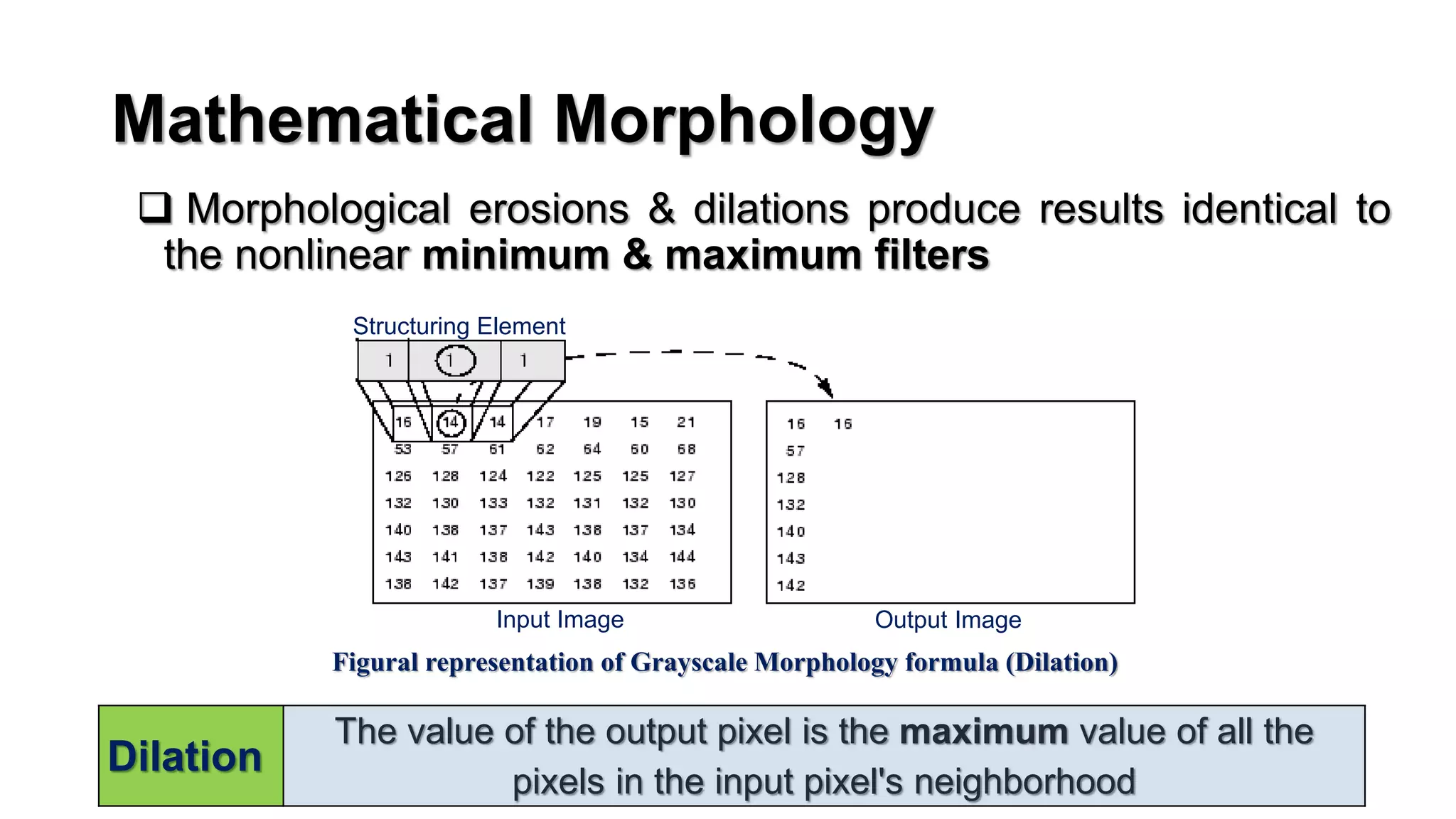
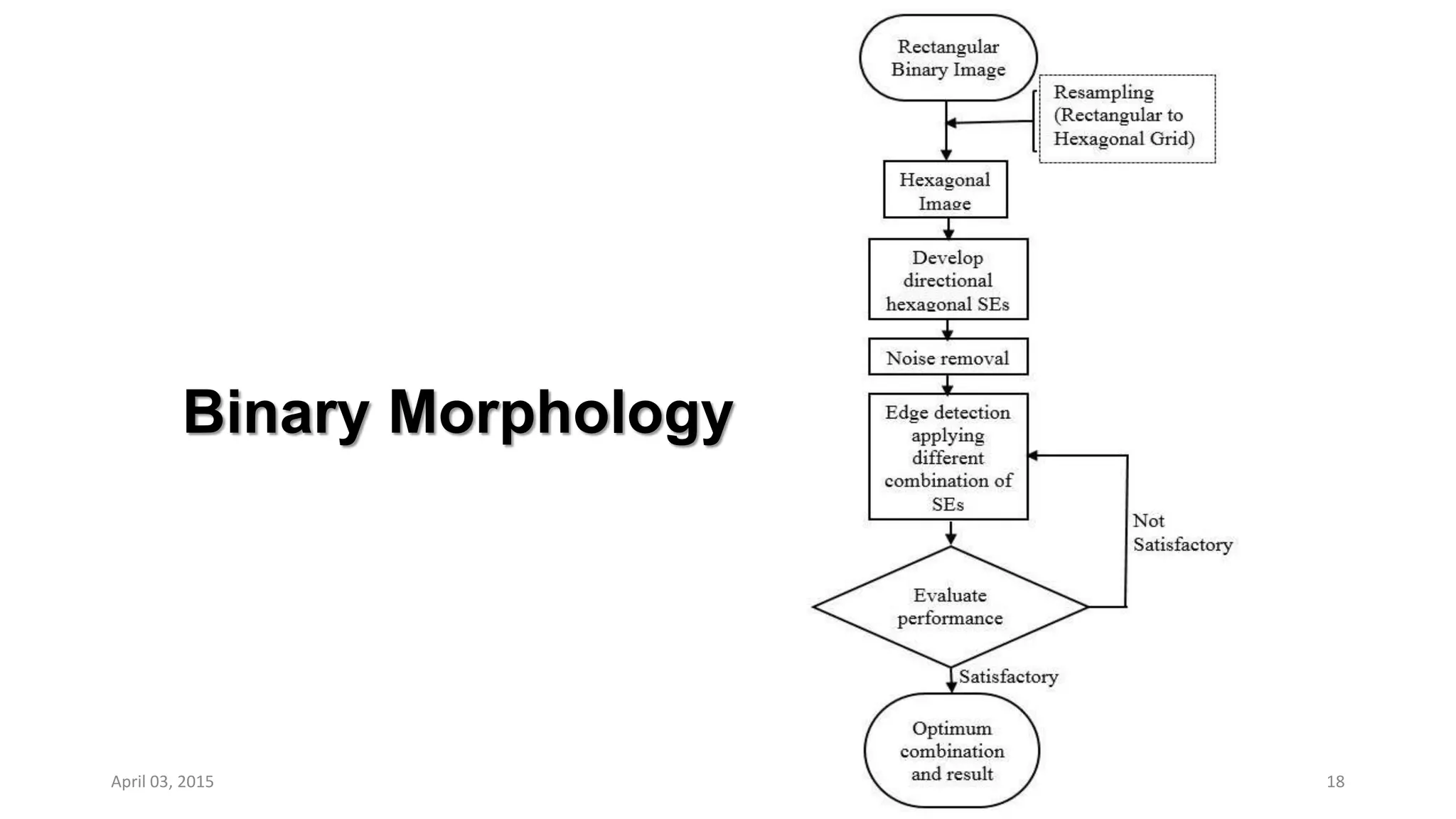
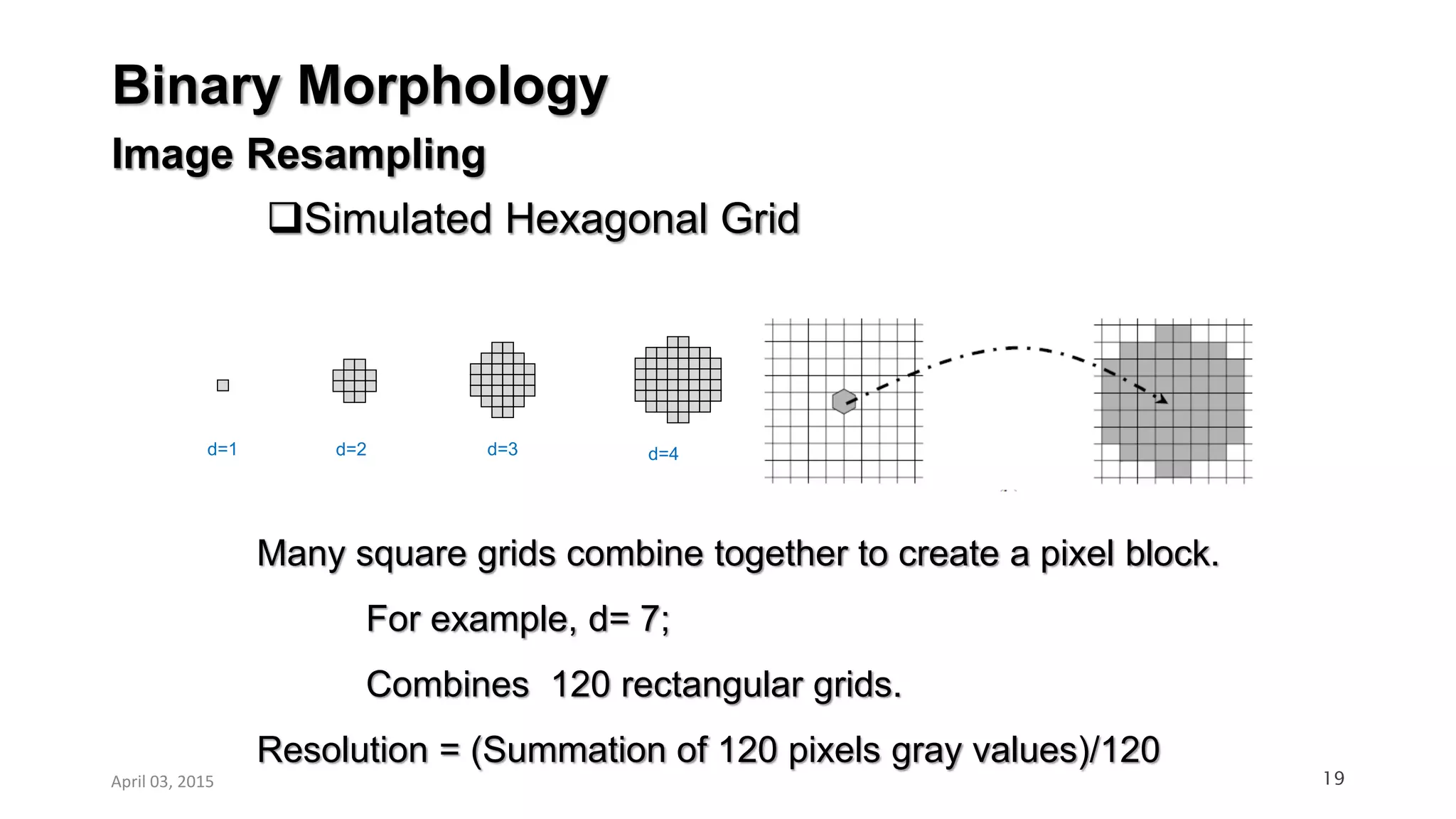
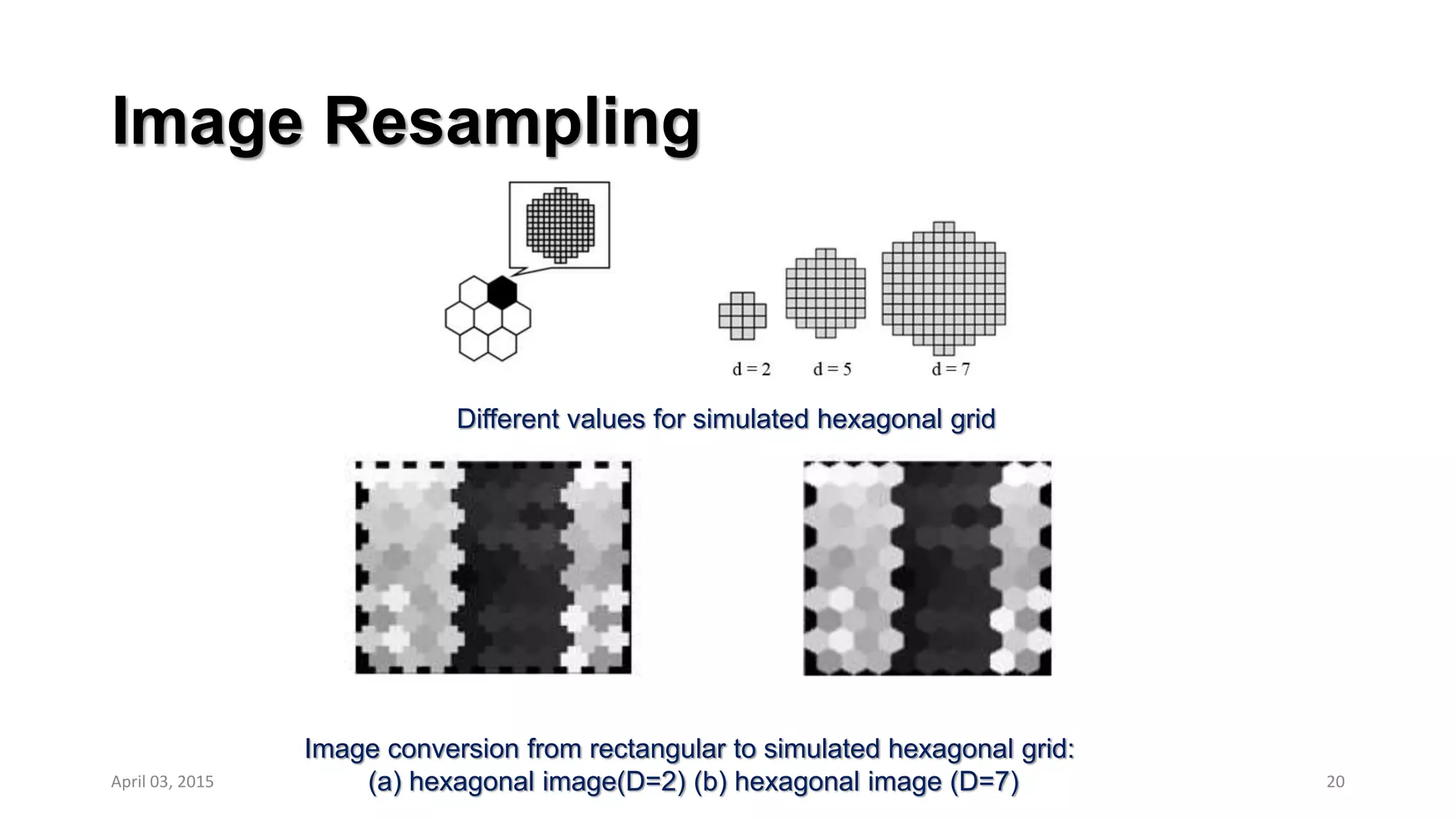
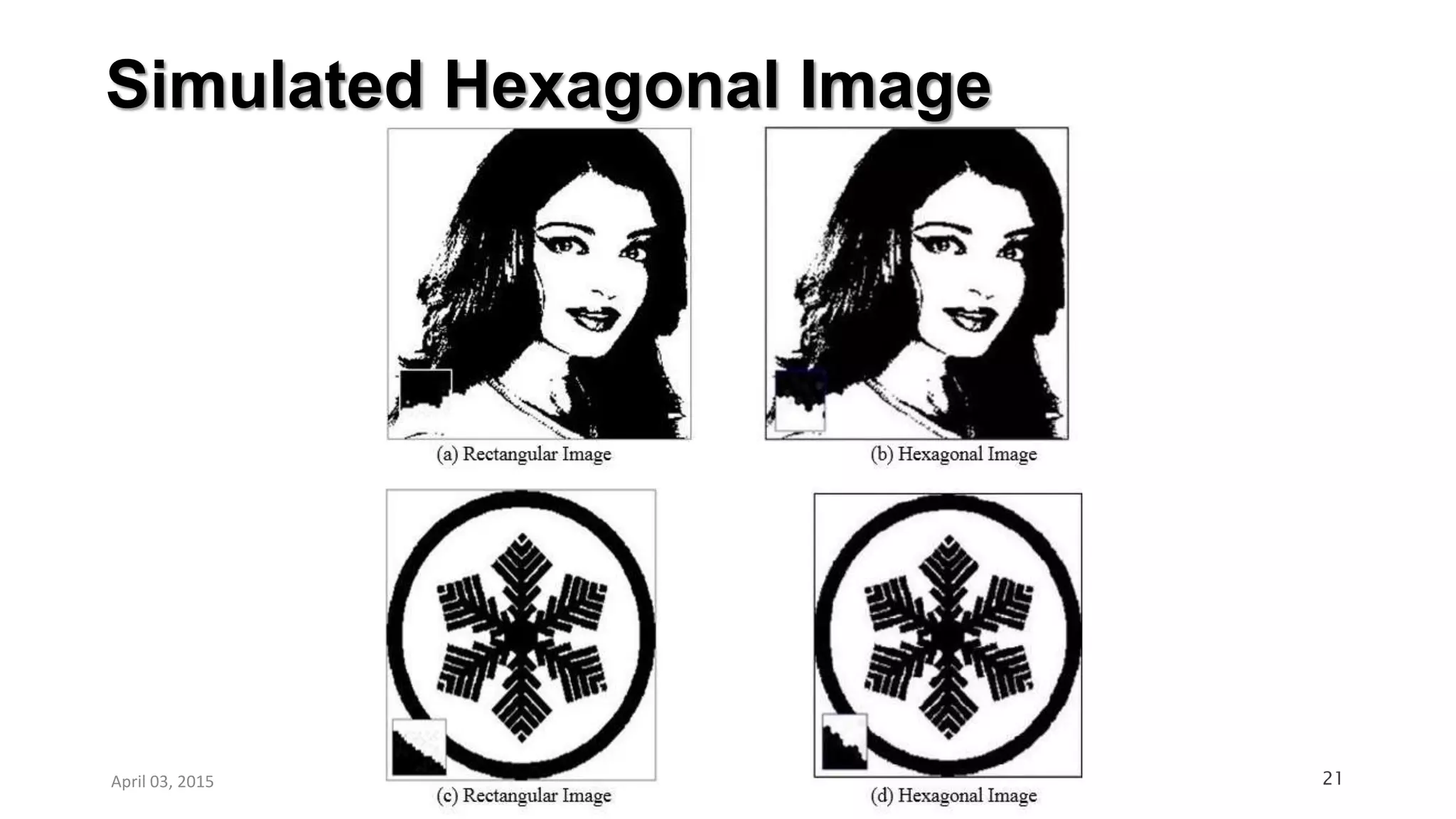
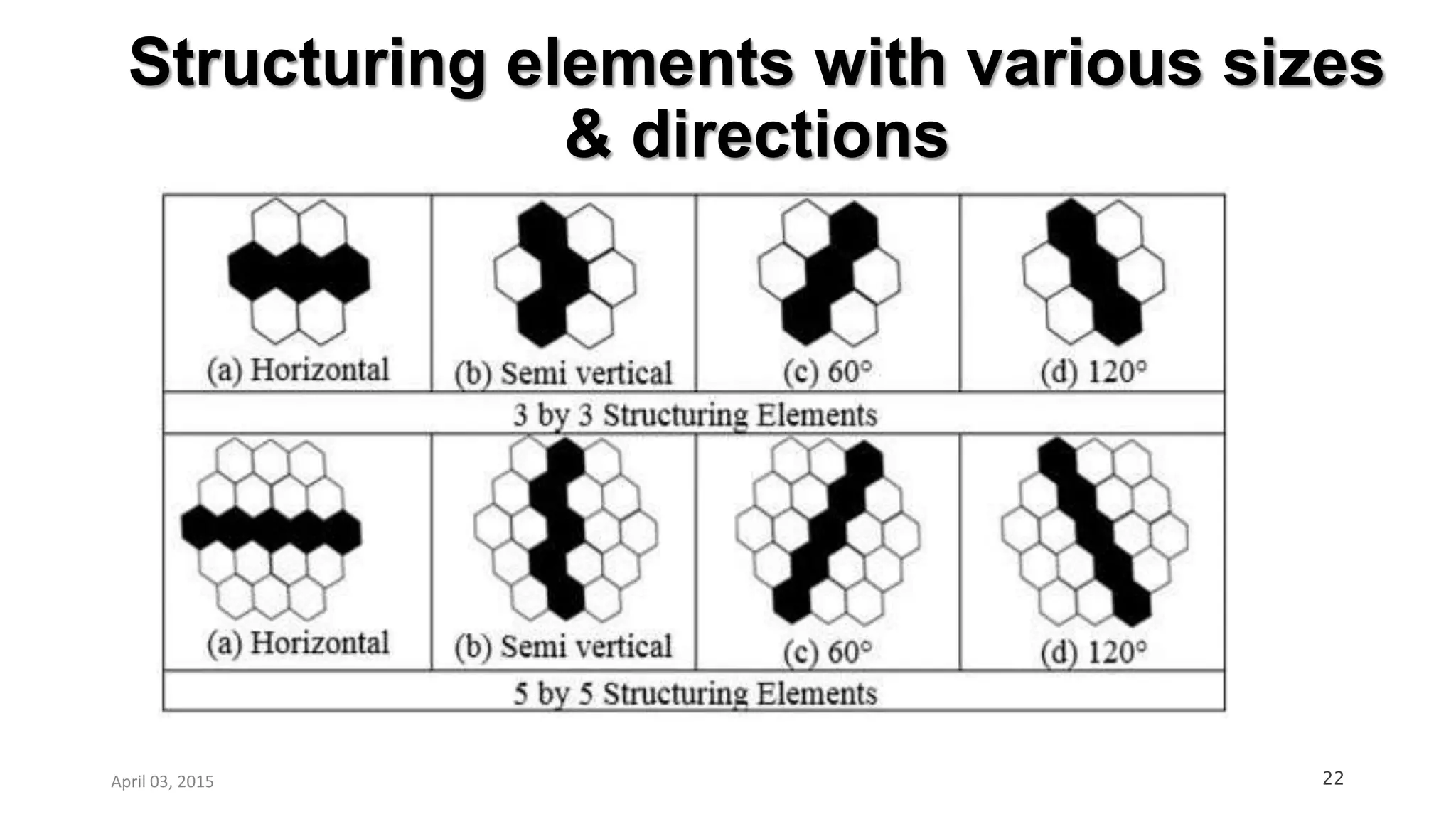
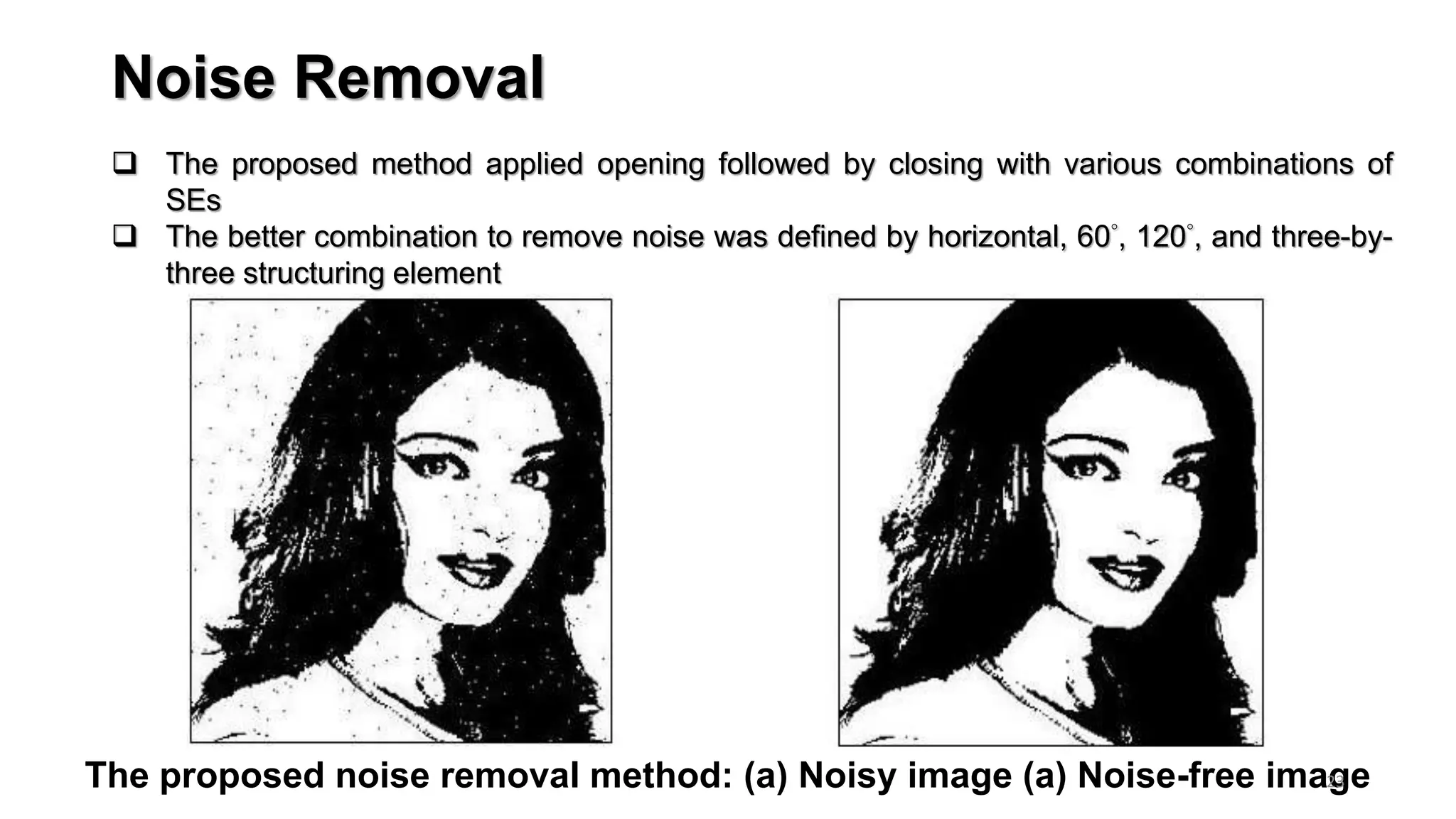
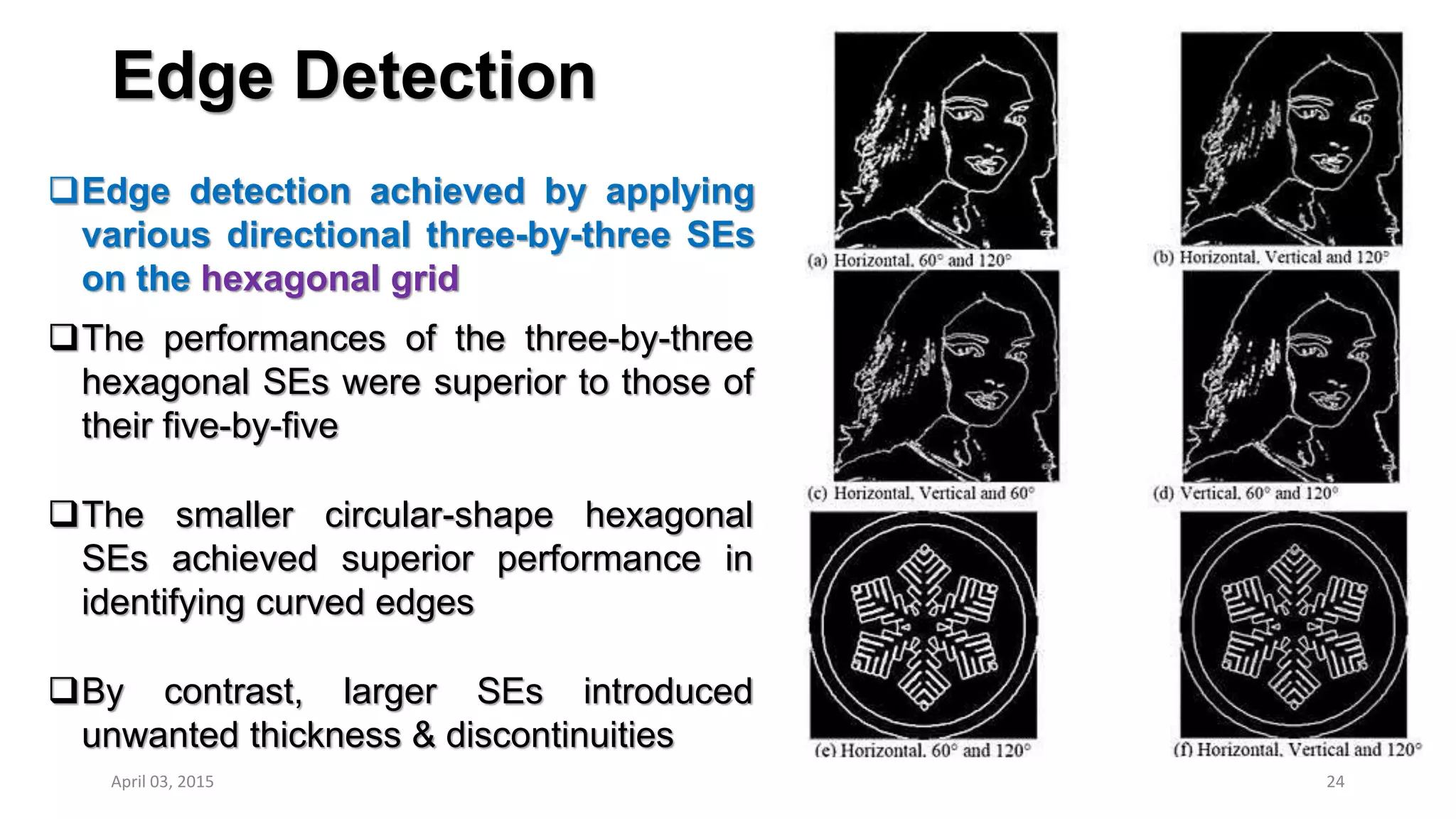
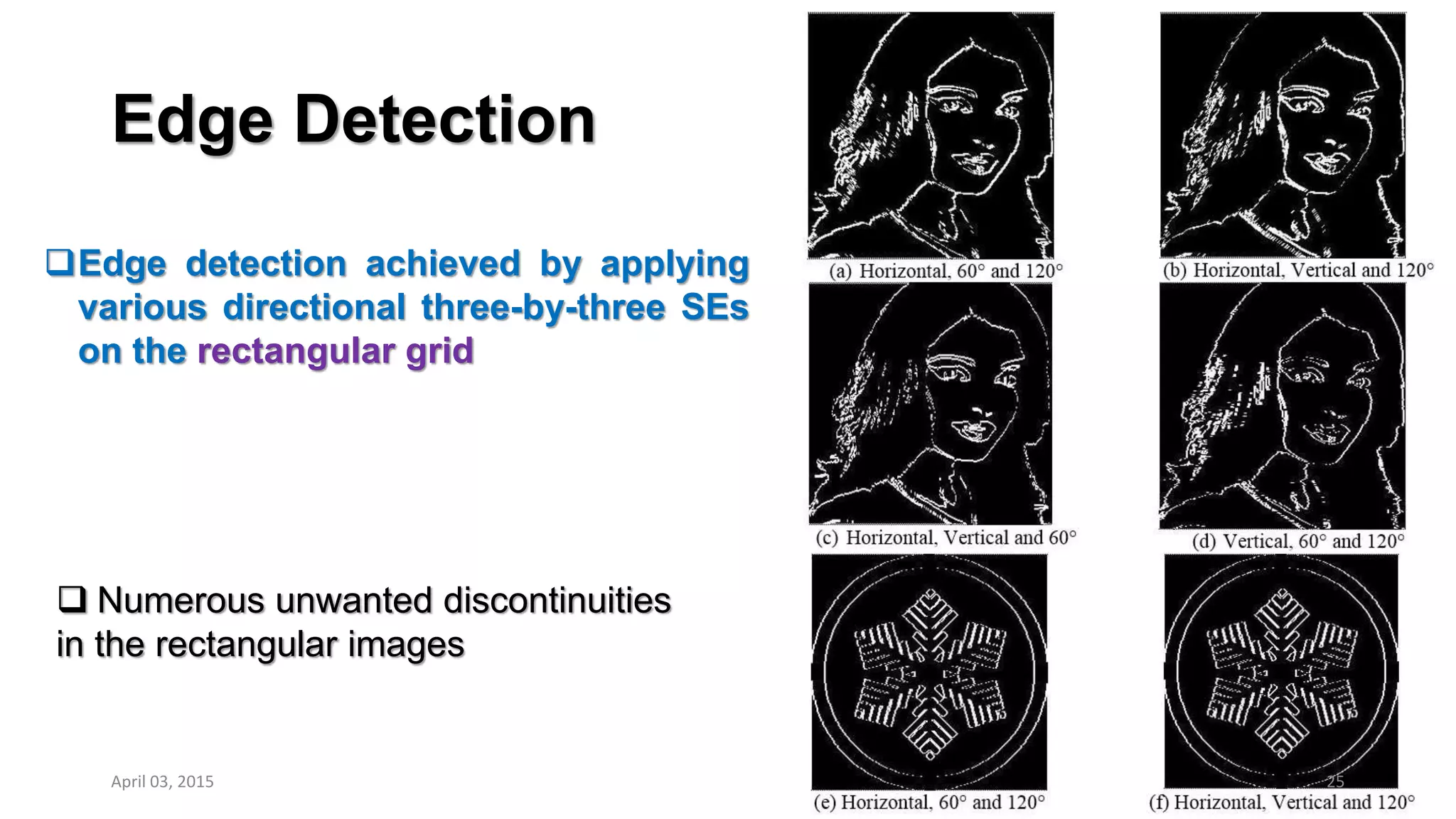
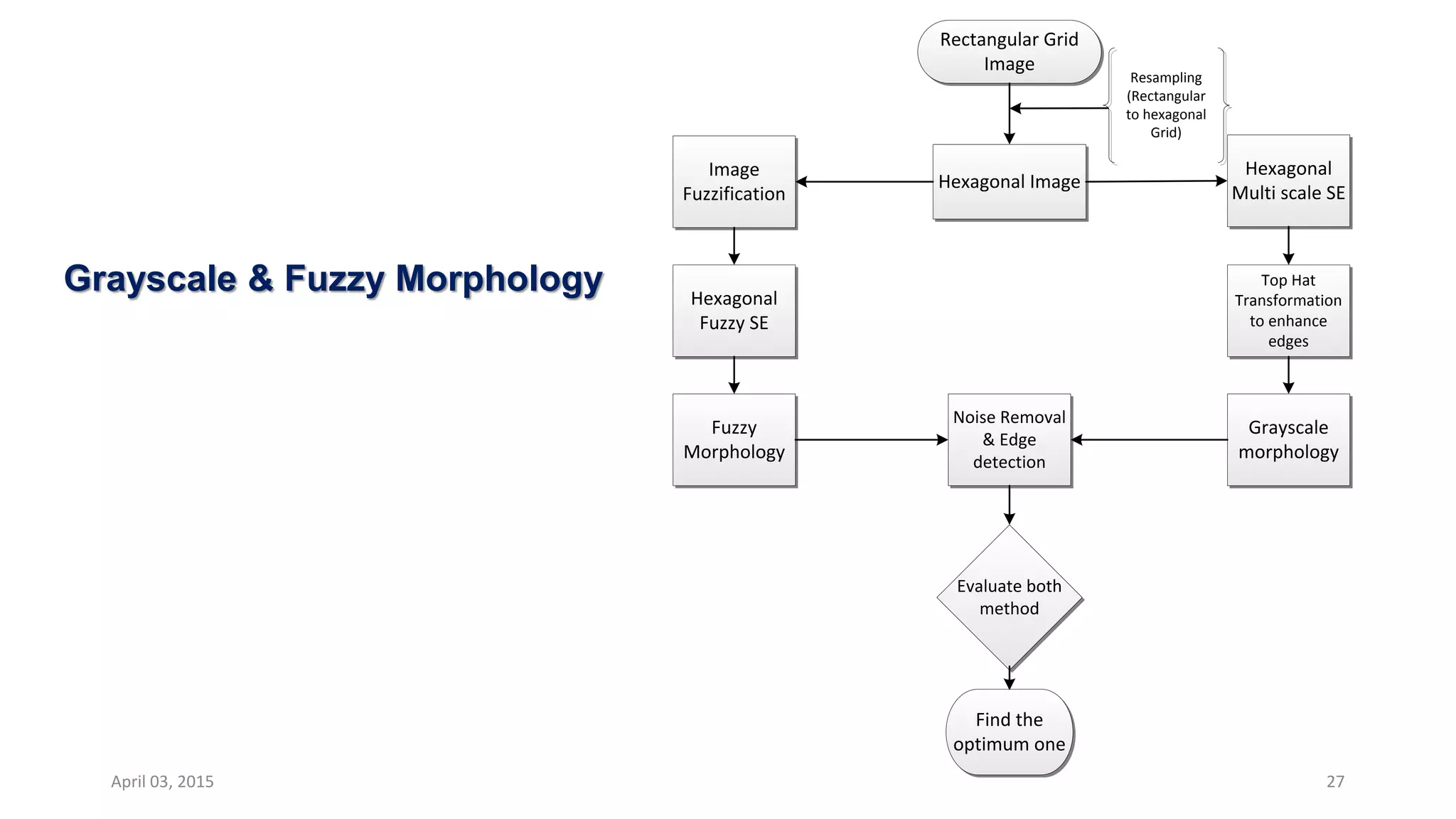
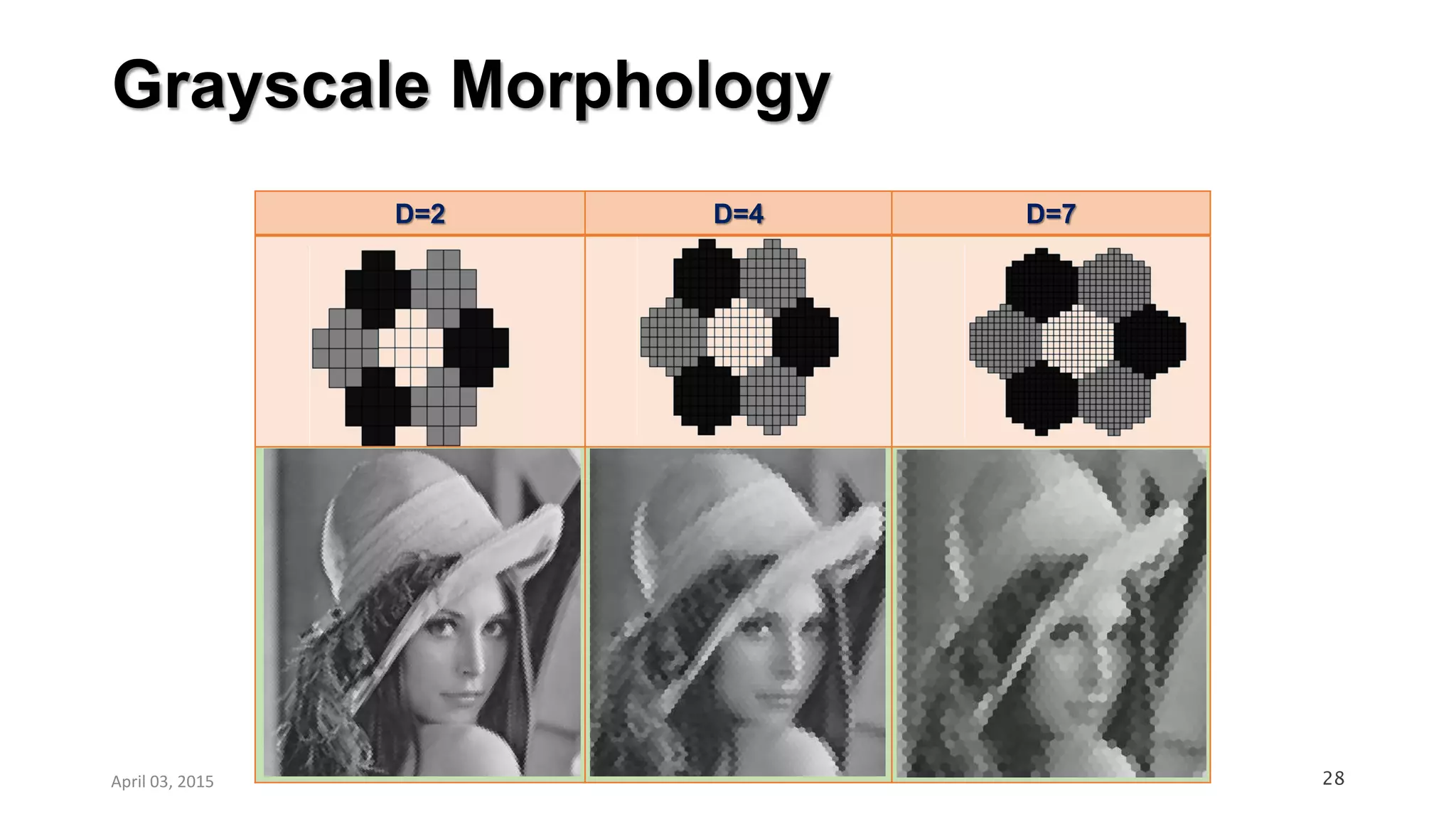
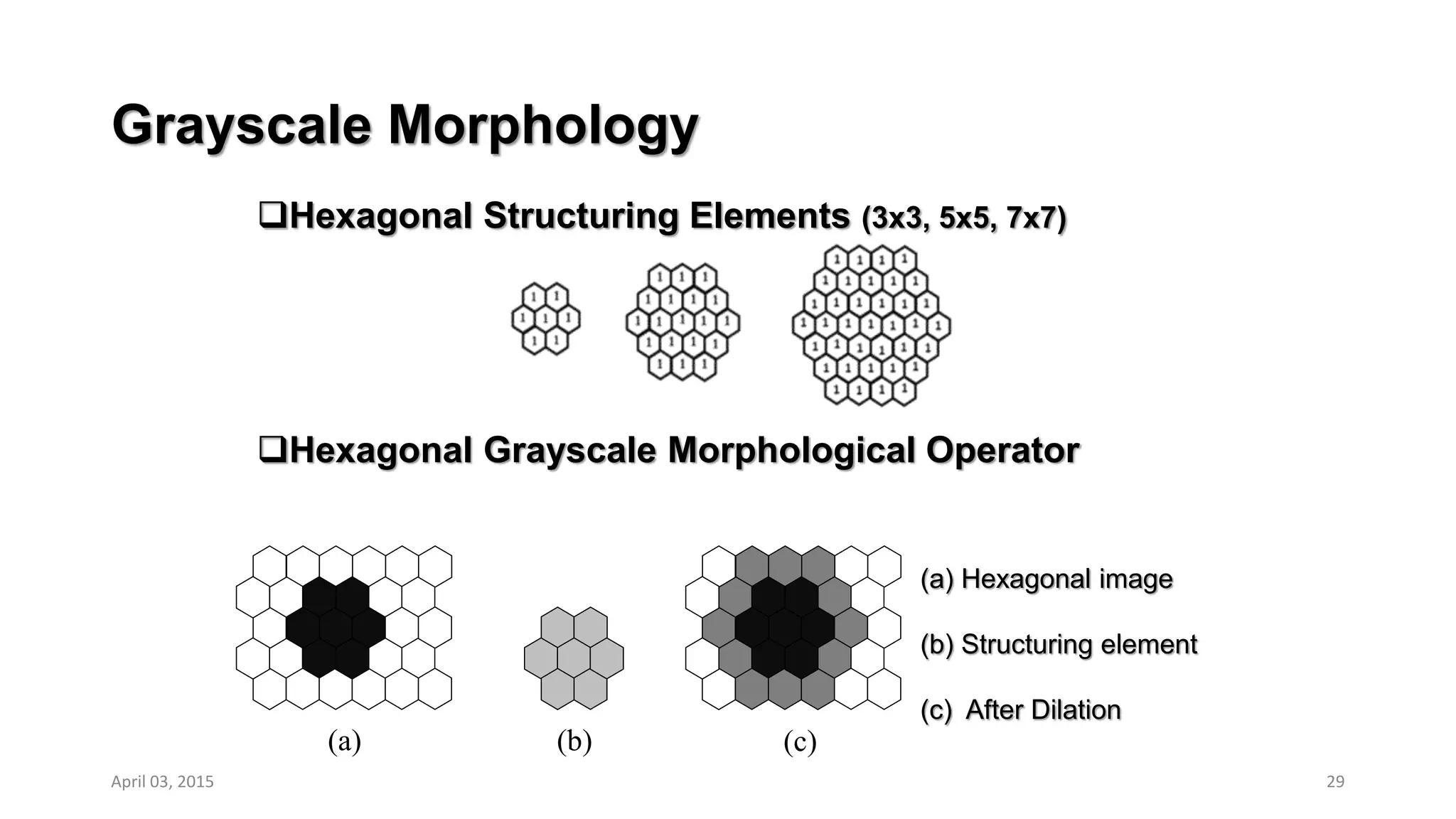
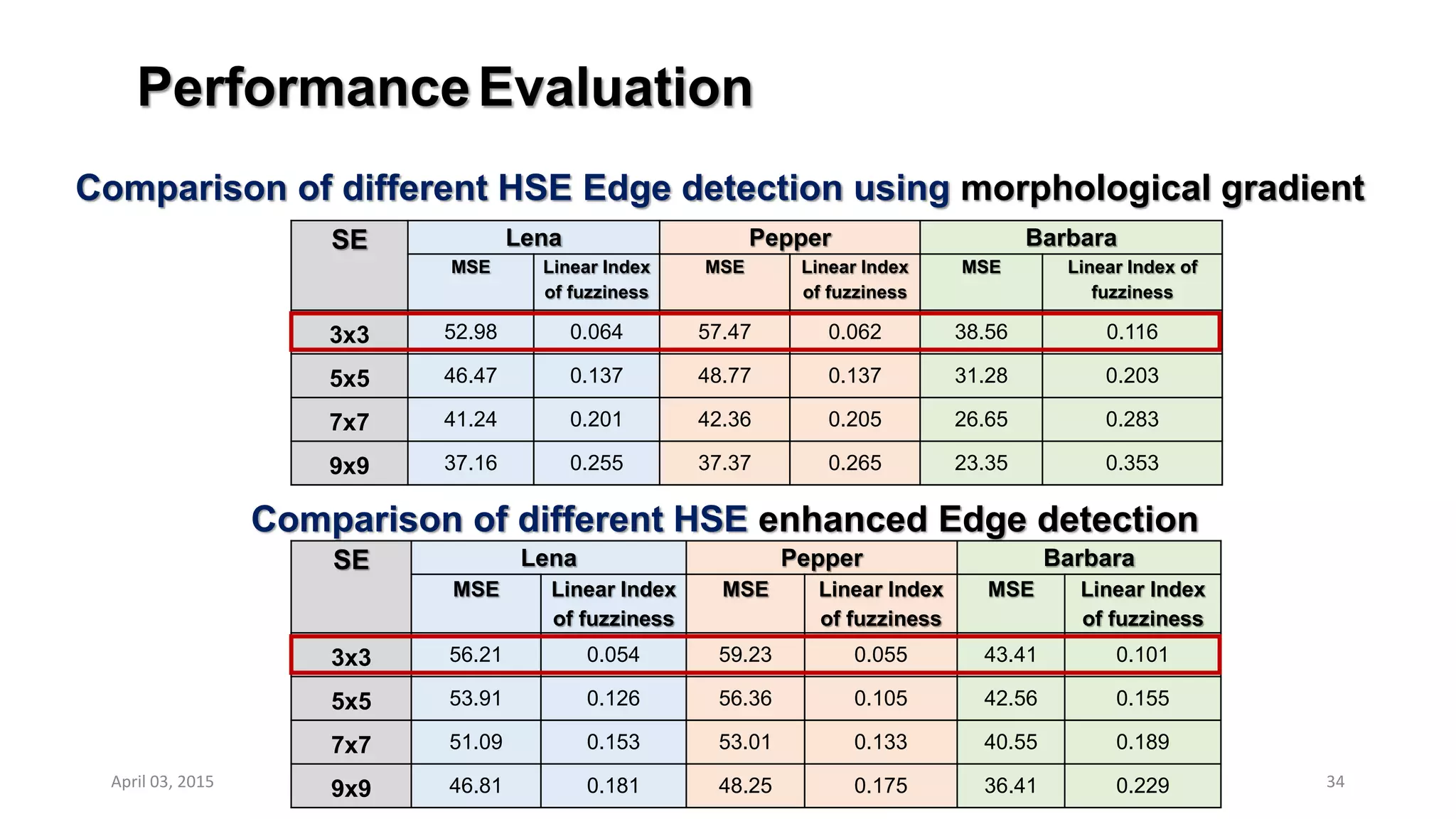
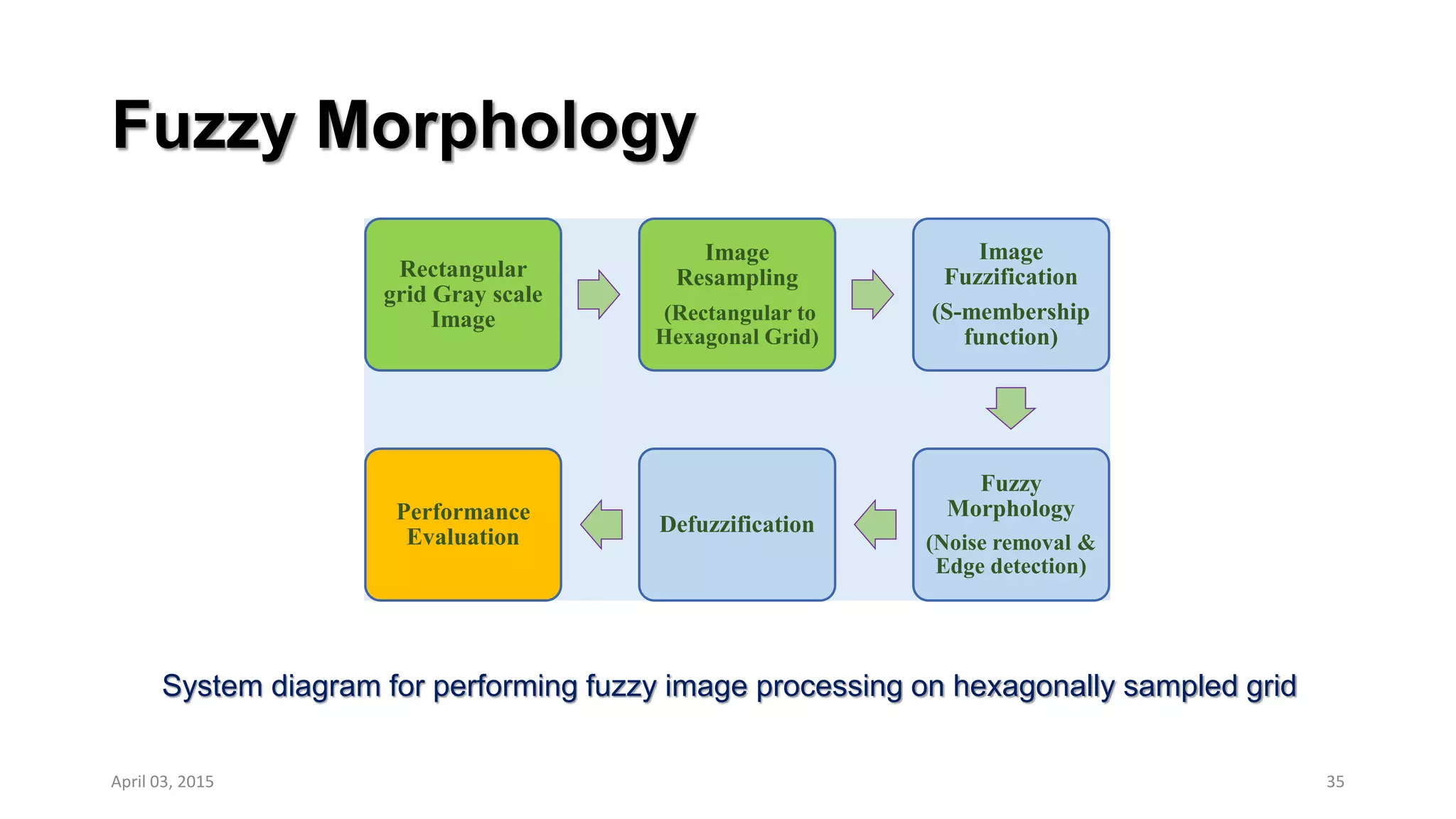
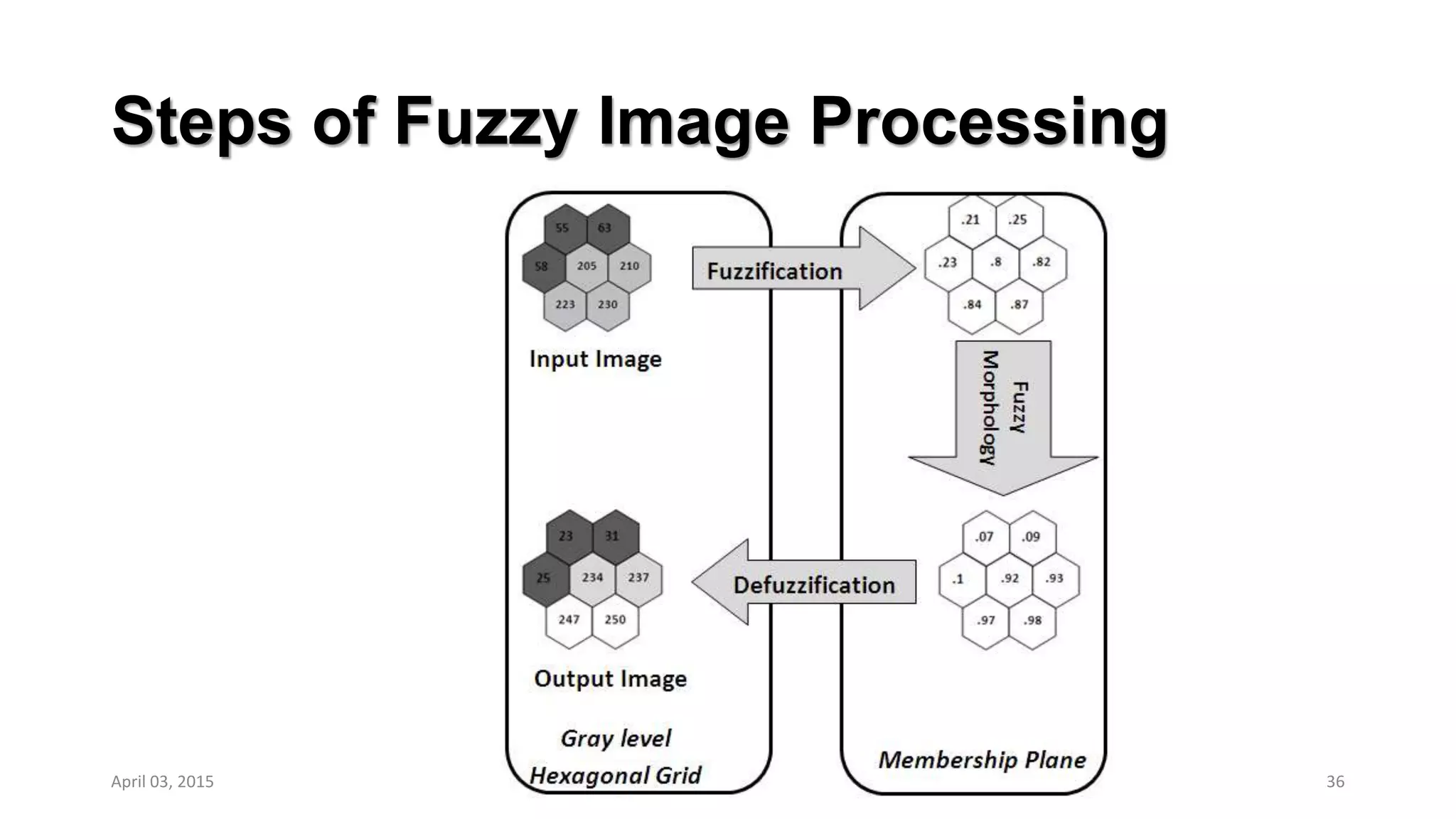
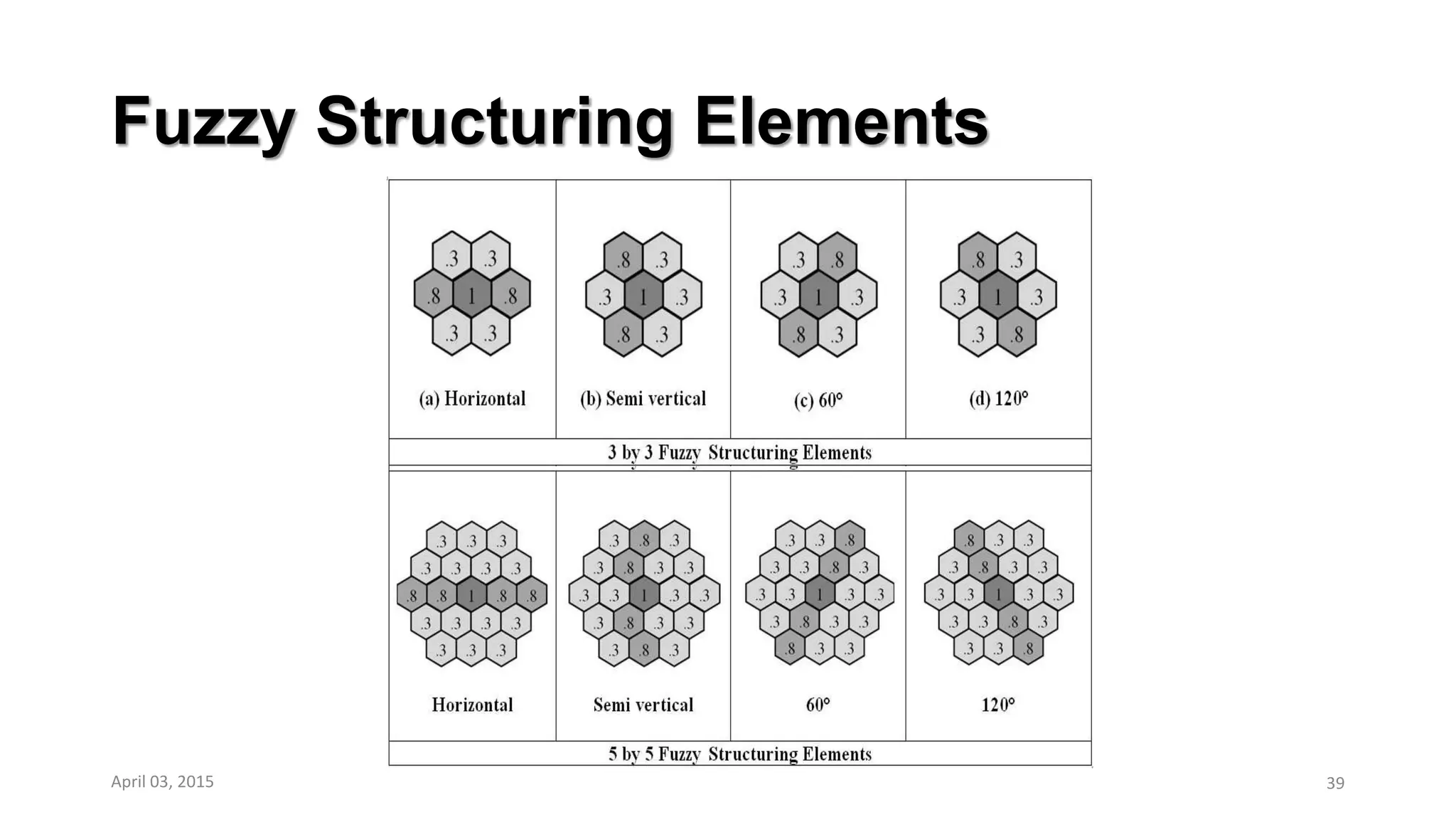
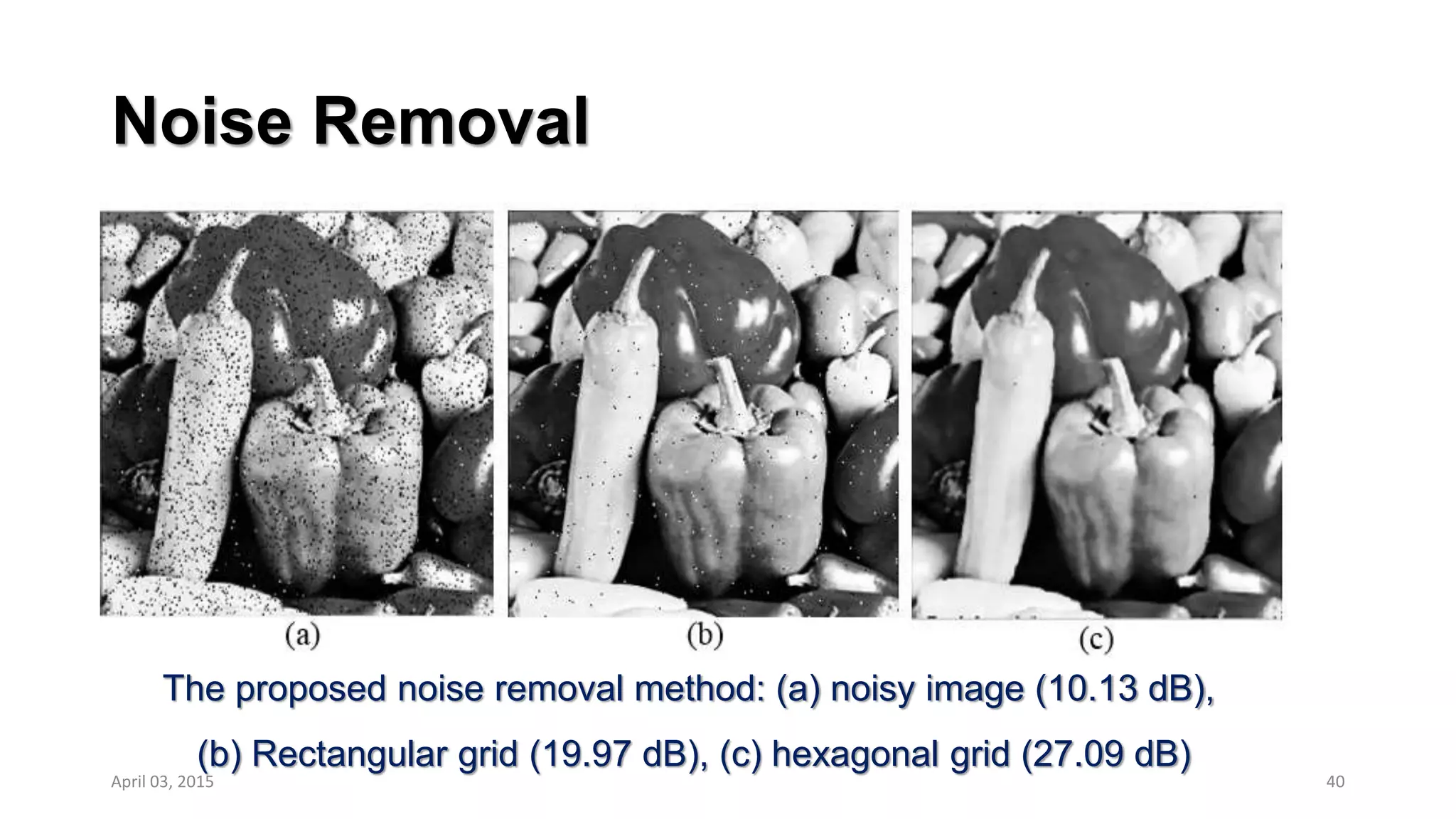
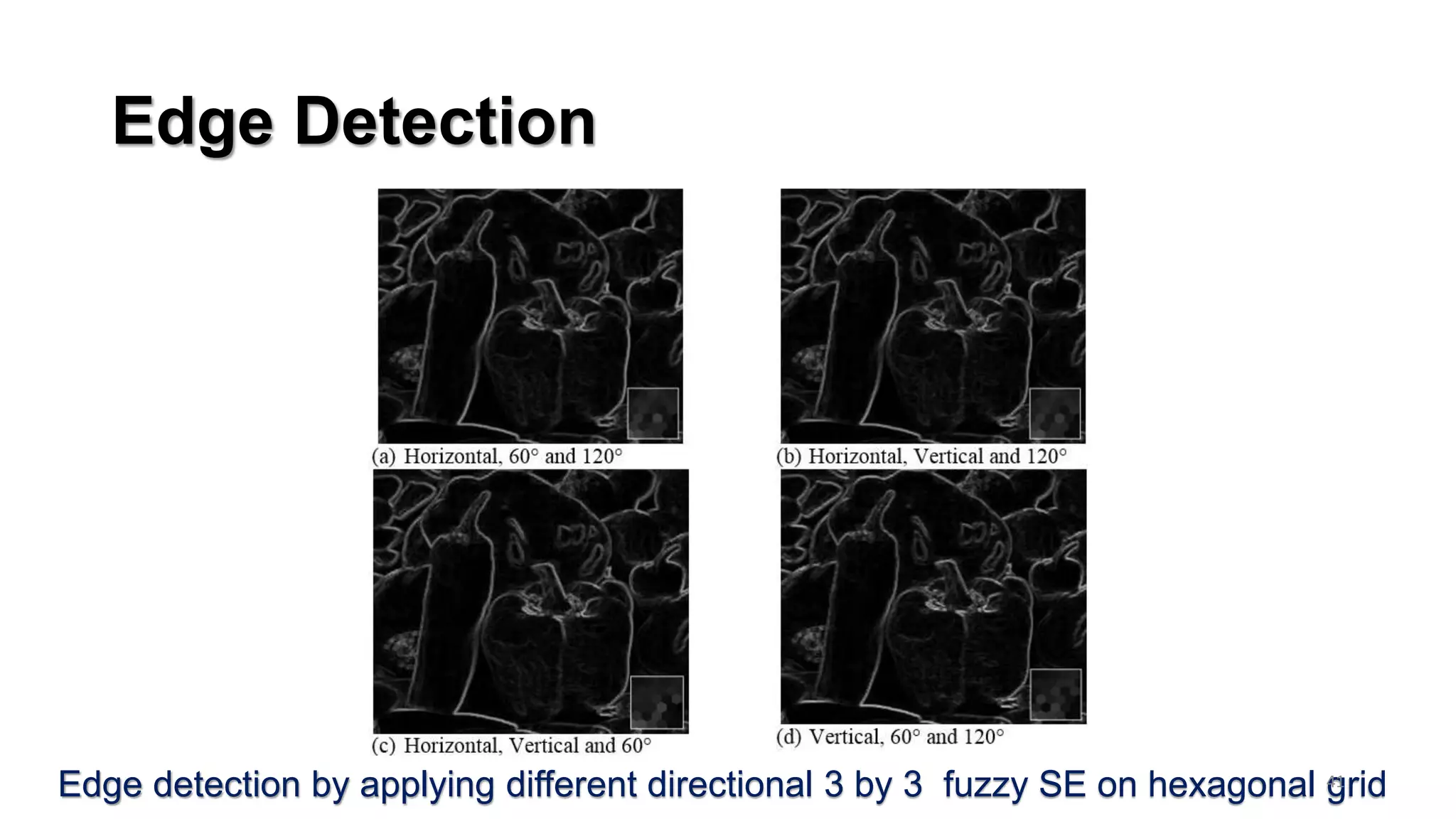
