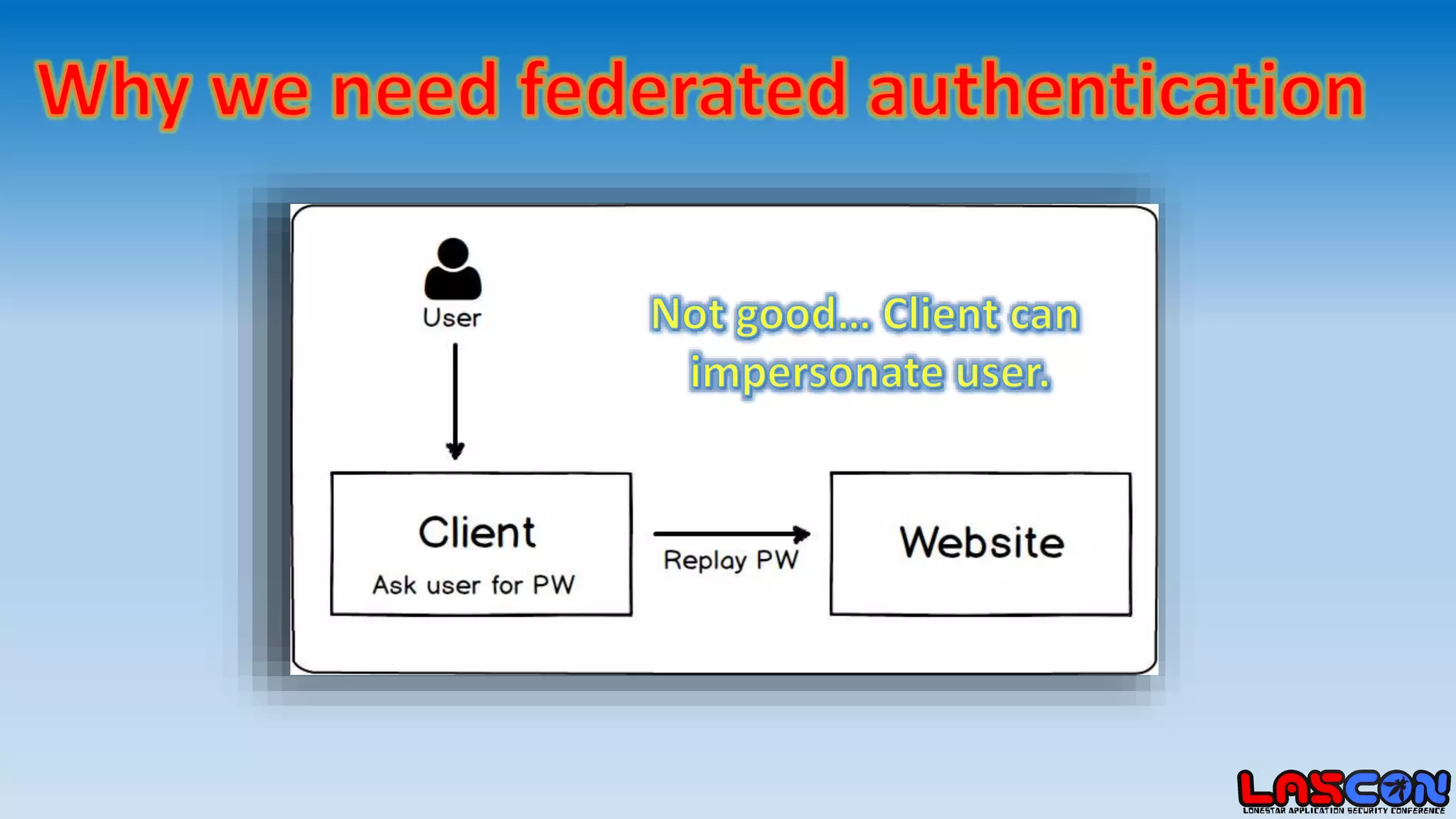
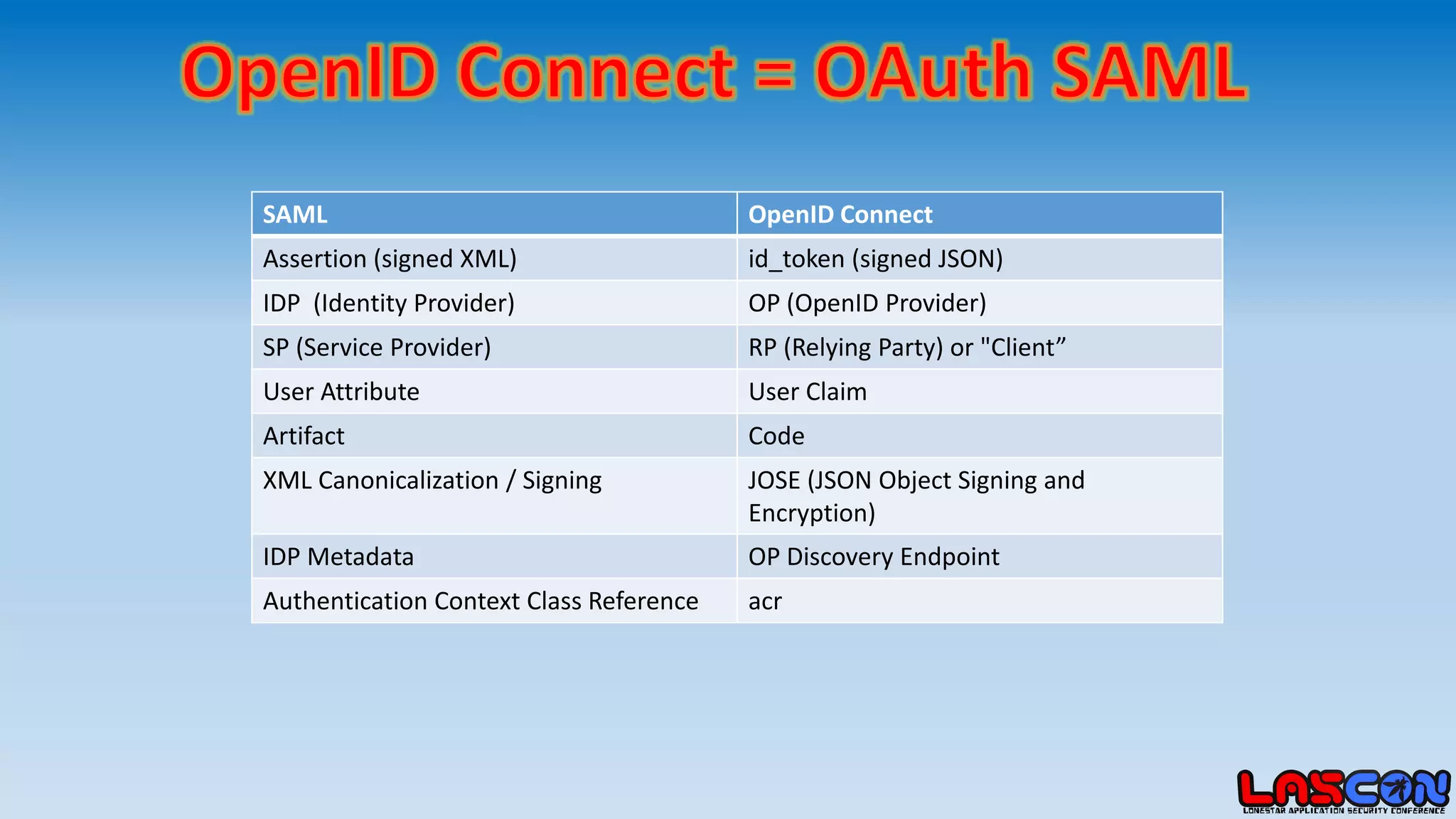
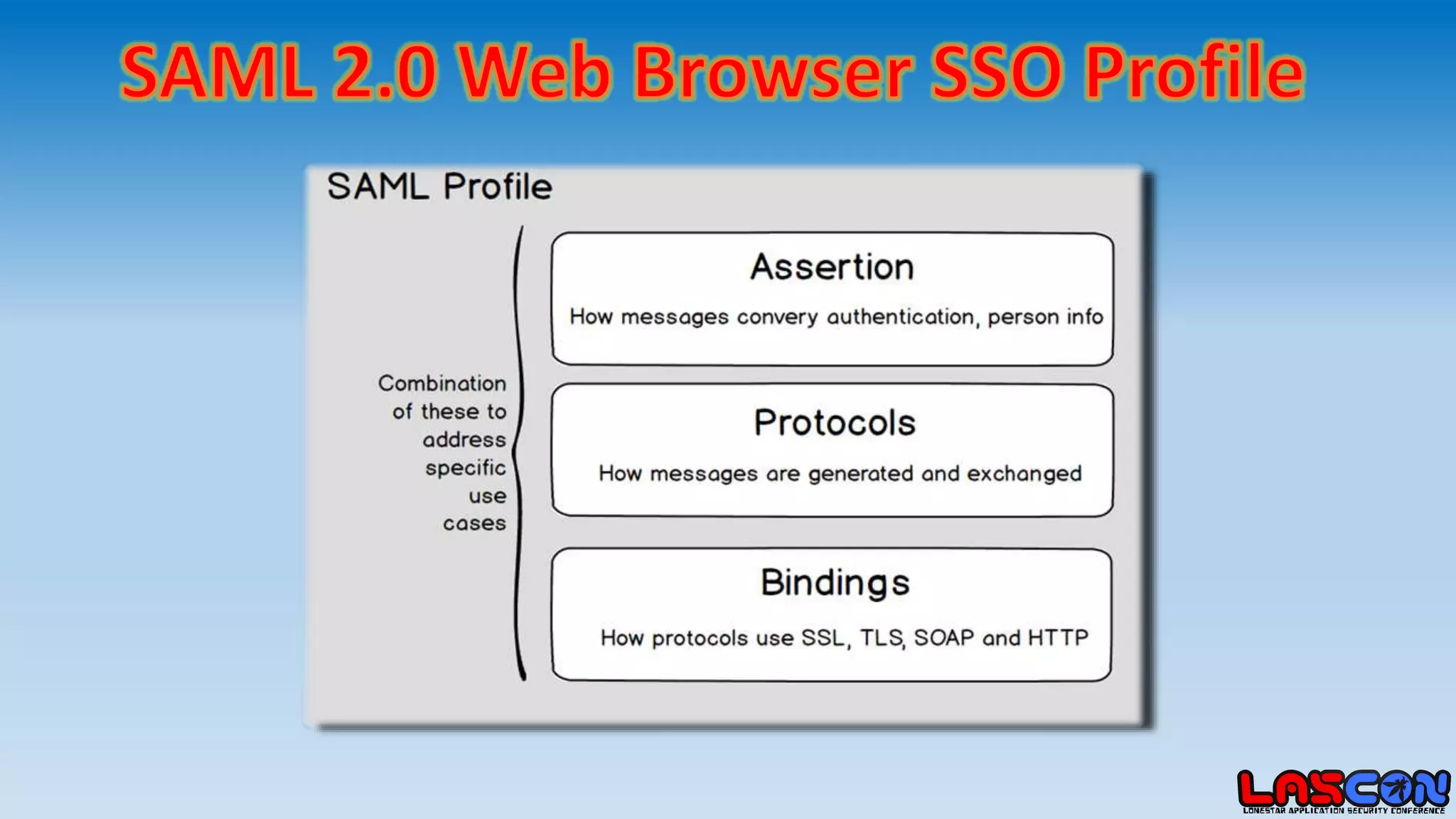
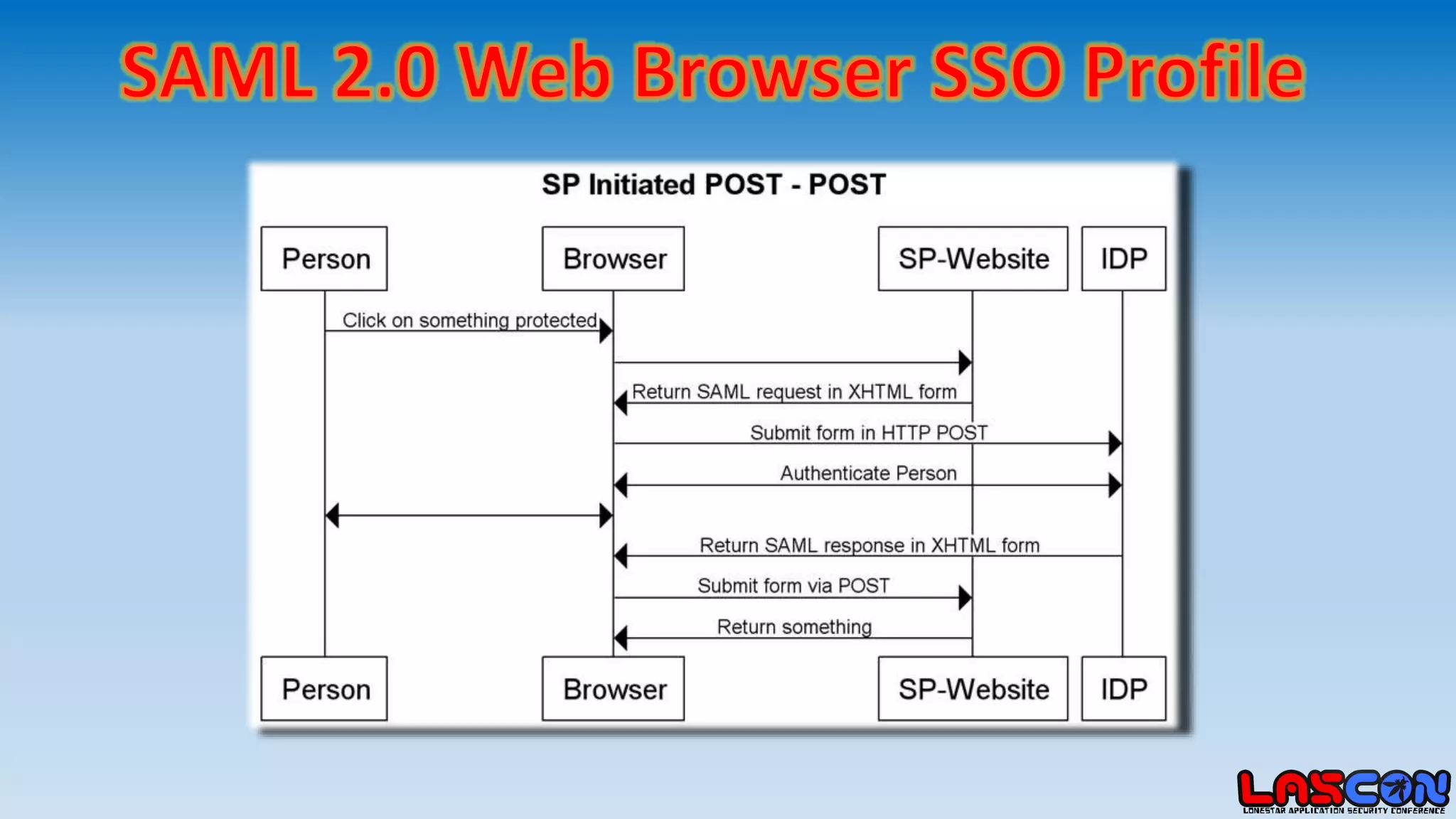
