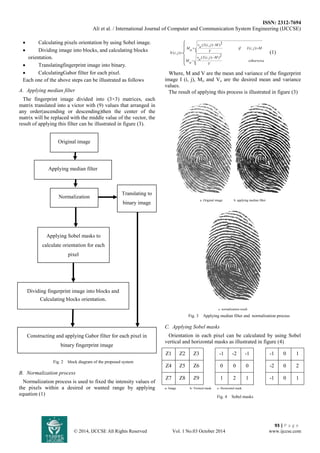
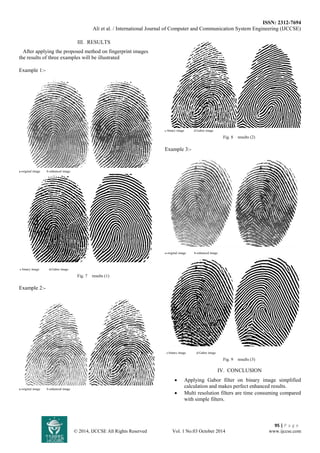
The document discusses the use of Gabor filters for enhancing biometric images, particularly fingerprint images, to improve feature extraction. It describes a proposed method involving several steps such as median filtering, normalization, orientation calculation, and translating the fingerprint image into binary format, followed by Gabor filter application. The results indicate that this approach simplifies calculations and yields better enhancement for fingerprint identification systems.


![ISSN: 2312-7694
Ali et al. / International Journal of Computer and Communication System Engineering (IJCCSE)
96 | P a g e
© 2014, IJCCSE All Rights Reserved Vol. 1 No.03 October 2014 www.ijccse.com
Good enhancement methods make fingerprint system more reliable.
REFERENCES
1- [Iwasokun 2012] Iwasokun Gabriel Babatunde, AkinyokunOluwole Charles, Alese Boniface Kayode, and OlabodeOlatubosun "Fingerprint Image Enhancement: Segmentation to Thinning",(IJACSA) International Journal of Advanced Computer Science and Applications, 2012.
2- [Kumud 2011] KumudArora, and Dr.PoonamGarg "A Quantitative Survey of various Fingerprint Enhancement techniques", International Journal of Computer Applications, 2011.
3- [Liu 2008] Liu Wei "Fingerprint Classification Using Singularities Detection", international journal of mathematics and computers in simulation, 2008.
4- [Peihao 2007] Peihao Huang, Chia-Yung Chang, Chaur-Chin Chen "Implementation of an Automatic Fingerprint Identification System", IEEE, 2007.
5- [Salil 2002] Salil Prabhakar, Anil K. Jain, and Sharath Pankanti "Learning fingerprint minutiae location and type", Watson Research Center, Yorktown Heights, NY 10598, USA, 2002.
6- [William 2001] William K. Pratt "digital image processing ", Los Altos, California, USA, 2001.](https://image.slidesharecdn.com/rp30105815-141110061602-conversion-gate02/85/Gabor-Filter-5-320.jpg)