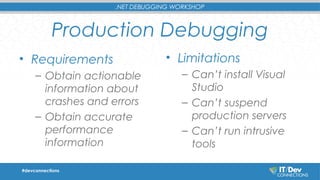
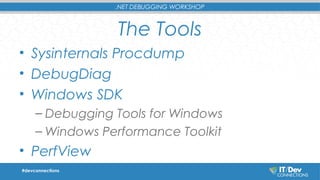
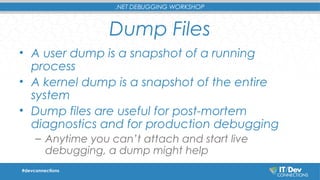
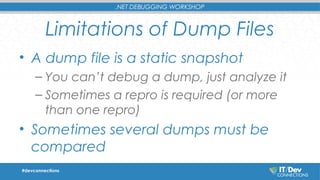
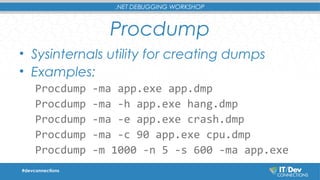
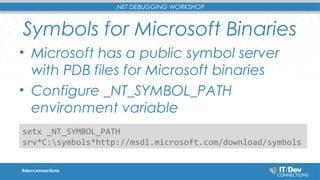
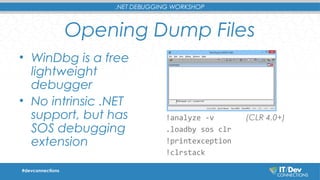
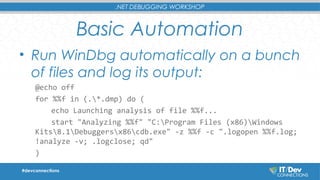
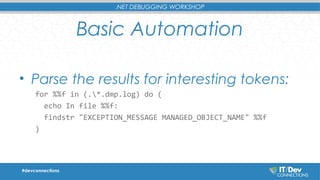
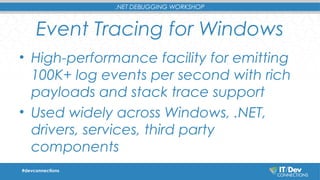
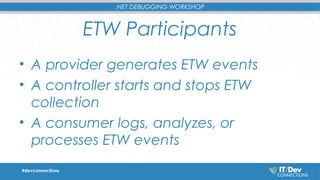
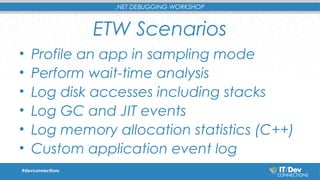
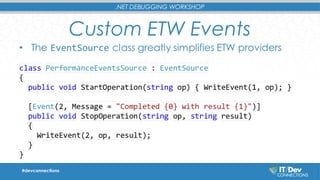
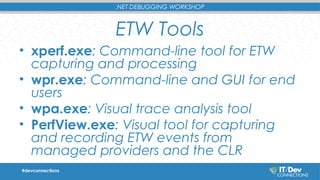
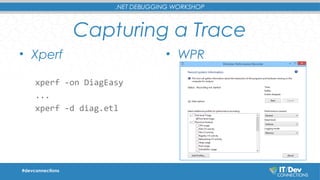
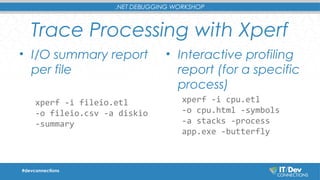
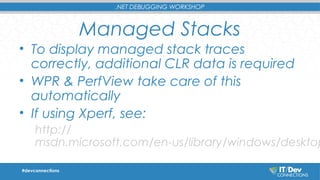
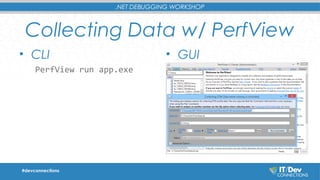
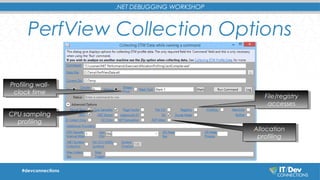
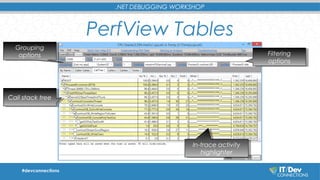
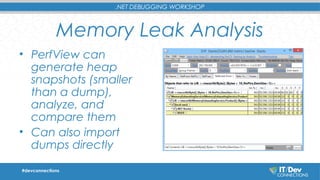
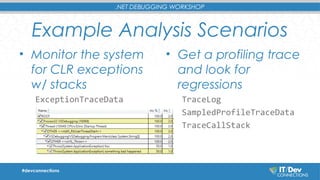
This document summarizes a workshop on .NET debugging techniques. The workshop covers debugging production issues, analyzing system and application performance, and automating debugging processes. It discusses tools like Procdump, DebugDiag, and Windows debugging tools. It also covers debugging techniques like generating dump files, using Event Tracing for Windows (ETW) to collect traces, and analyzing traces with tools like PerfView. The goal is to help integrate automatic error analysis and triage into development processes.