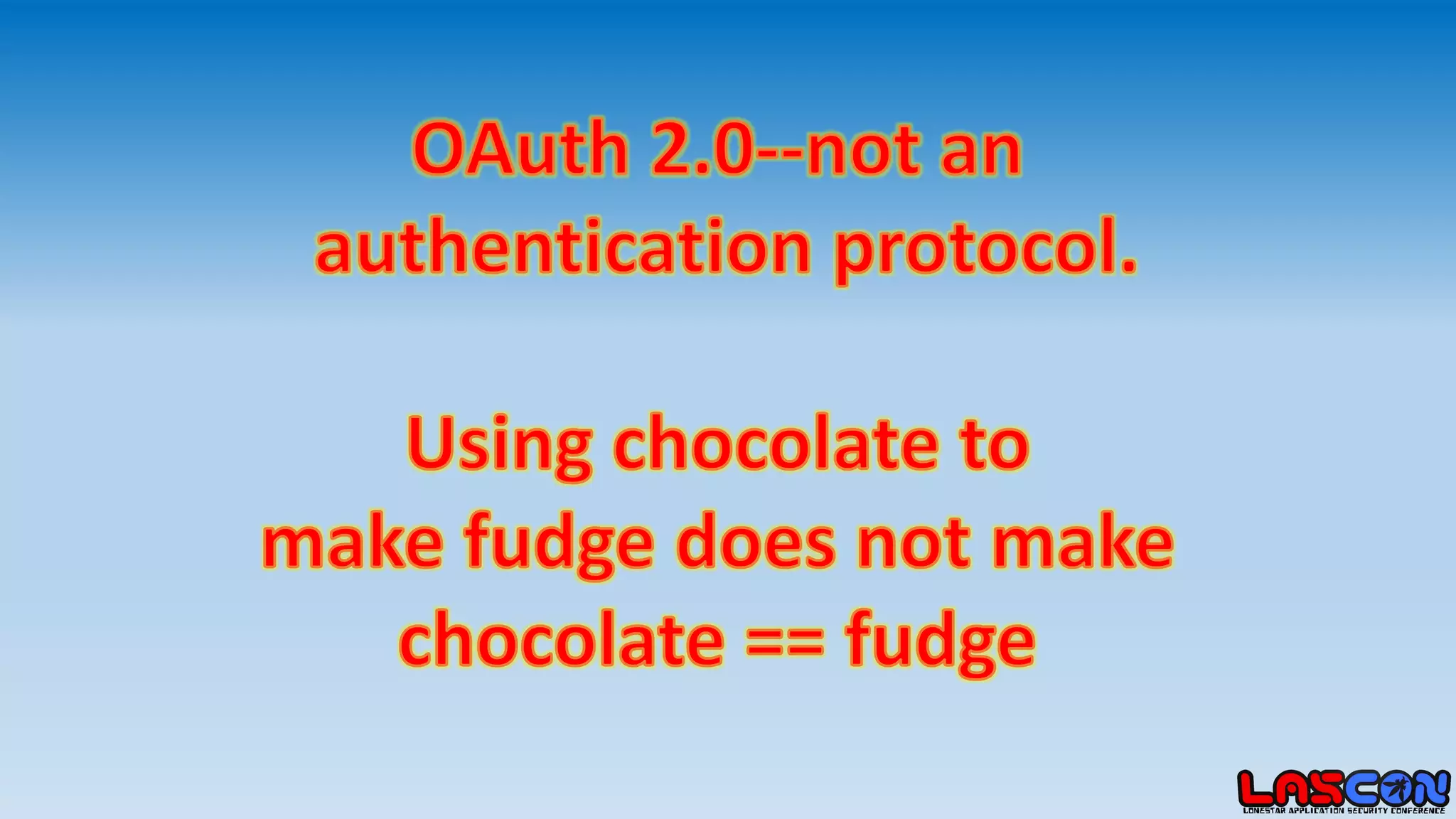
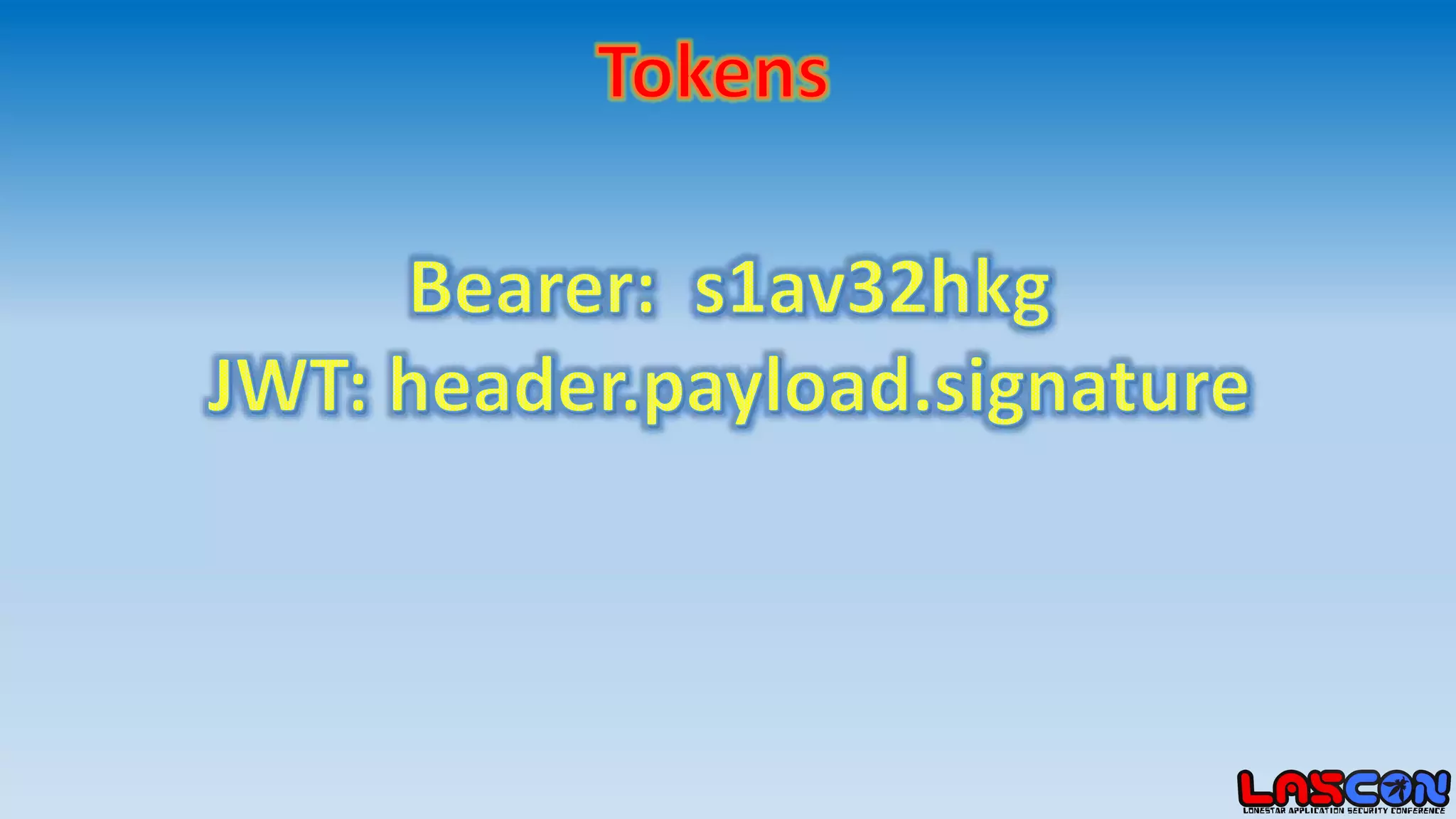
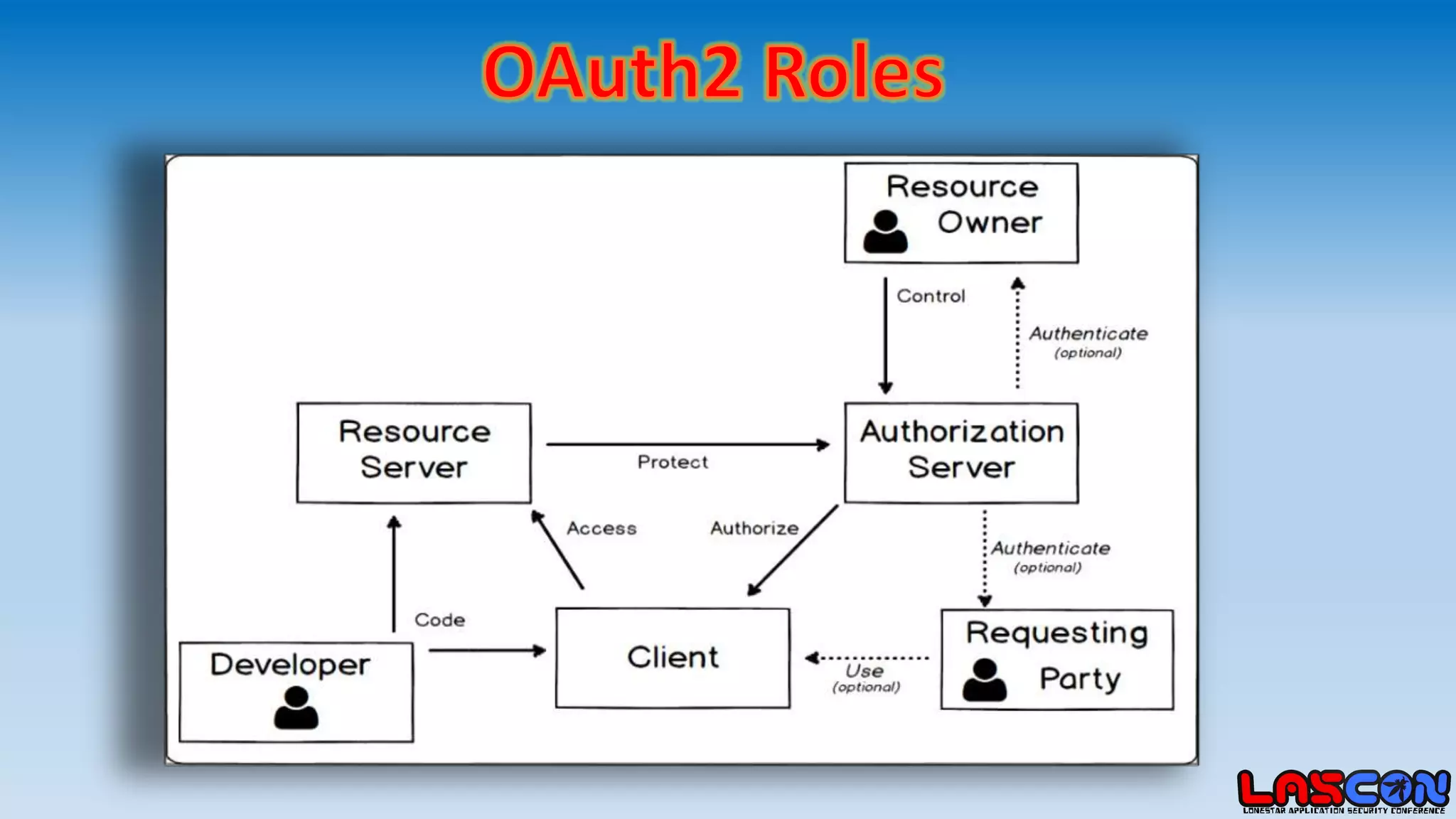
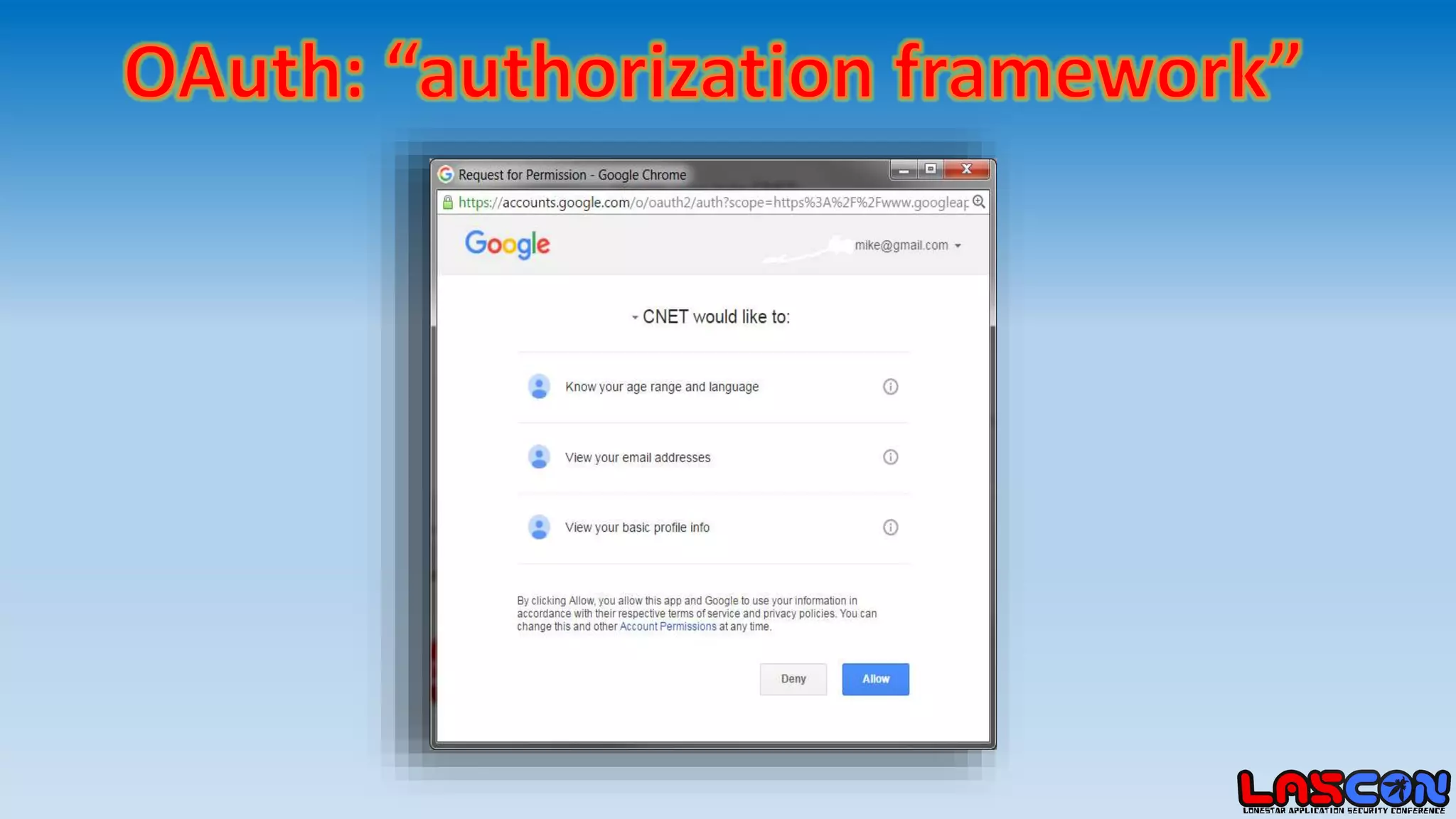
