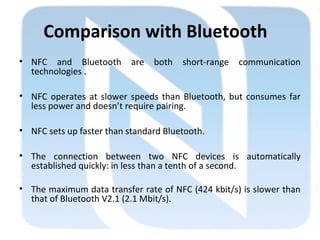
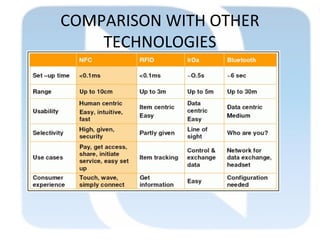
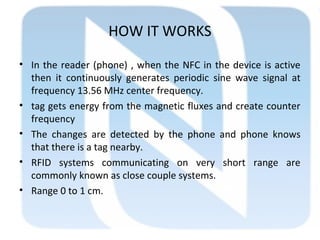
Near field communication (NFC) allows short-range wireless data exchange between devices when they are brought within close proximity of a few centimeters. It has applications in contactless payments, data sharing, and connecting devices like pairing Bluetooth headsets. NFC operates at 13.56 MHz and supports data transfer rates up to 424 Kbit/s. It provides advantages over RFID and Bluetooth through faster setup and lower power consumption. Common uses of NFC include mobile payments, social networking, smartphone automation through NFC tags, and data sharing through technologies like Android Beam. The future of NFC may include uses in vehicle ignition, electronic ticketing, mobile commerce, and health monitoring.


![Comparison with RFID technology
• Basically, the technologies Radio Frequency
Identification and Near Field Communication use the
same working standards.
• However, the essential extension of RFID is the
communication mode between two active devices.
• In addition to contactless smart cards (ISO 14443
[7]), which only support communication between
powered devices and passive tags, NFC also provides
peer-to-peer communication](https://image.slidesharecdn.com/seminarnfc-140513114959-phpapp02/85/NFC-TECHNOLOGY-14-320.jpg)