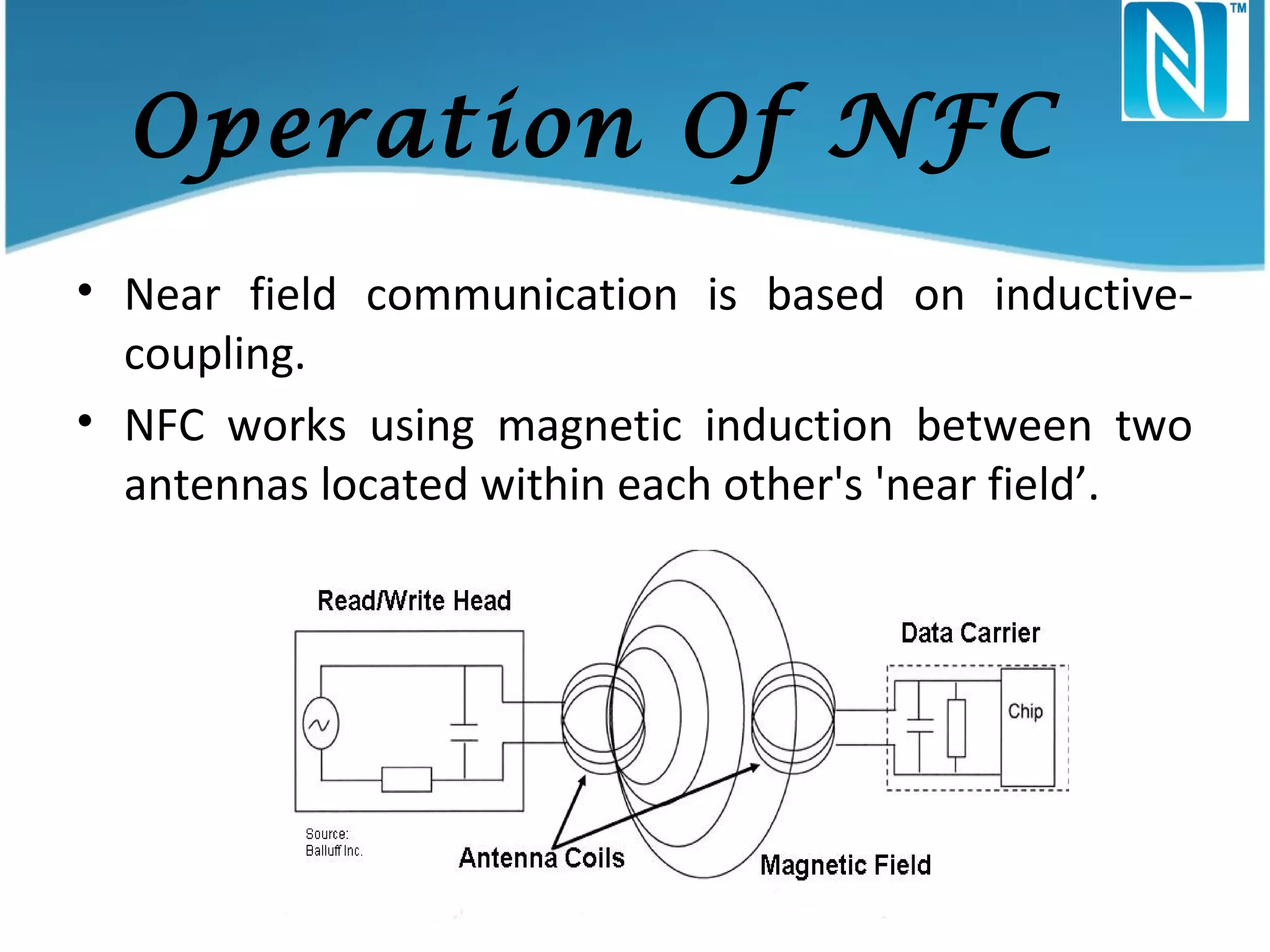
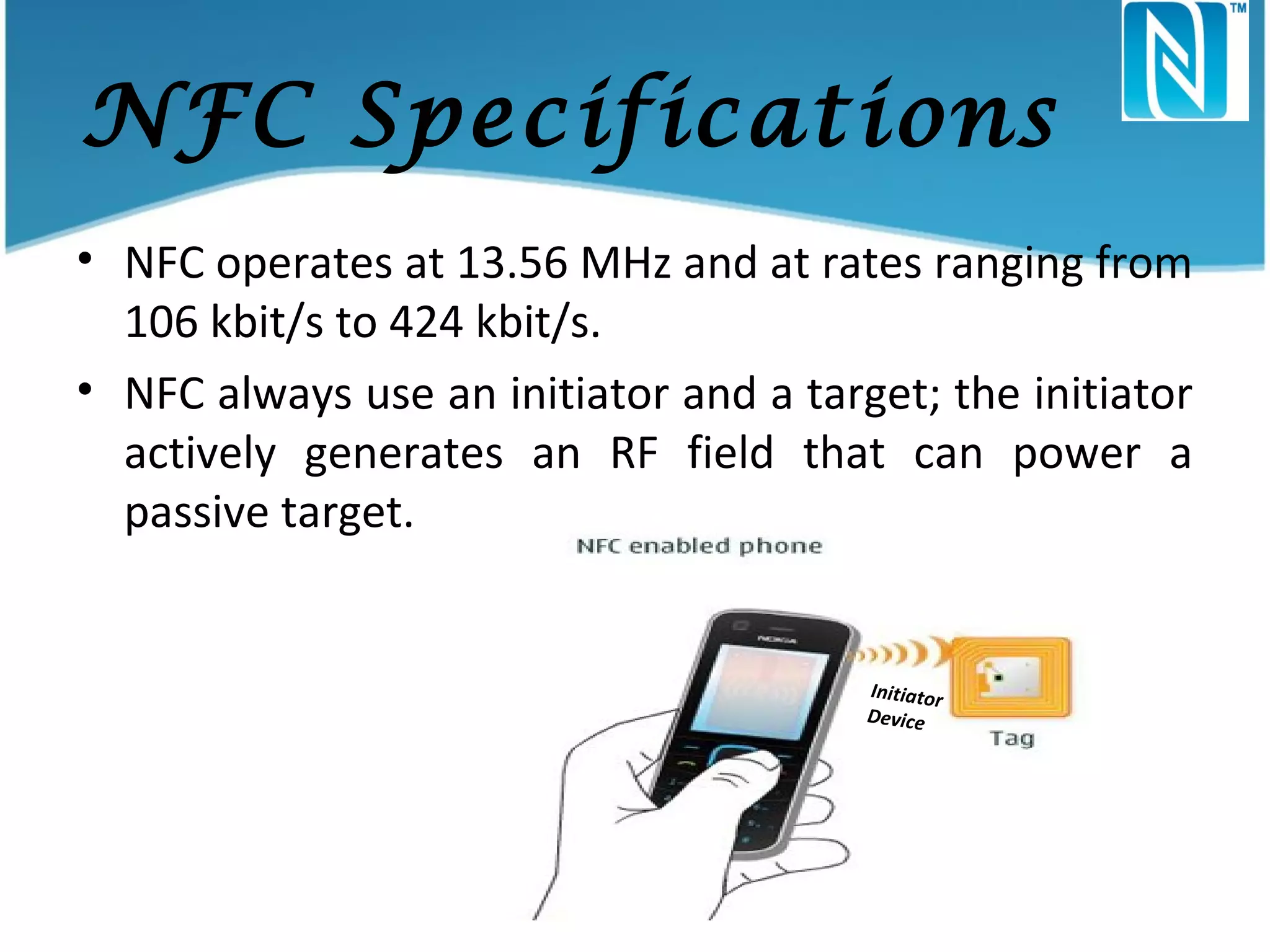
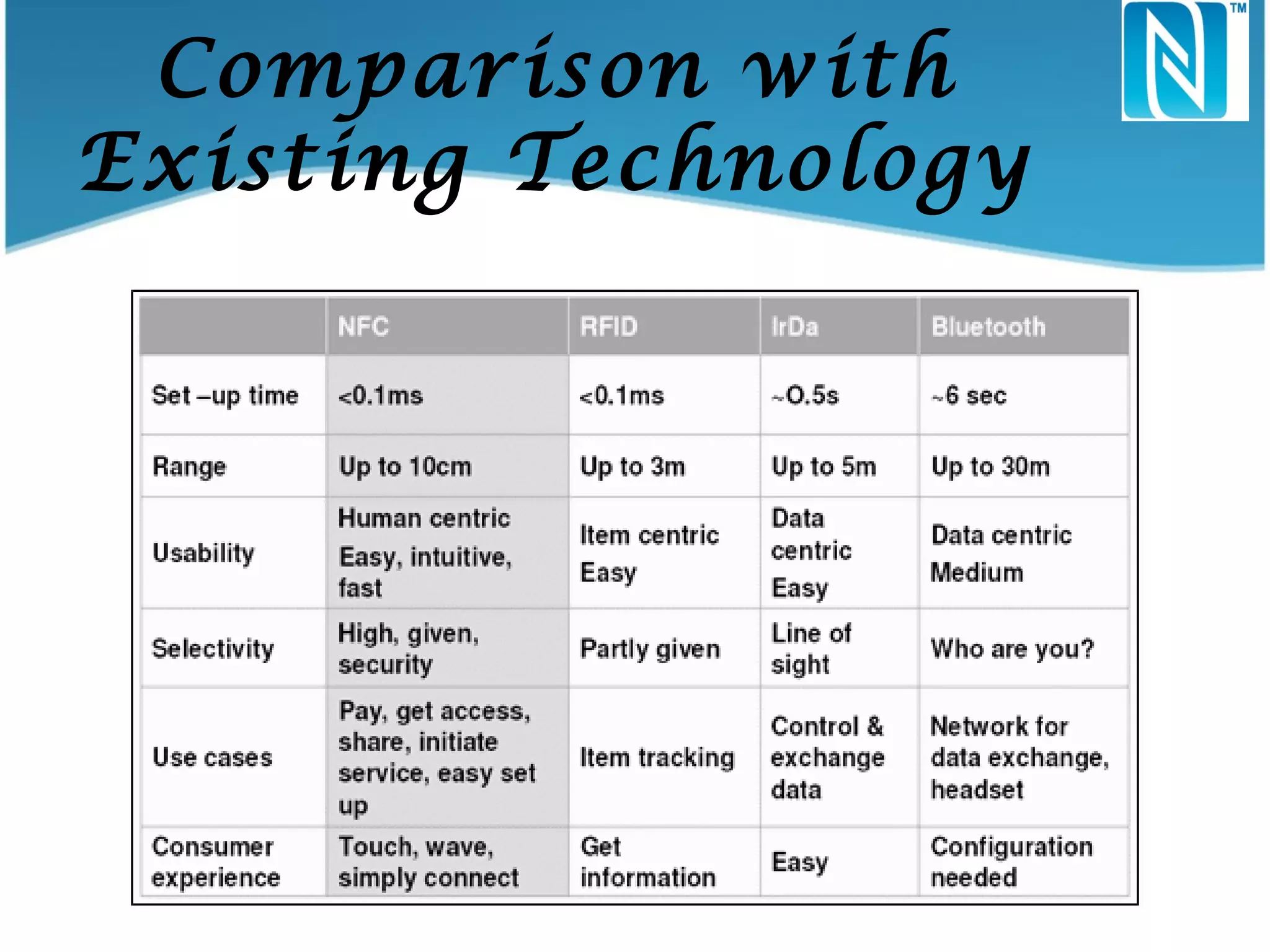
Near Field Communication (NFC) is a wireless communication technology that allows short-range data transfer between devices, primarily designed for mobile and handheld devices. Developed by Philips and Sony in 2002, NFC operates based on RFID principles and has various applications including mobile payments, access control, and peer-to-peer data exchange. Advantages of NFC include convenience and secure communication, though it is limited by short operational range and slower data transfer rates.