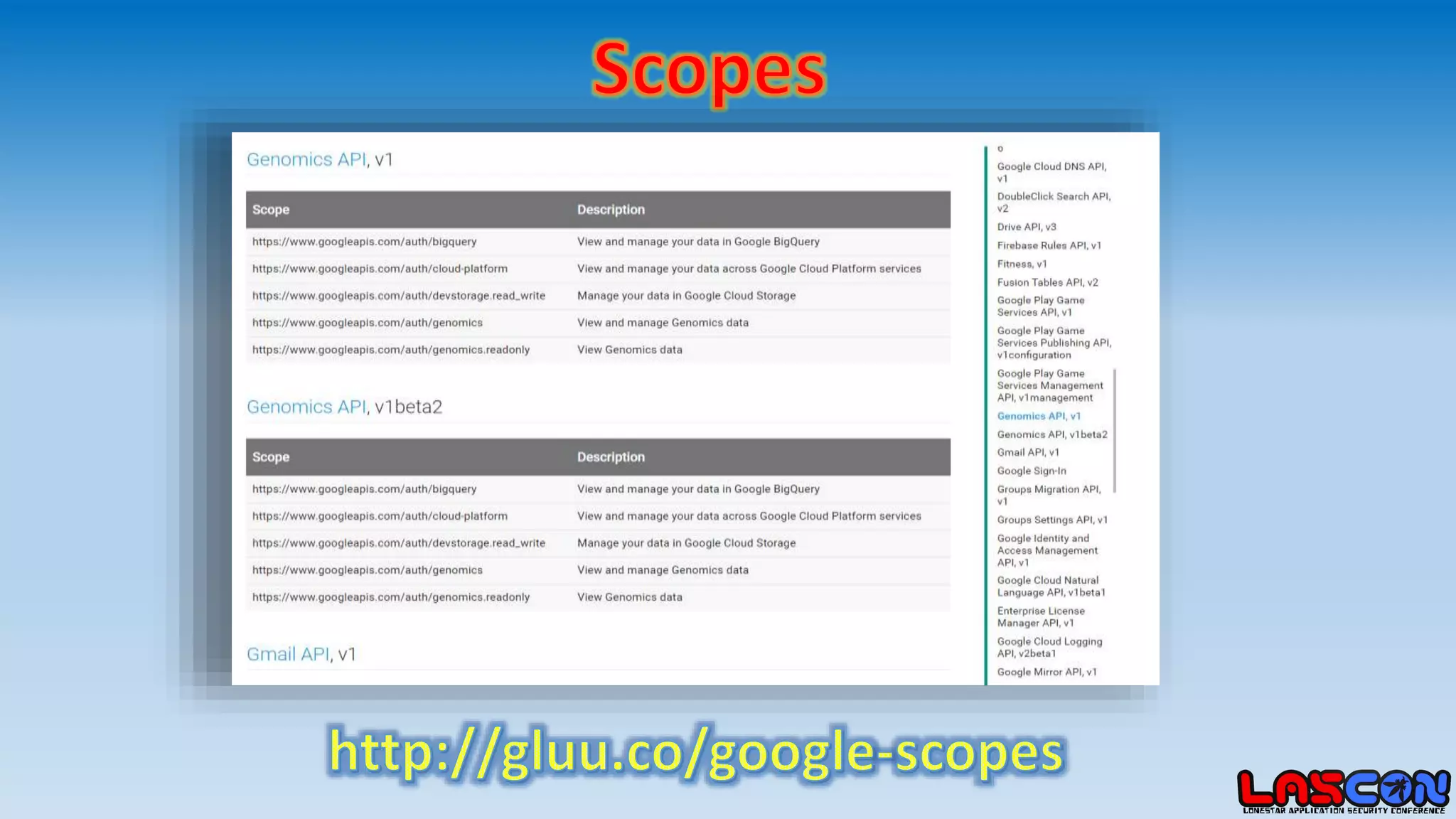
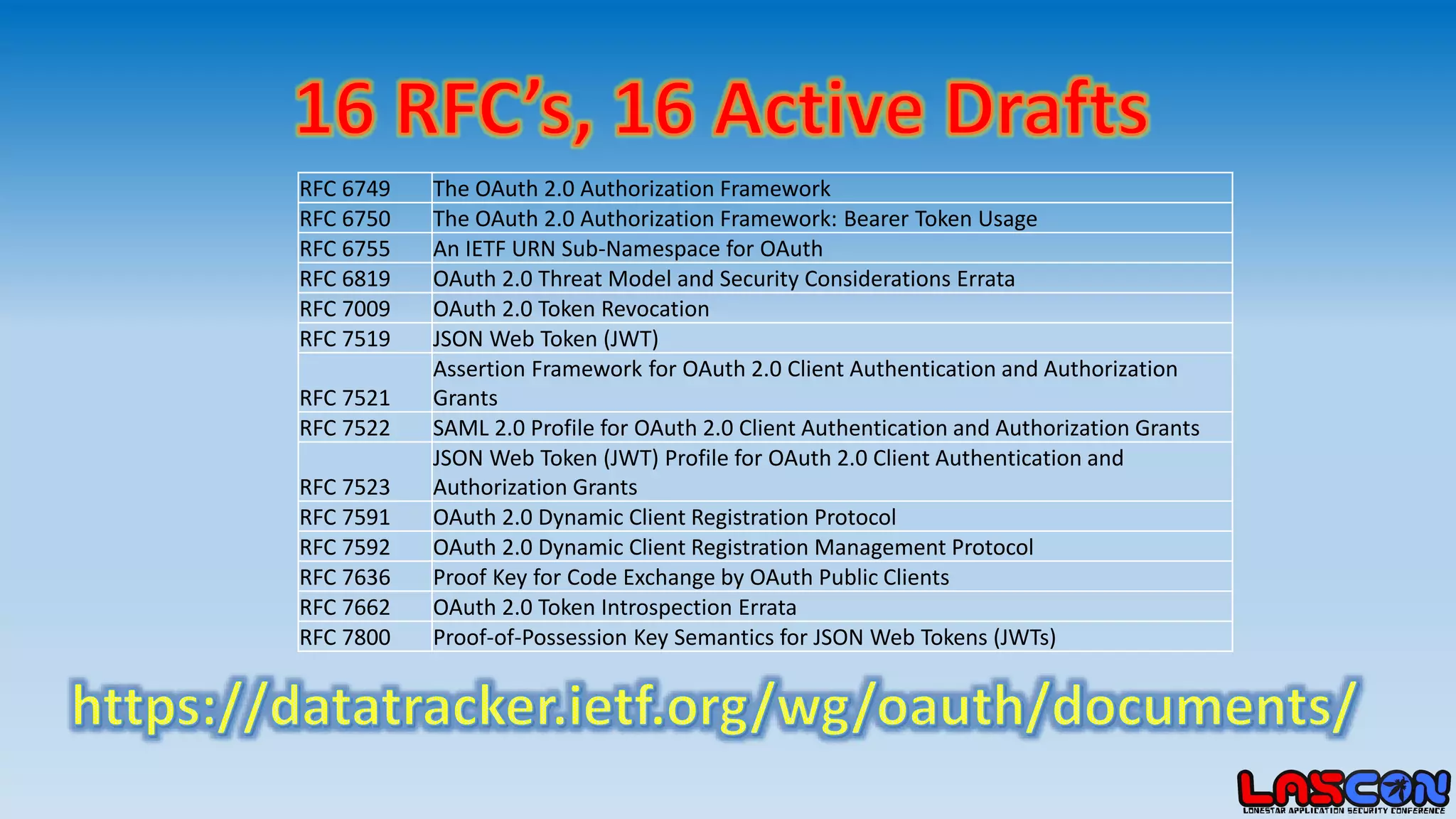
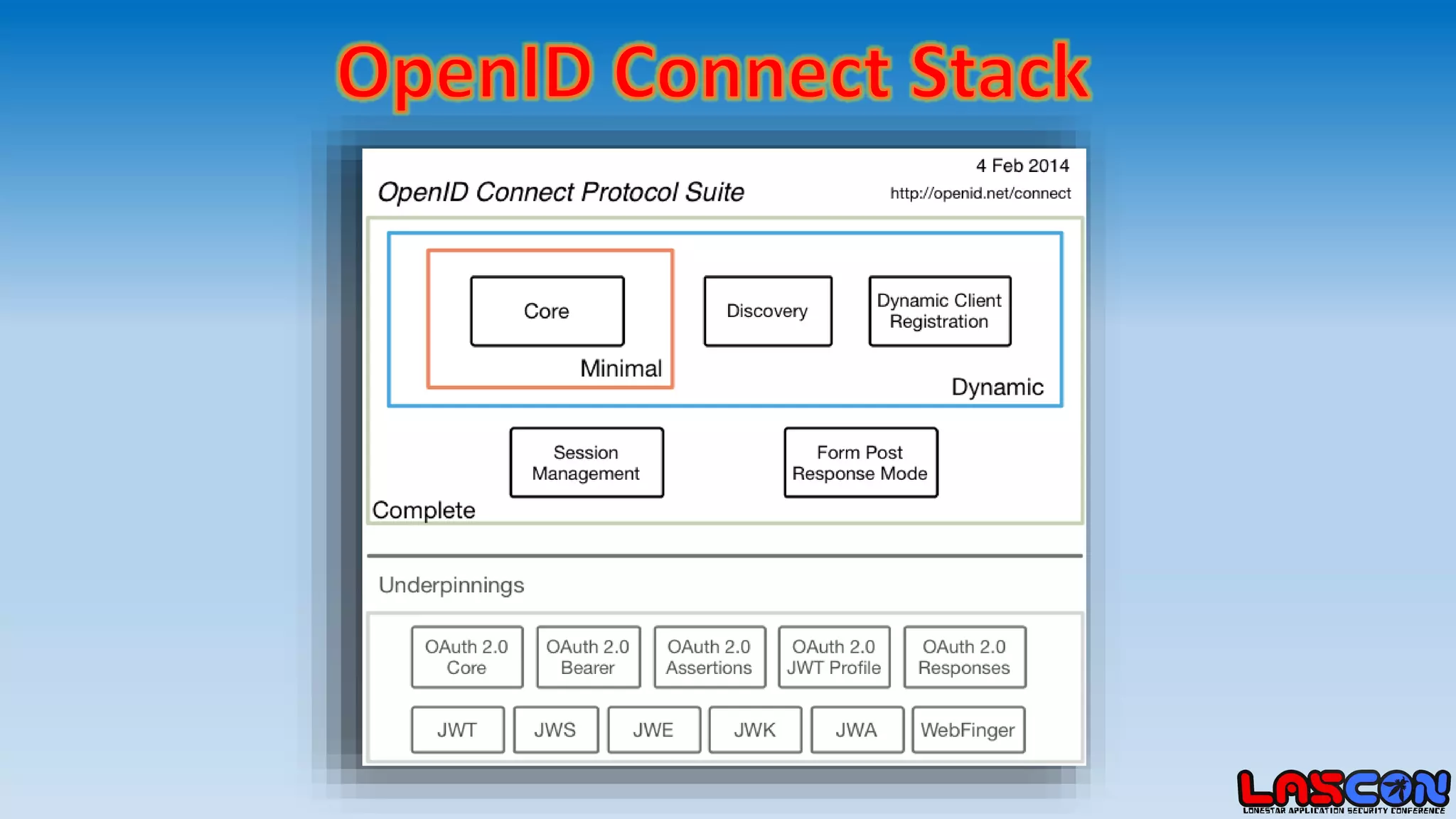
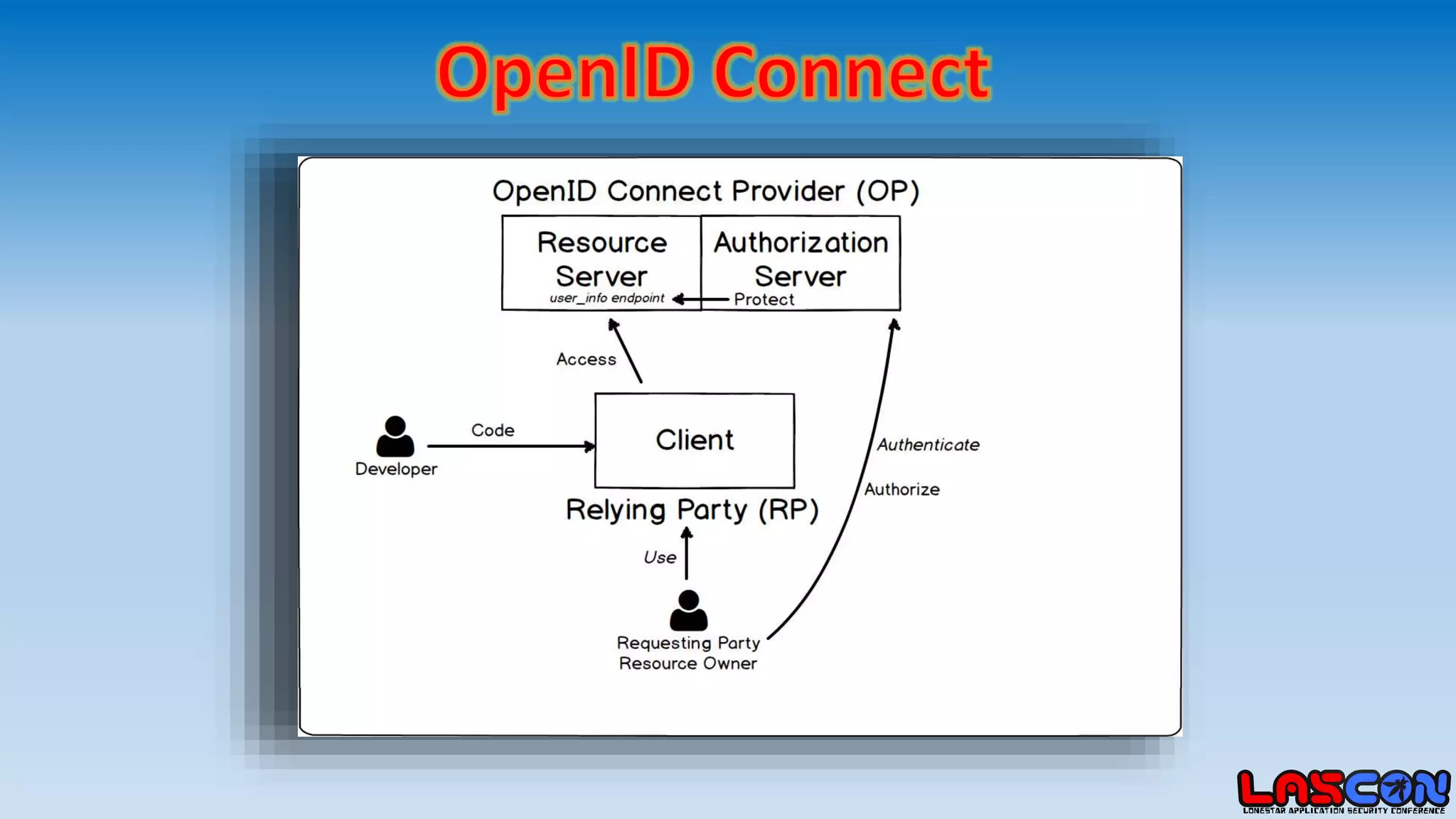
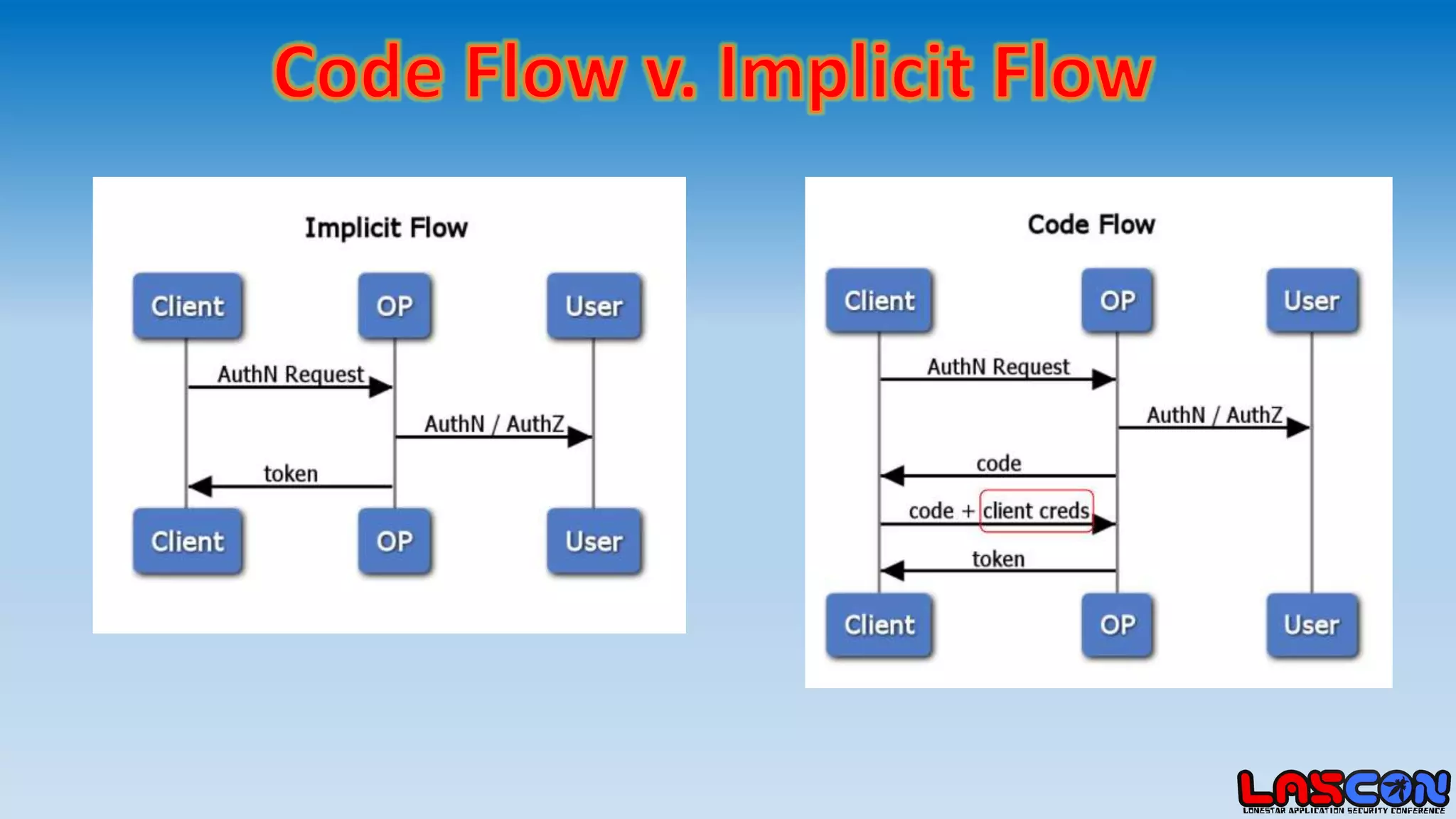