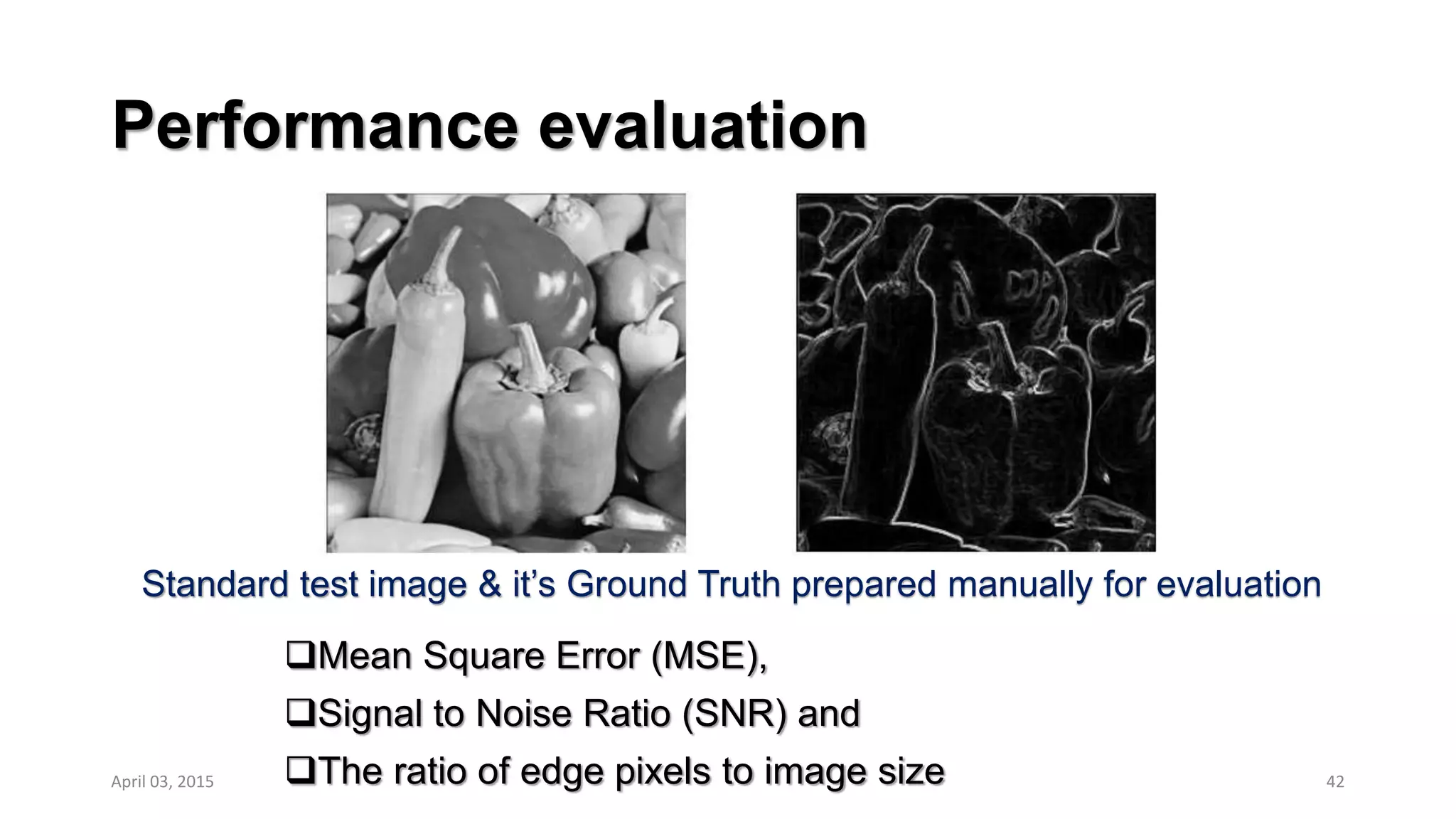
The document outlines a research project on developing edge detection methods and walking strategies for multi-legged robots. It discusses using morphological operations on hexagonal grid images to remove noise and detect edges for low resolution images in real-time applications with low computational power. It describes developing structuring elements of various sizes and directions, and comparing performance of hexagonal versus rectangular grid images. The document also explores using fuzzy morphology and discusses evaluating different methods to determine the optimal approach for edge detection to enable efficient walking strategies for robots with damaged legs.
![What is Fuzzy Set?
