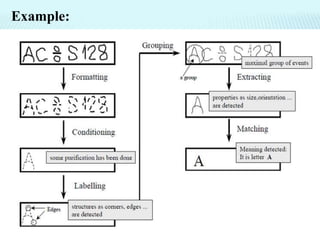
The document outlines the key steps involved in image recognition:
1. Capturing an image digitally and representing it as pixels.
2. Conditioning the image by suppressing unwanted variations to highlight important patterns.
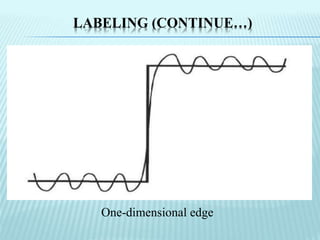
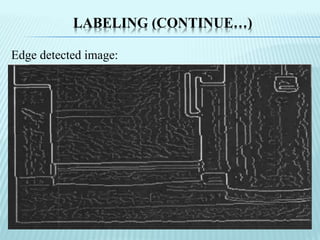
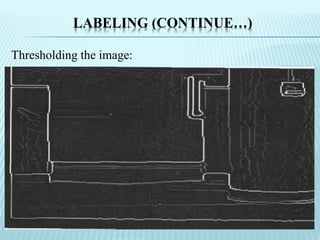
3. Labeling important patterns by detecting edges and applying thresholding to identify significant edges.
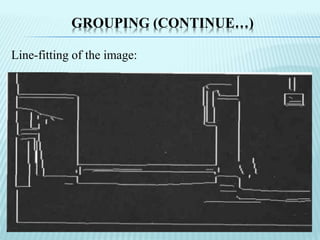
4. Grouping edges into lines and objects and extracting features like centroids to represent the image logically.
5. Matching objects in the image to stored models to recognize and identify the objects.