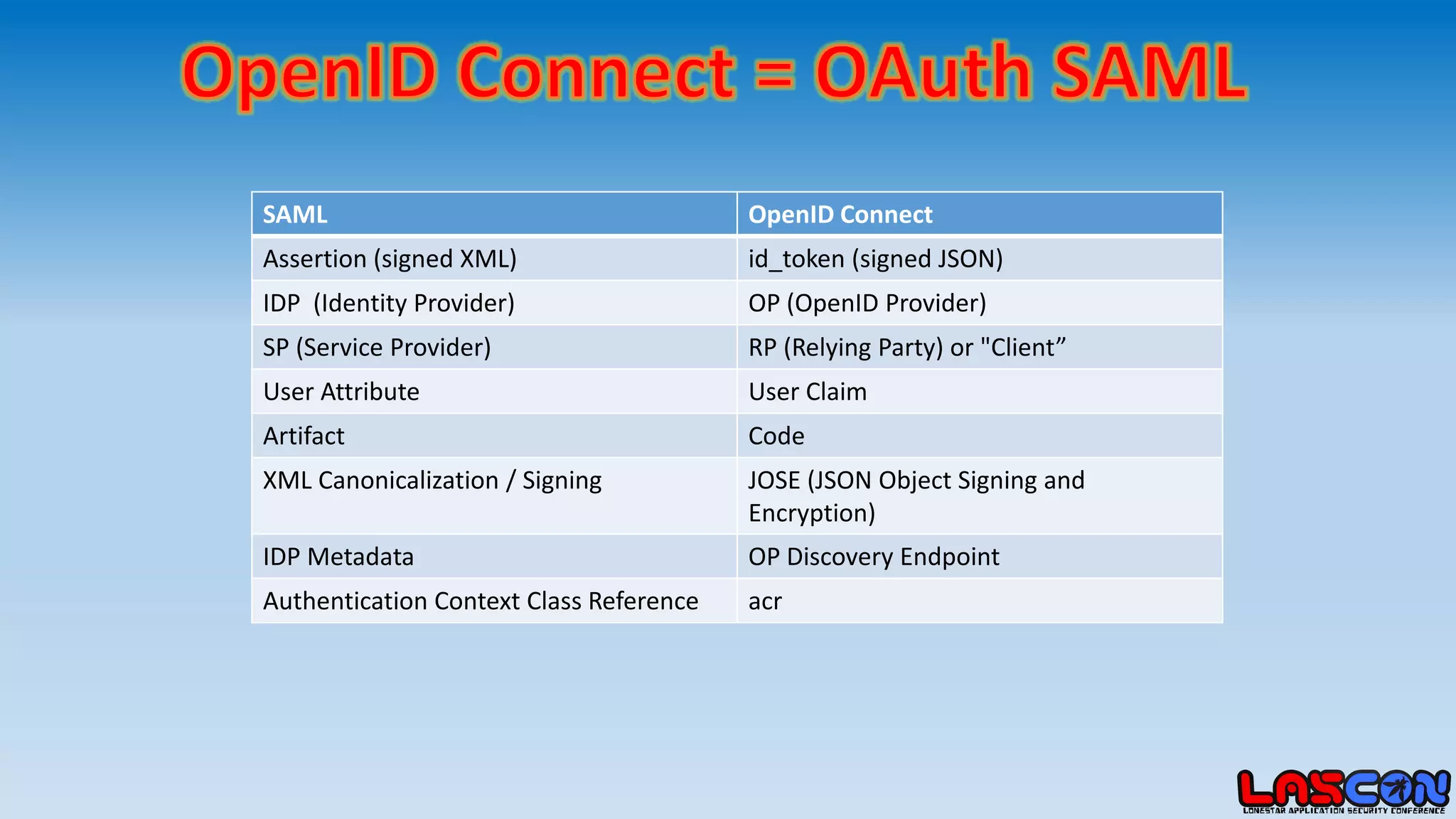
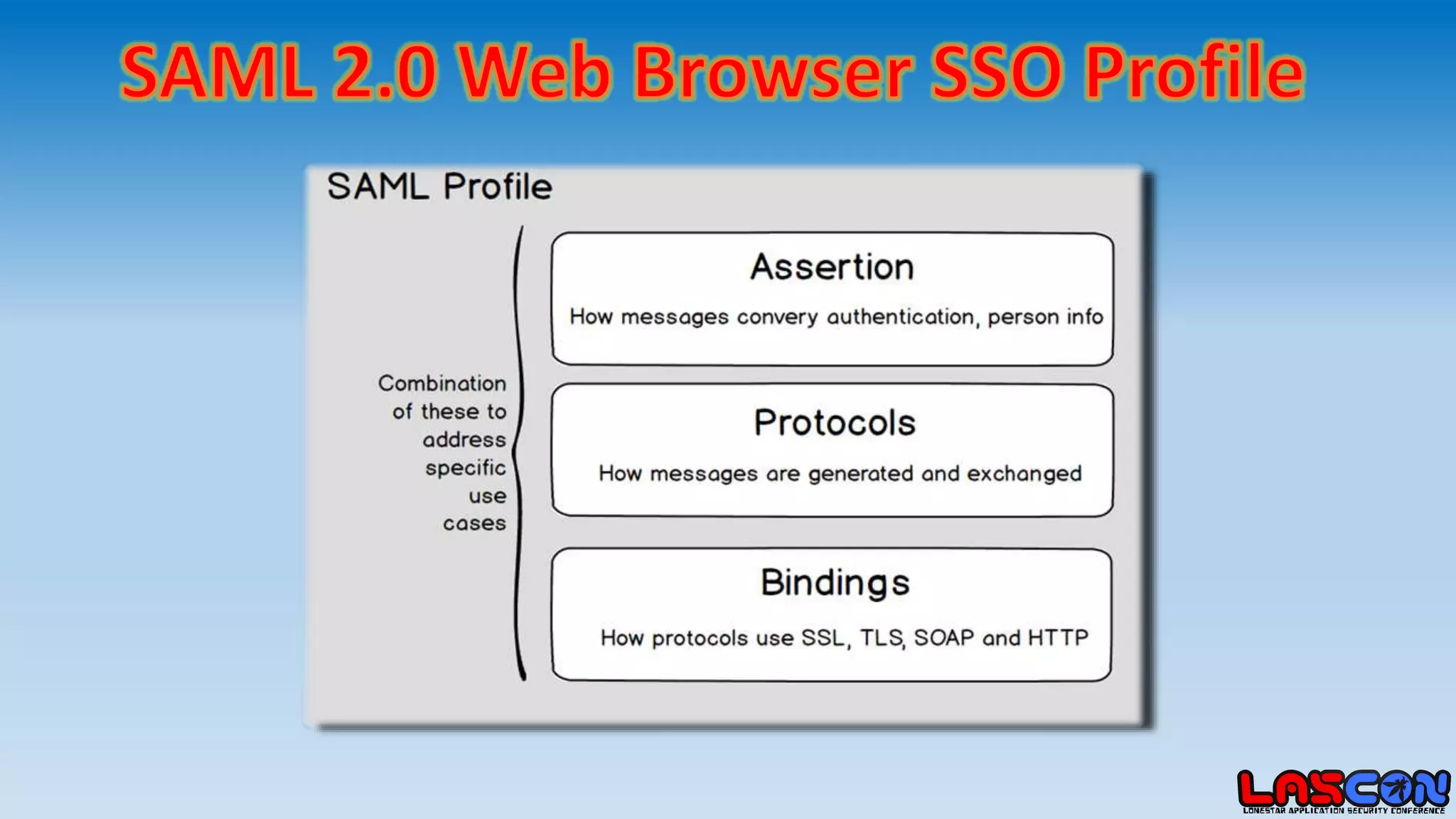
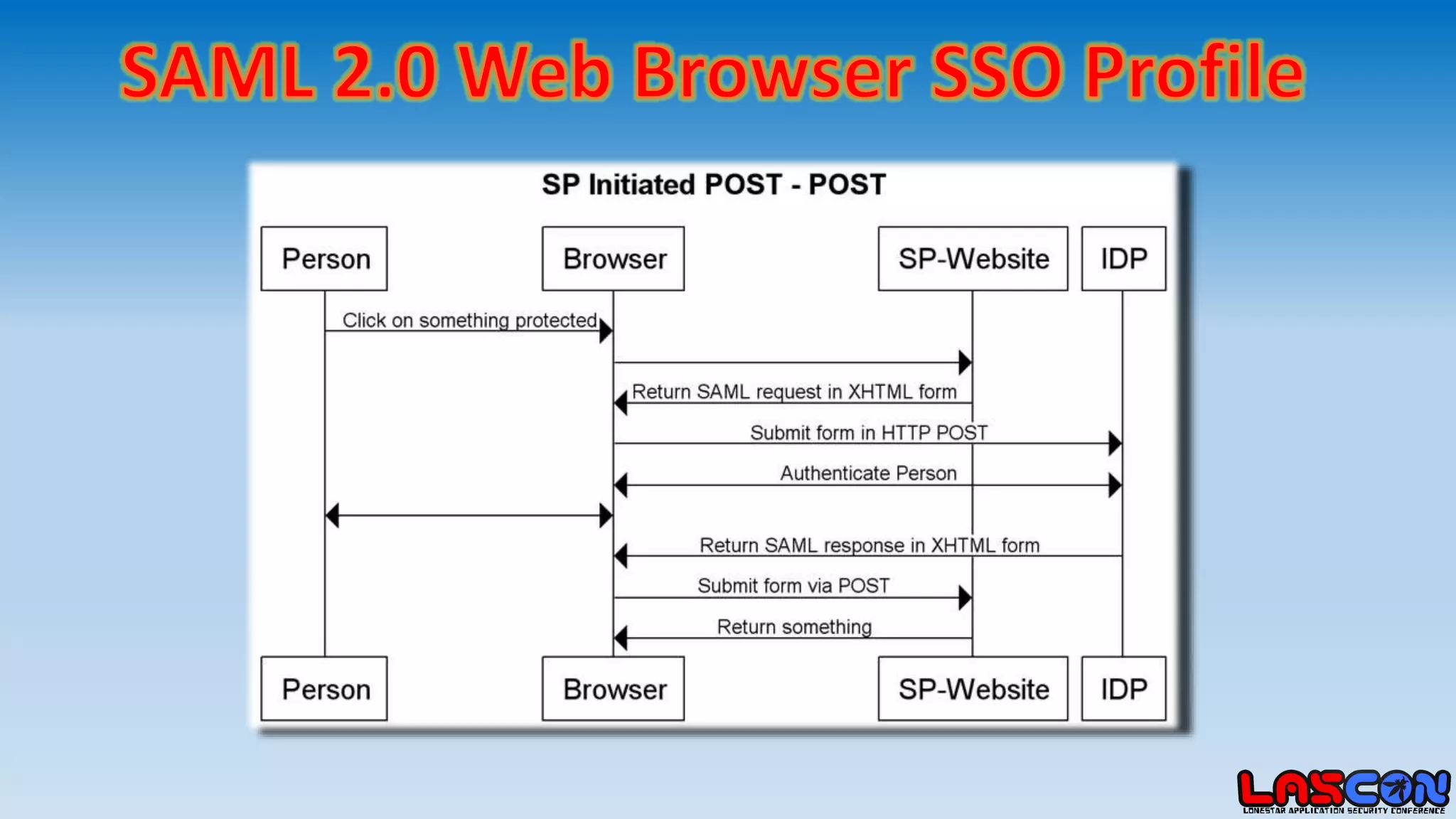
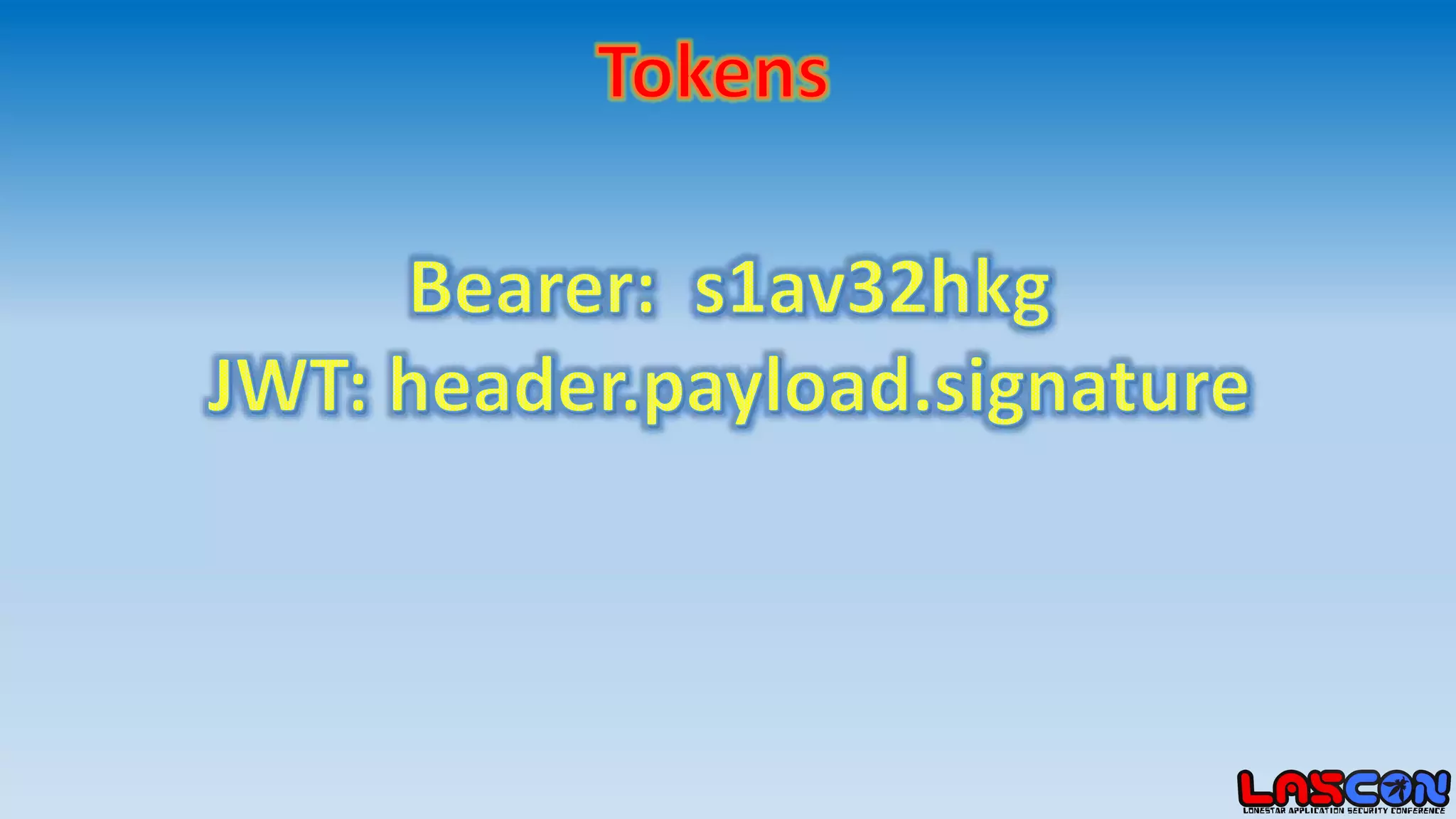