Fuzzy sets first introduced by Lotfi A. Zadeh[1] as an extension of the
classical set theory
In crisp set a pixel is either black or white. For edge detection, its an
edge or a no-edge. But the edges are not always precisely defined.
Fuzzy images are characterized by the degree to which each pixel
belongs to a particular region
9
Crisp set and fuzzy set for grayscale image
[1] Zadeh, L. A. (1965). Fuzzy sets. Information and control, 8(3), 338-353.
Crisp set
“dark gray-levels”
fuzzy set
“dark gray-levels”
April 03, 2015](https://image.slidesharecdn.com/ppt20150401-160211065914/75/Multi-legged-Robot-Walking-Strategies-with-an-Emphasis-on-Image-based-Methods-9-2048.jpg)
![Multi Legged Robot
Considerable research[1,2] done on robot vision and has been primarily
based on the rule of forbidden walking regions
Inagaki[3] investigated the leg failure situations in hexapod robots of
which one leg was damaged.
More recently, Yang[4] mentioned that it is helpful to lock the joint
associated with a damaged motor.
However, locking mechanism always cannot provide support. When
collapse occurs at 2nd or 3rd joint in a leg
16
[1] R. Ponticelli and P. G. de Santos, "Obtaining terrain maps and obstacle contours for terrain-recognition tasks," Mechatronics, vol. 20, 2010.
[2] J. Estremera, et. al. "Continuous free-crab gaits for hexapod robots on a natural terrain with forbidden zones: An application to humanitarian demining,” Robotics & Autonomous Systems, 2010.
[3] K. Inagaki, "Gait study for hexapod walking with disabled leg," in Intelligent Robots and Systems, IROS'97.
