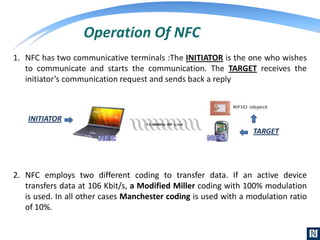
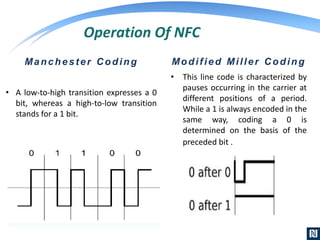
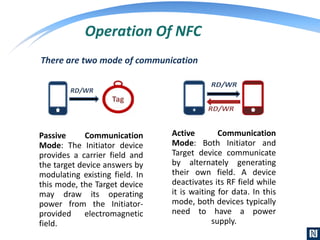
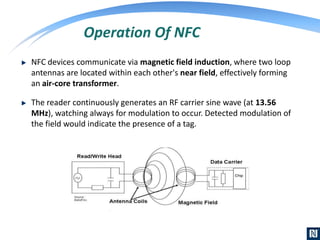
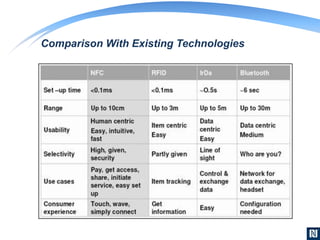
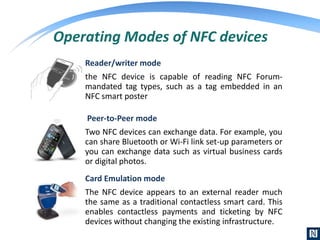
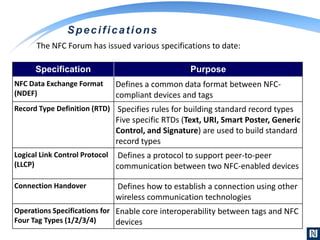
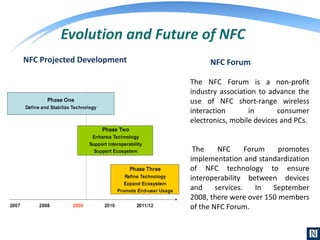
NFC, or Near Field Communication, is a short-range wireless communication technology that allows data exchange between devices when they are touched or brought within close proximity of each other. It operates at 13.56 MHz and has a maximum range of about 10 cm. NFC uses magnetic field induction to enable communication between two devices. One device must have an NFC reader/writer while the other contains an NFC tag. Common applications of NFC include contactless payments, data sharing, and connection handovers to establish wireless links between devices. The technology is standardized by the NFC Forum and is seeing increasing adoption in smartphones and other mobile devices.