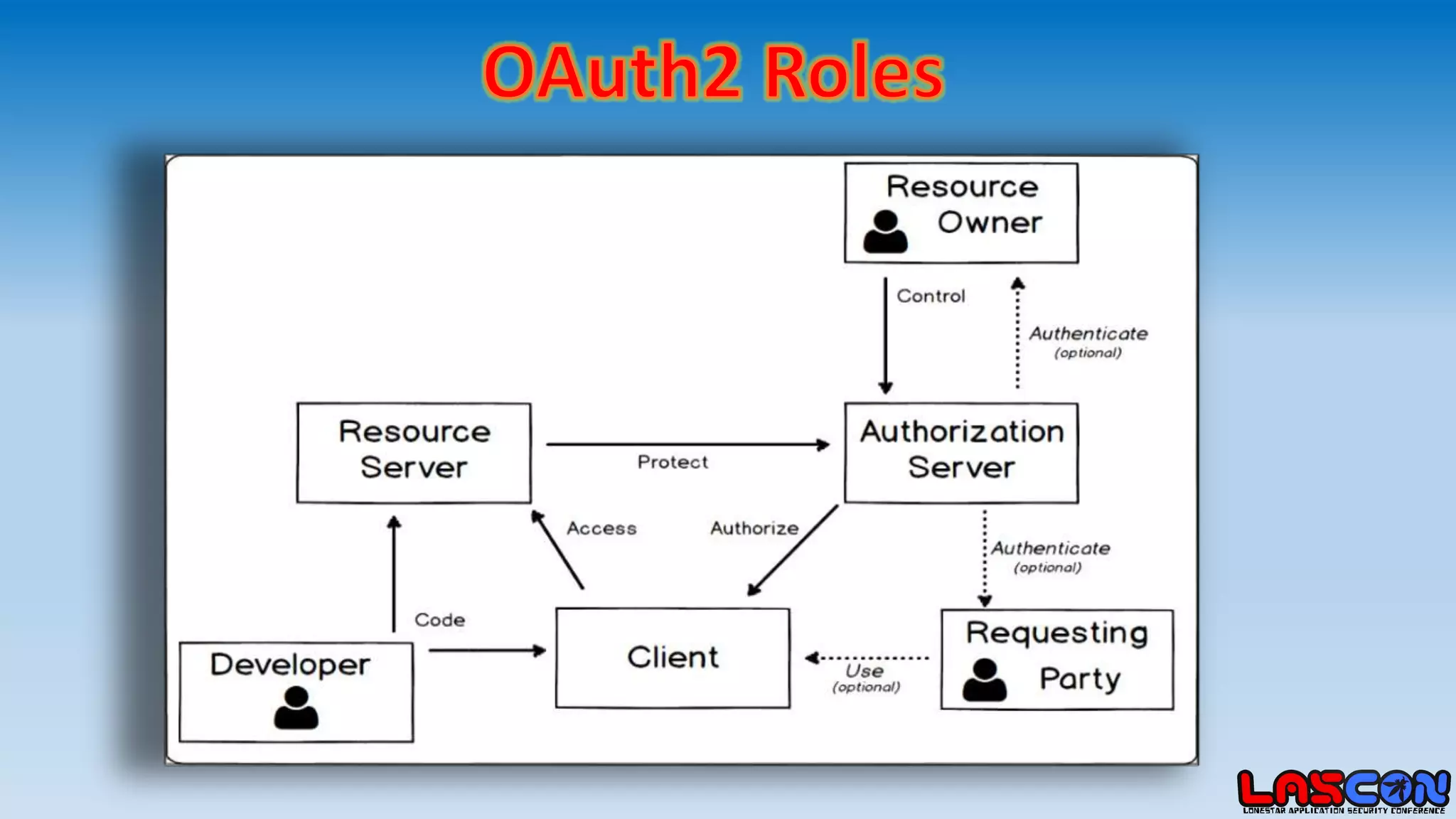
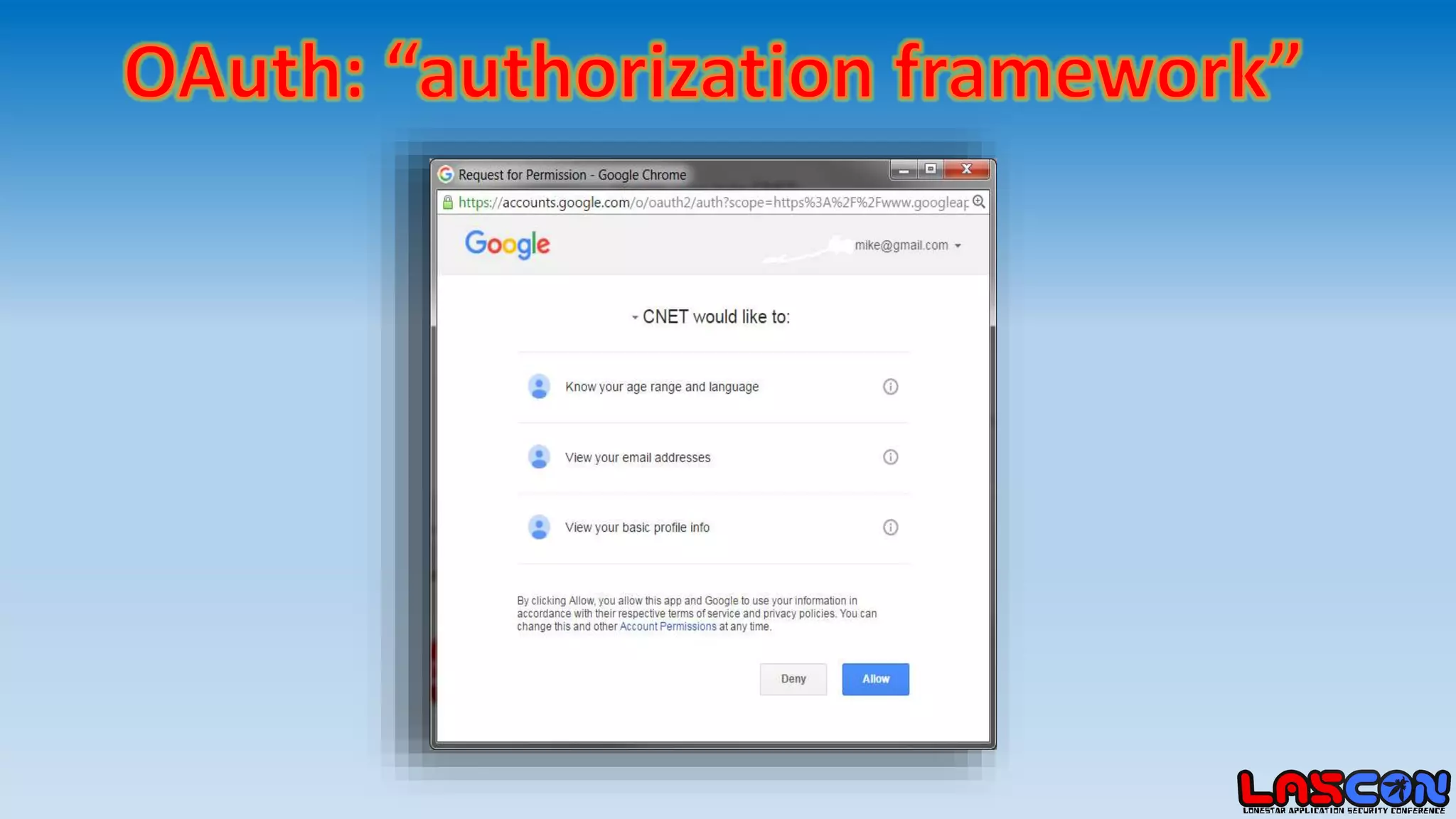
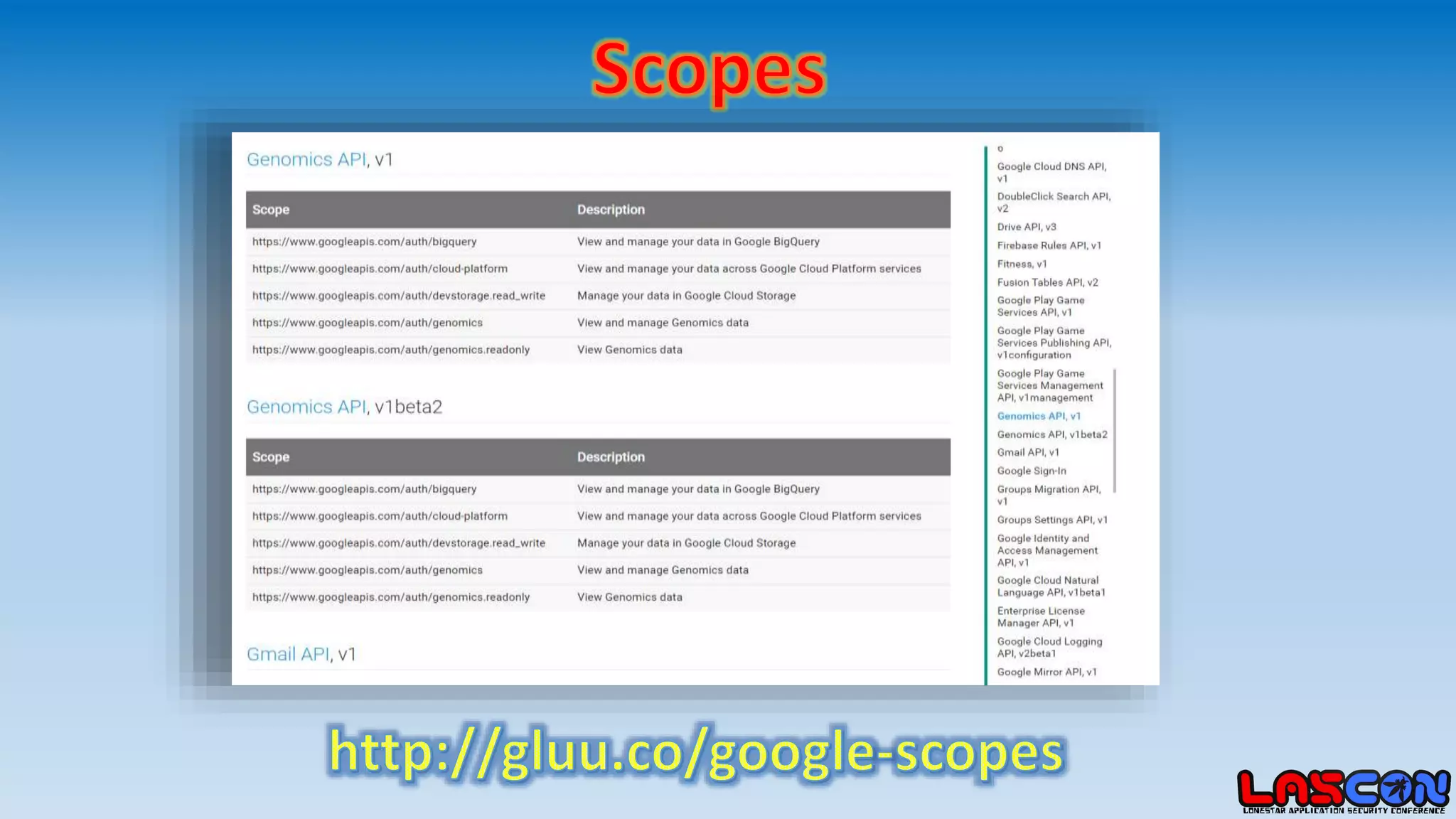
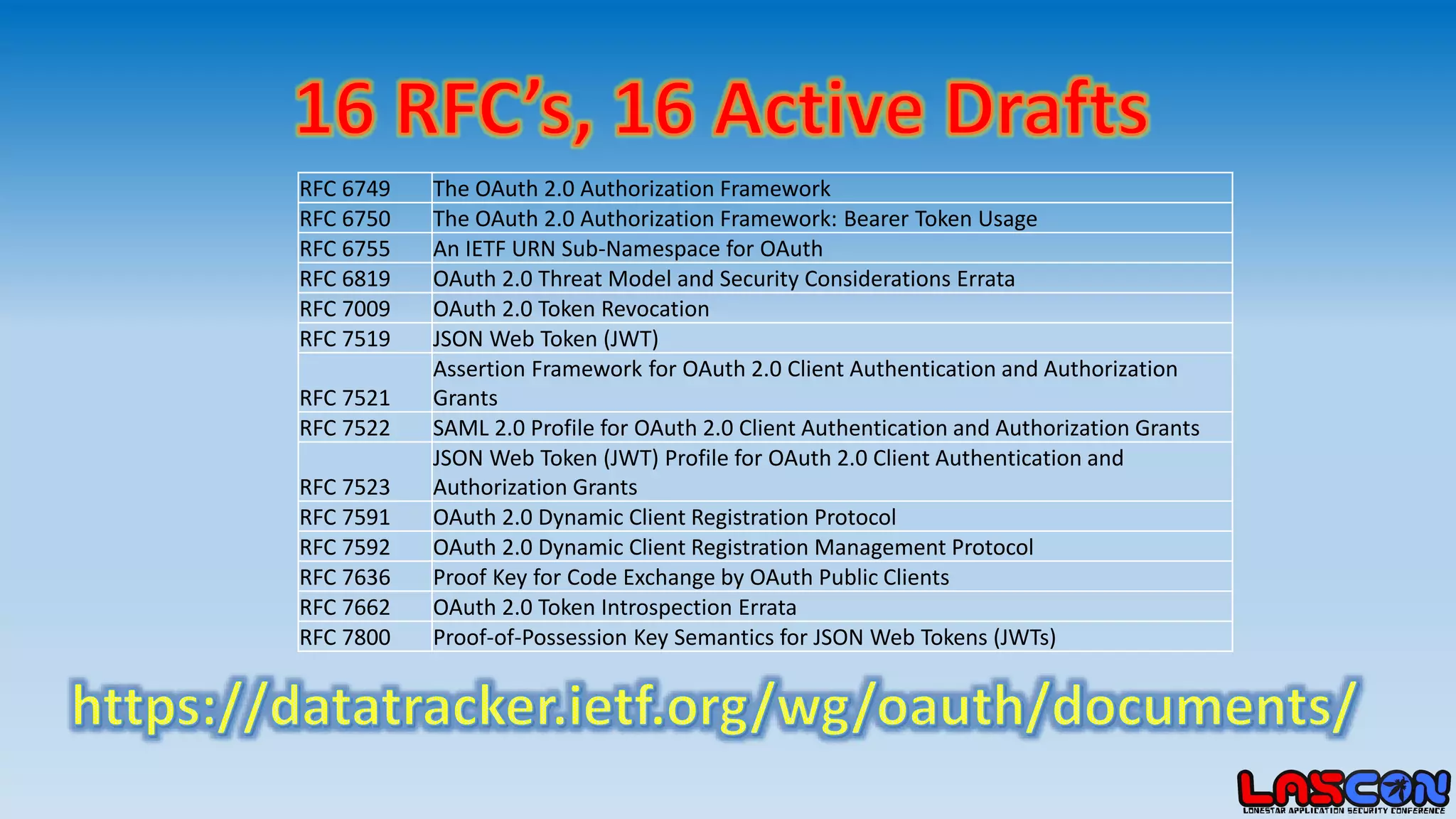