[4] J.-M. Yang, "Gait synthesis for hexapod robots with a locked joint failure," Robotica, vol. 23, 2005.](https://image.slidesharecdn.com/ppt20150401-160211065914/75/Multi-legged-Robot-Walking-Strategies-with-an-Emphasis-on-Image-based-Methods-16-2048.jpg)
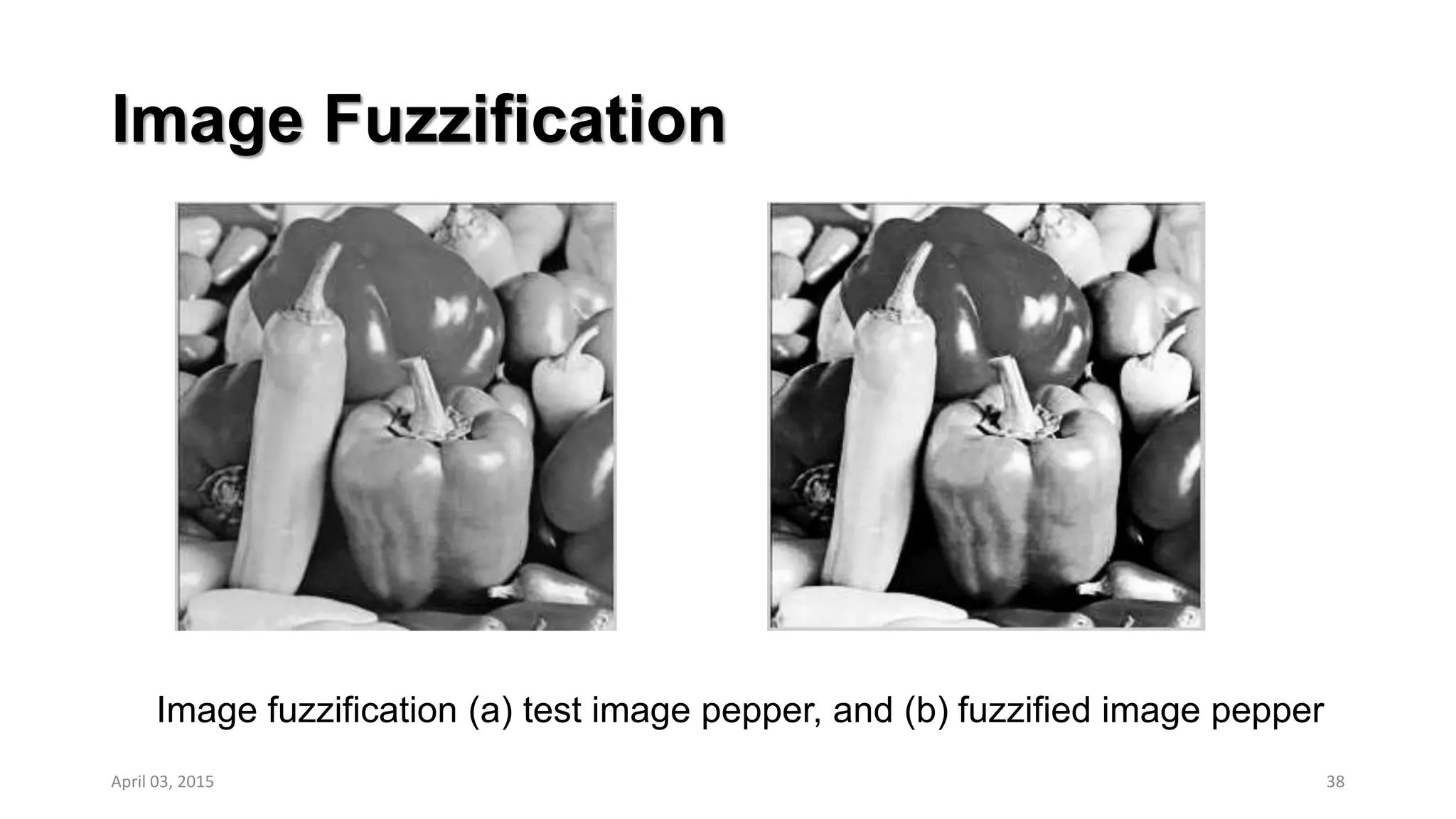
![Image Fuzzification
S-membership function as given below:
μ(x) = 0 x<a,
= 2 [(x -a)/(c - a)]2 a < x < b
= 1 – 2 [(x - c)/(c - a)]2 b < x < c,
= 1 x > c,
where, b is any value between a and c. For a = Xmin, c = Xmax
37
Membershipdegree
Pixels
April 03, 2015](https://image.slidesharecdn.com/ppt20150401-160211065914/75/Multi-legged-Robot-Walking-Strategies-with-an-Emphasis-on-Image-based-Methods-37-2048.jpg)