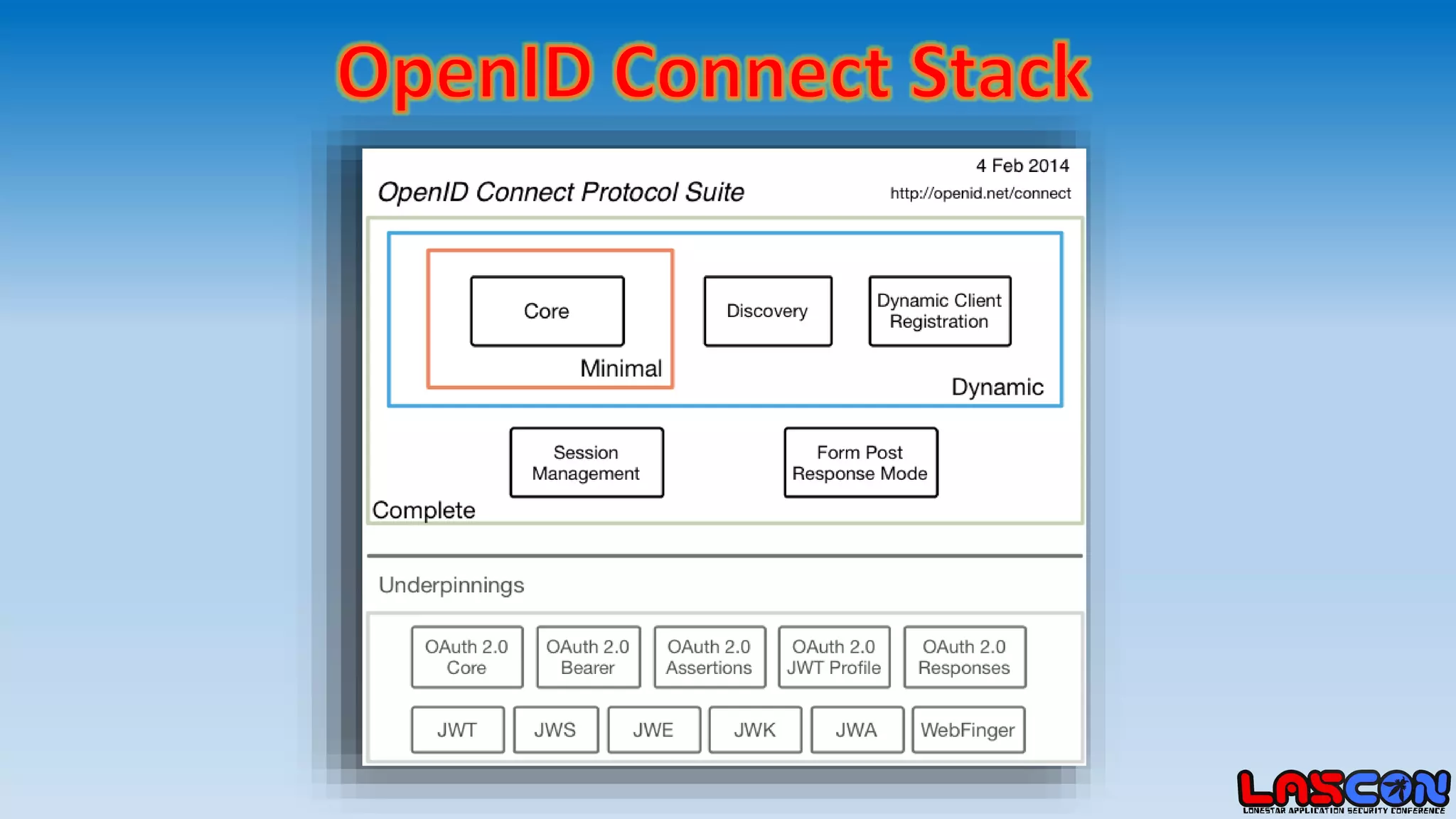
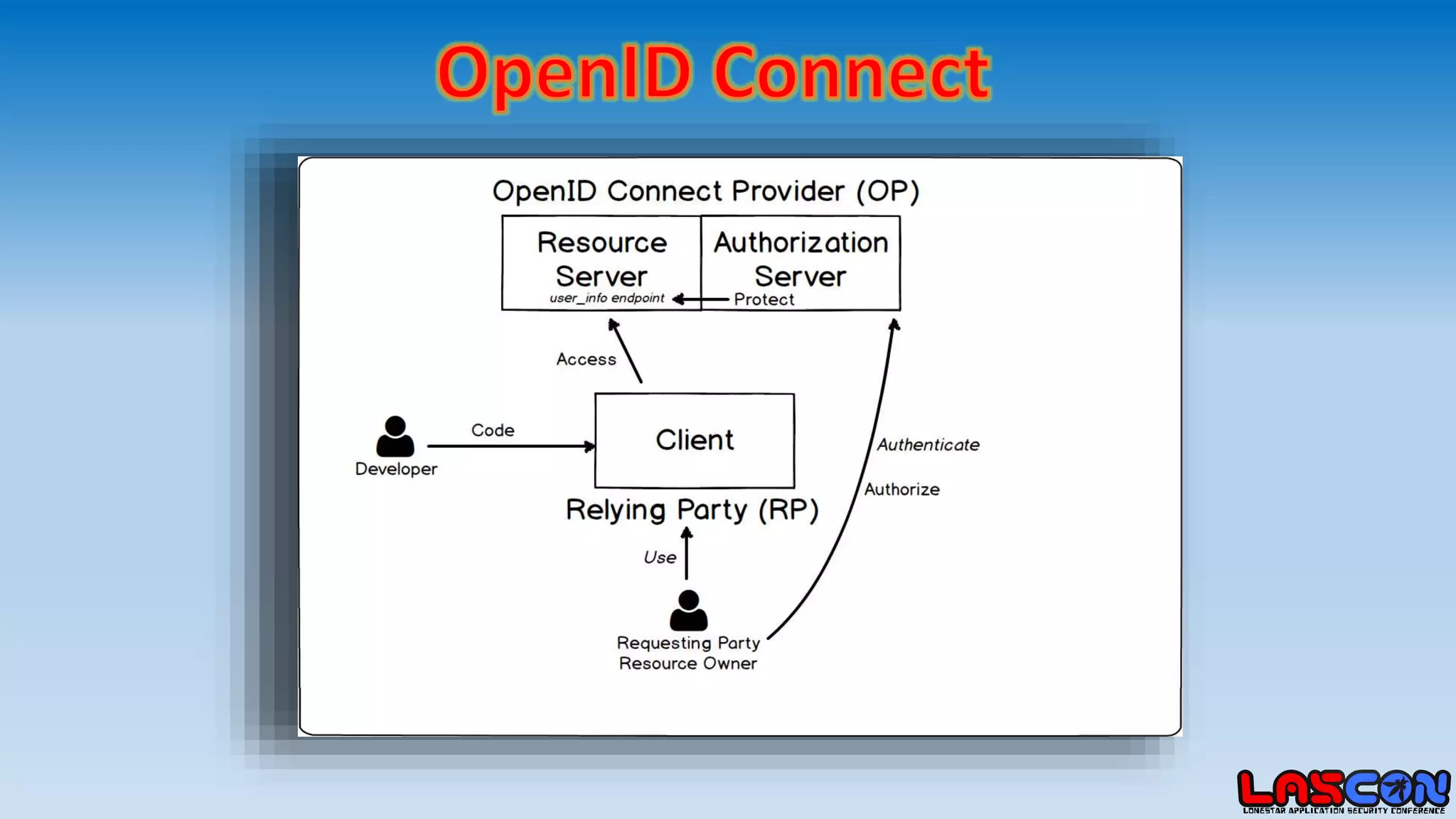
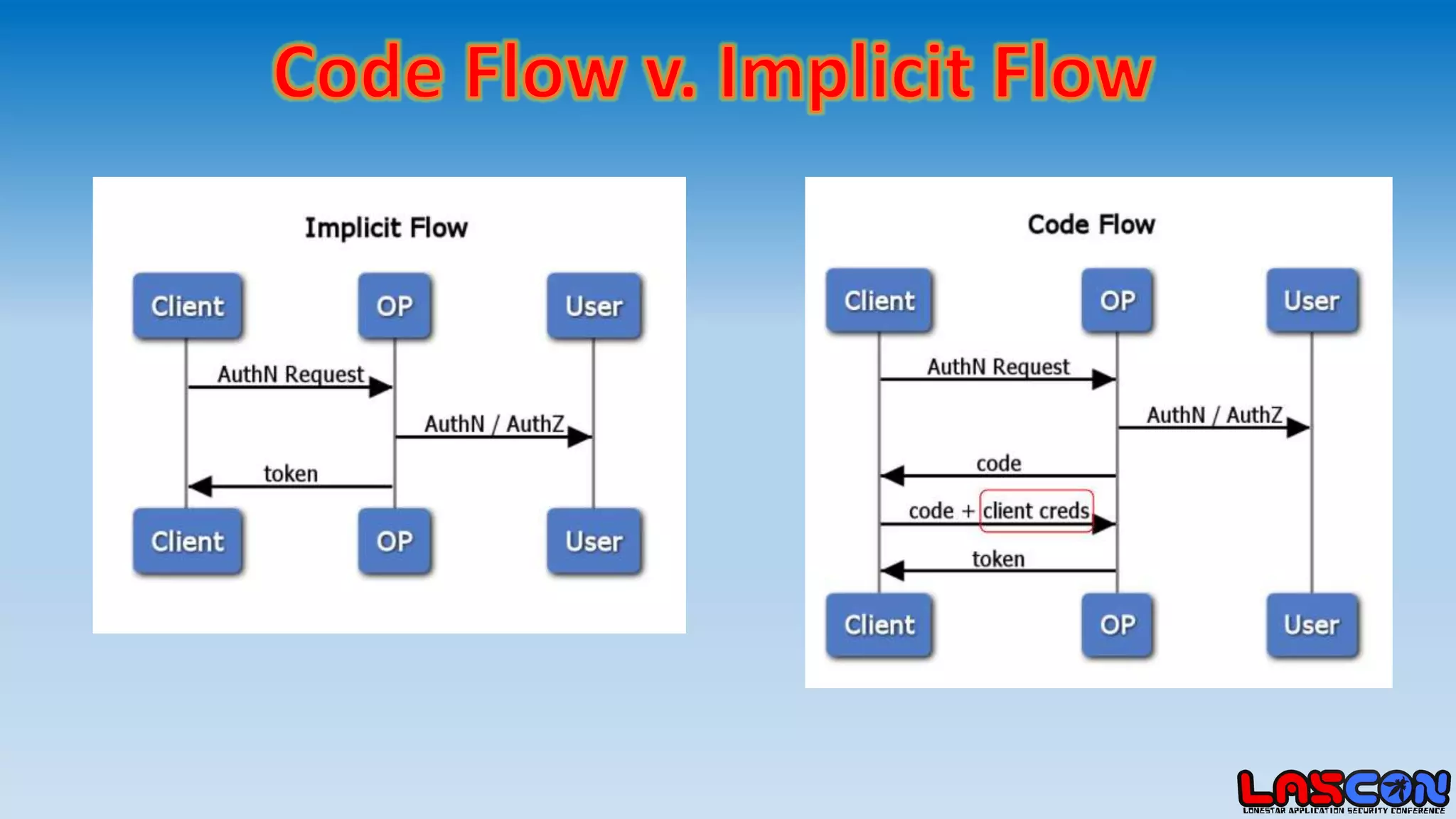
The document discusses the differences and relationships between SAML, OAuth, and OpenID Connect, highlighting key components like assertions, tokens, and identity providers. It references multiple RFCs that outline the specifications and security protocols related to OAuth 2.0 and JWTs. The content is aimed at providing a comprehensive understanding of authentication and authorization frameworks.