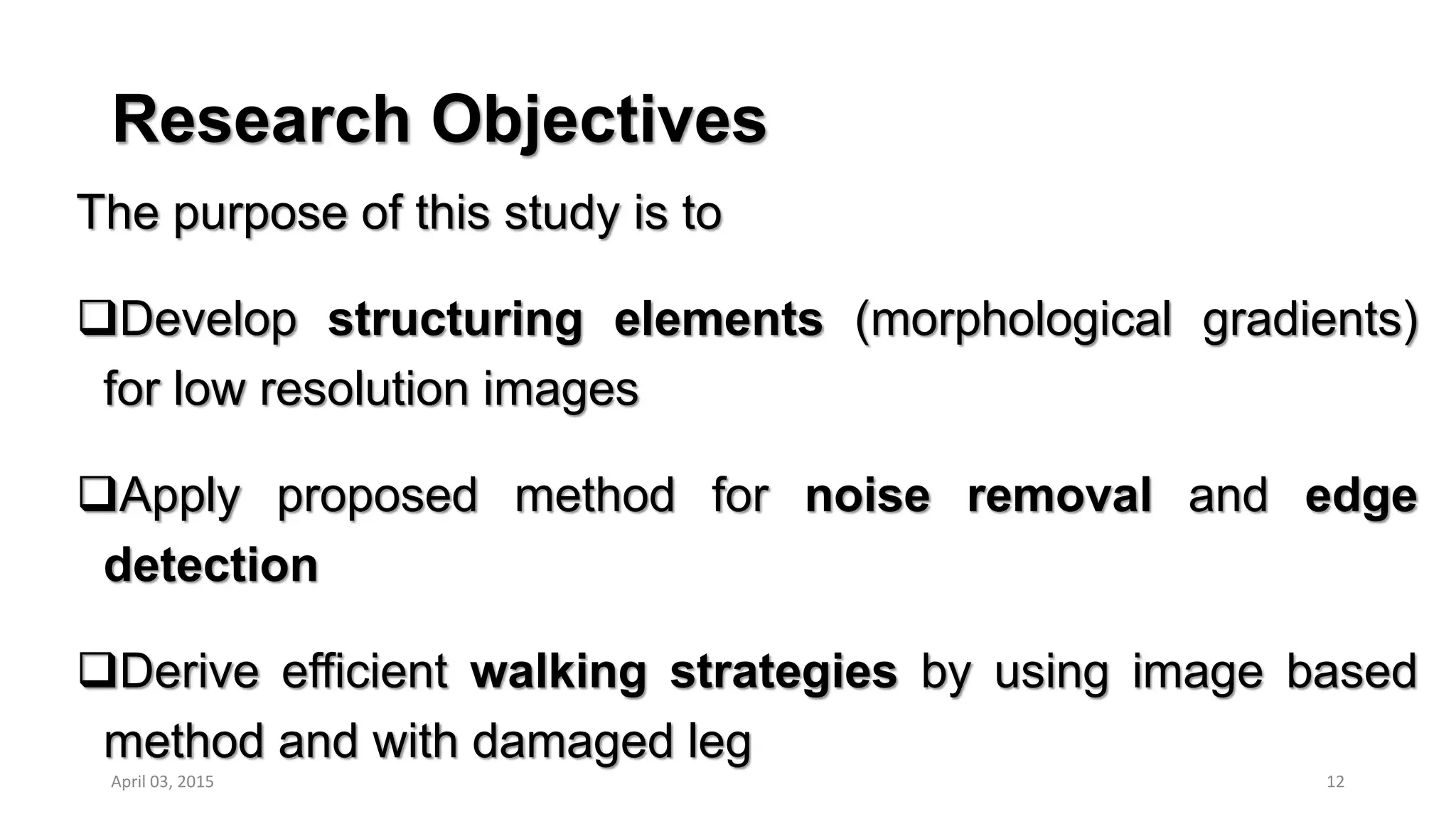
![Comparison of
Alternative Gait
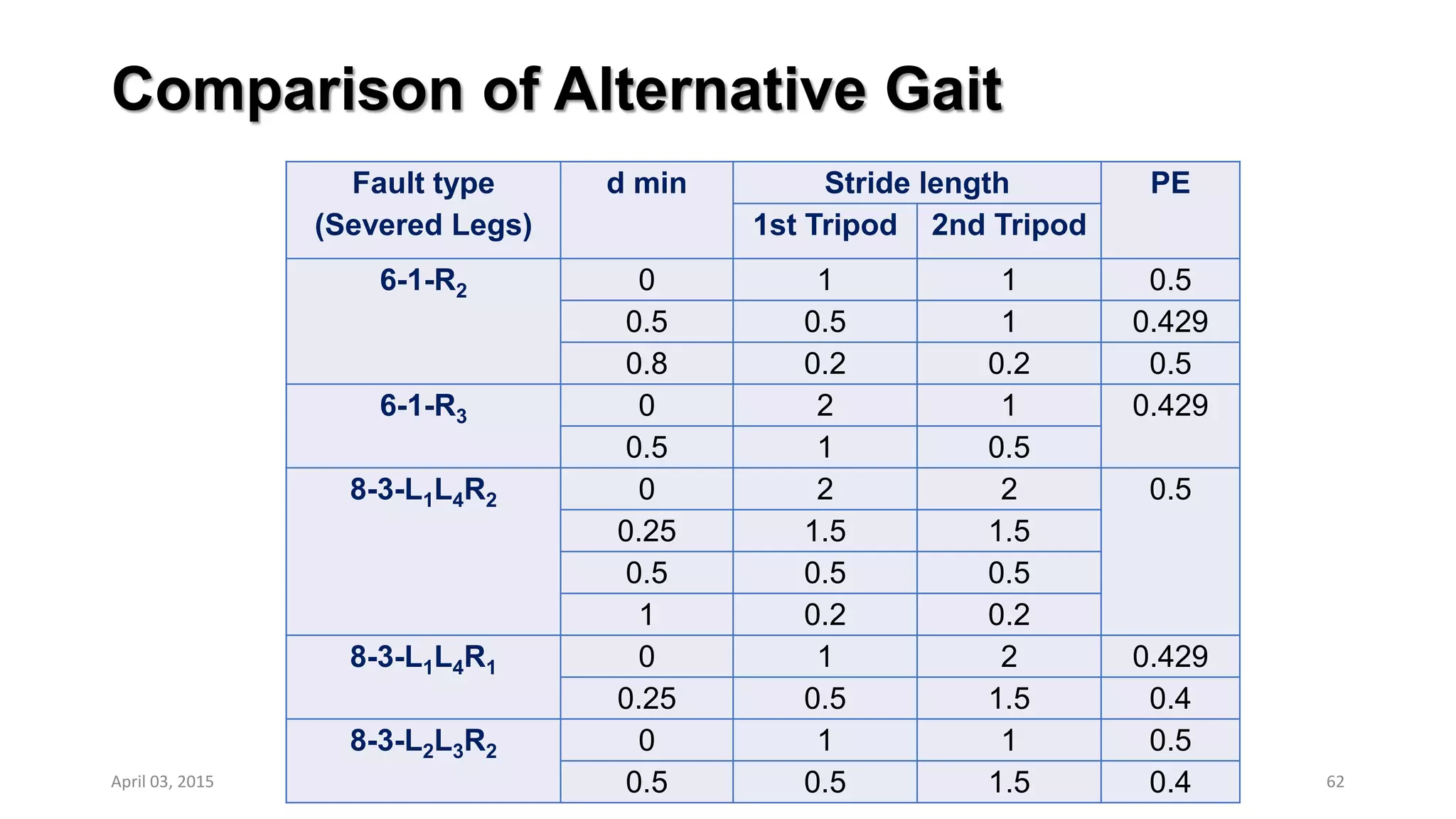
Fault type
(Severed Legs)
Axial stability
PE
[SL+]min [SL-]min
6-2
6-2-L3R3 3.75 0 0
6-2-L1R2 2 3.75 <0.2
6-2-L2R2 3.75 3.75 0.333
8-2
8-2-L2R3
1.52
1.52
1
8-2-L4R2
1.25
8-2-L4R1 1.25
8-2-L4R3
2.64 08-2-L4R4
8-2-L2L4
8-2-L2L3 0 0
8-2-L2R2 1.52 2.64
8-2-L1L4 1.25 1.25
8-3
8-3-L1L4R1
0
1.25
0.5
8-3-L2L3R2 2.64
8-3-L2L4R1, L4R1R2 1.25
8-3-L2L4R3, L3L4R2
1.52
0
8-3-L2L3R1, L2L4R4 <0.2
8-3-L3L4R3 2.64
0
8-3-L4R3R4 - -
8-3-L1L4R2
1.52 1.25 0.5
8-3-L2L4R2
8-4
8-4-L2L3R1R2
1.52
3.75
0
8-4-L2L4R1R2
2.64
8-4-L1L4R1R2 0
8-4-L2L4R3R4 3.75 0
8-4-L1L4R2R3
2.64
2.64
<0.2
8-4-L1L4R2R4 1.25
8-4-L2L3R1R3
3.75
8-4-L2L4R2R3
3.75
8-4-L2L4R2R4 1.25
8-4-L3L4R3R4 - - 0
8-4-L2L3R2R3 3.75 3.75 0.333
April 03, 2015 63](https://image.slidesharecdn.com/ppt20150401-160211065914/75/Multi-legged-Robot-Walking-Strategies-with-an-Emphasis-on-Image-based-Methods-63-2048.jpg)
![Non Fixed Position Adjustment (NFP)
64
Best Combination for [3|3] type gait sequence
(a) 8-2-L2 R3 type as an example
(b) Before adjustment, L3 R1 R4 constitute
support polygon
(c) SL + = 1.52 S, SL- = 2.64 S, d min = 0.53 S
(d) Six legged standard form by using step
less transportation.
(e) Now, SL + and SL- become equal (both
2.08 S), and d min = 1.08S and the whole
system become more stable
April 03, 2015
Support Polygon (L3 R1 R4 )
L3
R4
R1](https://image.slidesharecdn.com/ppt20150401-160211065914/75/Multi-legged-Robot-Walking-Strategies-with-an-Emphasis-on-Image-based-Methods-64-2048.jpg)
![Non Fixed Position Adjustment (NFP)
65
Best combination for [2|4] type
The R3 leg in (L3, R1, R3) support polygon
is first moved downward by 0.5S, making
(SL+) increase from 1.25S to 1.5S
Then L3 is move downward by 0.03S to
equalize the two SL values to 1.51S.
Since the other group (L2, R2, R4) is of
opposite shape, so it is adjusted reversely
The minimal SL value (dmin) is thus increased
from 1.25S to 1.51S.
This is now the better configuration for [2|4]
category
Support Polygon
(L3 R1 R3 )
R3L3
R1
L2 R2
L4](https://image.slidesharecdn.com/ppt20150401-160211065914/75/Multi-legged-Robot-Walking-Strategies-with-an-Emphasis-on-Image-based-Methods-65-2048.jpg)